01 Novak Standards
-
Upload
rumen-genov -
Category
Documents
-
view
221 -
download
2
Transcript of 01 Novak Standards

Information Security Standards
Luděk Novák, CISA, CISSP
2nd May 2007

2
Agenda
Sub-commission JTC 1/SC 27 – IT Security techniques
Information security management standards (ISO/IEC 27000 family)
Cryptographical standards Security evaluation standards Security controls and services Identity management and privacy
IT Service management

3
Tutorial aims
Introduction to activities of organizations for standardization• ISO – International Organization for Standardization
http://www.iso.org • ČNI – Czech standards institute
http://www.cni.cz Compact overview of new and upcoming information security
standards• Activities of sub-commission JTC1/SC27
– IT Security techniques
It is not possible discussed details of the standards

4
Introduction of sub-commission JTC 1/SC 27
Focus of sub-commission JTC 1/SC 27 – IT Security techniques• Identification of generic requirements (including requirements
methodology) for IT system security services• Development of security techniques and mechanisms (including
registration procedures and relationships of security components)• Development of security guidelines
(e.g., interpretative documents, risk analysis)• Development of management support documentation and
standards (e.g., terminology and security evaluation criteria)
Sub-commission activities review• Over 80 projects (nearly 50 active) • More than 50 published information security standards• A lot of interesting suggestion has shown up recently

5
Structure of JTC1/SC 27 – IT Security techniques
From 2006 JTC 1/SC 27/WG 1
Information security management systems (ISMS)
JTC 1/SC 27/WG 4Security controls and services
JTC 1/SC 27/WG 2Cryptography a security mechanisms
JTC 1/SC 27/WG 3Security evaluation and assessment
JTC 1/SC 27/WG 5Identity management and privacy technologies
Till 2006 JTC 1/SC 27/WG 1
Requirements, security services and guidelines
JTC 1/SC 27/WG 2Security techniques and mechanisms
JTC 1/SC 27/WG 3Security evaluation criteria

6
Working group aims
Source: JTC 1/SC 27

7
Work programme for WG1: Information Security Management System (ISMS)
Published ISO/IEC 27001:2005
Information security management system – Requirements
ISO/IEC 27002:2005 (ISO/IEC 17799)Code of practice for information security management
ISO/IEC 27006:2007 Requirements for the accreditation of bodies providing certification of ISMS
ISO/IEC 13335Management of information and communications technology security
ISO/IEC TR 13335Guidelines for the management of IT Security
Upcoming ISO/IEC 27005
Information security risk management
ISO/IEC 27004Information security management metrics and measurements
ISO/IEC 27000Information security management system fundamentals and vocabulary
ISO/IEC 27003Information security management system implementation guidance
ISO/IEC 27007Information security management system auditor guidelines(not approved)

8
ISO/IEC 27000 family New family accepted in the spring 2005
• Different numbers for BS 7799 based standards (ISO/IEC 17799 vice versa ISO/IEC 24743)
Harmonization of two concepts• ISO/IEC 13335 – academic approach• BS 7799 – pragmatic approach
ISO/IEC 27000 family criteria• Provide direct support or detailed guidance and interpretation for the
implementation of the PDCA processes and requirements of defined in ISO/IEC 27001 (e.g. risk assessment, identification of assets, ISMS effectiveness)
• Address conformity assessments or sector-specific requirements for ISMS
• Contribute and add value to ISO/IEC 27001 of the PDCA processes• Specification of a relationship to ISO/IEC 27001• Standards excluded from this ISMS family are those that only
address the implementation of controls from ISO/IEC 27002 – see WG4 activities

9
ISO/IEC 27000 family review
ISMS Overview and vocabularyISO/IEC 27000:2008? (ISO/IEC 13335-1)
ISMS MeasurementISO/IEC 27004:2008?
Risk managementBS 7799-3:2006
ISO/IEC 27005:2007? (ISO/IEC TR 13335-3:1998)
ISMS RequirementsISO/IEC 27001:2005
(BS 7799-2:2002)
ISMS Code of practiceISO/IEC 27002:2005
(ISO/IEC17799)
ISMS Implementation guidelines
ISO/IEC 27003:2008?
ISMS Auditor GuidelinesISO/IEC 27007?
Specific standards and guidelines
Annex A
ISMS Certification schemeISO/IEC 27006:2007 (EA 7/03)

10
ISO/IEC 27001:2005 (formerly BS 7799-2)
Information security management system – Requirements • Standards is based on BS 7799-2:2002• ISO/IEC 27001 published in October 2005
(BS 7799-2 validity was finished)• Czech version (ČSN ISO/IEC 27001:2006) published
in October 2006 ISMS Certification is based on this standard !!!
• Transformation period for BS 7799-2 is 1,5 year i.e. till 14th April 2007
• Audits after 14th April 2006 should follow ISO/IEC 27001• Accreditation bodies specifies necessary details

11
ISO/IEC 27001:2005 principlesDefinition of requirements on Information Security Management
System – ISMS Information security management process based on PDCA Model
• Plan – Do – Check – ActEnsure the selection of adequate and proportionate security controls
that protect information assets and give confidence to interested parties
All defined requirements are mandatory and it is not possible to exclude anyone
• But it is not necessary to implement all security controls !!!
Requirements
Plan
Do
Check
Act
Satisfaction SatisfactionCus
tom
ers Requirements
Supp
liers

12
Plan – Establish ISMS
ISMS process requirements ISMS Scope ISMS Policy Risk management (BS 7799-3)
• Define a risk management approach
• Identify and assess risks• Evaluate risk treatment
options • Select security controls
(ISO/IEC 27002:2005) Management approval
• ISMS Operation • Residual risks
Statement of applicability
Recommendations Assign a responsible security
manager ISMS training
• Project team• Asset owners
Appropriate risk management• Adequate approach to risks • Assets and their owners
identification• Maintenance of the risk
catalog Statement of applicability
• Key document for any security manager

13
Implement and operate ISMS
Plan – outline of activities during a year/cycle Manual – ISMS long term policies, rules and
procedures Measurement – ISMS effectiveness indicators and
metrics Awareness – people should know, understand and
follow the policies Sources – there is no ISMS without people (and
tools) Documentation – document live cycle rules !!! Records – evidence of particular ISMS activities

14
Monitor and review ISMS
ISMS monitoring and checking• Management and responsible persons• Security incidents assessment• Results of ISMS measurements
ISMS Internal audits• Internal auditors
ISMS Reviews• Senior management

15
Maintain and improve ISMS
Continual improvement• Positively based –
using chances to improve ISMS
Corrective actions Preventive actions
• Negatively based – eliminate nonconformities, mistakes, failures, …

16
ISO/IEC 27001:2005 main changes
Slightly revised BS 7799-2:2002 New requirement to measure effectiveness of ISMS ISMS internal linkages are more important
• Demonstrate relationship from selected controls back to risk assessment and treatment
New requirements on statement of applicability• Information if control is currently implemented
Review of risk assessment as a part of ISMS management review (at least annually)
Small changes in text and structure• ISMS Internal audit as the chapter 6 – formerly 6.4• Annex B was removed – Guidance on use of the standard
(it will be transferred to ISO/IEC 27003)• Using of security controls from ISO/IEC 17799:2005

17
ISO/IEC 27002:2005 (ISO/IEC 17799)
Code of practice for information security management
• Complex and balanced set of controls how to protect information assets
• Code of practice is respected internationally
• Published in June 2005• Czech edition in August 2006• ISO/IEC 27002 should be used since
spring 2007
Information security „best practice“ is described
• 11 security clauses• 39 control objectives• 133 controls• Structured description
• Control• Implementation guidance• Other information
• Verb „should“ is used
There is no management system in the standard There are no management techniques how to select and
enforce security controls (see ISO/IEC 27001)

18
Structure of ISO/IEC 27002:2005 (ISO/IEC 17799)
Source: ISO/IEC 17799:2005
Security clauses
Organizing information
security
Information systems
acquisition, development
and maintenance
Information security incident management
Access control
Business continuity
management
Compliance
Human resources security
Security policy
Asset management
Communications and operations management
Physical and environmental
security

19
Main changes in ISO/IEC 27002:2005 (ISO/IEC 17799)
Formal changes Structured control description
• Control, implementation guidance, other information More precise terminology
• Security forum -> Management commitment to information security
Selected changes in control catalogue External subject security
• Merge of third parties and outsourcing, customer access security New approach to human resource security
• Follows employment live-cycle: prior to employment, duding employment, termination or change of employment
New clause for information security incident management New controls related to progress of security needs
• Responsibility for assets (ownership of assets and acceptable use of assets)• Controls against mobile codes• On-line transactions• Technical vulnerability management
Removal of some so technical controls • Cryptography, data network, ...

20
!!! ISO/IEC 17799:2000 using danger !!!
Attention! There are a lot of mistakes and inaccuracies in the version from 2000 – high risk of using inappropriate methodology including ČSN ISO/IEC 17799:2001 or ČSN ISO/IEC 17799:2005
Big disadvantage of the old version is that authorizations are not taken away• There is no control for employment termination• It has influence to a lot of security controls• A lot of trivialities are missing – e.g. changing of passwords set by
vendors, …
ISO/IEC 27002:2005 solves the problems • Operating system access controls are also applicable e.g. on DBMS

21
ISMS Overview and vocabularyISO/IEC 27000 – ISMS Overview and vocabulary
Fundamental principles, concepts and vocabulary for ISMS Based on OECD principles
• Awareness of the need for information security• Responsibility assignment of information security• Response to prevent and detect information security incidents• Ethics respecting legitimate interests• Democracy to ensure information security is compatible with society values• Risk Management providing levels of assurance towards acceptable risks• Security design and implementation incorporated as an essential element• Security management ensuring a comprehensive approach• Continuous improvement of information security
Harmonization with other management systems (QMS, EMS, ITSMS, …)
Publishing planed at the end of 2008• ISO/IEC 13335-1:2004 will be withdrawn

22
ISMS Implementation guidanceISO/IEC 27003 – Information Security Management System Implementation Guidance
Recommendation how to implement ISMS effectively Critical success factors Deep explanation of all ISMS requirements following PDCA
• Objectives• Preconditions• Organizing the work• Who to involve• How is it done• Results
Document and record recommendations
Be published at the end of 2008

23
ISMS Measurements
ISO/IEC 27004 Information Security Management Measurements A tool for definition of ISMS metrics and indicators Pre-defined structure for metrics and how to deal with metrics
• Measure name and code• Purpose of measure• Measurement calculation details• Value and scale – Nominal, Ordinal, Interval, Ratio• Data Collection Procedure• Stakeholders – Owner, Customer, Collector, Communicator, Reviewer• Life cycle – frequency of collection, periodicity of reporting, period of
analysis etc.• Decision criteria
Completely new standard – publishing is planed in 2008 (middle) Important for the future – indicator based argumentation

24
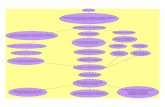
ISMS Measurement as a feedback
Source: draft of ISO/IEC 27004
Indicators
Decision criteria
Risk management
Security measures
Security management
Measurementmethods
Information flows
Security effectiveness
Business needs
Define measurement
priorities

25
Examples of ISMS metrics
Percentage (%) of system users/security personnel that have received basic awareness training
Average frequency of audit records review and analyses for inappropriate activity
Percentage of systems using automated mechanisms to conduct analysis and reporting of inappropriate activities
Percentage (%) of systems that are compliant with the baseline configuration
Percentage (%) of systems successfully addressed in the testing of the contingency plan
Percentage of accounts not associated with specific users Percentage (%) of system components that undergo maintenance on
schedule Cost of information security incidents of unauthorized access to
information systems, due to physical security failures Percentage (%) of employees who signed acknowledgement that they
have read and understood rules of behavior, before being authorized access to the information system
Source: NIST SP 800-80 Guide for Developing Performance Metrics for Information Security (draft)http://csrc.nist.gov/publications/drafts/draft-sp800-80-ipd.pdf

26
Risk management
ISO/IEC 27005 – Information Security Risk Management Based on ISO/IEC TR 13335-3
• A lot of texts, where essential is a bit hidden• BS 7799-3 as pragmatic approach
Concept interprets risk assessment and treatment requirements of ISO/IEC 27001
Wide catalogues of threats and vulnerabilities Harmonization with general risk management rules
(upcoming standard ISO/IEC 25700 – Risk management) Publishing planed at the end of 2007
• ISO/IEC TR 13335 – parts 3 and 4 will be withdrawn

27
Information Security Risk Management
BS 7799-3:2006 – Guidelines for Information Security Risk Management
Risk assessment• Asset identification• Legal, regulatory and contractual requirements• Asset valuation• Identification and assessment of threats and vulnerabilities• Risk calculation and evaluation• Risk assessor
Risk treatment and management decision-making• Decision-making• Risk treatment (reduce/accept/avoid/transfer risks)• Residual risk
Ongoing risk management activities• Maintenance and monitoring
http://www.bsi-global.com/ICT/Security/bs7799-3.xalter

28
ISMS certification rules
ISO/IEC 27006 – Requirements for the accreditation of bodies providing certification of information security management systems
Hot issue• Previous rules EA-7/03 follow BS 7799-2:1999
which was not based on PDCA model Close relationship with new compliance rules
ISO/IEC 17021:2006 • Certification body requirements • Certification audit requirements• Certification auditor requirements• ISMS audit recommendations
Published February 2007

29
Management of ICT security (ISO/IEC 13335 future)
ISO/IEC 13335 – Management of Information and Communications Technology Security (MICTS)• Part 1: Concepts and models for information and
communications technology security management (2004)• Merge of part 1 and 2 of previous ISO/IEC TR 13335
• Part 1: Concepts and models for IT Security• Part 2: Managing and planning IT Security
• It will be withdrawn by publishing of ISO/IEC 27000
ISO/IEC TR 13335 – Guidelines for the management of IT Security (GMITS)• Part 3: Techniques for the management of IT Security (1998) • Part 4: Selection of safeguards (2000)• Previously planed as revision of ISO/IEC 13335-2• As ISO/IEC 27005 a member of ISO/IEC 27000 family• They will be withdrawn by publishing of ISO/IEC 27005
• Part 5: Management guidance on network security (2001)• Covered by ISO/IEC 18028 – IT Network security

30
BSI (British Standard Institute) Guidelines
BIP 0071 – Guidelines on requirements and preparation for ISMS certification based on ISO/IEC 27001
BIP 0072 – Are you ready for ISMS audit based on ISO/IEC 27001:2005?
BIP 0073 – Guide to the implementation and auditing of ISMS controls based on ISO/IEC 27001
BIP 0074 – Measuring the effectiveness of your ISMS implementations based on ISO/IEC 27001
http://www.bsi-global.com/ICT/Security/index.xalter

31
ISMS for industrial branches
ISO TR 13569:2005 – Information Security Guidelines for Financial Services
ISO 27799 – Security Management in Health Using ISO/IEC 17799
ISO/IEC 27031 – Security management guidelines for telecommunications (ISMS-T X.1051)
Considered projects• ISMS for lotteries• ISMS for transportation• ISMS for automotive industry• ISMS for small and medium business

32
Financial services security
ISO TR 13569:2005 – Financial Services – Information Security Guidelines• Corporate information security policy• Management of information security – Security programme• Organization for information security• Risk analysis and assessment• Security controls implementation and selection• IT systems controls• Implementation of specific controls
(financial cards, cheques, electronic money, ...)• Miscellaneous• Follow-up safeguards• Incident handling
Focused on financial specifics + useful examples Guidelines are not fully compliant with ISO/IEC 27000 family

33
ISMS in health
ISO 27799 – Security Management in Health Using ISO/IEC 17799
Specific requirements for ISMS in health industry• ISO/IEC 27001 – interpretation of ISMS
requirements• ISO/IEC 17799 – details for security controls
(if necessary) General ISMS is strictly followed
It is a pity that number of ISO/IEC 17799 is changing

34
Work programme for WG2: Cryptography and Security Mechanisms (1)
ISO/IEC 7064 Data processing – Check character systems• Published 2003
ISO/IEC 9796 Digital signature schemes giving message recovery• 3 parts published 2002 – 2006, under revision
ISO/IEC 9797 Message authentication codes (MACs) • 2 parts published 1999 – 2002, under revision, 3rd part is upcoming
ISO/IEC 9798 Entity authentication• 6 parts published 1997 – 2005
ISO/IEC 10116 Modes of operation for an n-bit block cipher algorithm• Published 2006
ISO/IEC 10118 Hash-functions• 4 parts published 1998 – 2004 (2006), under revision
ISO/IEC 11770 Key management• 4 parts published 1996 – 2006, under revision

35
Work programme for WG2: Cryptography and Security Mechanisms (2)
ISO/IEC 13888 Non-repudiation• 3 parts published 1997 – 2004, under revision
ISO/IEC 14888 Digital signatures with appendix• 3 parts published 1998 – 2006, under revision
ISO/IEC 15946 Cryptographic techniques based on elliptic curves • 4 parts published 2002 – 2004, under revision
ISO/IEC 18031 Random bit generation• Published 2005
ISO/IEC 18032 Prime number generation• Published 2005
ISO/IEC 18033 Encryption algorithms • 4 parts published in 2005 – 2006
ISO/IEC 19772 Data encapsulation mechanisms• Upcoming

36
Work programme for WG3: Security Evaluation and Assessment
Common criteria etc. ISO/IEC 15408:2005
Evaluation criteria for IT Security
ISO/IEC 18045:2005Methodology for IT security evaluation
ISO/IEC TR 19791:2006Security assessment of operational systems
ISO/IEC 15292:2003Protection profile registration procedures
ISO/IEC TR 15446:2004Guide on the production of protection profiles and security targets
ISO/IEC 19790:2006Security requirements for cryptographic modules
ISO/IEC 24759Test requirements for cryptographic modules
ISO/IEC 21827:2003Systems Security Engineering – Capability Maturity Model (SSE-CMM)
ISO/IEC 15443A framework for IT security assurance

37
Common criteria and their progress ISO/IEC 15408 – Evaluation criteria for IT security
• Part 1: Introduction and general model • Part 2: Security functional requirements• Part 3: Security assurance requirements
ISO/IEC 18045 – Methodology for IT security evaluation ISO/IEC 15446 – Guide for the production of protection profiles and
security targets
Common criteria are general framework• Trend to simplify works of evaluators without reduction of evaluation quality

38
Operational system assessment
ISO/IEC TR 19791:2006Security assessment of operational systems
Implementation and operationsecurity aspects enlargement of evaluation scheme based on „Common criteria“ (ISO/IEC 15408)
New groups of requirements• System protection profile (SPP)• System security target (SST)

39
Operation security requirementsSeven new classes for operation security functions FOD – Administration
• Security policy, management forum, management review, personnel roles and responsibilities, risk management, incident management, service agreements
FOS – IT Systems • Security requirements, change control, malicious code control, development and
operational environment, network security, monitoring, records FOA – User Assets
• User assets management, roles and responsibilities, privacy FOB – Business
• Business impact analysis, fault isolation, business continuity plans, intellectual property FOP – Facility and Equipment
• Equipment, facilities and premises within the operational system FOT – Third party
• Security operational control requirements for third parties FOM – Management
• Management of operational controls (security parameters, classification of assets, security responsibilities, reporting of security incidents)
Nine new classes for operation security assurance

40
CMM® Security
ISO/IEC 21827 – Systems Security Engineering – Capability Maturity Model (SSE-CMM®)
Capability model for security Advantage: more levels to compare security enforcement Not fully compliant with ISMS (ISO/IEC 27001)

41
SSE-CMM® process structureSecurity Base Practices PA01 Administer Security Controls PA02 Assess Impact PA03 Assess Security Risk PA04 Assess Threat PA05 Assess Vulnerability PA06 Build Assurance Argument PA07 Coordinate Security PA08 Monitor Security Posture PA09 Provide Security Input PA10 Specify Security Needs PA11 Verify and Validate Security
Project and Organizational Base Practices PA12 – PA 22: Ensure quality, manage configurations, manage project, manage
product line evolution, coordinate with suppliers, …
Harmonized with software live cycle rules• ISO/IEC 15504 – Process assessment • ISO/IEC 15288 – System life cycle processes

42
Cryptographic modules securityISO/IEC 19790:2006 – Security requirements for cryptographic modules
International version of FIPS 140-2Security requirements in 4 levelsSecurity testing of cryptographic
modules outside US
Evaluation methodology defined as ISO/IEC 24759 – Test requirements for cryptographic modules
It is expected that FIPS 140-3 will be incorporated into next revision
Security features Cryptographic module
specification Cryptographic module ports
and interfaces Roles, services, and
authentication Finite state model Physical security Operational environment Cryptographic key
management Self-tests Design assurance Mitigation of other attacks

43
IT Security assurance
ISO/IEC TR 15443 – A framework for IT security assurance

44
Some studied methods ISO/IEC 12207 – Software Life Cycle
Processes ISO/IEC 14598 – Software product
evaluation ISO/IEC 15288 – System Life Cycle
Processes ISO/IEC 15504 – Software Process
Assessment ISO/IEC 13335 – Management of
information and communications technology security (MICTS)
ISO/IEC 15408 – Evaluation criteria for IT security
ISO/IEC 17799 – Code of practice for information security management
BS 7799.2 – Information security management systems – Specification with guidance for use
ISO/IEC 21827 – Systems Security Engineering – Capability Maturity Model (SSE-CMM®)
CMM – Capability Maturity Model (for Software)
SA-CMM – Software Acquisition Capability Maturity Model
SE-CMM – Systems Engineering Capability Maturity Model
CMMI – Capability Maturity Model Integration
TSDM – Trusted Software Development Methodology
IT Baseline Protection Manual Penetration Testing Personnel Assurance – e.g. CISA,
CISM, CISSP, CPP Rational Unified Process (RUP)
CobiT – Control Objectives for Information and related Technology

45
Work programme for WG4: Security Controls and Services
ISO/IEC 14516Guidelines on the use and management of Trusted Third Party services
ISO/IEC 15945Specification of TTP services to support the application of digital signatures
ISO/IEC 18014Time stamping services and protocols
ISO/IEC 24762Guidelines for information and communications technology disaster recovery services
ISO/IEC 18028IT network security
ISO/IEC 15947IT intrusion detection framework
ISO/IEC 18043:2006Guidelines for the selection, deployment and operations of Intrusion Detection Systems (IDS)
ISO/IEC TR 18044:2004Information security incident management

46
ISO/IEC 18028 – IT network security ISO/IEC 18028-1:2006
Part 1: Network security management
ISO/IEC 18028-2:2006 Part 2: Network security architecture
ISO/IEC 18028-3:2005 Part 3: Securing communications between networks using security gateways
ISO/IEC 18028-4:2004Part 4: Securing remote access
ISO/IEC 18028-5:2005 Part 5: Securing communications across networks using virtual private networks

47
Network security management
ISO/IEC 18028-1:2006 – IT network security Part 1: Network security management Using of PDCA Model (Plan – Do – Check – Act) Harmonized with general approaches to information security
management Security controls harmonized with ISO/IEC 27002
(ISO/IEC 17799) Security risks and controls for different types of networks
• Local Area Networking• Wide Area Networking• Wireless Networks• Radio Networks• Broadband Networking• IP Convergence (data, voice, video)

48
Concept of network security management

49
Appropriate Potential Control Areas
Network Security Architecture (ISO/IEC 18028-2) Secure Service Management Framework Network Security Management Technical Vulnerability Management (ISO/IEC 17799:12.6) Identification and Authentication (ISO/IEC 17799:11.4) Network Audit Logging and Monitoring (ISO/IEC 17799:10.10) Intrusion Detection (ISO/IEC 17799:13) Protection against Malicious Code (ISO/IEC 17799:10.4) Common Infrastructure Cryptographic Based Services
(ISO/IEC 17799:12.3) Business Continuity Management (ISO/IEC 17799:14)

50
Tree views on reference architecture
ISO/IEC 18028-2:2006 – IT network security Part 2: Network security architecture Security Dimension
• Grouping of security measures that are used to implement particular aspects of network security
Security Layer• Hierarchy of network equipment and facility groupings
Security Plane • Certain type of network activity protected by the
mechanisms

51
Security Dimension Access Control
• Authorization for the use of the network resources Authentication
• Confirmation of identities or other authorizing attributes of communicating entities.
Non-repudiation• Technical means for preventing an individual or entity from denying having
performed a particular action Data Confidentiality
• Protection of data from unauthorized disclosure Communication Flow
• Ensurance that information flows only between the authorized end points Data Integrity
• Ensurance of correctness or accuracy Availability
• Ensurance that there is no denial of authorized access to network elements, stored information, information flows, services and applications due to events impacting the network
Privacy• Protection of any information that might be derived from the observation of
network activities

52
Security layers
Application Security Layer• Security of the network-based applications accessed by
customers (web, e-mail, ASP, ...) Service Security Layer
• Security of services that Service Providers provide to their customers (from basic transport and connectivity to service enablers)
Infrastructure Security Layer • Network transmission facilities as well as individual
network elements (routers, switches, servers, communication links, ...)

53
Security plane
End-user Security Plane• Security of access and use of the Service Provider's
network by customers Control Security Plane
• Protection of the activities that enable the efficient delivery of information, services and applications across the network
Management Security Plane• Protection of Operations Administration Maintenance
and Provisioning (OAM&P) functions of the network elements, transmission facilities, back-office systems (Operations Support Systems, Business Support Systems, Customer Care Systems, etc.) and Data Centres

54
Reference architecture for network security

55
Network security policy (example)
Introduction Starting points Terms and definitions Network security areas
• Application services security• Communication services security• Infrastructure security• Network security control• Network security management
Policy updating Security goals Applied controls

56
Using security gateways
ISO/IEC 18028-3:2005 – Part 3: Securing communications between networks using security gateways
Selection and configuration• Selection of a security gateway
architecture and appropriate components
• Hardware and software platform• Configuration• Security features and settings• Administration• Logging• Documentation• Audit• Training and education
Techniques• Packet filtering• Stateful packet inspection• Application proxy• Network Address Translation (NAT)• Content analyzing and filtering
Security Gateway Architectures• Packet filter firewall• Dual-homed gateway• Screened host• Screened subnet

57
Remote access security
ISO/IEC 18028-4:2004 – Part 4: Securing remote access Information on the various types and techniques for remote
access and helps the intended audience to identify adequate measures to protect remote access against identified threats
Includes wireless access Security policy example

58
Virtual private networks
ISO/IEC 18028-5:2005 – Part 5: Securing communicationsacross networks using Virtual Private Networks VPN Security objectives and requirements Guidelines for the selection of secure VPNs Guidelines for the implementation of secure VPNs Technologies and protocols used to implement VPNs
• Layer 2, layer 3, upper layers• FR, ATM, MPLS, PPP, L2F, L2TP, IPsec, SSL, SShell

59
Intrusion detection systems
IDS Selection • Information Security Risk Assessment• Host or Network IDS• Considerations• Tools that complement IDS (SIM, …)• Scalability • Technical support • Training
IDS Deployment• Advantages/disadvantages
of different IDS types IDS Operations
• IDS Tuning • IDS Vulnerabilities • Handling IDS Alerts • Response Options • Legal Considerations
ISO/IEC 18043:2006 – Selection, deployment and operations of intrusion detection systems

60
Security incident managementISO/IEC TR 18044:2004 Information Security Incident Management
Plan – ISIRT Plan and Prepare• Information Security Incident Management Policy, Scheme and Policies • Establishment of Information Security Incident Response Team (ISIRT)• Awareness and Training
Do – ISIRT Use• Detection and Reporting • Event/Incident Assessment and Decision• Responses
Check – ISIRT review• Further Forensic Analysis• Lessons Learnt • Identification of Security and/or Scheme Improvements
Act – ISIRT Improve• Make Security Improvements• Security Risk Analysis and Management Improvement• Make Scheme Improvements

61
Home network security
ISO/IEC 24767 – Home Network Security Secure interconnection of electronic equipments in home networks
• Part 1: Security Requirements and Internal Security Services: Secure Communication Middleware Protocol
• Part 2: External security service Prepared by sub-commission JTC1/SC25 Published during 2007

62
Business continuity management (BCM)
Complexity of BCM is similar to ISMS Two/tree independent activities related to BCM
• British Standards Institution is preparing a new standard BS 25999
• Part 1: Code of practice (published 2006)• Part 2: Specification (in development)
• JTC 1/SC 27 is working on a new standardISO/IEC 24762 – Guidelines for information andcommunications technology disaster recovery services
• Based on Singapore standard SS 507 for Business Continuity/Disaster Recovery (BC/DR) Service Providers
• JTC 1/SC 27 is waiting for BCM project approval

63
Business continuity management (BCM)
Code of practice – BS 25999-1:2006 • BCM policy• BCM programme management • Understanding the organization• Determining business continuity
strategy• Developing and implementing
a BCM response• Exercising, maintaining and
reviewing BCM arrangements
• Embedding BCM in the organization’s culture
BCM Specification will be published as BS 25999-2 during 2007• BS 25999 replaces PAS 56:2003

64
Work programme for WG5: Privacy, Identity and Biometric Security ISO/IEC 15816
Security information objects for access control
ISO/IEC 24760A framework for identity management
ISO/IEC 29100A privacy framework
ISO/IEC 29101A privacy reference architecture
ISO/IEC 19792A framework for security evaluation and testing of biometric technologies
ISO/IEC 24745Biometric template protection
ISO/IEC 24761Authentication context for biometrics
ISO/IEC 29115Authentication assurance

65
Summary of JTC 1/SC 27 work Systematic progress and standard harmonization Pragmatic approach to standard development
using best practice PDCA Model as basic part for process definition
Standardization future• Security management for small and medium business• Privacy• Controls for security control failure• PDCA Cycle feedback
• Monitoring and checking• ISMS Auditing• Continual improvement
Source: http://isotc.iso.org/livelink/livelink?func=ll&objId=327974&objAction=browse&sort=name

66
Security related management systems
Software engineering rules• Quality management and software live cycle• IT Service management
High influence on risks in IT environment• Important security improvements

67
Quality management (QMS)
Quality – ability of products/services to satisfies defined and expected requirements
QMS is well-known and generally accepted management system• Tool for communication with other departments and end-users• Basic requirements on resource, document and record management
etc.• Primary aim for information technology management
ISO/IEC 90003 – Guidelines for the application of ISO 9001:2000 to computer software
Source: ISO Fosus, February 2005
ISO/IEC 90003Product
realizationResource
managementMeasurement, analysis and
improvements
Quality management
systemManagement responsibility

68
Concept of software engineering
Zdroj: ISO Fosus, February 2005
ISO 9001:2000 – Quality managementISO/IEC 90003:2004 – Software quality management
ISO/IEC 12207 Software life
cycle processes
ISO/IEC 9126Product quality
ISO/IEC 16326Project management
ISO/IEC 15846/ISO 10007Configuration management
ISO/IEC 15504Process assessment
ISO/IEC 14143Functional size measurement
ISO/IEC 14102Evaluation and selection of CASE tools
ISO/IEC 15026System and software integrity levels
ISO/IEC 14764Software maitenance
ISO/IEC 15910Software user documentation process
ISO/IEC 14598Software product avaluation
ISO/IEC 15939Software measurement process

69
IT Service management (ITSM)
IT Service – a described set of facilities, IT and non-IT, supported by the IT service provider that fulfils one or more needs of the Customer and that is perceived by the Customer as a coherent whole
ITSM definition • Specification – ISO/IEC 20000-1:2005 (BS 15000-1)• Code of practice – ISO/IEC 20000-2:2005 (BS 15000-2)
Other resources • ITIL – IT Infrastructure Library (nowadays version 2)
(detail explanation of ISO/IEC 20000 processes)• ITIL version 3 will be released in May 2007
• Some ITIL derivations – IBM, HP, Microsoft, Sun, …Microsoft Operations Framework http://www.microsoft.com/mof
• IT Service Management Forum Czech Republic http://www.itsmf.cz

70
ISO/IEC 20000 Overview International standard for IT service management
• Part 1: Specification• Part 2: Code of practice
ISO/IEC 20000 based on BS 15000• Just small changes and improvements• Based on PDCA Model• Using of ITIL best practice
As ISO published in December 2005• Czech version of part 1 published in October 2006• Part 2 will be published during 2007

71
ISO/IEC 20000 and ITIL relationship
ISO/IEC 20000 – International standard• Part 1: Specification (16 pages)• Part 2: Code of practice (34 pages)
BSI – Interpretations and recommendations• BIP 0005 – A Manager's Guide
to Service Management • BIP 0015 – IT Service Management.
Self-assessment workbook (72 pages)• BIP 0030 – BIP 0039 Publications
ITIL – Detail explanation of processes• Service support (~ 300 pages)• Service delivery (~ 350 pages)• Business perspective (~ 180 pages)
ITIL
BIP 0005BIP 0015
ISO/IEC 20000

72
IT service management processes
Source: ISO/IEC 20000
Service Delivery Processes
Relationship Processes
Resolutin Processes
Release Process
Capacity Management
Release Management
Control Processes
Supplier Management
Business Relationship Management
Change Management
Problem Management
Configuration Management
Incident Management
Information Security Management
Service Level Management
Service Continuity and
Availability Management
Service Reporting Budgeting and Accounting for
IT services
Planning and implementing new or changed services

73
ISO/IEC 20000 Processes (1) Service delivery processes
• Service level managementObjective: To define, agree, record and manage levels of service
• Service reportingObjective: To produce agreed, timely, reliable, accurate reports for informed decision making and effective communication
• Service continuity and availability managementObjective: To ensure that agreed service continuity and availability commitments to customers can be met in all circumstances
• Budgeting and accounting for IT servicesObjective: To budget and account for the cost of service provision
• Capacity managementObjective: To ensure that the service provider has, at all times, sufficient capacity to meet the current and future agreed demands of the customer’s business needs
• Information security managementObjective: To manage information security effectively within all service activities
Source: ISO/IEC 20000

74
ISO/IEC 20000 Processes (2) Relationship processes
• Business relationship managementObjective: To establish and maintain a good relationship between the service provider and the customer based on understanding the customer and their business drivers
• Supplier managementObjective: To manage suppliers to ensure the provision of seamless, quality services
Resolution processes• Incident management
Objective: To restore agreed service to the business as soon as possible or to respond to service requests
• Problem managementObjective: To minimize disruption to the business by proactive identification and analysis of the cause of incidents and by managing problems to closure.
Source: ISO/IEC 20000

75
ISO/IEC 20000 Processes (3) Control processes
• Configuration managementObjective: To define and control the components of the service and infrastructure and maintain accurate configuration information
• Change managementObjective: To ensure all changes are assessed, approved, implemented and reviewed in a controlled manner
Release process• Release management process
Objective: To deliver, distribute and track one or more changes in a release into the live environment
Planning and implementing new services• Planning and implementing new or changed services
Objective: To ensure that new services and changes to services will be deliverable and manageable at the agreed cost and service quality.
Source: ISO/IEC 20000

76
PDCA Model for IT service management
Source: ISO/IEC 20000 and Jenny Dugmore
Manage servicesManagement responsibility
PLANPlan service management
DOImplement
service management
Business requirements
Customer requirements
Request for new/changed services
Other processes e. g. business,
supplier, cusromer
Service Desk
Other teams, e.g. security, IT operations
Business results
Customer satisfaction
New / changed services
Team and people satisfaction
Other processese.g. business,
suplier, customer
CHECKMonitor, measure
and review
ACTContinual
improvement
Service Delivery Processes
Relationship Processes
Resolutin Processes
Release Process
Capacity Management
Release Management
Control Processes
Supplier Management
Business Relationship Management
Change Management
Problem Management
Configuration Management
Incident Management
Information Security Management
Service Level Management
Service Continuity and
Availability Management
Service Reporting Budgeting and Accounting for
IT services
Planning and implementing new or changed services

77
ISO/IEC 20000 Processes (4) IT service management system processes
• Requirements for a management systemObjective: To provide a management system, including policies and a framework to enable the effective management and implementation of all IT services
• Plan service management Objective: To plan the implementation and delivery of service management
• Implement service management and provide the servicesObjective: To implement the service management objectives and plan.
• Monitoring, measuring and reviewingObjective: To monitor, measure and review that the service management
• Continual improvementObjective: To improve the effectiveness and efficiency of service delivery and management
Source: ISO/IEC 20000

78
BSI Publications related to ISO/IEC 20000 BIP 0030 – Achieving ISO/IEC 20000 Management Decisions BIP 0031 – Achieving ISO/IEC 20000 Why People Matter BIP 0032 – Achieving ISO/IEC 20000 Making Metrics Work BIP 0033 – Achieving ISO/IEC 20000 Managing End-to-end
Service BIP 0034 – Achieving ISO/IEC 20000 Finance for Service
Managers BIP 0035 – Achieving ISO/IEC 20000 Enabling Change BIP 0036 – Achieving ISO/IEC 20000 Keeping the Service
Going BIP 0037 – Achieving ISO/IEC 20000 Capacity Management BIP 0038 – Achieving ISO/IEC 20000 Integrated Service
Management BIP 0039 – Achieving ISO/IEC 20000 The Differences
Between BS 15000 and ISO/IEC 20000
Source: http://www.bsi-global.com/ICT/Service/index.xalter ITIL
BIP 0005BIP 0015
ISO/IEC 20000

79
Conclusion
It is always easier to copy than starts form beginning
ISO and ČNI standards are good source for copying• Basic vision, what and how can be used, is needed
Copying si also needs high level of professionalism
Thanks for your attention and good lack