Wesley Shields & MuradKhan - … and Control Analysis • Malware protocols change • Protocols...
-
Upload
nguyenthuan -
Category
Documents
-
view
219 -
download
4
Transcript of Wesley Shields & MuradKhan - … and Control Analysis • Malware protocols change • Protocols...
© 2013 The MITRE Corporation. All rights reserved.
Wesley Shields & Murad Khan
Approved for Public Release; Distribution Unlimited. 13-0108
Does This Sound Familiar?
• You’re responding to an incident
• You find malware that talks on a network
• What happened?
– Who said what?
– Any information stolen?
– Additional malware uploaded?
– Any unknown C2?
© 2013 The MITRE Corporation. All rights reserved.
You Need Data!
• Collect data from the hosts
– Scale problems (lots of hosts, what data?)
– Compromised hosts can not be trusted
• Collect data from the network
– Less scale problems (still lots of data)
– Chokepoints make things manageable
– Unless you’re Travis Goodspeed et al. packets don’t lie (ground truth)
• We like network data!
© 2013 The MITRE Corporation. All rights reserved.
Command and Control Analysis
• Malware protocols change
• Protocols hide in plain sight
– So much HTTP based malware!
• Need to understand layer 7
– Existing tools for this: tcpdump, wireshark, vortex,
commercial tools, etc.
– All have various tradeoffs
© 2013 The MITRE Corporation. All rights reserved.
Introducing ChopShop
• Protocol analysis/decoding framework
• Python
• Open source
• Modular & extensible
© 2013 The MITRE Corporation. All rights reserved.
WAT?
© 2013 The MITRE Corporation. All rights reserved.
12 copies of the same function in 12 different files.
WAT?
© 2013 The MITRE Corporation. All rights reserved.
Yes, someone™ actually concatenated a bunch of payloads into a string!
“So I have this decoder for network traffic, except it doesn’t read PCAP files.”
Stop The Insanity!
© 2013 The MITRE Corporation. All rights reserved.
One base64 implementation
Multiple packet_time formats
Common timestamp printing function.
Likely won’t need packet_time family.
• Share common code in libraries!
ChopShop Design Goals
• Stop reinventing the wheel
• Modular
• Standardize
• Simple to use
• Simple to write
• Share the core
– The secret sauce is in the modules
© 2013 The MITRE Corporation. All rights reserved.
Increase Adoption
Sadly, C is a bit newbie unfriendly. Need to use something else…
Python sounds perfectly reasonable (and arbitrary)…
© 2013 The MITRE Corporation. All rights reserved.
https://twitter.com/codinghorror/statuses/904415232
Framework?
Core• Process data
• …
• Profit!
• Load modules
• Reassemble streams
• Hand streams to modules
• Process module position in
stream
• Handle bookkeeping
Modules
© 2013 The MITRE Corporation. All rights reserved.
• moduleName
• Required Functions:
– init(module_data)
– taste(tcp_data)
– handleStream(tcp_data)
• Optional Functions:
– module_info()
– teardown(tcp_data)
– shutdown(module_data)
The Anatomy of a Module
© 2013 The MITRE Corporation. All rights reserved.
Data Structures
AKA: Bookkeeping
(TCP Data Object)
• The core of the core of chopshop!
• From a module author’s perspective. ☺
• Important stuff it contains:
• addr – Quadtuple (src, sport, dst, dport)
• timestamp of the packet being processed
• Information about the client
• Information about the server
• Information relative to the stream as seen by a specific module
• Information about a specific module
• Functions it contains:
• discard() – How many bytes in the buffer this module has processed
• stop() – This module no longer cares about this stream
© 2013 The MITRE Corporation. All rights reserved.
• Things they contain you should care about:
– data: array of stream contents reassembled so far
– count: amount of data reassembled
– offset: where in the stream you currently are
– count_new: amount of data new in this call
Client and Server Objects?
© 2013 The MITRE Corporation. All rights reserved.
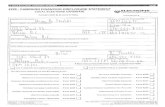
• Initialization (Required)
– Process your arguments
– Setup module_data?
• Process data
– taste() (Required)
– handleStream() (Required)
– teardown()
• Shutdown
– Flush buffers, print statistics, etc.
The Life of a Module
© 2013 The MITRE Corporation. All rights reserved.
Understanding RATs
• You can understand what a RAT can do by
RE’ing it
• You can understand what an operator of a RAT
did by decoding the protocol
• Don’t confuse actions taken by an operator
with actions taken automatically by the
malware!
© 2013 The MITRE Corporation. All rights reserved.
Gh0st
• Leaked source malware
• 33,400 results for “gh0st rat” on Google
• AV companies write about it a lot
• Attributed to Chinese hacking group
• Great example for this talk– If your malware is on wikipedia it isn’t a secret!
• The VOHO Campaign: An In Depth Analysis (RSA)
• Know Your Digital Enemy: Anatomy of a Gh0st RAT (McAfee)
• The Many Faces of Gh0st Rat (Norman ASA)
© 2013 The MITRE Corporation. All rights reserved.
Gh0st Protocol
• Flag: Usually 5 bytes (Gh0st, LURK0, Heart …)
– Usually human-readable, doesn’t have to be!
• DWORD: Compressed message length
• DWORD: Uncompressed message length
• WORD: zlib header
• Data
© 2013 The MITRE Corporation. All rights reserved.
Decoding Gh0st
• Goal: Figure out the size of the message.
• Search every DWORD in the first N bytes of a
stream.
• If the DWORD matches the packet length,
jump past the next DWORD and look for
\x78\x9c
• If zlib header exists, go back to length DWORD
and everything before it is the flag.© 2013 The MITRE Corporation. All rights reserved.
Decoding Gh0st
• Buffer up the entire message
• Decompress it
• Parse the token/command
• Profit…
© 2013 The MITRE Corporation. All rights reserved.
Problems With Decoding Gh0st
• Available source = Variants
• zlib technically not required
• New tokens and commands throw off the
enum
• Your mileage may vary in the wild
– Still need to RE malware!
© 2013 The MITRE Corporation. All rights reserved.
Demo Time
TapTap
ChopShopChopShop
Client*
(Evil Operator)
Client*
(Evil Operator)
Server*
(Victim Laptop)
Server*
(Victim Laptop)
© 2013 The MITRE Corporation. All rights reserved.
Tri-part Design
UI (ChopUi) Library (ChopLib)
ChopShop
Queue
Modules
stdout gui json
© 2013 The MITRE Corporation. All rights reserved.
Why ChopShop?
• Standard API, input and output, common
libraries
• Streaming not buffering
• Easier than writing wireshark plugins or
dissectors
• Rapid development
• Be as open about your decoders as you want
© 2013 The MITRE Corporation. All rights reserved.
Open Source
• https://github.com/MITRECND/chopshop
• http://www.mitre.org/work/cybersecurity/
• Create your decoders (modules)
• Contribute them back if you want
• Share them with your peers
© 2013 The MITRE Corporation. All rights reserved.
Questions?
rot13(ChopShop)
© 2013 The MITRE Corporation. All rights reserved.
http://blogs.rsa.com/wp-content/uploads/VOHO_WP_FINAL_READY-FOR-Publication-09242012_AC.pdf
http://download01.norman.no/documents/ThemanyfacesofGh0stRat.pdf
http://www.mcafee.com/us/resources/white-papers/foundstone/wp-know-your-digital-enemy.pdf