VeriFlow: Verifying Network-Wide Invariants in Real Time
-
Upload
open-networking-summits -
Category
Technology
-
view
61 -
download
4
Transcript of VeriFlow: Verifying Network-Wide Invariants in Real Time
VeriFlow: Verifying Network-Wide Invariants in Real Time
Ahmed Khurshid, Xuan Zou, Wenxuan Zhou, Matthew Caesar, P. Brighten Godfrey
University of Illinois at Urbana-Champaign (UIUC)
April 16, 2013
ONS 2013
Open Networking Summit
Challenges in Network Debugging
4/22/2013 Department of Computer Science, UIUC 2
http://groups.geni.net/geni/chrome/site/thumbnails/wiki/TangoGENI/OF-VLAN3715_1000.jpg
Complex interactions
Misconfigurations
Unforeseen bugs
Difficult to test the entire network state
space before deployment
Effects of Network Errors • Allow unauthorized
packets to enter a secured zone in a network
• Make services and the infrastructure prone to attacks
• Make critical services unavailable
• Affect network performance
4/22/2013 Department of Computer Science, UIUC 3
?
Network
Network Debugging Techniques
4/22/2013 Department of Computer Science, UIUC 4
Configuration Verification Traffic/Flow Monitoring
Software using Cisco NetFlow http://snmp.co.uk/scrutinizer/
Limitations of Configuration Verification
• Prediction is difficult
– Various configuration languages
– Dynamic distributed protocols
• Prediction misses implementation bugs in control plane
4/22/2013 Department of Computer Science, UIUC 5
Configuration
Control plane
Data-plane state
Network behavior
Input
Predicted
Our Approach: Data-plane Verification
• Less prediction
• Closer to actual network behavior
• Unified analysis for multiple control-plane protocols
• Can catch control-plane implementation bugs
4/22/2013 Department of Computer Science, UIUC 6
Configuration
Control plane
Data-plane state
Network behavior
Input
Predicted
Data Plane Verification in Action
• Our first tool, Anteater*, uses data plane verification technique to debug network operations
• We evaluated Anteater with UIUC campus network
– 178 routers
– 1,627 FIB entries per router (mean)
• It revealed 23 real bugs in 2 hours
4/22/2013 Department of Computer Science, UIUC 7
* Haohui Mai, Ahmed Khurshid, Rachit Agarwal, Matthew Caesar, P. Brighten Godfrey, and Samuel T. King, "Debugging the Data Plane with Anteater", ACM SIGCOMM, August 2011.
Finds problems after they occur and (potentially)
cause damage
Can we run verification in real time?
4/22/2013 Department of Computer Science, UIUC 8
Block dangerous changes
Provide immediate warning
Checking network-wide invariants in real time as the network evolves
Need to verify new updates at high speeds
Challenges in Real-Time Verification
• Challenge 1: Obtaining real-time view of network
– Solution: Utilize the centralized data-plane view available in an SDN (Software-Defined Network)
• Challenge 2: Verification speed
– Solution: Off-the-shelf techniques?
4/22/2013 Department of Computer Science, UIUC 9
No, too slow!
Our Tool: VeriFlow
• VeriFlow checks network-wide invariants in real time using data-plane state – Absence of routing loops and black holes, access
control violations, etc.
• Provides a set of functions to write custom query algorithms – Check forwarding behavior of specific packet sets – Verify effects of potential changes
4/22/2013 Department of Computer Science, UIUC 10
VeriFlow
New rules
VeriFlow Operation
4/22/2013 Department of Computer Science, UIUC 11
Network Controller
Generate equivalence
classes
Generate forwarding
graphs Run queries
Diagnosis report • Type of invariant violation • Affected set of packets
Rules violating network invariant(s)
Good rules
Limit the Search Space
4/22/2013 Department of Computer Science, UIUC 12
VeriFlow
Generate Equivalence Classes
Updates
Equivalence class: Packets experiencing the same forwarding actions throughout the network.
Fwd’ing rules
Equiv. classes
0.0.0.0/1 64.0.0.0/3
1 2 3 4
0.0.0.0/0
Experiment
• Simulated an IP network using a Rocketfuel topology – 172 routers
• Replayed Route Views BGP traces – 5 million RIB entries – 90K BGP updates
• Checked for loops and black holes
• Microbenchmarked each phase of VeriFlow’s operation
4/22/2013 Department of Computer Science, UIUC 13
Performance Result
4/22/2013 Department of Computer Science, UIUC 14
97.8% of the updates were verified within 1 millisecond
Experiment (cont.)
• Mininet OpenFlow network – Rocketfuel topology with 172 switches, one host per switch
• NOX controller, learning switch application
• TCP connections between random pairs of hosts
4/22/2013 Department of Computer Science, UIUC 15
NOX Controller + Switch Application
VeriFlow TCP SYN
Effect on Flow Table Update Throughput
4/22/2013 Department of Computer Science, UIUC 16
Up
dat
e th
rou
ghp
ut
(msg
/sec
)
Overhead of VeriFlow is low
Conclusion
• VeriFlow achieves real-time verification – A layer between SDN controller and network devices – Handles multiple packet header fields efficiently – Runs queries within hundreds of microseconds – Exposes an API for writing custom invariants
• Future work – Handling packet transformations efficiently – Dealing with multiple controllers
4/22/2013 Department of Computer Science, UIUC 17
Thank you
http://www.cs.illinois.edu/~khurshi1
Data Plane Verification in Action • FlowChecker [Al-Shaer et al., SafeConfig 2010]
– Uses BDD-based model checker
• Anteater [Mai et al., SIGCOMM 2011] – Uses SAT-based model checking – Revealed 23 real bugs in the UIUC campus network
• Header Space Analysis [Kazemian et al., NSDI 2012] – Uses set-based custom algorithm – Found multiple loops in the Stanford backbone network
4/22/2013 Department of Computer Science, UIUC 20
Find problems after they occur and
(potentially) cause damage
Running time: Several seconds to a few hours
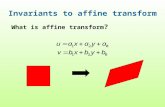
Computing Equivalence Classes
4/22/2013 Department of Computer Science, UIUC 21
(device, rule) pairs
(don’t care/wildcard)
2. Represent Forwarding Behavior
4/22/2013 Department of Computer Science, UIUC 22
VeriFlow
Generate Forwarding Graphs
Generate Equivalence Classes
Updates
All the info to answer queries!
Equivalence Class 1
Equivalence Class 2
3. Run Query to Check Invariants
4/22/2013 Department of Computer Science, UIUC 23
VeriFlow
Generate Forwarding Graphs
Generate Equivalence Classes
Run Queries Updates
Black holes, Routing loops, Isolation of multiple VLANs, Access control policies
Good rules Bad rules
Diagnosis report
•Type of invariant violation •Affected set of packets
API to write custom invariants
• VeriFlow provides a set of functions to write custom query algorithms – Gives access to the affected set of equivalence classes and
their forwarding graphs
– Verification becomes a standard graph traversal algorithm
• Can be used to – Check forwarding behavior of specific packet sets
– Verify effects of potential changes
4/22/2013 Department of Computer Science, UIUC 24
Performance Result
4/22/2013 Department of Computer Science, UIUC 25
97.8% of the updates were verified within 1 millisecond
Effect of Equivalence Class Count
4/22/2013 Department of Computer Science, UIUC 26
Number of ECs strongly influences verification time
Number of ECs affected by new rule
Effect of Multiple Header Fields
4/22/2013 Department of Computer Science, UIUC 27
Data link source
Data link destination
Network source
Network destination
Data link type
More fields -> More equivalence classes -> Longer verification time
Related Work • Header space analysis: Static checking for networks, NSDI 2012
• A NICE way to test OpenFlow applications, NSDI 2012
• Abstractions for network update, SIGCOMM 2012
• Debugging the data plane with Anteater, SIGCOMM 2011
• Can the production network be the testbed?, OSDI 2010
• FlowChecker: Configuration analysis and verification of federated OpenFlow infrastructures, SafeConfig 2010
• Network configuration in a box: Towards end-to-end verification of network reachability and security, ICNP 2009
4/22/2013 Department of Computer Science, UIUC 28
4/22/2013 Department of Computer Science, UIUC 30
A(1)
10.0.0.33
10.0.0.32
10.0.0.64 10.0.0.128
10.0.0.129
10.0.0.65 10.0.0.66
B(2)
C(3)
D(4)
E(5)
F(6)
G(7) H(8)
J(10)
I(9)
1
2
3
4
1
2
3
1 2
1
2 3 4
1 2
3 4
2
1 1
2
1 2
3
3
1 2 4
1 2
3
Name(ID)
Intfn
Intf1
4/22/2013 Department of Computer Science, UIUC 31
A(1)
10.0.0.33
10.0.0.32
10.0.0.64 10.0.0.128
10.0.0.129
10.0.0.65 10.0.0.66
B(2)
C(3)
D(4)
E(5)
F(6)
G(7) H(8)
J(10)
I(9)
1
2
3
4
1
2
3
1 2
1
2 3 4
1 2
3 4
2
1 1
2
1 2
3
3
1 2 4
1 2
3
Name(ID)
Intfn
Intf1