ab initio admin online training | ab initio admin course | ab initio admin training
System Admin Security Training
description
Transcript of System Admin Security Training

System Admin Security Training
Orange Team

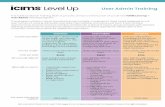
Overview System Admin Duties Employee Documents and Security Controls Security Threats Threat Mitigation Incident Response

System Admin Duties Perform backup and restore data Add and remove users Add and remove hardware and software Configure and maintain hardware and software General user support Maintain documentation and licenses Negotiate with vendors System planning Security management

System Admin Duties Monitor system resource usage and performance Detect and correct problems Optimize performance Manage resources Automate tasks Determine and enforce usage policy Educate users Corporate priority liaison

A Lot Of Things To Do… … and it’s better to do them securely! “Bake in” security Can’t anticipate all problems Can limit the problems you have

Perform Backup and Restore Data
Encrypt backups Secure storage
o Physical access controlo Environmental protections
Controlled restorationso No network connectionso Clean destination (no malware)o Verified assistance

Add and Remove Hardware and
Software Old accounts can be used as backdoor Completely remove old access rights Add users while adhering to…
o Need-to-knowo Minimum privilege

Add and Remove Hardware and
Software Inform users of potential outages Secure install
o Configure firsto Attach to network as late as possible
Secure removalo Install replacements firsto Avoid loss of functionalityo Dispose securely (data retrieval)

Configure and Maintain Hardware and Software
Keep copies of configurations Configure new elements before attaching to
network Use standard maintenance routines
o Documento Update
Verified assistance

General User Support Beware of social engineering Callers provide credentials
o Educate users to safeguard credentialso Do not prompt
Safeguard credentialso Do not reveal unnecessarilyo Protect methods for credential creation

Maintain Documentation and
Licenses Document procedureso New SA educationo Consistencyo Audit Assurance
Do not use illegitimate softwareo Cheapero Unethicalo Illegalo Insecure

Negotiate With Vendors
Licensed products can get expensive Minimize the cost of secure behavior Vendor relationships are important
o Inform them of security concernso Request new products/solutionso Receive updated hard/firm/softwareo Continued business is valued and will be rewarded

System Planning Scaling
o Security problems and solutions scale differentlyo New node = new possible failureo New AV != more secure
Assessing new technologyo Anticipate problemso “Shinier” does not mean “safer”
Anticipating and avoiding problemso Malware/attack trendso Follow day-to-day guidelines strictly

Security Management “An ounce of prevention is worth a pound of
cure.” Prioritize security Ideal management solution
o Simpleo Reproducible o Covers security needs
Your job, not the users

Monitor System Resource Usage and Performance
Do not invade privacy Use data to…
o Identify future purchaseso Notice potential threats
• Excessive or unusual usage• Antivirus logs
o Ensure expectations are met (SLA)

Detect and Correct Problems
Use system monitoring devices Preemptive corrections
o Patchingo Updatingo Upgrading
Reactive correctionso See incident response

Optimize Performance Users get frustrated with poor system
performance Users will optimize for themselves
o Non-complianceo Installing adware/freewareo Working around slow or ineffective processes
Don’t optimize by removing/compromising security

Manage Resources Know what you have and use Bad situations
o Unaccounted-for router on networko Unconfigured workstationo Ordering unneeded license keys
Wasting resources leads to budget cuts and layoffs
Misplacing resources leads to vulnerabilities

Automate Tasks Script day-to-day tasks Focus extra time on harder tasks Don’t introduce security holes
o Unauthorized use of privileged scripts/programso Scripts disabling security featureso Testing/Debugging/Configuration programs used on ‘live’
network

Determine and Enforce Usage Policy
Correct usage is essential Meaningless without enforcement

Educate Users A smart user is a safe user Eliminate “low hanging fruit”
o Social engineeringo Bad linkso Phishing emailso Removal media

Corporate Priority Liaison
Competing goalso Management’s budgeto Your securityo Customer’s service needso Employee convenience
Security needs to wino Sell to managemento Educate users

Employee Documents Acceptable Use Policy (AUP) Service Level Agreement (SLA) Non-Disclosure Agreement (NDA) Employee Contract
Your responsibility to enact if there are no documents.

Security Controls Need-to-know Security awareness training Separation of duties Job rotation Vacations Auditing/reviews

Security Threats External
o Hackingo E-mail attacks
Internalo Malwareo Ignoranceo Insider

Security Threats: Hacking
Exploitation of web services Poorly configured gateways Use of backdoors
o Social engineeringo Previous intrusiono Internal corroborator

Security Threats: E-mail
Phishing Spam Trojans Viruses

Security Threats: Malware
Many sourceso Hackingo Insidero Ignorance
Spreads quickly Use up resources

Security Threats: Ignorance Clicking bad links Poor e-mail discretion Downloading malware USB attacks

Security Threats: Insider
Usually hardest to detecto They know the systemo Sometimes privileged user
Disgruntled employee Abuse of trust

Threat Mitigation Preparation
o Security practiceso Education
Incident Response Plano If none, create one
Form a Computer Security Incident Response Teamo Individuals capable of correct responseo Include members of management

Incident Response Identify Initial Response
o Record basic detailso Assemble CSIRTo Notify important individuals
Formulate strategy Investigate
o Thorough data collectiono Determine what/who/how
Report Resolve

Rules To Work By A smart user is a safe user Policy enforcement is the first step to a secure
system Put security first in everything you do

BibliographyMandia, Kevin, Chris Prosise, and Matt Pepe. Incident Response & Computer Forensics. Second ed. N.p.: Brandon A. Nordin, n.d. 11-32. Print.