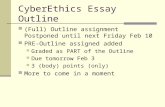
Outline
description
Transcript of Outline


Outline
Infections 1) r57 shell 2) rogue software
What Can We Do? 1) Seccheck 2) Virus total 3) Sandbox
Prevention 1) Personal Software Inspector 2) Network Software Inspector

















Basic Steps for an Infection Save all important data Best: Wipe the machine-do a fresh
install If this is not possible- then try to clean it Change all passwords Install latest anti-virus software Apply all patches Turn on the Firewall Let the NSO know so we can search for
other compromised machines

Advanced Steps for an Infection SecCheck Virus Total Malware Analysis:1.Norman Sandbox2.Anubis3.CWSandbox4.Threat Expert

Different Types of Infections Virus – Relies on users to spread:
email attachments, links in an email Worm – can spread on its own Trojan – A malicious file that appears
to be legitimate Bot – A worm that phones home to a
Command & Controller so the attacker can give it instructions

What Do Most Infections Do? Send Spam Scan the network Attack other machines – called a DDOS
(Distributed Denial of Service) attack Run a distribution server for malicious files:
web server or ftp server Set up a Phishing site Act as a proxy for other malicious traffic Download spyware and adware to the
machine Run a keylogger

Guidelines for Attempting to Clean a Machine Install an AV tool like Symantec Anti-
Virus Corporate Edition with the latest signatures and run a full scan
Other techniques/tools: Seccheck (Windows) netstat –anb (Windows command line) lsof (Linux) Ultimate Boot CD for Windows (UBCD) Sysinternals Suite (Windows GUI)

Spam Proxys and SecCheck
Lawrence Baldwin is the author of seccheck and owner of mynetwatchman.com
He was directly involved in taking down a spam botnet which was responsible for sending out 5-10% of the mail on the Internet =~ about 2-10 billion spam messages per day

SecCheck continued
Windows forensic tool Aids in the detection and removal
of malicious software Passive Runs in about three-six minutes Send me the URL for the report
and I can help analyze it

STC Josh Leibner after running SecCheck“I'm pretty baffled as to why AV,
HijackThis, and AdAware didn't catch any of this. I'll set up another appointment with the student so that I can more thoroughly clean the computer.”

Actual Reports for WashU IPs http://sc.mynetwatchman.com/seccheck/Submissio
nStatus.jsp?submissionID=190837b316eedbd6aab02db074f67a77
http://sc.mynetwatchman.com/seccheck/SubmissionStatus.jsp?submissionID=76a554a590f845d26fc06274d5a847c8
http://sc.mynetwatchman.com/seccheck/SubmissionStatus.jsp?submissionID=4d7ab225b5f447f6346db1f4733bbac6
http://sc.mynetwatchman.com/seccheck/SubmissionStatus.jsp?submissionID=70c2f42b966fe39baf6478595d92403b
http://sc.mynetwatchman.com/seccheck/SubmissionStatus.jsp?submissionID=7bc71e08adf1cf344d1689ac7a0d08a9





Use A Tool to Check for Third Party Software Vulnerabilities Like Secunia’s PSI or NSI








Useful Links:
http://www.virustotal.com/ http://www.norman.com/microsites/nsi
c/ http://anubis.iseclab.org/index.php http://www.cwsandbox.org/ http://www.mynetwatchman.com/
tools/sc/ http://technet.microsoft.com/en-us/
sysinternals/default.aspx http://www.ubcd4win.com/

Contact Information And More Useful Links http://nso.wustl.edu – NSO website If you have a computer security incident email the
NSO at [email protected] or directly to me at [email protected]
http://www.wustl.edu/policies/compolcy.html - WashU Computer Policy
www.mynetwatchman.com/tools/sc/ - Seccheck www.ubcd4win.com – Ultimate Boot CD for Windows www.antiphishing.org – Phishing Information mozilla.com – Download Firefox http://www.microsoft.com/athome/security/
spyware/software/default.mspx - Microsoft Defender

Watch Out For Malicious links and attachments Links to phishing and hacking sites, as
well as malicious files, can arrive by email, instant message, web page, etc.
Know your source! Verify before clicking. Don’t open anything unexpected. ~100 users were removed from the
network for days because of a bot infection transmitted through an AIM link

Use it to identify:PhishingMalicious linksAnd to protect personal information!