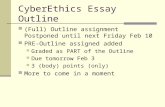
Outline
description
Transcript of Outline

International Grid Trust Federation
towards worldwide interoperability in identity
management
UK Presidency 2005 e-IRG Meeting
David L. Groep, IGTF and EUGridPMA Chair, 2005-12-13

e-Infrastructure Reflection Group – Dec 2005 - 2
David Groep – [email protected]
Outline
Grid Security Authentication vs. Authorisation Grid Identity Management
Authentication Federation EUGridPMA International Grid Trust Federation Guidelines and Requirements
Roadmap for an integrated AAI

e-Infrastructure Reflection Group – Dec 2005 - 3
David Groep – [email protected]
Essentials on Grid Security
Control access to shared services Support multi-user collaborations
Composed of individuals acting alone – their home organisation administration may not know about their activities
Allow users/application communities to establish relations Both personal and community-based aggregation of
resources, based on personal or community-mediated trust
Enable single sign-on Security must be hidden from the user as far as
possible
Resource owner must always stay in control

e-Infrastructure Reflection Group – Dec 2005 - 4
David Groep – [email protected]
Virtual vs. Organic structure
Organization A Organization B
Compute Server C1Compute Server C2
Compute Server C3
File server F1 (disks A and B)
Person C(Student)
Person A(Faculty)
Person B(Staff) Person D
(Staff)Person F(Faculty)
Person E(Faculty)
Virtual Community C
Person A(Principal Investigator)
Compute Server C1'
Person B(Administrator)
File server F1 (disk A)
Person E(Researcher)
Person D(Researcher)
Graphic from Frank Siebenlist, ANL & Globus AllianceGGF OGSA Working Group
Virtual communities (Virtual Organisation) are many A single person will typically be in many communities
Users want single signon across all these communities

e-Infrastructure Reflection Group – Dec 2005 - 5
David Groep – [email protected]
Stakeholders in Grid Security
Grid Security is user centric
Conceptually, all members of a VO are equal Users can provide their own services Provider organisations may or may not have human
members (or they actually only sell resources to a VO)
There is no a priori trust relationship between members VO lifetime can vary from hours to decades People and resources are members of multiple VOs VOs not necessarily persistent (both long- and short-lived)
… but a relationship is required as a basis for authorising access for traceability and liability, incident handling, and
accounting

e-Infrastructure Reflection Group – Dec 2005 - 6
David Groep – [email protected]
VO embedding today
as part of a Grid ‘ecosystem’where ecosystem takes care of end-to-end solution ‘Infrastructure’ (a collective of Resource Centres)
a single project-centric VOuser groups join up together and participate in a single project with implicit sharing agreement between users and
centres sharing across all user communities in the project still typical for transient, ad-hoc research collaborations
any single user may (and will) participate in both types

e-Infrastructure Reflection Group – Dec 2005 - 7
David Groep – [email protected]
Relying parties in Grid Security
In Europe Enabling Grid for E-sciencE (EGEE) (222 sites) Distributed European Infrastructure for Supercomputer
Applications (DEISA) (~11 sites) South East European Grid (SEE-GRID) (10 countries) many national projects (VL-e, UK e-Science, Grid.IT, IRISgrid,
…)
In the Americas EELA: E-infrastructure Europe and Latin America (24 partners) WestGrid (6 sites), GridCanada, … Open Science Grid (OSG) (54 sites) TeraGrid (9 sites) and also many others …
In the Asia-Pacific AP Grid (~10 countries and regions participating) Pacific Rim Applications and Grid Middleware Assembly (~15
sites) …
~400data as per December 8th, 2005

e-Infrastructure Reflection Group – Dec 2005 - 8
David Groep – [email protected]
Separating Authentication and Authorization
Single Authentication token (“passport”) issued by a party trusted by all, recognised by many resource providers, users, and VOs satisfies traceability requirement in itself does not grant any access, but provides
a unique binding between an identifier and the subject*
Per-VO Authorisations (“visa”) granted to a person/service or a set of them (a VO) granted by the resource owner based on the ‘passport’ name
providers can obtain lists of authorised users per VO,but can still ban individual users

e-Infrastructure Reflection Group – Dec 2005 - 9
David Groep – [email protected]
Grid Authorization today
Leverages authentication provided by a PKI (the ‘passport’) Identity management decoupled from access control Creation of short-lived ‘tokens’ (‘proxy’ certificates)
for single sign-on based on these identities
But: Variety of mechanisms
Per-resource list of authorized users Directories of authorized users Embedded assertions
Variety of sources of authority Semantics to describe roles and rights differs No common namespace
Integration with other AA mechanisms still in progress…

Authentication

e-Infrastructure Reflection Group – Dec 2005 - 11
David Groep – [email protected]
PKI in academia and industry and …
Various commercial providers Main commercial drive: secure web servers based on PKI Entrust, Global Sign, Thawte, Verisign, SwissSign, … primary market is server authentication, no end-user
identities
usually expensive but don’t actually subsume liability … are implicitly trusted by many,
since web browsers pre-install the roots of trust use of commercial CAs solves the ‘pop-up’ problem
... so for (web) servers a pop-up free service is still needed Academic PKI
generally a task of the NREN or national e-science project got better attention only after the advance of grid
computing National PKI
in generally uptake of 1999/93/EC is slow where available, a national PKI can be leveraged

e-Infrastructure Reflection Group – Dec 2005 - 12
David Groep – [email protected]
The Federated PKI for Grid Authentication
A Federation of many independent CAs common minimum requirements trust domain as required by users and relying parties well-defined and peer-reviewed acceptance process
No strict hierarchy with a single top spread of reliability, and limitation of failure (resilience) maximum leverage of national efforts and
complementarities
CA 1CA 2
CA 3
CA ncharter
guidelines
acceptanceprocess
relying party 1
relying party n

e-Infrastructure Reflection Group – Dec 2005 - 13
David Groep – [email protected]
Relying Party issues to be addressed
Common Relying Party requests on the Authorities
1. standard accreditation profiles sufficient to assure approximate parity in CAs
2. monitor [] signing namespaces for name overlaps
3. a forum [to] participate and raise issues
4. [operation of] a secure collection point for information about CAs which you accredit
5. common practices where possible
[list courtesy of the Open Science Grid]

e-Infrastructure Reflection Group – Dec 2005 - 14
David Groep – [email protected]
Building the federation
PKI providers (‘CAs’) and Relying Parties (‘sites’) together shape the common requirements Several profiles for different identity management
models Authorities testify to compliance with profile guidelines Peer-review process within the federation
to (re) evaluate members on entry & periodically
Reduce effort on the relying parties single document to review and assess for all CAs
Reduce cost on the CAs no audit statement needed by certified accountants but participation in the federation comes with a price
Requires that the federation remains manageable in size
Ultimate decision always remains with the RP

e-Infrastructure Reflection Group – Dec 2005 - 15
David Groep – [email protected]
EUGridPMA founded April 2004 as a successor to the CACG
The European Policy Management Authority for Grid Authentication in e-Science (hereafter called EUGridPMA) is a body
• to establish requirements and best practices for grid identity providers • to enable a common trust domain applicable to authentication of end-entities in inter-organisational access to distributed resources.
As its main activity the EUGridPMA
• coordinates a Public Key Infrastructure (PKI) for use with Grid authentication middleware.
The EUGridPMA itself does not provide identity assertions, but instead asserts that - within the scope of this charter – the certificates issued by the Accredited Authorities meet or exceed the relevant guidelines.
The EUGridPMA “constitution”

e-Infrastructure Reflection Group – Dec 2005 - 16
David Groep – [email protected]
EUGridPMA Membership
EUGridPMA membership for (classic) CAs a single Authority
per country, large region (e.g. the Nordic Countries), or international treaty organization.
‘the goal is to serve the largest possible community with a small number of stable CAs’
operated as a long-term commitment
Many CAs are operated by the (national) NREN(CESNET, ESnet, Belnet, NIIF, EEnet, SWITCH, DFN, … )
or by the e-Science programme/science foundation(UK eScience, VL-e, CNRS, … )

e-Infrastructure Reflection Group – Dec 2005 - 17
David Groep – [email protected]
Coverage of the EUGridPMA
Green: Countries with an accredited CA The EU member states (except LU, MT) + AM, CH, IL, IS, NO, PK, RU, TR, “SEE-catch-
all”
Other Accredited CAs: DoEGrids (.us) GridCanada (.ca) CERN ASGCC (.tw)* IHEP (.cn)** Migrated to APGridPMA per Oct 5th, 2005

e-Infrastructure Reflection Group – Dec 2005 - 18
David Groep – [email protected]
The Catch-All CAs
Project-centric “catch all” Authorities
For those left out of the rain in EGEE CNRS “catch-all” (Sophie Nicoud) coverage for all EGEE partners
For the South-East European Region regional catch-all CA
For LCG world-wide DoeGrids CA (Tony Genovese & Mike Helm, ESnet) Registration Authorities through Ian Neilson

e-Infrastructure Reflection Group – Dec 2005 - 19
David Groep – [email protected]
EUGridPMA Relying Party Members
All EU 6th framework e-Infrastructure projects DEISA EGEE SEE-GRID
The LHC Computing Grid Project (“LCG”) The Open Science Grid Project (US) TERENA
National projects represented via their national CA: e-Science programme UK Virtual Lab e-Science, the Netherlands …

e-Infrastructure Reflection Group – Dec 2005 - 20
David Groep – [email protected]
TACAR
Authoritative source for validation of trust anchors independent administration improves resilience TACAR certificate itself published in paper/journals Many trust anchors collected, not only for grid use

e-Infrastructure Reflection Group – Dec 2005 - 21
David Groep – [email protected]
Growth of the CACG and EUGridPMA
0
10
20
30
40
Mar
-01
Sep-0
1
Mar
-02
Sep-0
2
Mar
-03
Sep-0
3
Mar
-04
Sep-0
4
Mar
-05
Sep-0
5
acc
red
ited
CA
s
His
tory

e-Infrastructure Reflection Group – Dec 2005 - 22
David Groep – [email protected]
March 2003: The Tokyo Accord
… meet at GGF conferences. … … work on … Grid Policy Management Authority:
GRIDPMA.org develop Minimum requirements – based on EDG work develop a Grid Policy Management Authority Charter [with] representatives from major Grid PMAs:
European Data Grid and Cross Grid PMA: 16 countries, 19 organizations
NCSA Alliance Grid Canada DOEGrids PMA NASA Information Power Grid TERENA Asian Pacific PMA:
AIST, Japan; SDSC, USA; KISTI, Korea; Bll, Singapore; Kasetsart Univ., Thailand; CAS, China
His
tory

e-Infrastructure Reflection Group – Dec 2005 - 23
David Groep – [email protected]
Extending Trust:IGTF – the International Grid Trust Federation
TAGPMA APGridPMA
common, global best practices for trust establishment better manageability and response of the PMAs
The America’s Grid PMA
Asia-Pacific Grid PMA
European Grid PMA

e-Infrastructure Reflection Group – Dec 2005 - 24
David Groep – [email protected]
APGridPMA
13 members from the Asia-Pacific Region,
Launched June 1st, 2004, chaired by Yoshio Tanaka
First face-to-face meeting on Nov 29th, 2005 Today 6 ‘production-quality’ authorities in
operation
•AIST (.jp)•APAC (.au)•BMG (.sg)•CMSD (.in)•HKU CS SRG (.hk)•KISTI (.kr)•NCHC (.tw)
•NPACI (.us)•Osaka U. (.jp)•SDG (.cn)•USM (.my)•IHEP Beijing (.cn)•ASGCC (.tw)

e-Infrastructure Reflection Group – Dec 2005 - 25
David Groep – [email protected]
TAGPMA
To cover all of the Americas 8 members to date
Launched June 28th, 2005chaired by Darcy Quesnel, CANARIE
• Canarie (.ca)• OSG (.us)• TERAGRID (.us)• Texas H.E. Grid (.us)• DOEGrids (.us)
• SDSC (.us)• FNAL (.us)• Dartmouth (.us)
• Brazil (pending)

e-Infrastructure Reflection Group – Dec 2005 - 26
David Groep – [email protected]
IGTF Federation Structure
EUGridPMA• CA E1
• CA E2
• …
APGridPMA• CA A1
• …
TAGPMA• CA T1
• …
IGTF Federation Document
Common Authentication Profiles
Classic(EUGridPMA)
SLCS(TAGPMA)
trustrelations
SubjectNamespaceAssignment
DistributionNaming
Conventions

e-Infrastructure Reflection Group – Dec 2005 - 27
David Groep – [email protected]
Common Guidelines for all of the IGTF Federation Document• Namespace assignments• Distribution layout
Classic X.509 CAs with secured infrastructure
Short-lived Credential Services
‘experimental’ CAs
…
Collective requirements(technology agnostic)
Technology specificguidelines
Management assigned to specific PMAs

e-Infrastructure Reflection Group – Dec 2005 - 28
David Groep – [email protected]
Guidelines: common elements
Coordinated namespace Subject names refer to a unique entity (person, host) Basis for authorization decisions
Common Naming Common structure for trust anchor distribution in the
federation Trusted, redundant, download sources
Harmonized ‘concerns’ and ‘incident’ handling Guaranteed point of contact Forum to raise issues and concerns
Requirement for documentation of processes Detailed policy and practice statement Open to auditing by federation peers

e-Infrastructure Reflection Group – Dec 2005 - 29
David Groep – [email protected]
Guidelines: secured X.509 CAs
Identity vetting procedures Based on (national) photo ID’s Face-to-face verification of applicants
via a network of Registration Authorities Periodic renewal (once every year) Record retention at least 3 years
Secure operation off-line signing key or special (FIPS-140.3 or better)
hardware
Response to incidents Timely revocation of compromised certificates

e-Infrastructure Reflection Group – Dec 2005 - 30
David Groep – [email protected]
Guidelines: short-lived credential service
Issue short-lived credentials (for grid: proxies) based on another site-local authentication system e.g. Kerberos CA based on existing administration
Same common guidelines apply documented policies and processes a reliable identity vetting mechanism accreditation of the credential issuer with a PMA identity vetting data retention
Same X.509 format, but no user-held secrets

e-Infrastructure Reflection Group – Dec 2005 - 31
David Groep – [email protected]
Relationships: IGTF, PMAs, TACAR and GGF

e-Infrastructure Reflection Group – Dec 2005 - 32
David Groep – [email protected]
Five years of growth
December 2000: First CA coordination meeting for the DataGrid project
March 2003:Tokyo Accord (GGF7)
April 2004:Foundation of the EUGridPMA
June 2004:Foundation of the APGridPMA
June 2005:Foundation of TAGPMA (GGF14)
October 2005:Establishment of the International Grid Trust Federation IGTF
…

e-Infrastructure Reflection Group – Dec 2005 - 33
David Groep – [email protected]
Along the e-IRG Roadmap
the federated approach to an integrated AA infrastructure for eEurope
Towards an integrated AAI for academia in Europe
The e-IRG notes the timely operation of the EUGridPMA in conjunction with the TACAR CA Repository and it expresses its satisfaction for a European initiative that serves e-Science Grid projects. […] The e-IRG strongly encourages the EUGridPMA / TACAR to continue their valuable work […] (Dublin, 2004)
The e-IRG encourages work towards a common federation for academia and research institutes that ensures mutual recognition of the strength and validity of their authorization assertions. (The Hague, 2005)

e-Infrastructure Reflection Group – Dec 2005 - 34
David Groep – [email protected]
Recent developments in this direction
from the EUGridPMA side Extending PMA and the IGTF actively to more
countries and regions Specifically open to inter-working with other federations
from TERENA NRENs-GRID workshop series TF-EMC2 / TF-Mobility possible TACAR extensions
REFEDS – Research and Education Federations broad AAI scope IGTF, eduroam, A-Select, PAPI, SWITCH-AAI, InCommon,
HAKA, FEIDE/Moria See http://www.terena.nl/tech/refeds/

e-Infrastructure Reflection Group – Dec 2005 - 35
David Groep – [email protected]
EUGridPMA – http://www.eugridpma.org/
IGTF – http://www.gridpma.org/






![Outline Product Liability Riina Spr2009 Outline[1]](https://static.fdocuments.us/doc/165x107/54fbf0ed4a795937538b4ab9/outline-product-liability-riina-spr2009-outline1.jpg)