Worm Defense Alexander Chang CS239 – Network Security 05/01/2006.
-
Upload
shanna-walters -
Category
Documents
-
view
212 -
download
0
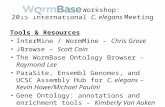
Transcript of Worm Defense Alexander Chang CS239 – Network Security 05/01/2006.

Worm Defense
Alexander ChangCS239 – Network Security05/01/2006

What is a worm?
Self-replicating/self-propagating programs
Spread from system to system without user interaction
Finds vulnerabilities in systems and uses them to spread
Spread via network Different from virus which requires
user interaction

Danger? Take over systems Access sensitive information
Passwords, credit card numbers, patient records, emails
Disrupts system functionsGovernment, nuclear power plants, hospitals
DDoS attack Bandwidth saturation

Code Red (CRv1)
July 13th, 2001 Exploit Microsoft IIS vulnerabilities Each infected system scans random
32bit IP addresses to attack Bug in the random generator
resulting linear spread

Code Red I (CRv2)
July 19th, 2001 Same as CRv1 but with random
generator bug fix DDoS payload targeting IP address of
www.whitehouse.gov Bug in the code made it die for date
>= 20th of the month

Code Red II
August 4th, 2001 Not related to Code Red (just
comment says Code Red) Exploit buffer overflow in MS IIS web
server Installed remote root backdoor which
can be used for anything

Nimda
September 18th, 2001 Multiple method of spreading
MS IIS vulnerabilityEmailCopying over network sharesWebpage infectionScan backdoor left by Code Red II
From no probing to 100 probes/sec in just 30 minutes

Sapphire/Slammer/SQLSlammer January 25th, 2003 Exploit MS SQL Server buffer overflow Fastest spreading worm Peak rate of 55million scans/sec after just 3
min Rate slowed down because bandwidth
saturation No malicious payload, just saturated
bandwidth causing many servers out of connection

Slammer effect : Before and after 30 minutes
What if Slammer had malicious payload?

Used Techniques
Random scanning Code Red, Code Red I
Localized scanning Code Red II Machines in the same network are more likely
to run the same software Multi-vector
Nimda Several methods of spreading

Possible Techniques 1
Hit-list scanning First 10k infection is the hardest Use a list of 10~50k vulnerable machines Several methods to generate the list
Stealthy scan: random scan taking several months Distributed scan: using already compromised hosts DNS search: already known servers such as mail/web
servers Just listening: P2P networks advertise their servers,
previous worms advertised many servers

Possible Techniques 2
Permutation ScanningRandom scan probes same host multiple
timesPermutation of IP addressesWhen an infected host is found, start
from random point in the permutationSelf-coordinated, comprehensive
scanningVery high infection rate

Possible Techniques 3
Warhol Worm Hit-list and permutation scanning combined Start off quickly and high infection rate Simulation shows 99.99% of 300k hosts infected in
less than 15 min. Many other techniques
Topological scanning – use info from the infected machine to spread machines in the same subnet
Flash worm – using high band width with compressed hit-list Stealth worms – web servers to clients, P2P

Dealing with worm threat
Prevention Prevent vulnerability by Secure coding practices Patching software Heterogeneity of network
Treatment Patching after breakout Virus scanning
Containment

Containment
IncomingBlack listSignature based detection Identify scanning characteristics of worms
OutgoingTCP connection thresholdUse worm signature for outbound traffic

Detection – signature based
Attack Signature: A description which represents a particular attack or action
Eg, a classic antivirus signature Vulnerability Signature:
A description of the class of vulnerable systems Eg, “Windows XP, SP2, not patched since 10/1/2004”
A description of how to exploit a particular vulnerability Behavioral Signatures:
A behavior necessary for a class of worms (E.G. Scanning) A behavior common to many implementations (half-open
connections)

Detection – runtime analysis
Mark all the data from unsafe source and derived data to be dirty
Any execution attempts are signaled as possible threat
Generate Self-Certifying Allerts and distribute to peers using overlay – peers only run overlay code so less susceptible to attacks
Each host verifies alert in a VM and if the vulnerability is found, generates filter
Multiple filters to prevent false positive Generic filter – disjunction of multiple specific conditions Specific filter – more stringent conditions

Thoughts
Detection Polymorphic worms
Obfuscation, encryption False positive
Attacker generates suspicious traffic with byte strings that are common in normal traffic
Signature generation time Dynamic taint analysis – expensive or low
coverage and resource-hungry

Thoughts
Distribution/deploymentPervasive P2P collaboration
E2E detection and distributionSecure communication
Overlay?
Intrusion detection systems? Honeypots, honeyfarms?

Remarks
Future worms will be more aggressive Need automatic detection mechanisms
No global answer, need to apply all the techniques
Network level detections have limitations because of limited/no knowledge of software vulnerabilities
E2E detection, secure P2P distribution of worm information