Utility Software m3
-
Upload
kalai-shan -
Category
Documents
-
view
218 -
download
0
Transcript of Utility Software m3
-
7/28/2019 Utility Software m3
1/10
Utility
software is system
software designed to help
analyze, configure,optimize or maintain a computer. A single piece
of utility software is usually called a utility or
tool.
Utility software usually focuses on how the
computer infrastructure (including the computerhardware, operating system, application
software and data storage) operates. Due to this
focus, utilities are often rather technical and
targeted at people with an advanced level of
computer knowledge in contrast to application
software, which allows users to do things likecreating text documents, playing games,
listening to music or viewing websites.
UTILITY SOFTWARE
http://en.wikipedia.org/wiki/System_softwarehttp://en.wikipedia.org/wiki/System_softwarehttp://en.wikipedia.org/wiki/Computer_hardwarehttp://en.wikipedia.org/wiki/Computer_hardwarehttp://en.wikipedia.org/wiki/Operating_systemhttp://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Data_%28computing%29http://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Application_softwarehttp://www.google.com.my/imgres?q=komputer+kartun&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=_SgrhnHNodoHuM:&imgrefurl=http://media.photobucket.com/image/kartun/sabrigm/nerd_computer.gif?o=3&docid=xG_vFKYpdQL5UM&imgurl=http://i298.photobucket.com/albums/mm271/sabrigm/nerd_computer.gif&w=245&h=266&ei=d-gKUObYNMbqrAfXkoHICA&zoom=1&iact=hc&vpx=690&vpy=108&dur=1781&hovh=212&hovw=196&tx=111&ty=131&sig=116660631131696221296&page=1&tbnh=122&tbnw=112&start=0&ndsp=12&ved=1t:429,r:4,s:0,i:81http://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Data_%28computing%29http://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Application_softwarehttp://en.wikipedia.org/wiki/Operating_systemhttp://en.wikipedia.org/wiki/Computer_hardwarehttp://en.wikipedia.org/wiki/Computer_hardwarehttp://en.wikipedia.org/wiki/System_softwarehttp://en.wikipedia.org/wiki/System_softwarehttp://www.google.com.my/imgres?q=UTILITY+SOFTWARE&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=HSGHrgEL4y15qM:&imgrefurl=http://www.life123.com/technology/computer-software/utility-software/a-guide-to-utility-software.shtml&docid=W5VfQYo3S6zETM&imgurl=http://sp.life123.com/bm.pix/spreadsheet-software-2.s600x600.jpg&w=419&h=286&ei=GukKUKX-EIe3rAf_o4HJCA&zoom=1&iact=hc&vpx=626&vpy=135&dur=3027&hovh=185&hovw=272&tx=148&ty=130&sig=116660631131696221296&page=1&tbnh=101&tbnw=136&start=0&ndsp=12&ved=1t:429,r:4,s:0,i:121http://www.google.com.my/imgres?q=komputer+kartun&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=_SgrhnHNodoHuM:&imgrefurl=http://media.photobucket.com/image/kartun/sabrigm/nerd_computer.gif?o=3&docid=xG_vFKYpdQL5UM&imgurl=http://i298.photobucket.com/albums/mm271/sabrigm/nerd_computer.gif&w=245&h=266&ei=d-gKUObYNMbqrAfXkoHICA&zoom=1&iact=hc&vpx=690&vpy=108&dur=1781&hovh=212&hovw=196&tx=111&ty=131&sig=116660631131696221296&page=1&tbnh=122&tbnw=112&start=0&ndsp=12&ved=1t:429,r:4,s:0,i:81http://www.google.com.my/imgres?q=UTILITY+SOFTWARE&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=HSGHrgEL4y15qM:&imgrefurl=http://www.life123.com/technology/computer-software/utility-software/a-guide-to-utility-software.shtml&docid=W5VfQYo3S6zETM&imgurl=http://sp.life123.com/bm.pix/spreadsheet-software-2.s600x600.jpg&w=419&h=286&ei=GukKUKX-EIe3rAf_o4HJCA&zoom=1&iact=hc&vpx=626&vpy=135&dur=3027&hovh=185&hovw=272&tx=148&ty=130&sig=116660631131696221296&page=1&tbnh=101&tbnw=136&start=0&ndsp=12&ved=1t:429,r:4,s:0,i:121http://www.google.com.my/imgres?q=komputer+kartun&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=_SgrhnHNodoHuM:&imgrefurl=http://media.photobucket.com/image/kartun/sabrigm/nerd_computer.gif?o=3&docid=xG_vFKYpdQL5UM&imgurl=http://i298.photobucket.com/albums/mm271/sabrigm/nerd_computer.gif&w=245&h=266&ei=d-gKUObYNMbqrAfXkoHICA&zoom=1&iact=hc&vpx=690&vpy=108&dur=1781&hovh=212&hovw=196&tx=111&ty=131&sig=116660631131696221296&page=1&tbnh=122&tbnw=112&start=0&ndsp=12&ved=1t:429,r:4,s:0,i:81 -
7/28/2019 Utility Software m3
2/10
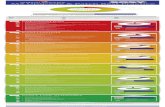
Utility Function
Anti-virus utilities scan forcomputer viruses.
Backup utilities can make a
copy of allinformation stored on
a disk, and restore
either the entire disk
(e.g. in an event of
disk failure) or
selected files (e.g. in
an event of accidental
deletion).
Data compression utilities output a
shorter stream or a
smaller file whenprovided with a
stream or file.
-
7/28/2019 Utility Software m3
3/10
Disk checkers can scan operating
hard drive
Disk cleaners
can find files that
are unnecessary to
computer
operation, or take
up considerableamounts of space.
Disk cleaner helps
the user to decide
what to delete
when their harddisk is full.
http://www.google.com.my/imgres?q=disk+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=B4SapZ8oio2JhM:&imgrefurl=http://miqdadcyber.blogspot.com/2011/08/melakukan-perawatan-pc.html&docid=fp-i27KHRkcphM&imgurl=http://2.bp.blogspot.com/-OdwhkBosqtY/TlndkKSlQcI/AAAAAAAAAE4/m2KRR6sfgKk/s1600/disk+cleaner.jpg&w=400&h=300&ei=rMQKUMLuMcforQfG2O3ICA&zoom=1&iact=hc&vpx=257&vpy=124&dur=6269&hovh=194&hovw=259&tx=192&ty=116&sig=116660631131696221296&page=2&tbnh=126&tbnw=138&start=11&ndsp=15&ved=1t:429,r:6,s:11,i:125http://www.google.com.my/imgres?q=disk+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=HOa1vE_WYgqFhM:&imgrefurl=http://www.viprasys.org/vb/f171/wise-disk-cleaner-build-479-v7-22-portable-3-mb-sendspace-1100643/&docid=TVK2Bg1EsPFH4M&imgurl=http://viprasys.org/xfs/image/direct/1UjO49xJ9D/wise-disk-cleaner.jpg&w=450&h=312&ei=rMQKUMLuMcforQfG2O3ICA&zoom=1&iact=hc&vpx=641&vpy=79&dur=976&hovh=187&hovw=270&tx=150&ty=106&sig=116660631131696221296&page=3&tbnh=119&tbnw=172&start=26&ndsp=15&ved=1t:429,r:13,s:26,i:196http://www.google.com.my/imgres?q=disk+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=B4SapZ8oio2JhM:&imgrefurl=http://miqdadcyber.blogspot.com/2011/08/melakukan-perawatan-pc.html&docid=fp-i27KHRkcphM&imgurl=http://2.bp.blogspot.com/-OdwhkBosqtY/TlndkKSlQcI/AAAAAAAAAE4/m2KRR6sfgKk/s1600/disk+cleaner.jpg&w=400&h=300&ei=rMQKUMLuMcforQfG2O3ICA&zoom=1&iact=hc&vpx=257&vpy=124&dur=6269&hovh=194&hovw=259&tx=192&ty=116&sig=116660631131696221296&page=2&tbnh=126&tbnw=138&start=11&ndsp=15&ved=1t:429,r:6,s:11,i:125http://www.google.com.my/imgres?q=disk+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=HOa1vE_WYgqFhM:&imgrefurl=http://www.viprasys.org/vb/f171/wise-disk-cleaner-build-479-v7-22-portable-3-mb-sendspace-1100643/&docid=TVK2Bg1EsPFH4M&imgurl=http://viprasys.org/xfs/image/direct/1UjO49xJ9D/wise-disk-cleaner.jpg&w=450&h=312&ei=rMQKUMLuMcforQfG2O3ICA&zoom=1&iact=hc&vpx=641&vpy=79&dur=976&hovh=187&hovw=270&tx=150&ty=106&sig=116660631131696221296&page=3&tbnh=119&tbnw=172&start=26&ndsp=15&ved=1t:429,r:13,s:26,i:196http://www.google.com.my/imgres?q=disk+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=B4SapZ8oio2JhM:&imgrefurl=http://miqdadcyber.blogspot.com/2011/08/melakukan-perawatan-pc.html&docid=fp-i27KHRkcphM&imgurl=http://2.bp.blogspot.com/-OdwhkBosqtY/TlndkKSlQcI/AAAAAAAAAE4/m2KRR6sfgKk/s1600/disk+cleaner.jpg&w=400&h=300&ei=rMQKUMLuMcforQfG2O3ICA&zoom=1&iact=hc&vpx=257&vpy=124&dur=6269&hovh=194&hovw=259&tx=192&ty=116&sig=116660631131696221296&page=2&tbnh=126&tbnw=138&start=11&ndsp=15&ved=1t:429,r:6,s:11,i:125http://www.google.com.my/imgres?q=disk+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=HOa1vE_WYgqFhM:&imgrefurl=http://www.viprasys.org/vb/f171/wise-disk-cleaner-build-479-v7-22-portable-3-mb-sendspace-1100643/&docid=TVK2Bg1EsPFH4M&imgurl=http://viprasys.org/xfs/image/direct/1UjO49xJ9D/wise-disk-cleaner.jpg&w=450&h=312&ei=rMQKUMLuMcforQfG2O3ICA&zoom=1&iact=hc&vpx=641&vpy=79&dur=976&hovh=187&hovw=270&tx=150&ty=106&sig=116660631131696221296&page=3&tbnh=119&tbnw=172&start=26&ndsp=15&ved=1t:429,r:13,s:26,i:196 -
7/28/2019 Utility Software m3
4/10
Disk defragmenters can detect computer
files whose contents
are broken across
several locations on
the hard disk, and
move the fragments to
one location toincrease efficiency.
Disk partitions can divide an individual
drive into multiple
logical drives, each
with its own filesystem which can be
mounted by the
operating system and
treated as an individual
drive.
http://www.google.com.my/imgres?q=disk+partitions&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=DK1JLkAMheGBbM:&imgrefurl=http://www.blogrollcenter.com/news/hard-disk-partitioning-guide/&docid=2pFY4b2huYaHVM&imgurl=http://www.blogrollcenter.com/news/gallery/technology-internet/hard_disk_partitioning_guide_1.jpg&w=618&h=439&ei=tccKUILBAo-zrAfGyYHMCA&zoom=1&iact=hc&vpx=82&vpy=130&dur=654&hovh=189&hovw=266&tx=177&ty=136&sig=116660631131696221296&page=1&tbnh=109&tbnw=153&start=0&ndsp=11&ved=1t:429,r:0,s:0,i:69http://www.google.com.my/imgres?q=disk+defragmenter&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=VfTO4CJOc5PLyM:&imgrefurl=http://www.ylcomputing.com/content/view/342/150/&docid=u-eqVGqq8UqLUM&imgurl=http://www.ylcomputing.com/images/free-defrag/free-defrag.gif&w=470&h=369&ei=fcYKUJfmJ5DJrQet0dHICA&zoom=1&iact=hc&vpx=260&vpy=2&dur=2202&hovh=199&hovw=253&tx=144&ty=96&sig=116660631131696221296&page=3&tbnh=120&tbnw=153&start=27&ndsp=15&ved=1t:429,r:1,s:27,i:227http://www.google.com.my/imgres?q=disk+partitions&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=DK1JLkAMheGBbM:&imgrefurl=http://www.blogrollcenter.com/news/hard-disk-partitioning-guide/&docid=2pFY4b2huYaHVM&imgurl=http://www.blogrollcenter.com/news/gallery/technology-internet/hard_disk_partitioning_guide_1.jpg&w=618&h=439&ei=tccKUILBAo-zrAfGyYHMCA&zoom=1&iact=hc&vpx=82&vpy=130&dur=654&hovh=189&hovw=266&tx=177&ty=136&sig=116660631131696221296&page=1&tbnh=109&tbnw=153&start=0&ndsp=11&ved=1t:429,r:0,s:0,i:69http://www.google.com.my/imgres?q=disk+defragmenter&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=VfTO4CJOc5PLyM:&imgrefurl=http://www.ylcomputing.com/content/view/342/150/&docid=u-eqVGqq8UqLUM&imgurl=http://www.ylcomputing.com/images/free-defrag/free-defrag.gif&w=470&h=369&ei=fcYKUJfmJ5DJrQet0dHICA&zoom=1&iact=hc&vpx=260&vpy=2&dur=2202&hovh=199&hovw=253&tx=144&ty=96&sig=116660631131696221296&page=3&tbnh=120&tbnw=153&start=27&ndsp=15&ved=1t:429,r:1,s:27,i:227http://www.google.com.my/imgres?q=disk+partitions&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=DK1JLkAMheGBbM:&imgrefurl=http://www.blogrollcenter.com/news/hard-disk-partitioning-guide/&docid=2pFY4b2huYaHVM&imgurl=http://www.blogrollcenter.com/news/gallery/technology-internet/hard_disk_partitioning_guide_1.jpg&w=618&h=439&ei=tccKUILBAo-zrAfGyYHMCA&zoom=1&iact=hc&vpx=82&vpy=130&dur=654&hovh=189&hovw=266&tx=177&ty=136&sig=116660631131696221296&page=1&tbnh=109&tbnw=153&start=0&ndsp=11&ved=1t:429,r:0,s:0,i:69http://www.google.com.my/imgres?q=disk+defragmenter&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=VfTO4CJOc5PLyM:&imgrefurl=http://www.ylcomputing.com/content/view/342/150/&docid=u-eqVGqq8UqLUM&imgurl=http://www.ylcomputing.com/images/free-defrag/free-defrag.gif&w=470&h=369&ei=fcYKUJfmJ5DJrQet0dHICA&zoom=1&iact=hc&vpx=260&vpy=2&dur=2202&hovh=199&hovw=253&tx=144&ty=96&sig=116660631131696221296&page=3&tbnh=120&tbnw=153&start=27&ndsp=15&ved=1t:429,r:1,s:27,i:227 -
7/28/2019 Utility Software m3
5/10
Disk space analyzers for the visualization of
disk space usage bygetting the size for
each folder (including
sub folders) & files in
folder or drive.
showing the
distribution of the
used space.
http://www.google.com.my/imgres?q=disk+space+analyzers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=PBoI5_KGycUOvM:&imgrefurl=http://www.sadcatsoft.com/df/main.php&docid=QjvOXB-aGESKuM&imgurl=http://www.sadcatsoft.com/df/sm_scr1_960.jpg&w=480&h=300&ei=bcgKUKWGO4i4rAfs0d3ICA&zoom=1&iact=hc&vpx=697&vpy=143&dur=1606&hovh=177&hovw=284&tx=163&ty=114&sig=116660631131696221296&page=6&tbnh=105&tbnw=168&start=70&ndsp=15&ved=1t:429,r:14,s:70,i:343 -
7/28/2019 Utility Software m3
6/10
File managers
provide a convenient
method of performing
routine data
management tasks,
such as deleting,
renaming, cataloging,
uncataloging, moving,
copying, merging,
generating andmodifying data sets.
Cryptographic utilities encrypt and
decrypt streams and
files.
http://www.google.com.my/imgres?q=Cryptographic&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=lPza2MjMUTHW2M:&imgrefurl=http://www.riskmanagementmonitor.com/cryptographic-lock-baffles-the-fbi/&docid=M-__R5cAXEIG6M&imgurl=http://www.riskmanagementmonitor.com/wp-content/uploads/2010/06/encryption.jpg&w=500&h=375&ei=e9wKUKThB4XtrAfYg9TICA&zoom=1&iact=hc&vpx=722&vpy=2&dur=428&hovh=194&hovw=259&tx=151&ty=111&sig=116660631131696221296&page=3&tbnh=127&tbnw=198&start=28&ndsp=15&ved=1t:429,r:4,s:28,i:173http://www.google.com.my/imgres?q=Cryptographic&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=_x3f2SVM69XvXM:&imgrefurl=http://www.brothersoft.com/dekart-rsa-cryptographic-provider-275733.html&docid=sJZzTv4EMZwNQM&imgurl=http://img.brothersoft.com/screenshots/softimage/d/dekart_rsa_cryptographic_provider-275733-1250750020.jpeg&w=464&h=438&ei=e9wKUKThB4XtrAfYg9TICA&zoom=1&iact=hc&vpx=300&vpy=101&dur=4125&hovh=218&hovw=231&tx=73&ty=118&sig=116660631131696221296&page=2&tbnh=130&tbnw=138&start=13&ndsp=15&ved=1t:429,r:6,s:13,i:131http://www.google.com.my/imgres?q=Cryptographic&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=lPza2MjMUTHW2M:&imgrefurl=http://www.riskmanagementmonitor.com/cryptographic-lock-baffles-the-fbi/&docid=M-__R5cAXEIG6M&imgurl=http://www.riskmanagementmonitor.com/wp-content/uploads/2010/06/encryption.jpg&w=500&h=375&ei=e9wKUKThB4XtrAfYg9TICA&zoom=1&iact=hc&vpx=722&vpy=2&dur=428&hovh=194&hovw=259&tx=151&ty=111&sig=116660631131696221296&page=3&tbnh=127&tbnw=198&start=28&ndsp=15&ved=1t:429,r:4,s:28,i:173http://www.google.com.my/imgres?q=Cryptographic&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=_x3f2SVM69XvXM:&imgrefurl=http://www.brothersoft.com/dekart-rsa-cryptographic-provider-275733.html&docid=sJZzTv4EMZwNQM&imgurl=http://img.brothersoft.com/screenshots/softimage/d/dekart_rsa_cryptographic_provider-275733-1250750020.jpeg&w=464&h=438&ei=e9wKUKThB4XtrAfYg9TICA&zoom=1&iact=hc&vpx=300&vpy=101&dur=4125&hovh=218&hovw=231&tx=73&ty=118&sig=116660631131696221296&page=2&tbnh=130&tbnw=138&start=13&ndsp=15&ved=1t:429,r:6,s:13,i:131http://www.google.com.my/imgres?q=Cryptographic&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=lPza2MjMUTHW2M:&imgrefurl=http://www.riskmanagementmonitor.com/cryptographic-lock-baffles-the-fbi/&docid=M-__R5cAXEIG6M&imgurl=http://www.riskmanagementmonitor.com/wp-content/uploads/2010/06/encryption.jpg&w=500&h=375&ei=e9wKUKThB4XtrAfYg9TICA&zoom=1&iact=hc&vpx=722&vpy=2&dur=428&hovh=194&hovw=259&tx=151&ty=111&sig=116660631131696221296&page=3&tbnh=127&tbnw=198&start=28&ndsp=15&ved=1t:429,r:4,s:28,i:173http://www.google.com.my/imgres?q=Cryptographic&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=_x3f2SVM69XvXM:&imgrefurl=http://www.brothersoft.com/dekart-rsa-cryptographic-provider-275733.html&docid=sJZzTv4EMZwNQM&imgurl=http://img.brothersoft.com/screenshots/softimage/d/dekart_rsa_cryptographic_provider-275733-1250750020.jpeg&w=464&h=438&ei=e9wKUKThB4XtrAfYg9TICA&zoom=1&iact=hc&vpx=300&vpy=101&dur=4125&hovh=218&hovw=231&tx=73&ty=118&sig=116660631131696221296&page=2&tbnh=130&tbnw=138&start=13&ndsp=15&ved=1t:429,r:6,s:13,i:131 -
7/28/2019 Utility Software m3
7/10
Hex editors directly modify the text
or data of a file. These
files could be data oran actual program.
Memory tester check for memory
failures.
Network utilities analyze the
computer's
network
connectivity,
configure
network
http://www.google.com.my/imgres?q=hex+editor&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=GTdlXOMKqKo2yM:&imgrefurl=http://www.sb-software.com/hexeditor/about.html&docid=I20lEAyNub2yTM&imgurl=http://www.sb-software.com/hexeditor/hexshot1.jpg&w=610&h=502&ei=bN0KUNzoHI3IrQfa4L3JCA&zoom=1&iact=hc&vpx=504&vpy=116&dur=3315&hovh=204&hovw=248&tx=115&ty=167&sig=116660631131696221296&page=1&tbnh=101&tbnw=123&start=0&ndsp=12&ved=1t:429,r:3,s:0,i:105http://www.google.com.my/imgres?q=memory+tester&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=bg87I9XHi8cKLM:&imgrefurl=http://mikelab.kiev.ua/index_en.php?page=programs/vmt_en&docid=sqLnLrls7cIAIM&imgurl=http://mikelab.kiev.ua/PROGRAMS/IMAGE/vmt.gif&w=640&h=480&ei=Ot4KUN__IcjXrQeA693ICA&zoom=1http://www.google.com.my/imgres?q=hex+editor&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=GTdlXOMKqKo2yM:&imgrefurl=http://www.sb-software.com/hexeditor/about.html&docid=I20lEAyNub2yTM&imgurl=http://www.sb-software.com/hexeditor/hexshot1.jpg&w=610&h=502&ei=bN0KUNzoHI3IrQfa4L3JCA&zoom=1&iact=hc&vpx=504&vpy=116&dur=3315&hovh=204&hovw=248&tx=115&ty=167&sig=116660631131696221296&page=1&tbnh=101&tbnw=123&start=0&ndsp=12&ved=1t:429,r:3,s:0,i:105http://www.google.com.my/imgres?q=memory+tester&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=bg87I9XHi8cKLM:&imgrefurl=http://mikelab.kiev.ua/index_en.php?page=programs/vmt_en&docid=sqLnLrls7cIAIM&imgurl=http://mikelab.kiev.ua/PROGRAMS/IMAGE/vmt.gif&w=640&h=480&ei=Ot4KUN__IcjXrQeA693ICA&zoom=1 -
7/28/2019 Utility Software m3
8/10
settings, check
data transfer
or log events.
Registry cleaners clean and
optimize the
Windows
registry by
removing
old registry
keys that are
no longer in
use.
http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=gpzb8JSSUnOejM:&imgrefurl=http://reviewsnbonus.com/uncategorized/registry-cleaner-review/&docid=p7sS89tzr3TATM&imgurl=http://reviewsnbonus.com/wp-content/uploads/2011/01/windows-registry-cleaner.jpg&w=353&h=352&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=264&vpy=2&dur=1152&hovh=224&hovw=225&tx=154&ty=30&sig=116660631131696221296&page=1&tbnh=120&tbnw=120&start=0&ndsp=10&ved=1t:429,r:6,s:0,i:88http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=w3zqy9R6DuLyLM:&imgrefurl=http://www.paretologic.com/products/regcure/&docid=xRmjWKHlkIpWLM&imgurl=http://www.paretologic.com/images/regcure_manage_startup.jpg&w=490&h=377&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=725&vpy=123&dur=5934&hovh=197&hovw=256&tx=173&ty=118&sig=116660631131696221296&page=1&tbnh=116&tbnw=151&start=0&ndsp=10&ved=1t:429,r:4,s:0,i:81http://www.google.com.my/imgres?q=network&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=4hZUASV120tJKM:&imgrefurl=http://www.nwc.com.my/main/index.php/products/5-wired-wireless-networking&docid=j3-7rbaCfwj8WM&imgurl=http://www.nwc.com.my/main/images/wirless-networks-in-a-regulated-environment.jpg&w=400&h=300&ei=hd8KULOHN8zorQegxtTICA&zoom=1&iact=hc&vpx=722&vpy=36&dur=5308&hovh=194&hovw=259&tx=149&ty=141&sig=116660631131696221296&page=5&tbnh=128&tbnw=172&start=58&ndsp=15&ved=1t:429,r:4,s:58,i:350http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=gpzb8JSSUnOejM:&imgrefurl=http://reviewsnbonus.com/uncategorized/registry-cleaner-review/&docid=p7sS89tzr3TATM&imgurl=http://reviewsnbonus.com/wp-content/uploads/2011/01/windows-registry-cleaner.jpg&w=353&h=352&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=264&vpy=2&dur=1152&hovh=224&hovw=225&tx=154&ty=30&sig=116660631131696221296&page=1&tbnh=120&tbnw=120&start=0&ndsp=10&ved=1t:429,r:6,s:0,i:88http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=w3zqy9R6DuLyLM:&imgrefurl=http://www.paretologic.com/products/regcure/&docid=xRmjWKHlkIpWLM&imgurl=http://www.paretologic.com/images/regcure_manage_startup.jpg&w=490&h=377&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=725&vpy=123&dur=5934&hovh=197&hovw=256&tx=173&ty=118&sig=116660631131696221296&page=1&tbnh=116&tbnw=151&start=0&ndsp=10&ved=1t:429,r:4,s:0,i:81http://www.google.com.my/imgres?q=network&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=4hZUASV120tJKM:&imgrefurl=http://www.nwc.com.my/main/index.php/products/5-wired-wireless-networking&docid=j3-7rbaCfwj8WM&imgurl=http://www.nwc.com.my/main/images/wirless-networks-in-a-regulated-environment.jpg&w=400&h=300&ei=hd8KULOHN8zorQegxtTICA&zoom=1&iact=hc&vpx=722&vpy=36&dur=5308&hovh=194&hovw=259&tx=149&ty=141&sig=116660631131696221296&page=5&tbnh=128&tbnw=172&start=58&ndsp=15&ved=1t:429,r:4,s:58,i:350http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=gpzb8JSSUnOejM:&imgrefurl=http://reviewsnbonus.com/uncategorized/registry-cleaner-review/&docid=p7sS89tzr3TATM&imgurl=http://reviewsnbonus.com/wp-content/uploads/2011/01/windows-registry-cleaner.jpg&w=353&h=352&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=264&vpy=2&dur=1152&hovh=224&hovw=225&tx=154&ty=30&sig=116660631131696221296&page=1&tbnh=120&tbnw=120&start=0&ndsp=10&ved=1t:429,r:6,s:0,i:88http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=w3zqy9R6DuLyLM:&imgrefurl=http://www.paretologic.com/products/regcure/&docid=xRmjWKHlkIpWLM&imgurl=http://www.paretologic.com/images/regcure_manage_startup.jpg&w=490&h=377&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=725&vpy=123&dur=5934&hovh=197&hovw=256&tx=173&ty=118&sig=116660631131696221296&page=1&tbnh=116&tbnw=151&start=0&ndsp=10&ved=1t:429,r:4,s:0,i:81http://www.google.com.my/imgres?q=network&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=4hZUASV120tJKM:&imgrefurl=http://www.nwc.com.my/main/index.php/products/5-wired-wireless-networking&docid=j3-7rbaCfwj8WM&imgurl=http://www.nwc.com.my/main/images/wirless-networks-in-a-regulated-environment.jpg&w=400&h=300&ei=hd8KULOHN8zorQegxtTICA&zoom=1&iact=hc&vpx=722&vpy=36&dur=5308&hovh=194&hovw=259&tx=149&ty=141&sig=116660631131696221296&page=5&tbnh=128&tbnw=172&start=58&ndsp=15&ved=1t:429,r:4,s:58,i:350http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=gpzb8JSSUnOejM:&imgrefurl=http://reviewsnbonus.com/uncategorized/registry-cleaner-review/&docid=p7sS89tzr3TATM&imgurl=http://reviewsnbonus.com/wp-content/uploads/2011/01/windows-registry-cleaner.jpg&w=353&h=352&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=264&vpy=2&dur=1152&hovh=224&hovw=225&tx=154&ty=30&sig=116660631131696221296&page=1&tbnh=120&tbnw=120&start=0&ndsp=10&ved=1t:429,r:6,s:0,i:88http://www.google.com.my/imgres?q=Registry+cleaners&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=w3zqy9R6DuLyLM:&imgrefurl=http://www.paretologic.com/products/regcure/&docid=xRmjWKHlkIpWLM&imgurl=http://www.paretologic.com/images/regcure_manage_startup.jpg&w=490&h=377&ei=kOAKUOnAMoTirAeeyOXICA&zoom=1&iact=hc&vpx=725&vpy=123&dur=5934&hovh=197&hovw=256&tx=173&ty=118&sig=116660631131696221296&page=1&tbnh=116&tbnw=151&start=0&ndsp=10&ved=1t:429,r:4,s:0,i:81http://www.google.com.my/imgres?q=network&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=4hZUASV120tJKM:&imgrefurl=http://www.nwc.com.my/main/index.php/products/5-wired-wireless-networking&docid=j3-7rbaCfwj8WM&imgurl=http://www.nwc.com.my/main/images/wirless-networks-in-a-regulated-environment.jpg&w=400&h=300&ei=hd8KULOHN8zorQegxtTICA&zoom=1&iact=hc&vpx=722&vpy=36&dur=5308&hovh=194&hovw=259&tx=149&ty=141&sig=116660631131696221296&page=5&tbnh=128&tbnw=172&start=58&ndsp=15&ved=1t:429,r:4,s:58,i:350 -
7/28/2019 Utility Software m3
9/10
Screensavers desired to prevent
phosphor burn-in on CRT
and plasma computer
monitors by blanking thescreen or filling it with
moving images or patterns
when the computer is not
in use. Contemporary
screensavers are used
primarily for
entertainment or security.
System monitors for monitoring resources
and performance in a
computer system.
http://www.google.com.my/imgres?q=%E2%80%A2Screensavers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=e1u4r9Jz0Q3BiM:&imgrefurl=http://www.technobeta.com/?p=180&docid=_F6TJ0pewAPkJM&imgurl=http://www.technobeta.com/wp-content/uploads/2007/03/vista-screensaver-ribbons.jpg&w=1024&h=768&ei=FeEKUK3AJ83MrQeC-tDICA&zoom=1&iact=hc&vpx=89&vpy=121&dur=708&hovh=194&hovw=259&tx=166&ty=84&sig=116660631131696221296&page=3&tbnh=127&tbnw=161&start=27&ndsp=15&ved=1t:429,r:0,s:27,i:224http://www.google.com.my/imgres?q=%E2%80%A2Screensavers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=D5k6QN-x7EwHJM:&imgrefurl=http://www.cool-screensavers.com/3dxmas.html&docid=ayv1gv458hyTjM&imgurl=http://www.cool-screensavers.com/skins/3d/christmas_large.jpg&w=400&h=300&ei=FeEKUK3AJ83MrQeC-tDICA&zoom=1&iact=hc&vpx=261&vpy=18&dur=1946&hovh=194&hovw=259&tx=151&ty=132&sig=116660631131696221296&page=2&tbnh=127&tbnw=160&start=12&ndsp=15&ved=1t:429,r:11,s:12,i:210http://www.google.com.my/imgres?q=%E2%80%A2Screensavers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=e1u4r9Jz0Q3BiM:&imgrefurl=http://www.technobeta.com/?p=180&docid=_F6TJ0pewAPkJM&imgurl=http://www.technobeta.com/wp-content/uploads/2007/03/vista-screensaver-ribbons.jpg&w=1024&h=768&ei=FeEKUK3AJ83MrQeC-tDICA&zoom=1&iact=hc&vpx=89&vpy=121&dur=708&hovh=194&hovw=259&tx=166&ty=84&sig=116660631131696221296&page=3&tbnh=127&tbnw=161&start=27&ndsp=15&ved=1t:429,r:0,s:27,i:224http://www.google.com.my/imgres?q=%E2%80%A2Screensavers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=D5k6QN-x7EwHJM:&imgrefurl=http://www.cool-screensavers.com/3dxmas.html&docid=ayv1gv458hyTjM&imgurl=http://www.cool-screensavers.com/skins/3d/christmas_large.jpg&w=400&h=300&ei=FeEKUK3AJ83MrQeC-tDICA&zoom=1&iact=hc&vpx=261&vpy=18&dur=1946&hovh=194&hovw=259&tx=151&ty=132&sig=116660631131696221296&page=2&tbnh=127&tbnw=160&start=12&ndsp=15&ved=1t:429,r:11,s:12,i:210http://www.google.com.my/imgres?q=%E2%80%A2Screensavers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=e1u4r9Jz0Q3BiM:&imgrefurl=http://www.technobeta.com/?p=180&docid=_F6TJ0pewAPkJM&imgurl=http://www.technobeta.com/wp-content/uploads/2007/03/vista-screensaver-ribbons.jpg&w=1024&h=768&ei=FeEKUK3AJ83MrQeC-tDICA&zoom=1&iact=hc&vpx=89&vpy=121&dur=708&hovh=194&hovw=259&tx=166&ty=84&sig=116660631131696221296&page=3&tbnh=127&tbnw=161&start=27&ndsp=15&ved=1t:429,r:0,s:27,i:224http://www.google.com.my/imgres?q=%E2%80%A2Screensavers&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=D5k6QN-x7EwHJM:&imgrefurl=http://www.cool-screensavers.com/3dxmas.html&docid=ayv1gv458hyTjM&imgurl=http://www.cool-screensavers.com/skins/3d/christmas_large.jpg&w=400&h=300&ei=FeEKUK3AJ83MrQeC-tDICA&zoom=1&iact=hc&vpx=261&vpy=18&dur=1946&hovh=194&hovw=259&tx=151&ty=132&sig=116660631131696221296&page=2&tbnh=127&tbnw=160&start=12&ndsp=15&ved=1t:429,r:11,s:12,i:210 -
7/28/2019 Utility Software m3
10/10
DISEDIAKAN OLEH,THIPHANATH A/L SELVARAJOO
NEEROSHA A/P GOPAL
KRISHNAN
PPISMP BT (SK) 2012
System profilers provide detailed
information about the
software installed and
hardware attached to thecomputer.
http://www.google.com.my/imgres?q=system+profiler&um=1&hl=en&biw=1024&bih=450&tbm=isch&tbnid=4VhgWm2sUS28gM:&imgrefurl=http://echoone.com/bugreports/asp.html&docid=WERdeQvEZL9rRM&imgurl=http://echoone.com/bugreports/images/aspshot.jpg&w=600&h=400&ei=GeUKUOSqH4rrrQfFlNnICA&zoom=1&iact=hc&vpx=576&vpy=91&dur=7028&hovh=183&hovw=275&tx=144&ty=79&sig=116660631131696221296&page=1&tbnh=103&tbnw=154&start=0&ndsp=10&ved=1t:429,r:8,s:0,i:94