Topic 3 – Network Layer and WAN Introduction Forwarding and Routing Network service models Virtual...
-
Upload
cameron-daniels -
Category
Documents
-
view
222 -
download
0
Transcript of Topic 3 – Network Layer and WAN Introduction Forwarding and Routing Network service models Virtual...

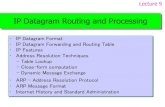
Topic 3 – Network Layer and WAN
•Introduction•Forwarding and Routing•Network service models•Virtual circuit networks•Datagram networks•Router architecture and performance•IPv4•IPv4 addressing•DHCP•NAT•ICMP

Learning Outcomes• Clear understanding of the role of the network layer
in achieving source to destination delivery.• Appreciate the differences between datagram and
virtual circuit packet switching.• The distinction between forwarding and routing.• The basic semantics and syntax of IPv4.• Able to fragment according to the IPv4 protocol.• Good working knowledge of the IPv4 address
formats and structure.• Understand the role of DHCP and its basic
operation • Understand the role of NAT and its basic operation.

Introduction• Delivers transport segments from sending to receiving host .
• On sending side encapsulates segments into datagrams.
• On receiving side, delivers segments to transport layer.
• Network layer protocols in every host, router.
• Router examines header fields in all IP datagrams passing through.
See next slide for schematic
application
transportnetworkdata linkphysical
application
transportnetworkdata linkphysical
networkdata linkphysical network
data linkphysical
networkdata linkphysical
networkdata linkphysical
networkdata linkphysical
networkdata linkphysical
networkdata linkphysical
networkdata linkphysical
networkdata linkphysical
networkdata linkphysicalnetwork
data linkphysical

Datagram sent by H1 to H2. The diagram show the networking layers in action.
Network Layers

Forwarding and Routing
• Forwarding: Transfer packets from router’s input to appropriate router output.
• Routing: Determine route taken by packets from source to destination.
• Routing algorithms/protocols: Methods enable efficient routing for a given set of conditions.

Interplay between routing and forwarding
Datagram arriving at router
1
23
0111
value in arrivingpacket’s header
routing algorithm
local forwarding tableheader value output link
0100010101111001
3221

Network Service models
What service model for transporting datagrams from sender to receiver should be followed?
Possible requirements for individual datagrams:• Guaranteed delivery.• Guaranteed delivery with less than 40 ms. delay.For the flow of datagrams:• In-order datagram delivery• Guaranteed minimum bandwidth to flow• Restrictions on changes in inter-packet spacing
The next slide shows the service model taken by the two major forms of packet switching.

NetworkArchitecture
Internet
ATM
ATM
ATM
ATM
ServiceModel
best effort
CBR
VBR
ABR
UBR
Bandwidth
none
constantrateguaranteedrateguaranteed minimumnone
Loss
no
yes
yes
no
no
Order
no
yes
yes
yes
yes
Timing
no
yes
yes
no
no
Congestionfeedback
no (inferredvia loss)N/A - nocongestionN/A - nocongestionyes
no
Guarantees ?
Actual Network layer service models:

Virtual circuit and Datagram networks
Network layer connection and connection-less service.
• Datagram network provides a network-layer connectionless service
• VC network provides a network-layer connection service - analogous to the transport-layer services’ but:

Virtual circuit networks“Source-to-destination path behaves much like a
telephone circuit”
• Call setup, teardown for each call before data can flow
• Each packet carries VC identifier (not destination host address)
• Every switch on source-destination path maintains “state” for each passing connection
• Link and switch resources (bandwidth, buffers) may be allocated to VC (dedicated resources offer predictable services)

VC implementationA VC consists of:
1. Path from source to destination
2. VC identifiers, one identifier for each link along the path.
3. Entries in forwarding tables of switches along path
• A packet belonging to a VC carries a VC identifier (more like L2 operation than interpreting a L3 destination address)
• VC number can be changed on each link.– New VC number comes from forwarding table

12 22 32
1 23
VC number
Interfacenumber
Incoming interface Incoming VC # Outgoing interface Outgoing VC #
1 12 3 222 63 1 18 3 7 2 171 97 3 87… … … …
Forwarding table :
Switches maintain connection state information!
Forwarding table

Virtual circuits: signaling protocols
• Used to setup, maintain and teardown VC• Used in ATM, frame-relay, X.25• Not used in today’s Internet (datagram)
application
transportnetworkdata linkphysical
application
transportnetworkdata linkphysical
1. Initiate call 2. incoming call
3. Accept call4. Call connected5. Data flow begins 6. Receive data

Datagram Networks• No call setup at network layer• Routers: no state about end-to-end connections
– no network-level concept of “connection”• Packets forwarded using destination host address
– packets between same source-destination pair may take different paths
application
transportnetworkdata linkphysical
application
transportnetworkdata linkphysical
1. Send data 2. Receive data
Network
DestinationSource

Destination Address Range Link Interface
11001000 00010111 00010000 00000000 through 0 11001000 00010111 00010111 11111111
11001000 00010111 00011000 00000000 through 1 11001000 00010111 00011000 11111111
11001000 00010111 00011001 00000000 through 2 11001000 00010111 00011111 11111111
otherwise 3
> 4 billion (232)possible entries
Ex. Forwarding table for IPv4
(Used by the Router to determine the forwarding decision)

Prefix Match Link Interface 11001000 00010111 00010 0 11001000 00010111 00011000 1 11001000 00010111 00011 2 otherwise 3
DA: 11001000 00010111 00011000 10101010
Examples
DA: 11001000 00010111 00010110 10100001 Which interface?
Which interface?
The initial part of some Net prefix’ (Net-ids)are the same with sub-netting so Longest prefix matching

Internet (datagram)• Independent data exchange
among computers– “elastic” service, no strict timing
req. • “Smart” end systems (computers)
– can adapt, perform control, error recovery
– Allows simple network processes - complexity at “edge”
• Many link types – different characteristics– uniform service difficult (QoS)
ATM (VC)• Evolved from telephony• QoS:
– strict timing, reliability requirements
– Offers guaranteed service
• “Dumb” end systems– telephones– complexity inside
network
Datagram or VC network: why?

Two key router functions: • Run routing algorithms/protocol (RIP, OSPF, BGP)• Forwarding datagrams from incoming to outgoing
link
Router Architecture Overview

Decentralized switching: • Given datagram destination, lookup output
port using forwarding table in input port memory (local – detached from central processor)
• Goal: complete input port processing at ‘line speed’
• Queuing: if datagrams arrive faster than forwarding rate into switch fabric
Physical layer:bit-level reception
Data link layer:e.g., Ethernet
Input Port Functions

Three types of switching fabrics
Interconnection network

First generation routers:• Traditional computers with switching under direct control of CPU
•Packet copied to system’s memory• Speed limited by memory bandwidth (2 bus crossings per datagram)
InputPort
OutputPort
Memory
System Bus
Switching via memory

• datagram from input port memory to output port memory via a shared bus
• bus contention: switching speed limited by bus bandwidth
• 32 Gbps bus, Cisco 5600: sufficient speed for access and enterprise routers
Switching Via a Bus

Switching via An Interconnection Network
• overcome bus bandwidth limitations• Banyan networks, other interconnection
nets initially developed to connect processors in multiprocessor
• advanced design: fragmenting datagram into fixed length cells, switch cells through the fabric.
• Cisco 12000: switches 60 Gbps through the interconnection network

• Buffering required when datagrams arrive from fabric faster than the transmission rate
• Scheduling discipline chooses among queued datagrams for transmission
Output Ports

• buffering when arrival rate via switch exceeds output line speed
• queuing (delay) and loss due to output port buffer overflow!
Output port queuing

• Fabric slower than input ports combined -> queuing may occur at input queues
• Head-of-the-Line (HOL) blocking: queued datagram at front of queue prevents others in queue from moving forward
• queuing delay and loss due to input buffer overflow!
Input Port Queuing

forwardingtable
Host, router network layer functions:
Routing protocols•path selection•RIP, OSPF, BGP
IP protocol•addressing conventions•datagram format•packet handling conventions
ICMP protocol•error reporting•router “signaling”
Transport layer: TCP, UDP
Link layer
physical layer
Networklayer
The Internet Network layer

IPv4 introduction• The IP network address is a data structure understood by a network
which uniquely identifies the source and destination within the network. • A unicast/broadcast/multicast IPv4 address is a 32 bit value (4 bytes)
which is allocated to each system in the Internet. • The 32-bit value uniquely identifies this system, and therefore no two
systems may have the same IP address. Some systems have more than one IP address, in which case they may be reached by any of their IP addresses.
• Each IP address consists of two parts, the network part (identifying the network/subnet or LAN broadcast domain, to which the computer is attached) and the host part (which identifies the host within the local network).
• This is a flat allocation technique. Administrators of a specific IP network may freely allocate host addresses within their network, without co-ordination with any other administrators in the Internet. However, they are not allowed to allocate host addresses belonging to a network number which has not been assigned to them.
• IPv4 addresses are normally written in a format known as "dotted decimal notation".
• An IP address may be unicast (for a specific end system), network broadcast (for all systems on a LAN) or multicast (for a group of end systems).

ver length
32 bits
data (variable length,typically a TCP
or UDP segment)
16-bit identifier
header checksum
time tolive
32 bit source IP address
IP protocol versionnumber
header length (bytes)
max numberremaining hops
(decremented at each router)
forfragmentation/reassembly
total datagramlength (bytes)
upper layer protocolto deliver payload to
head.len
type ofservice
“type” of data flgsfragment
offsetupper layer
32 bit destination IP address
Options (if any) E.g. timestamp,record routetaken, specifylist of routers to visit.
how much overhead with TCP?
• 20 bytes of TCP• 20 bytes of IP• = 40 bytes + app
layer overhead
IPv4 datagram format

IPv4 Semantics and syntax I• Version, 4bits (always set to the value 4 in the current version
of IP). • HLEN, IP Header Length, 4bits (The number of 32 -bit words
or 4 Byte or rows forming the header - usually five).• Type of Service, 8bits , now known as Differentiated Service
Code Point (usually set to 0, but may indicate particular Quality of Service needs from the network, the DSCP defines the way routers should queue packets while they are waiting to be forwarded).
• Total Length, 16 bits, size of Datagram (in bytes, this is the combined length of the header and the data)
• Identification (16-bit number which together with the source address uniquely identifies this packet - used during reassembly of fragmented data-grams)
• Flags, 3bits, (a sequence of three flags (one of the 4 bits is unused) used to control whether routers are allowed to fragment a packet (i.e. the Don’t fragment flag, DF flag), and to indicate the parts of a packet to the receiver)

IPv4 Semantics and syntax II
• Fragmentation Offset, 13bits (a byte count from the start of the original sent packet, set by any router which performs IP fragmentation router)
• Time To Live (Number of hops /links which the packet may be routed over, decremented by most routers- used to prevent accidental routing loops)
• Protocol, 8bits (SAP) which indicates the type of transport packet being carried (e.g. 1 = ICMP; 2= IGMP; 6 = TCP; 17= UDP).
• Header Checksum, 16bits, is inserted by the sender and updated whenever the packet header is modified by a router - Used to detect processing errors. Packets with an invalid checksum are discarded by all nodes in an IP network)
• Source Address, 32bits (theIPv4 address of the original sender of the packet)
• Destination Address, 32bits (the IPv4 address of the final destination of the packet)
• Options (not normally used, but, when used, the IP header length will be greater than five 32-bit words to indicate the size of the options field)

• network links have MTU (max.transfer size) - largest possible link-level frame.– different link types,
different MTUs • large IP datagram divided
(“fragmented”) within network– one datagram becomes
several datagrams– “reassembled” only at
final destination– IP header bits used to
identify, order related fragments
fragmentation: in: one large datagramout: 3 smaller datagrams
reassembly
IP Fragmentation & ReassemblyAn example of the operation of one of the IPv4 header fields

ID=x
offset=0
fragflag=0
length=4000
ID777
offset=0
fragflag=1
length=1500
ID777
offset=185
fragflag=1
length=1500
ID777
offset=370
fragflag=0
length=1040
One large datagram becomesthree smaller datagrams
Example• 4000 byte datagram
is sent• MTU = 1500 bytes
is the largest packet that can be forwarded.
1480 bytes in data field
offset = 1480/8
IP Fragmentation and Reassembly example
Original datagram

Example detail

IPv4 address: 32-bit identifier for host and router interface
interface: connection between host/router and physical link– router’s typically have
multiple interfaces– host typically has one
interface– IP addresses
associated with each interface
223.1.1.1
223.1.1.2
223.1.1.3
223.1.1.4 223.1.2.9
223.1.2.2
223.1.2.1
223.1.3.2223.1.3.1
223.1.3.27
223.1.1.1 = 11011111 00000001 00000001 00000001
223 1 11
IP Addressing: introduction
IPv4 address - dotted decimal

Useful stuff about IPv4

Diagram shows internetworking running within and between autonomous systems (networks under a single management regime)
Autonomous System
Larger AS having greater internal networking structure

IPv4 Net prefix and Netmasks• The IPv4 network address is identified as the bit-wise logical
AND of the 32-bit IPv4 address with another 32-bit quantity, the netmask. All systems with the same network number share the same netmask (sometimes called a "subnet mask").
• The netmask has a bit with a logical '1' for each bit that is a part of the network number, and a logical '0' for each bit which is a part of the host number. The netmask may be written in dotted decimal notation.
• e.g. a 24-bit network prefix has a netmask which may be written as 255.255.255.0.
• Hence, the IP address 129.7.1.10 with a netmask of 255.255.255.0 has the network prefix of 129.7.1.0.
• A 24-bit network prefix leaves a host part of 8 bits. That is a network with 254 unique hosts addresses. (Special addresses - 0 is reserved for the network itself, and the all one's host address is reserved for use as the network broadcast address).
• The netmask is often represented by writing the IP address followed by a slash ('/') with the number of bits of the net prefix. The above net prefix can also be represented as /24

Some examples of masking
IP address subnet mask Net
prefix host part
7.7.7.7/8 255.0.0.0 7.0.0.0 7.7.7
139.133.7.10/24 255.255.255.0 139.133.7.0 10
129.5.255.2/16 255.255.0.0 129.5.0.0 255.2
131.108.2.1/30 255.255.255.252 131.108.2.0 1

• IP address: – subnet part (high
order bits)– host part (low order
bits) • What is a subnet ?
– device interfaces with same subnet part of IP address
– can physically reach each other without intervening router
223.1.1.1
223.1.1.2
223.1.1.3
223.1.1.4 223.1.2.9
223.1.2.2
223.1.2.1
223.1.3.2223.1.3.1
223.1.3.27
network consisting of 3 subnets
subnet
Subnets – distinction from network

223.1.1.0/24223.1.2.0/24
223.1.3.0/24
Recipe• To determine the
subnets, detach each interface from its host or router, creating islands of isolated networks. Each isolated network is called a subnet.
Subnet mask: /24
Subnets

How many?
Hopefully you decided on 6
223.1.1.1
223.1.1.3
223.1.1.4
223.1.2.2223.1.2.1
223.1.2.6
223.1.3.2223.1.3.1
223.1.3.27
223.1.1.2
223.1.7.0
223.1.7.1223.1.8.0223.1.8.1
223.1.9.1
223.1.9.2
Subnets

CIDR: Classless InterDomain Routing– subnet portion of address of arbitrary length– address format: a.b.c.d/x, where x is # bits in
subnet portion of address
11001000 00010111 00010000 00000000
subnetpart
hostpart
200.23.16.0/23
IP addressing: CIDR - in contrast to the class based approach

Q: How does a host get an IP address?
• hard-coded by system admin. in a file, eg.– Windows: control-panel->network-
>configuration->tcp/ip->properties– UNIX: /etc/rc.config. or
• DHCP: Dynamic Host Configuration Protocol: dynamically get address from ISP server– “plug-and-play”
IP addresses: how to get one?

DHCP: Dynamic Host Configuration Protocol
Goal: allow host to dynamically obtain its IP address from network server when it joins a networkCan renew its lease on address in use
Allows reuse of addresses (only hold on to address while connected and “on”)
Support for mobile users who want to join network (more intermittently)
DHCP overview:– Host broadcasts “DHCP discover” message.– DHCP server responds with “DHCP offer” msg.– Host requests IP address: “DHCP request” msg.– DHCP server sends address: “DHCP ack” msg.

Arriving DHCP client needsaddress in thisnetwork
223.1.1.1
223.1.1.2
223.1.1.3
223.1.1.4 223.1.2.9
223.1.2.2
223.1.2.1
223.1.3.2223.1.3.1
223.1.3.27
A
BE
DHCP server
DHCP client-server scenario

DHCP server: 223.1.2.5 arriving client
time
DHCP discover
src : 0.0.0.0, 68 dest.: 255.255.255.255,67yiaddr: 0.0.0.0transaction ID: 654
DHCP offer
src: 223.1.2.5, 67 dest: 255.255.255.255, 68yiaddrr: 223.1.2.4transaction ID: 654Lifetime: 3600 secsDHCP request
src: 0.0.0.0, 68 dest:: 255.255.255.255, 67yiaddrr: 223.1.2.4transaction ID: 655Lifetime: 3600 secs
DHCP ACK
src: 223.1.2.5, 67 dest: 255.255.255.255, 68yiaddrr: 223.1.2.4transaction ID: 655Lifetime: 3600 secs
DHCP client-server scenario

Q: How does network get subnet part of IP address?
A: Gets allocated portion of its provider ISP’s address space
ISP's block 11001000 00010111 00010000 00000000 200.23.16.0/20
Organization 0 11001000 00010111 00010000 00000000 200.23.16.0/23 Organization 1 11001000 00010111 00010010 00000000 200.23.18.0/23 Organization 2 11001000 00010111 00010100 00000000 200.23.20.0/23 ... ….. …. ….
Organization 7 11001000 00010111 00011110 00000000 200.23.30.0/23
IP addresses: how to get one?

“Send me anythingwith addresses beginning 200.23.16.0/20”
200.23.16.0/23
200.23.18.0/23
200.23.30.0/23
Fly-By-Night-ISP
Organization 0
Organization 7Internet
Organization 1
ISPs-R-Us“Send me anythingwith addresses beginning 199.31.0.0/16”
200.23.20.0/23Organization 2
...
...
Hierarchical addressing allows efficient advertisement of routing information:
Hierarchical addressing: route aggregation

Hierarchical addressing: more specific routes
ISPs-R-Us has a more specific route to Organization 1
“Send me anythingwith addresses beginning 200.23.16.0/20”
200.23.16.0/23
200.23.18.0/23
200.23.30.0/23
Fly-By-Night-ISP
Organization 0
Organization 7Internet
Organization 1
ISPs-R-Us“Send me anythingwith addresses beginning 199.31.0.0/16or 200.23.18.0/23”
200.23.20.0/23Organization 2
...
...

IP addressing: the last word...
Q: How does an ISP get block of addresses?
A: ICANN: Internet Corporation for Assigned
Names and Numbers– allocates addresses– manages DNS– assigns domain names, resolves disputes

Class From To Decimal Mask
Class "A 10.0.0.0 10.255.255.255 255.0.0.0
Class "B 172.16.0.0 172.31.255.255 255.240.0.0 (or 255.255.0.0)
Class "C192.168.0.0
192.168.255.255
255.255.0.0 (or 255.255.255.0)
Private address spaceAn IP (Internet Protocol) Address is a 32-bit number broken up into "quads" of 1 byte each, separated by dots. 1 byte is 8 bits which in decimal is a number in the range 0 to 255. For example, 10.234.56.71 is an IP Address. There are only so many "real" IP addresses, and they are (and have been) perpetually very close to being used up and thus are very difficult to get.One of the solutions to this problem is so-called "private" IP Addresses. These are ranges of IP Addresses set aside expressly for use by a company or other entity internally. Private IP Addresses cannot be used to connect directly to the Internet--that is they are non-routable. These are also often called RFC1918 addresses.

NAT: Network Address Translation
10.0.0.1
10.0.0.2
10.0.0.3
10.0.0.4
138.76.29.7
local network(e.g., home network)
10.0.0/24
rest ofInternet
Datagrams with source or destination in this network
have 10.0.0/24 address for source, destination (as
usual)
All datagrams leaving localnetwork have same single source NAT IP address:
138.76.29.7,different source port
numbers
NAT: Network Address Translation

NAT: Network Address Translation• Motivation: local network uses just one IP
address as far as outside world is concerned:– range of addresses not needed from ISP:
just one IP address for all devices– can change addresses of devices in local
network without notifying outside world– can change ISP without changing
addresses of devices in local network– devices inside local net not explicitly
addressable, visible by outside world (a security plus).

Implementation: NAT router must:
– outgoing datagrams: replace (source IP address, port #) of every outgoing datagram to (NAT IP address, new port #)
. . . remote clients/servers will respond using (NAT IP address, new port #) as destination addr.
– remember (in NAT translation table) every (source IP address, port #) to (NAT IP address, new port #) translation pair
– incoming datagrams: replace (NAT IP address, new port #) in dest fields of every incoming datagram with corresponding (source IP address, port #) stored in NAT table
NAT: Network Address Translation

10.0.0.1
10.0.0.2
10.0.0.3
S: 10.0.0.1, 3345D: 128.119.40.186, 80
1
10.0.0.4
138.76.29.7
1: host 10.0.0.1 sends datagram to 128.119.40.186, 80
NAT translation tableWAN side addr LAN side addr
138.76.29.7, 5001 10.0.0.1, 3345…… ……
S: 128.119.40.186, 80 D: 10.0.0.1, 3345
4
S: 138.76.29.7, 5001D: 128.119.40.186, 80
2
2: NAT routerchanges datagramsource addr from10.0.0.1, 3345 to138.76.29.7, 5001,updates table
S: 128.119.40.186, 80 D: 138.76.29.7, 5001
3
3: Reply arrives dest. address: 138.76.29.7, 5001
4: NAT routerchanges datagramdest addr from138.76.29.7, 5001 to 10.0.0.1, 3345
NAT: Network Address Translation

• 16-bit port-number field: – 60,000 simultaneous connections with a single
LAN-side address!
• NAT is controversial:– routers should only process up to layer 3– violates end-to-end argument
• NAT possibility must be taken into account by app designers, eg, P2P applications
– address shortage should instead be solved by IPv6
NAT: Network Address Translation

• client wants to connect to server with address 10.0.0.1– server address 10.0.0.1 local
to LAN (client can’t use it as destination addr)
– only one externally visible NATted address: 138.76.29.7
• solution 1: statically configure NAT to forward incoming connection requests at given port to server– e.g., (123.76.29.7, port 2500)
always forwarded to 10.0.0.1 port 25000
10.0.0.1
10.0.0.4
NAT router
138.76.29.7
Client?
NAT traversal problem

• solution 2: Universal Plug and Play (UPnP) Internet Gateway Device (IGD) Protocol. Allows NATted host to:learn public IP address
(138.76.29.7)add/remove port mappings
(with lease times)
i.e., automate static NAT port map configuration
10.0.0.1
10.0.0.4
NAT router
138.76.29.7
IGD
NAT traversal problem

• solution 3: relaying (used in Skype)– NATed client establishes connection to relay– External client connects to relay– relay bridges packets between to connections
138.76.29.7
Client
10.0.0.1
NAT router
1. connection torelay initiatedby NATted host
2. connection torelay initiatedby client
3. relaying established
NAT traversal problem

• used by hosts & routers to communicate network-level information– error reporting:
unreachable host, network, port, protocol
– echo request/reply (used by ping)
• network-layer “above” IP:– ICMP msgs carried in IP
datagrams• ICMP message: type, code
plus first 8 bytes of IP datagram causing error
Type Code description0 0 echo reply (ping)3 0 dest. network unreachable3 1 dest host unreachable3 2 dest protocol unreachable3 3 dest port unreachable3 6 dest network unknown3 7 dest host unknown4 0 source quench (congestion control - not used)8 0 echo request (ping)9 0 route advertisement10 0 router discovery11 0 TTL expired12 0 bad IP header
ICMP: Internet Control Message Protocol

• Source sends series of UDP segments to dest– First has TTL =1– Second has TTL=2, etc.– Unlikely port number
• When nth datagram arrives to nth router:– Router discards
datagram– And sends to source an
ICMP message (type 11, code 0)
– Message includes name of router& IP address
• When ICMP message arrives, source calculates RTT
• Traceroute does this 3 times
Stopping criterion• UDP segment eventually
arrives at destination host• Destination returns ICMP
“host unreachable” packet (type 3, code 3)
• When source gets this ICMP, stops.
Traceroute and ICMP

The End
Keep reviewing the tutorial sheets.