sem 2
-
Upload
rakesh-s-k -
Category
Documents
-
view
12 -
download
1
description
Transcript of sem 2

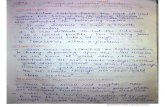
SCHEME OF TEACHING AND EXAMINATION
M.TECH. - DIGITAL COMMUNICATION & NETWORKING
II SEMESTER
Course
Code
Subject
Code Name of the Subject
Teaching hours/week Duration
of Exam
in Hours
Marks for Total
Marks Lecture Practical Tutorial I.A. Exam
10LDN21 10EC086 Wireless Communication 4 2 - 3 50*
100 150
10LDN22 10EC046 Linear Algebra 4 - 2 3 50#
100 150
10LDN23 10EC123 Modern DSP 4 2 - 3 50*
100 150
10LDN24 10EC125 Protocol Engineering 4 - 2 3 50#
100 150
10LDN25 10ECxxx Elective-II (10LDN25x) 4 - 2 3 50#
100 150
10LDN26 10EC921 Seminar / Mini-project -- 3 - -- 50$
-- 50
Project Phase-I (6 week Duration) should start between II Semester and III Semester, after availing a vacation of 2 weeks. This will
be evaluated during III semester.
Total 20 7 6 15 300 500 800 * Practical will be evaluated for 25 marks and internal assesment for 25 marks. Lab journals should be maintained.
# Assignments/seminar will be evaluated for 25 marks and internal assesment for 25 marks. Record of Assignments/seminar should be
maintained. $ Mini projet should be done individually and is assessed for 25 marks. Seminar on Miniproject will be assessed for 25 marks.
ELECTIVE – II
10LDN251 10EC023 Cryptography & Network
Security
10LDN253 10EC126
Real Time Operating Systems
10LDN252 10EC131 Wireless and Mobile Networks
II – SEMESTER
WIRELESS COMMUNICATIONS
Subject Code : 10EC086 IA Marks : 50
No. of Lecture Hours/Week : 04 Exam Hrs : 03
Total No. of Lecture Hours : 52 Exam Marks : 100
Wireless channel: physical modeling for wireless channels, input/output model of wireless channel, time and
frequency response, statistical models.
Point to point communication: detection in rayleigh fading channel, time diversity, antenna diversity,
frequency diversity, impact of channel uncertainity.
Capacity of wireless channels: AWGN channel capacity, resources of AWGN channel, Linear time invariant
gaussian channels, capacity of fading channels.
MIMO 1 – Spatial multiplexing and channel modeling: multiplexing capability of MIMO channels, physical
modeling of MIMO channels, modeling MIMO fading channels. MIMO II – Capacity and multiplexing
architectures: V-BLAST, fading MIMO channel, receiver architectures, slow fading MIMO channel, D-BLAST.
MIMO III – Diversity multiplexing tradeoff, universal code design.
References Books:
1. David Tse, P. Viswanath, “Fundamentals of wireless
communication”, Cambridge, 2006.
2. Andreas Molisch, “Wireless communications”, Wiley, 2009
William C Y Lee, “Mobile Communication Engineering Theory

and applications”, TMGH, 2008
3. Upen Dalal, “Wireless communication”, Oxford, 2009
1. Mark Ciampa, Jorge Olenwa, “Wireless communications”,
Cengage, 2007.
Laboratory Experiments:
Assignment for the Laboratory work: USE NS2 SIMULATOR (available FREE on the net)
1. Use NS2 simulator to check for the transmission power in the
Wireless network.
2. Using NS2 measure the losses in the channel.
3. Using NS2 implement the propagation model both indoor and
Out door.
4. Using NS2 measure the performance analysis of different
models.
5. Using NS2 implement the CDMA model.
6. Using NS2 measure the Latency, BW and efficiency of the
given Wireless model.
Any other experiments can be added to supplement the theory.
------------------------------------------------------------------------------
LINEAR ALGEBRA
Subject Code : 10EC046 IA Marks : 50
No. of Lecture Hours/Week : 04 Exam Hrs : 03
Total No. of Lecture Hours : 52 Exam Marks : 100
Linear Equations: Fields; system of linear equations, and its solution sets; elementary row operations and
echelon forms; matrix operations; invertible matrices, LU-factorization.
Vector Spaces: Vector spaces; subspaces; bases and dimension; coordinates; summary of row-equivalence;
computations concerning subspaces.
Linear Transformations: Linear transformations; algebra of linear transformations; isomorphism;
representation of transformations by matrices; linear functionals; transpose of a linear transformation.
Canonical Forms: Characteristic values; annihilating polynomials; invariant subspaces; direct-sum
decompositions; invariant direct sums; primary decomposition theorem; cyclic bases; Jordan canonical form.
Iterative estimates of characteristic values.
Inner Product Spaces: Inner products; inner product spaces; orthogonal sets and projections; Gram-Schmidt
process; QR-factorization; least-squares problems; unitary operators.
Symmetric Matrices and Quadratic Forms: Digitalization; quadratic forms; constrained optimization;
singular value decomposition.
REFERENCE BOOKS:
1. C. Lay, “Linear Algebra and its Applications,” 3rd
edition, Pearson
Education (Asia) Pte. Ltd, 2005.
2. Kenneth Hoffman and Ray Kunze, "Linear Algebra," 2nd
edition,
Pearson Education (Asia) Pte. Ltd/ Prentice Hall of India, 2004.
3. Bernard Kolman and David R. Hill, "Introductory Linear Algebra
with Applications”, Pearson Education (Asia) Pte. Ltd, 7th
edition,
2003.
4. Gilbert Strang, "Linear Algebra and its Applications”, 3rd
edition, Thomson Learning Asia, 2003.
MODERN DSP

Subject Code : 10EC123 IA Marks : 50
No. of Lecture Hours/Week : 04 Exam Marks : 03
Total No. of Lecture Hours : 52 Exam Hours : 100
Goal of the course – Advances in Digital Signal Processing involve variable sampling rates and thus the
multirate signal processing and hence their applications in communication systems and signal processing. It is
intended to introduce a basic course in multirate signal processing especially meant for students of branches
eligible for M Tech courses in EC related disciplines.
Review of Signals and Systems – Discrete time processing of continuous signals - Structure of a digital filter;
Frequency domain analysis of a digital filter; Quantization error; Sigma and Sigma Delta Modulation. Fourier
Analysis – DFT, DTFT, DFT as an estimate of the DTFT for Spectral estimation. DFT for convolution,
DFT/DCT for compression, FFT. Ideal Vs non ideal filters, FIR and IIR Filters Digital Filter Implementation;
Elementary Operations.
Digital Filters –, State Space realization, Robust implementation of Digital Filters, Robust implementation of
equi – ripple FIR digital filters
Multirate Systems and Signal Processing. Fundamentals – Problems and definitions; Upsampling and
downsampling; Sampling rate conversion by a rational factor;
Multistage implementation of digital filters; Efficient implementation of multirate systems.
DFT filter banks and Transmultiplexers – DFT filter banks, Maximally Decimated DFT filter banks and
Transmultiplexers. Application of transmultiplexers in communications Modulation.
Maximally Decimated Filter banks – Vector spaces, Two Channel Perfect Reconstruction conditions; Design
of PR filters Lattice Implementations of Orthonormal Filter Banks, Applications of Maximally Decimated filter
banks to an audio signal.
Introduction to Time Frequency Expansion; The STFT; The Gabor Transform, The Wavelet Transform; The
Wavelet transform; Recursive Multiresolution Decomposition.
References:
1. Roberto Cristi, “Modern Digital Signal Processing”, Cengage Publishers, India, (erstwhile Thompson
Publications), 2003.
2. S.K. Mitra, “Digital Signal Processing: A Computer Based Approach”, III Ed, Tata McGraw Hill, India,
2007.
3. E.C. Ifeachor and B W Jarvis, “Digital Signal Processing, a practitioners approach,” II Edition, Pearson
Education, India, 2002 Reprint.
4. Proakis and Manolakis, “Digital Signal Processing”, Prentice Hall 1996
(third edition). ---------------------------------- Laboratory Experiments: I. Modern Digital Signal Processing
i. Using MATLAB
1 Question based on response of LTI systems to different inputs
A LTI system is defined by the difference equation y[n]=x[n]+x[n-1]+x[n-2].
(a) Determine the impulse response of the system and sketch it.
(b) Determine the output y[n] of the system when the input is x[n]=u[n].
(c) Determine the output of the system when the input is a complex
exponential (Eg. x[n]=2ej0.2πn
).
2.Question on design of simple digital filter using the relationship between
pole and zeros and the frequency response of the system

Design a simple digital FIR filter with real co-efficients to remove a
narrowband (i.e., sinusoidal) disturbance with frequency F0=50 Hz. Let
Fs=300 Hz be the sampling frequency.
(a) Determine the desired zeros and poles of the filter.
(b) Determine the filter coefficients with the gain K=1
(c) Sketch the magnitude of the frequency response.
3 Question on simple digital filtering using the relationship between pole and zeros and the frequency response
of the system
Design an IIR filter with real co-efficients with same specifications
mentioned in Q2 and repeat the steps (a) to (c).
4. Question to understand the effect of time domain windowing
Generate a signal with two frequencies x(t)=3cos(2πF1t) + 2cos(2πF2t)
sampled at Fs=8 kHz. Let F1=1 kHz and F2=F1+Δ and the overall data
length be N=256 points.
(a) From theory, determine the minimum value of Δ necessary to
distinguish between the two frequencies.
(b) Verify this result experimentally. Using the rectangular window, look
at the DFT with several values of Δ so that you verify the resolution.
(c) Repeat part (b) using a Hamming window. How did the resolution
change?
5 Comparison of DFT and DCT (in terms of energy compactness)
Generate the sequence x[n]=n-64 for n=0,…127.
(a) Let X[k]=DFT{x[n]}. For various values of L, set to zero the “high
frequency coefficients” X[64-L]=….X[64]=…….=X[64+L]=0 and
take the inverse DFT. Plot the results.
(b) Let XDCT[k]=DCT(x[n]}. For the same values of L, set to zero the
“high frequency coefficients” XDCT[127-L]=…….XDCT[127]. Take the
inverse DCT for each case and compare the reconstruction with the
previous case.
6 Filter design
Design a discrete time low pass filter with the specifications given
below:
Sampling frequency = 2 kHz.
Pass band edge = 260 Hz
Stop band edge = 340 Hz
Max. pass band attenuation = 0.1 dB
Minimum stop band attenuation = 30 dB
Use the following design methodologies:
Hamming windowing
Kaiser windowing
Applying bilinear transformation to a suitable, analog Butterworth filter.
Compare the obtained filters in terms of performance (accuracy in
meeting specifications) and computational complexity.
ii. Using DSP PROCESSOR
1 Write an ALP to obtain the response of a system using linear convolution whose input and impulse response
are specified.
1. Write an ALP to obtain the impulse response of the given system, given the difference equation. .
2. Sampling of an Image.
3. Design of equiripple filters.
4. Application of frequency transformation in filter design.

5. Computation of FFT when N is not a power of 2.
6. Sampling rate conversion and plot of spectrum.
7. Analysis of signals by STFT and WT.
8. Delayed auditory feedback signal using 6713 processor.
9. Record of machinery noise like fan or blower or diesel generator
and obtaining its spectrum.
11. Synthesis of select dual tone multi frequency signals using 6713
processor.
12. Fourier Transform & its inverse Fourier Transform of an image.
Any other experiments can be added to supplement the theory.
PROTOCOL ENGINEERING
Subject Code : 10EC125 IA Marks : 50
No. of Lecture Hours/Week : 04 Exam Hrs : 03
Total No. of Lecture Hours : 52 Exam Marks : 100
Communication Model, software, subsystems, protocol development methods, protocol engineering process ;
Network Reference Model: services and interfaces, protocol functions, OSI and TCP/IP model,
Protocols: Host to network interface protocols, network protocols transport protocols, application protocols;
Protocol Specifications: Components of protocol, service specifications, entity specifications, interface and
interactions, multimedia protocol specifications, HDLC, ABP and RSVP specifications;
SDL: features, communication system using SDL, examples of SDL based protocol specifications, other
specification languages;
Protocol Verification, FSM based verification, validation, design errors, validation approaches, verification and
validation of ABP using SDL; Conformance testing, framework, conformance test architectures, test sequence
generation methods, TTCN, multimedia testing,
MPLS Testing; Performance testing methods, testing of TCP and OSPF, interoperability testing, scalability
testing;
Protocol Synthesis Algorithms, resynthesis, protocol implementation requirements, methods of
implementation, protocol compilers, tools for protocol engineering Assignments / practical can be chosen from
the Appendix of the mentioned reference books, particularly –book 1.
REFERENCE BOOKS:
1. Pallapa Venkataram, Sunil Kumar Manvi, “Communication Protocol Engineering”, PHI, 2004.
2. G. J. Holtzmann, “Design and validation of Computer protocols”, Prentice hall, 1991 (available on
web)
3. K. Tarnay, “Protocol Specification and Testing”, Plenum press, 1991
ELECTIVE – II
CRYPTOGRAPHY AND NETWORK SECURITY
Subject Code : 10EC023 IA Marks : 50
No. of Lecture Hours/Week : 04 Exam Hrs : 03
Total No. of Lecture Hours : 52 Exam Marks : 100

Overview: Services, Mechanisms and attacks, OSI security architecture, Model for network security. Classical Encryption Techniques: Symmetric cipher model, Substitution techniques, Transposition techniques, Rotor machine, Steganography, Problems.
Block Ciphers and DES (Data Encryption Standards): Simplified DES, Block cipher principles, DES,
Strength of DES, Block cipher design principles, Block cipher modes of operation, Problems.
Public Key Cryptography and RSA: Principles of public key cryptosystems, RSA algorithm, Problems.
Other Public Key Crypto Systems and Key Management: Key management, Diffie-Hellman key exchange,
Elliptic curve arithmetic, Elliptic curve cryptography, Problems.
Message Authentication and Hash Functions: Authentication requirements, Authentication functions,
Message authentication codes, Hash functions, Security of hash functions and MAC’s, Problems.]
Digital Signature and Authentication Protocol: Digital signature, Authentication protocols, Digital signature
standard.
Authentication Applications: Kerberos, X.509 authentication service, Kerberos encryption technique,
Problems.
Electronic Mail Security: Pretty good privacy, S/MIME, Data compression using ZIP, Radix-64 conversion,
PGP random number generator.
IP Security: Overview, IP security architecture, Authentication header, ESP (encapsulating security pay load),
Security associations, Key management, Problems.)
Firewalls: Firewall design principles; Trusted systems, Problems.
REFERENCE BOOKS:
1. William Stallings, “Cryptography and Network Security”, 3rd
edition, Pearson Education (Asia) Pvt.
Ltd./ Prentice Hall of India, 2003.
2. C. Kaufman, R. Perlman, and M. Speciner, “Network Security: Private Communication in a Public
World”, 2nd
edition, Pearson Education (Asia) Pvt. Ltd., 2002.
3. Atul Kahate, “Cryptography and Network Security”, Tata McGraw-Hill, 2003.
4. Eric Maiwald, “Fundamentals of Network Security”, McGraw-Hill, 2003.
Wireless and Mobile Networks
Subject Code : 10EC131 IA Marks : 50
No. of Lecture Hours/Week : 04 Exam Hours : 03
Total No. of Lecture Hours : 52 Exam Marks : 100
Review of fundamentals of wireless communication and networks. Wireless communication channel
specifications, wireless communication systems, wireless networks, switching technology, communication
problems, wireless network issues and standards.
Wireless body area networks (WBAN). Properties, network architecture, components, technologies, design
issues, protocols and applications.
Wireless personal area networks. Architecture, components, requirements, technologies and protocols,
Bluetooth and Zigbee.
Wireless LANS. Network components, design requirements, architectures, IEEE 802.11x, WLAN protocols,
802.11 p and applications.

WMANs. IEEE 802.16, architectures, components, WiMax mobility support, protocols, broadband networks
and applications. WWANs. Cellular networks, Satellite networks, applications.
Wireless adhoc networks. Mobile adhoc networks, Sensor networks, Mesh networks, VANETs. Research
issues in wireless networks.
References:
1. S. S. Manvi, M. S. Kakkasageri, “Wireles and Mobile Network
concepts and protocols”, Wiley, First edition, 2010.
2. P. Kaveh, Krishnamurthy, “Principles of wireless networks: A unified
approach”, PHI, 2006.
1. Iti Saha Mishra, Wireless communication and networks 3G and
beyond”, MGH, 2009
4. Mullet, “Introduction to wireless telecommunication systems and
networks”, Cengage, 2009.
5. Yi-Bing Lin, Imrich Chlamtac, “Wireless and mobile network
architectures”, Wiley, 2009
REAL TIME OPERATING SYSTEMS
Subject Code : 10EC126 IA Marks : 50
No. of Lecture Hours /week : 04 Exam Hours : 03
Total no. of Lecture Hours : 52 Exam Marks : 100
Introduction to Real-Time Embedded Systems: Brief history of Real Time Systems, A brief history of
Embedded Systems.
System Resources: Resource Analysis, Real-Time Service Utility, Scheduling Classes, The Cyclic Esecutive,
Scheduler Concepts, Preemptive Fixed Priority Scheduling Policies, Real-Time OS, Thread Safe Reentrant
Functions.
Processing: Preemptive Fixed-Priority Policy, Feasibility, Rate Montonic least upper bound, Necessary and
Sufficient feasibility, Deadline – Monotonic Policy, Dynamic priority policies.
I/O Resources:
Worst-case Execution time, Intermediate I/O, Execution efficiency, I/O Architecture.
Memory:
Physical hierarchy, Capacity and allocation, Shared Memory, ECC Memory, Flash filesystems.
Multiresource Services:
Blocking, Deadlock and livestock, Critical sections to protect shared resources, priority inversion.
Soft Real-Time Services:
Missed Deadlines, QoS, Alternatives to rate monotonic policy, Mixed hard and soft real-time services.
Embedded System Components:
Firmware components, RTOS system software mechanisms, Software application components.
Debugging Components:
Execptions assert, Checking return codes, Single-step debugging, kernel scheduler traces, Test access ports,
Trace ports, Power-On self test and diagnostics, External test equipment, Application-level debugging.
Performance Tuning:
Basic concepts of drill-down tuning, hardware – supported profiling and tracing, Building performance
monitoring into software, Path length, Efficiency, and Call frequency, Fundamental optimizations.
High availability and Reliability Design:

Reliability and Availability, Similarities and differences, Reliability, Reliable software, Available software,
Design trade offs, Hierarchical applications for Fail-safe design.
Design of RTOS – PIC microcontroller. (Chap 13 of book Myke Predko)
References:
3. “Real-Time Embedded Systems and Components” , Sam Siewert, Cengage Learning India Edition,
2007.
4. “ Programming and Customizing the PIC microcontroller” , Myke Predko, 3rd
Ed, TMH, 2008
5. “Programming for Embedded Systems”, Dreamtech Software
Team, John Wiley, 2008
6. “Embedded Linux: Hardware, Software & Interfacing” ,
Carig Hollabaugh, Pearson Education, 2009.