Principles of Network Forensics · 2011-04-30 · analyzing network autdit trails in order to...
Transcript of Principles of Network Forensics · 2011-04-30 · analyzing network autdit trails in order to...

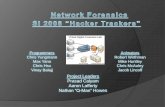
Principles of NetworkForensics
Richard Baskerville
Georgia StateUniversity

P Internet Concepts Review
PNetwork-based LiveAcquisitions
PNetwork Forensics Principles
Agenda
Principles of Network Forensics

Internet Concepts Review
IPv4

Packet Switched Networks
ErrorCheck Data Header
Packets
Customers
Cust. Cust. Cust.Cust.
LargCeu stomer
Packet Network
1
2
3
4
5
6 7
A-C
D-H I-M N-PQ-Y
Z

X.25 Packet
MessageFramCeh eckSequence
Flag01111110
Flag01111110
Address Control

Open Systems Interconnection (OSI) Model
PhysicLaal yer
DataL inkL ayer
NetworLka yer
TranspoLrat yer
SessioLna yer
PresentatioLna y.
ApplicatioLna yer
PhysicLaal yer
DataL inkL ayer
NetworLka yer
TranspoLrat yer
SessioLna yer
PresentatioLna y.
ApplicatioLna yer
Client Server

P Application Layer
P Host-to-Host Transport Layer
P Internet Layer
P Network Access Layer
Internet Model

Internet Layers
Data
Data + TL Pr
Data + TL/IL Pr
Application Layer
Transport Layer
Internet Layer
Network Access Layer
Data + TL/IL/NA Pr
FTP
TCP
IP
X.25
Data
Data + TL Pr
Data + TL/IL Pr
FTP
TCP
IP
X.25

< CCITT X.25< IEEE 802.3< Ethernet< Novell Netware< CSMA/CD< Token Ring (IEEE 802.5)
Network Access Layer

P Internet Protocol (IP)
P Datagram< Header (5-6 words)< Data
P Types of network nodes< Gateways< Hosts
P Internet Control Message Protocol (ICMP)
Internet Layer

P Transmission ControlProtocol (TCP)
< 6-word header< "reliable"< connection oriented
P User Datagram Protocol(UDP)
Transport Layer

P FTP
P Telnet
P SMTP
P DNS
P NFS
P RIP
P Gopher
P WAIS
P WWW
Application Layer

P IP Addresses< 4-byte numbers
– eg 121.11.21.18
< Network addresses– 121.11.21.0
< Multihomed hosts andgateways have twoaddresses
P Domain Name Service< Host tableNIC Host table
Internet Addressing
IPv4

Nesting Packets
Data
Header
Header
Header
Header
HeaderHeader
Data
Data
Data
Application Layer
Transport Layer
Internet Layer
Network Access Layer

Domain Hierarchy

Domain Name Server Response
ww.ibm.com?
com NS nic.com
www.ibm.com?
ibm.com NS vm1.ibm.com
www.ibm.com?
www.ibm.com A 111.222.101.111
nic.cbs.dk
nic.com
vm1.ibm.com
First
Second
Third

PTransport layer routingtables< lists destination nets with
gateways< "default" gateway where
unlisted IP packets aresent
PAddress resolution< Network access layer
Routing

Ports and Sockets
Telnet Client
Telnet Server
131.71.8.1
211.14.21.2
Socket:131.71.8.1.3121,211.14.21.2.23
Socket:211.14.21.2.23,131.71.8.1.3121

PSlowed Exhaustion ofIPv4 address space
PRouting tables simplified< Base address< Size of subnet
PEnabled more fluidsubnet proliferation
Classless Inter-Domain Routing
(CIDR)

P32-byte address numbers< Addresses IPv4 Address
Exhaustion
PAutoconfiguration < Router solicitation & advertisement
PMany other features, e.g.,< Multicast capability no longer
optional< Network layer security (encryption)
no longer optional
IPv6

Network-based LiveAcquisitions

PCases where circumstances preventremoving the media from the computer.
PSpecialty hardware (e.g., some laptops)
PUnusual hard drive geometries< Host Protected Areas (HPA)< Device Configuration Overlays (DCO)
PDisclosure of ongoing investigation < “Black bag” jobs
Motivation: Live Acquisitions

PHelix< Linux boot of Windows machine< C:\ drive write protected< Encase, FTK, dd imaging
PForensic Boot Disk< Diskette or CD< DOS< Windows 98< EnCase Boot Disk
Safely Booting Target Machine
Homemade

PUSB adapter
PDisk-to-disk< No boot required< Open the box, connect directly to drive
PCross-over cable< Use network acquisition technology
Connecting Acquisition Devices

PServlet installed on target machine< Requires administrator access< Can be installed remotely
PServlet feeds image to acquiring machine
PMay require authentication< (E.g., EnCase)
Live Network Acquisitions (I)

Live Network Acquisition (II)
AuthenticationServer
ForensicsExaminer
AcquisitionTarget
Network
Servlet

Network ForensicsPrinciples

The action of capturing, recording, andanalyzing network autdit trails in order todiscover the source of security breaches orother information assurance problems.
Network Forensics
Kim, et al (2004) “A fuzzy expert system for networkfornesics”, ICCSA 2004, Berlin: Springer-Verlag, p. 176

PProtocol< Eg, SQL-Injection
PMalware< Eg, Virus, Trojan, Worm
PFraud< Eg, Phishing, Pharming, etc.
Network Attacks

PSuccessful< Obfuscation of residue
PUnsuccessful< Residue is intact
Attack Residue

PManaging data volume
PManaging logging performance
PEnsuring logs are useful to reconstruct theAttack
PCorrelation of data in logs< Importance of timestamping
Network Traffic Capture
Logging Issues Driving Automated Support

Honeytraps
Systems Designed to be Compromised and Collect AttackData
From Yasinac, A. andManzano, Y. (2002)“Honeytraps, A NetworkForensic Tool” FloridaState University.

PSessionizing
PProtocol parsing andanalysis
PDecryption
PSecurity of Analysis andData< Avoiding detection and
analysis-data compromise
Network Traffic Analysis
Usually Requires Software Tools

PMinimizing distance to source
PTraversing firewalls, proxies and addresstranslation
PMuliple cooroborating collectors
PTime and location stamping
Traceback Evidence Processing

Principles of NetworkForensics
Richard Baskerville
Georgia StateUniversity