Performance Modeling of Anonymity Protocols
description
Transcript of Performance Modeling of Anonymity Protocols

Performance Modelingof Anonymity Protocols
Carey Williamson Niklas Carlsson
Andreas Hirt Michael J. Jacobson, Jr.
Department of Computer Science
University of Calgary
Financial support for this research support was provided by:
Natural Sciences and Engineering Research Council (NSERC),
Informatics Circle of Research Excellence (iCORE),
Alberta Ingenuity Fund (AIF), and
Canada Foundation for Innovation (CFI)

2
Introduction
Anonymous communication conceals who communicates what, to whom, and when
Allows individuals to communicate without fear of embarrassment, ridicule, or retribution
Cornerstone for freedom of speech

3
Some Real World Applications
Good: Freedom of speech in totalitarian regime Crime stoppers On-line counseling Whistle blowing Group evaluations Military communications …
Bad: Organized crime Terrorist groups ...

4
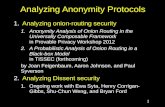
Outline
Review of Anonymity Schemes Our Work: Buses, Taxis, Motorcyles Performance Modeling Numerical Results Conclusion

5
xmkzykrziwqmqkdx
Re-routing with Layered Encryption
Layered Encryption: Add layers of encryption to make message contents change each hop
hello

6
xmkzykrziwqm
Layered Encryption: Add layers of encryption to make message contents change each hop
hello
Re-routing with Layered Encryption

7
Layered Encryption: Add layers of encryption to make message contents change each hop
hello
xmkzykrz
Re-routing with Layered Encryption

8
Layered Encryption: Add layers of encryption to make message contents change each hop
hello
xmkz
Sender?
hello
Problem: Timing analysis
Re-routing with Layered Encryption

9
Senders use nested (layered) encryption along re-routing path Mixes (re-routing nodes) mix input-output correlations:
Collect input batch Peel encryption layer away Output in random order
Message 1
Message 2
Message 3
Message 4
Message 5
Message 4
Message 3
Message 1
Message 5
Message 2
Mixes

10
Current Solutions
No Cover Traffic
Partial Cover Traffic
Full Cover Traffic
Schemes Crowds, TOR JAP, MorphMix
Mixmaster, Mixminion, Tarzan
Anonymity Weak Moderate Strong
Problems Vulnerable to known attacks
Vulnerable to known attacks
Not suitable for interactive applications, don’t scale well

11
Classic Buses Protocol[Beimel and Dolev 2003]
Metaphor: city bus, with regularly scheduled route, which obscures the movements of its messengers
Assume dark windows, and enclosed garages at each stop
hello
hello

12
Anonymity in Buses
Sender Anonymity: Suspected sender can claim they are forwarding a message on behalf of any other participant on the bus path
Receiver Anonymity: Suspected receiver can claim they forwarded a message to any other participant on the bus path

13
Key Ideas in Our Buses
Indirection path: re-routing path on top of bus overlay
Layered Encryption: encryption on reverse indirection path
Owned Seats: Each participant replaces owned seats every bus tour (online)
Receiving seats: bus copied and decrypted offline to find messages

14
Buses Protocol
S Rhello

15
S Rhello
xmkz
Buses Protocol

16
S Rhello
ymkq
Buses Protocol

17
S Rhello
Buses Protocol

18
S Rhello
Buses Protocol

19
ymkq
S Rhello
xmkz
Buses Protocol

20
helloxmkz
S Rhello
Buses Protocol

21
Improvements with Taxis
Processing Delay decreased by O(n) Owned seats are delayed once per bus tour
instead of n times (see MASCOTS 2008 paper )
Networking Delay decreased by O(n) Forwarding of unowned taxis can be
pipelined by giving unowned taxis network priority over owned taxis (see MASCOTS 2008 paper)

22
Improvements with Motorcycles
Routing Path length decreased to O(log n) Chord-based routing using finger table
Forwarding delay actually increases More “message transfers” occur at nodes
Still a net win overall!

23
Performance metric: one-way message delay DSR
Five main components Sender S must create/encrypt and send message Load-dependent sender-side delay
Queueing of (average) duration Ws Load-independent path delay
Path length HSR with (Dproc+Dnet) delay on each node Load-dependent transfer delay
Queueing at HT transfer nodes, each with duration WT
Target receiver R must decrypt and receive message
Model Overview
RTTnetprocSRSSSR DWHDDHWDD )(

24
Load-independent Delays
AnonymityProtocol
ProcessingDproc
NetworkDnet
Buses KNDseat KNs/r+p
Taxis KDseat Ks/r+p
Motorcycles
KDseat Ks/r+p
N nodes; K seats per node; Dseat processing per seat; s/r transmission time per seat; p per-hop propagation delay

25
Hop counts
Metric Buses/Taxis Motorcycles
HSR
(end-to-end)
N/2, if L=0
(1+L)(N+1)/2, otherwise
HT
(transfers)L HSR – 1
2
log)1(
log
1
1 log1
NL
h
Nh
N
L Nh

26
Load-dependent Delays
ProtocolSender
WS
TransfersWT
Cycle TimeTC
Buses
Taxis
Motor )(2
log)2/1()2/1(
)()2/1()2/1(
)()1()2/1(
pr
KsKD
NQTQT
pr
KsKDNQTQT
pr
KNsKNDNQTQT
seatCCCC
seatCCCC
seatCCCC

27
Light Load Case
Light load: No queueing QC 0 Example: Buses protocol
Dproc ~ N; Dnet ~ N; TC ~ N2; hence, DSR ~ N2
Scaling behavior Buses: DSR ~ N2
Taxis: DSR ~ N Motorcycles: DSR ~ log2N
RCnetprocSSR DTLDDN
LDD )2
1()(
2)1(

28
Queueing Analysis (1 of 3)
Single-seat (K=1) case Analysis on per-node basis
New messages at rate /N Message transfers at rate HT/N Assume Poisson arrivals at aggregate rate (1+ HT)/N
Either: - service period of duration TC
- vacation period of duration TC
(1+ HT)/N
Node i

29
Can be shown that generating function
In our system
Queueing Analysis (2 of 3)
1
001
,)(
))(1)(()(
zdz
dFpwhere
zzV
zFzVpzQ
NH
ezvzvzFzV
T
z
i
ii
i
ii
λ)1(
...)()( )1(
00

30
Queueing Analysis (3 of 3)
Expected queue length
Other metrics “relatively straightforward” to obtain, given the generating function Variance State probabilities q0, q1, …, qm
)1(2
)23(...][
10
zii dz
dQiqqE
2q

31
Experimental Validation (Buses)

32
Experimental Validation (Taxis)

33
Simulation Validation (Buses)

34
Simulation Validation (Taxis)

35
Simulation Validation (Motorcycles)

36
N=4 N=16
Impact of message generation rate
Different saturation points ( 1) E.g., capacity planning

37
Buses
Taxis
Motorcycles
Impact of node utilization
Queueing delays dominate when > 0.8
Note higher saturation point …
can sustain higher Hence, differences even
greater than shown …

38
Buses
Taxis
Motorcycles
Scaling results
for light load with K seats per node
Low load results As expected, scales
as (roughly) Buses N2
Taxis N Motorcycles log2N

39
Buses
Taxis
Motorcycles
Scaling results
for different load levels
Relative performance differences maintained at higher loads
In summary: Motorcycles provide a robust and scalable approach for anonymous network communication.

40
Conclusions
The average message latency of Practical Buses scales quadratically with number of participants
Analysis, simulation, and experimental results The average message latency of Taxis scales
linearly with the number of participants Analysis, simulation, and experimental results
The average message latency of Motorcycles scales logarithmically with the number of participants
Analysis and simulation results