Paper Corrected
-
Upload
drprakash-g-chithappa -
Category
Documents
-
view
217 -
download
0
Transcript of Paper Corrected

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 1/8
GENERATION OF SOPHISTICATED CHANNEL FOR SECRET FILE TRANSFER
Amravathi.M, Diana.C, Shalini Kumar and Sheela.R
Email ID:[email protected]
Telephone no:9944622257
Sona college of technology
Affiliated to Anna University
Salem.
Abstract:
Covert channel aims to hide the very existence of network communication between hosts.
Encryption only protects communication from being decoded by unauthorized parties,
whereas covert channels are used for secret transfer of information. This paper discusses
a novel covert file transfer protocol (CFTP) based on the IP record route option. The
CFTP protocol is used to secretly transfer text files and short messages between hosts.
Firewalls that limit the outgoing traffic to a few allowed application protocols (e.g. FTP)
can be circumvented by the CFTP protocol by making use of the ICMP header. The
proposed work is mainly intended for defense, business organizations and in every sector
where secrecy is the main concern. The hidden information exchanged by the CFTP
server and client cannot be identified by the hackers because the proposed IP packet will
be identical to the standard IP packet. To demonstrate the practical efficiency of the
proposed covert protocol, a user friendly tool based on the client/server technology is
recommended. Compared with related research, the contribution of our work is to
introduce a new generation of covert channels. It provides more sophisticatedcommunication channel that can be used for hiding information. This paper also makes
use of public key encryption ± RSA algorithm to reinforce security features.

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 2/8
Introduction:
Covert channels are regarded as one of the
main sub disciplines of data hiding. Covert
channel is a channel that is used for secret
information transfer by hiding the very
existence of communication. Typically, they
use communication means which are not
normally intended to be used for data transfer
and is neither designed nor intended for
network communication between hosts. This
property makes them quite elusive.
In computer networks, overt channels, such
as typical network protocols, are used as
carriers for covert channels. Covert channels
in computer network protocols are similar to
techniques for hiding information in audio,
visual or textual content (steganography).
While steganography requires some form of
content as cover, covert channels require
some network protocols as carrier.
The utilization of covert channels for
communication and coordination is typically
motivated by the existence of an adversarial
relationship between two parties. In addition,
many organizations and groups have an
interest to keep their communication secret.
However, simply using encryption does not
prevent adversaries from detecting
communication patterns. Often, only the
evidence of communication taking place is
sufficient to detect the onset of activity,
discover organizational structures or justify
further investigation. Many applications of
covert channels like unused header field,
modulating address field and packet length
techniques, etc are of a malicious or
unwanted nature, and therefore pose a serious
threat to network security. Furthermore,
because of increased measures against overt
channels, such as the free transfer of memory
storage devices in and out of organizations,
the use of covert channels in computer
networks will increase. Understanding
existing covert channel techniques is crucial
to the development of countermeasures. The
detection, elimination, and capacity
limitation of covert channels are challenging
but need to be addressed to secure future
computer networks. In this paper, a new
covert channel technique that offers a covert
file transfer protocol (CFTP) based on the
record route option of the IP header and
ICMP traffic is presented.
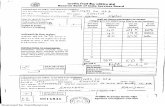
Figure1:Embedding covert channel in Overt Channel
Existing System:

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 3/8
Eighteen groups have been proposed to
describe existing covert channels[6].These
channels uses unused bits of header and
predefined header extensions for hiding the
secret information. Thus they are restricted
to small amounts of covert data transmission.
In the detection of Covert channels, all the
existing covert channels exhibits non-
standard or abnormal behavior and so the
anomalous packets can be easily filtered by
the firewall.
Two groups of covert channels are related to
the proposed paper. They are the following:
Header extensions and padding: Many
protocols support extension of the standard
headers. Usually there are some pre-defined
header extensions that allow transporting
non-mandatory information on demand, but
many protocols also allow header extensions
to carry data not foreseen in the original
specification, extending the capabilities of
the protocol.
Payload tunneling: Payload tunnels are
covert channels that tunnel one protocol
(usually the IP protocol) in the payload of another protocol. The main purpose of these
channels is circumventing firewalls that limit
outgoing traffic to a few allowed application
protocols (e.g. HTTP). Therefore, most of
these channels do not aim for stealth but
rather for maximizing the throughput. A
variety of tools exist for tunneling over
application protocols that are often not
blocked such as ICMP or HTTP .
P roposed System:
1. The proposed covert channel is
identical to normal use of the IP
protocol and consequently it will be
harder to detect. Hence, it
circumvents the firewall.
2. In some cases ,if the firewall does not
allow FTP traffic between inside and
outside hosts, then the proposed
CFTP can be used to transfer text files
and messages using IP traffic that is
usually allowed by the firewall.
To protect against eavesdropping, the CFTP
protocol generates ICMP packets withrandom types such as echo and timestamp
ICMP messages
1. Even with the sniffer, the hidden
information exchanged by the CFTP
server and client cannot be identified.
2. Since, the sniffer¶s users assume that
the hidden information in the recordroute IP options is just a list of router
IP addresses.
3. For providing confidentiality we use
public key encryption.

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 4/8
The IP Record Route Option:
In order to introduce the terms used by the
proposed covert channel and lay the
groundwork for what follows, we introduce
the IP record route option. The Internet
Protocol (IP) is the most commonly used
protocol in the network layer today, and is
used for all traffic moving across the Internet.
Upon receiving a TCP, UDP or ICMP packet,
the IP protocol generates a header which
includes the source and destination IP
addresses. An IP header is added to the front
of a TCP, UDP or ICMP packet to create the
resulting IP packet, which will be used to
carry the entire contents (IP header,
TCP/UDP/ICMP header, and application-
level data) across the network.
Figure 2. The IP header
The IP Options field is not required in every
datagram; options are included primarily for network testing or debugging. Option
processing is an integral part of the IP
protocol, and all standard implementations
must include it. The IP Options field is not
required in every datagram; options are
included primarily for network testing or
debugging. Option processing is an integral
part of the IP protocol, and all standard
implementations must include it.
Figure 3.The structure of the IP Options field
The length of the IP Options field varies
depending on which options are selected.
Some options are one byte long; they consist
of a single option code byte. Other options,
such as the Timestamps record and the Strict
source routing, have variable lengths. Each
option consists of a single octet option code,
which may be followed by a single octet
length and a set of data octets. The option
code byte is divided into three fields.
Figure 4.The field code of the IP header option
The fields consist of a 1-bit copy flag, a 2-
bits option class, and a 5-bits option number .
The copy flag controls the way gateways treat
options during fragmentation. When the copy
bit is set to 1, it specifies that the option
should be copied into all fragments. When it
is set to 0, it means that the option should

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 5/8
only be copied into the first fragment and not
into all fragments. The option class and
option number bits specify the general class
of the option, and the specific option in that
class, respectively. Table 1 shows how
classes are assigned.
There are eight possible options that can
accompany an IP datagram. Table 2 lists the
most used options and gives their option
class and option number values. As the list
shows, most options are used for control
purposes. The record route option allows the
source to create an empty list of IP addresses
and arrange for each gateway that handles the
datagram to add its IP address to the list.
Figure 5 shows the format of the record route
option. As described above, the Code field
contains the option number and option class
(e.g. 7 for record route option). The Length
field specifies the total length of the option as
it appears in the IP datagram, including the
first three octets. The Pointer field specifies
the offset within the option of the next
available slot. The remaining area in the
Options field is reserved for recording IP
address entries.
Whenever a host handles a datagram that has
the record route option set, the host adds its
IP address to the record route list (enough
space must be allocated in the option by the
original source to hold all entries that will be
needed). To add itself to the list, a host first
compares the pointer and length fields. If the
pointer is greater than the length, then the list
is full and the host forwards the datagram
without inserting its IP address. If the list is
not full, the host inserts its 4-octet IP address
at the position specified by Pointer , and
increments the value in the Pointer by four.
THE IP RECORD ROUTE OPTION
BASED COVERT CHANNEL
The principle of the covert channel:
When the IP header option designates a
record route, the fields Code and Pointer
should be set to the values 7 and 4,

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 6/8
respectively. The maximum value in the
Length field is 40 bytes. These fields and
their corresponding values are listed in Table
3.
In its way to the destination, each router
writes its IP address in the 4-byte-field
pointed by the value in the Pointer field.
Figure 5 shows the fields in the record route
option.
Figure 5. The format of the record route option in an
IP datagram
Then, the value of the Pointer field in the IP
header option is increased by 4.
Consequently, the next router would write its
IP address in the next 4-byte-field. However,
if the value of the Pointer field becomes
greater than the value of the Length field,then no more routers can write their IP
addresses.
Figure 6. A normal IP record route option
Therefore, we may establish a covert channel
if the initial value of the Pointer field is
greater than the value of the Length field, or
just greater than the length of the hidden
message. Specifically, if we set the initial
value of the Pointer field greater than thevalue of the Length field, then no router can
write its IP address. In this case, we can use
all the remaining 36 bytes of the IP header
option to insert a hidden message. This is
shown in Figure 7.a. However, if we set the
initial value of the Pointer field to a value
greater than the length of the hidden
message, then a number of routers can still
write their IP addresses in the remaining
bytes of the IP header option. This is shown
in Figure 7.b.
Figure 7.(A) The different values of the Pointer field
used for the covert channel

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 7/8
Figure 7.(B) The different values of the Pointer field
used for the covert channel
Proposed algorithm for embedding data:
Step 1:Get the secret data to be
transferred.
Step 2: Convert the secret data into
binary format.
Step 3: Encrypt the binary bits using
RSA algorithm.
Step 4: Process the encrypted data by
using the substitution algorithm.
Step 5:Perform logical operation on
the resultant data.
Encryption process:
Embedding process:
Advantages
1. Sniffers are unable to detect the
hidden messages which are assumed
to be router IP addresses.
2. The proposed technique offers 40
bytes of covert memory which is
considerably larger than the 4 byte
size available in TCP based covert
channel.
3. The covert channel has to follow
restrictions and the rules imposed by
the TCP protocol including
synchronization, flow control and
congestion control. In contrast, the
proposed techniques can exclusively
rely on ICMP traffic to carry hidden
messages.
4. The good rate of privacy, memory
and flexibility provided by the
proposed covert channel.
5. Confidentiality is provided by making
use of the public key encryption ±
RSA algorithm.
6. Confusion technique is given by
making use of the substitution
algorithm and logical operation.

8/6/2019 Paper Corrected
http://slidepdf.com/reader/full/paper-corrected 8/8
Conclusion:
This paper discusses a novel covert
file transfer protocol (CFTP) based on
the IP record route option used to
secretly transfer text files and short
messages between hosts. It was
understood that even with a Sniffer,
the hidden information exchanged by
the CFTP server and client cannot be
identified. Since, the Sniffer¶s users
assume that the hidden information in
the record route IP options is just a
list of router IP addresses. In addition,
to avoid the detection of the packet
flow between the CFTP server and
client, the packets exchanged do not
have the same ICMP packet types.
Compared to related work, the
novelty of the proposed protocol is
that it provides a new generation of
sophisticated covert channels that can
be used for hiding information.. The
hidden information is packaged in the
form of IP addresses. However, it is
possible for one to verify the validity
of these IP addresses in the
connection path. Therefore, a public
key encryption ± RSA algorithm
along with the substitution techniques
is used. This enhances the level of
security and favors secret file transfer.
References:
1. Steganography and Steganalysis by
Robert Krenn .
2. Practical Data Hiding in TCP/IP by
Kamran Ahren, Kundur.
3. Covert channel over TCP/IP and
Protocol Steganography by Kashif
Ali Siddiqui
4. .A survey of covert channels and
counter measures in computer
network protocols by
s.zander,G.Armitage,P.Branch.
5. S. Katzenbeisser and F. Petitcolas,
³Information Hiding Techniques for
Steganography and Digital
Watermarking.´
6. S. Zander, G. Armitage, P. Branch.
³A Survey of Covert Channels and
Countermeasures in Computer
Network Protocols.´