NERC CIP Cyber Security Standards V4 – Is it getting better or worse?
-
Upload
tripwire -
Category
Technology
-
view
966 -
download
1
Transcript of NERC CIP Cyber Security Standards V4 – Is it getting better or worse?
Join the conversation:
#CIPv4Webcast
NERC CIP Cyber Security Standards V4: Is it getting better or worse?
Join the conversation:
#CIPv4Webcast
NERC CIP Cyber Security Standards V4 – Is it getting better or worse?
Paul Reymann, CEO, ReymannGroup, Inc.James Stanton, Senior Energy Consultant, ReymannGroup, Inc.Cindy Valladares, Compliance Solutions Manager, Tripwire, Inc.
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
We will cover…
The New Prescriptive Bright-line Criteria
Struggles between FERC, NERC, & Industry
Practices for Security, Reliability, and Compliance
Smart Grid Evolution Benefits & Challenges
Visibility, Intelligence, and Automation are Key
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Energy’s Inverted Security Model
Smart Grid
One Big Network
SCADA
Internal Applications
Cyber Asset
Open to Cyber-ThreatsOpen to Cyber-Threats
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Cyber Security is a Priority!
Our work has also raised concerns about the increasing reliance on information technology and control systems, which are potentially vulnerable to cyber attack, including the systems used in the electricity sector.
General Accounting Office (GAO)
Foreign governments already have or are developing computer attack capabilities, and potential adversaries are developing a body of knowledge about U.S. systems and methods to attack these systems.
National Security Agency
The Stuxnet worm is affecting industry control systems worldwide, with over half of the infections occurring in the United States. The work exploits a zero-day vulnerability present in unpatched Windows software, and is targeting supervisory control and data acquisition (SCADA) systems.
Kent Dahlgren, Tripwire
Intelligent situational awareness and cyber-security with the right automated solutions is paramount!
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
CIP Version 4 Vetting Process
• Majority vote of the Ballot Pool of Registered Ballot Body participants.
Industry Approval
• NERC Board of Trustees.• Dissenting & minority positions highlighted with the drafting.
team’s and NERC staff’s comments.
NERC Approval
• Elect to approve as written;• Approve conditionally; or • Reject the standards.
FERC Approval
• Opportunity for industry to file comments.• Comments addressed in the Final Rule.FERC NOPR
6
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Potential FERC Timeline Scenario
NOPR in Federal Register
Industry Comments
Due
Final Order Published in
Federal Register
Effective Date
0 Days 30 Days 120 Days 150 Days
+ 24 months per NERC proposed implementation
plan
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
CIP Version 4 Bright-line Criteria
• Risk-based Assessment is Out.
• Prescriptive Criteria to Define Criticality of Assets is In.
Bright-line Criteria
• 1500 MW Generators.• Transmission Facilities
at 500kv or Higher.• Reliability Coordinator
Control Centers.
Bright-line Examples • Required.
• Identify Compliance Milestones.
• Follow Specific Criteria.
Implementation Plan
8
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Next Practices for Security, Reliability, & Compliance
Prescriptive Risk
Assessment
Identify All Assets
Categorize All Assets with Bright-line
Criteria
9
Prescriptive Controls: “What
to do”
Business Decision: “How to implement
controls”
Validate Security Controls
Document All Steps & Corrective
Actions
Continuously Manage & Monitor
Collect & Retain Data to Identify &
Respond to Security Incidents
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
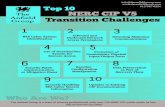
Smart Grid Evolution – Benefits & Challenges
10
Consumer Participation
Optimize Asset
Utilization & Efficiency
Proactive Response to
System Disturbances
Accommodates all generation
& storage options
Provides Quality
Power for Digital
Economy
Enables New Products,
Services, & Markets
Rethink:
Business Practices
Privacy Issues
Threats
Vulnerabilities
Security Controls
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
How do you get started?
Select the right technologies for:• Change control• Log management• Security event monitoring• Tracking & monitoring access to the network
Automate & centralize the CIP compliance process and technologiesWithout security, reliability will suffer
Visibility Intelligence Automation
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
More Prescriptive Guidance
13
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Tripwire Solutions for NERC
An integrated change auditing, configuration control and log management solution
A proven solution for continually monitoring the integrity of files and configurations in SCADA and other mission critical systems
A log management and SIEM solution to monitor and review logs and events of interest
A compliance solution that incorporates specific tests for NERC-CIP or DISA requirements on a number of different platforms:
AIX PowerPC 5.3 systems HP-UX (PA-RSIC) v11 systems Red Hat Linux Solaris SPARC SuSE Linux systems
Windows 2003 servers Win XP Desktops Windows 2003 and Active
Directory domain controllers Windows Server 2000
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Tripwire and Relevant CIPs
CIP-002: Critical Cyber Asset Identification
CIP-003: Security Management Controls
CIP-004: Personnel and Training
CIP-005: Electronic Security Perimeters
CIP-006: Physical Security of Critical Cyber Assets
CIP-007: Systems Security Management
CIP-008: Incident Reporting and Response Management
CIP-009: Recovery Plans for Critical Cyber Assets
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Tripwire and Relevant CIPs
CIP-002: Critical Cyber Asset Identification• R1: Identify Critical Assets and Critical Cyber Assets
CIP-003: Security Management Controls• R5: Document and implement program for managing access to CCA• R6: Change control and configuration management
CIP-005: Electronic Security Perimeters• R2: Control access points into electronic security perimeter • R3: Monitoring electronic access and review and assess logs for unauthorized access• R4: Control default accounts, passwords and network management
CIP-007: Systems Security Management• R1: Changes to CA and CCA don’t affect cyber security controls• R5: Records on user activity to minimize risk of unauthorized system access• R6: Maintain logs of system events related to cyber security and retain logs• R9: Review and update all documentation• Customized: for Security Patch Management | Malicious Software Prevention | Cyber
Vulnerability Assessment
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION18
VIA: Simply Compliant, More Secure.
Pre-Incident
Post-Incident
Implement Secure Configurations
State EventsPolicy
Continuous Monitoring
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Tripwire Enterprise Tripwire Log Center
File Integrity Monitoring
Compliance Policy Manager
Log Manager
SecurityEvent Manager
Tripwire VIATM
VISIBILITY INTELLIGENCE AUTOMATION
Tripwire VIA: Intelligent Threat Control
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
www.tripwire.com/energy-compliance
Join the conversation:
#CIPv4WebcastIT SECURITY & COMPLIANCE AUTOMATION
Additional Thought Leadership
• Summarizes key points• Describes the affect of CIP
compliance vs. noncompliance• Offers a Due Diligence Checklist• Complimentary copy
Join the conversation:
#CIPv4Webcast
Questions
Paul Reymann
(410) 956-7336
James Stanton
(410) 956 7334
Cindy Valladares
Twitter: @cindyv
Join the conversation:
#CIPv4Webcast
www.tripwire.comTripwire Americas: 1.800.TRIPWIRETripwire EMEA: +44 (0) 20 7382 5420Tripwire Japan: +812.53206.8610Tripwire Singapore: +65 6733 5051Tripwire Australia-New Zealand: +61 (0) 402 138 980
THANK YOU!
Cindy [email protected]
@cindyv