Man in-the-middle attack(http)
-
Upload
dawit-tesfayohannes-haile -
Category
Documents
-
view
40 -
download
4
Transcript of Man in-the-middle attack(http)

A5 - SECURITY MISCONFIGURATION
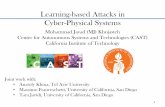
Man-in-the-Middle Attack (HTTP)

Man-in-the-middle attack(http)
The man-in-the middle attack intercepts a communication between two systems.
For example, in an http transaction the target is the TCP connection between client and server.

The MITM(http) attack is very effective because of the nature of the http protocol and data transfer which are all ASCII based.
There are several tools to realize a MITM attack(http). These tools are particularly efficient in LAN network environments.

tcpdump and wireshark are the tools that can be used to attack the victims in the network nodes.
In this scenario is I am using Wireshark, to attack the vulnerability in between the network nods.
Wireshark is a powerful network protocol analyzer. It can go to the deepest level of packet inspection .











Common Weakness Enumeration
CWE-318: Clear text Storage of Sensitive Information in Executable.
Summary: The application stores sensitive information in clear text in an executable.
Extended Description :Attackers can reverse engineer binary code to obtain secret data. This is especially easy when the clear text is plain ASCII. Even if the information is encoded in a way that is not human readable, certain techniques could determine which encoding is being used, then decode the information.