Gartner.mq.Global.mssp.2014
-
Upload
mbaezasoto -
Category
Documents
-
view
218 -
download
0
Transcript of Gartner.mq.Global.mssp.2014
-
8/9/2019 Gartner.mq.Global.mssp.2014
1/23
Magic Quadrant for Global MSSPs
Analyst(s): Kelly M. Kavanagh
Managed security services is a mature market with offerings from established service providers. This
Magic Quadrant presents enterprise buyers with advice on selecting MSS providers to support global
service requirements.
Market Definition/Description
For the purposes of this research, Gartner defines managed security services (MSSs) as "the remote
monitoring or management of IT security functions delivered via shared services from remote
security operations centers (SOCs), not through personnel on-site." Therefore, MSSs do not include
staff augmentation, nor any consulting or development and integration services.
MSSs broadly include:
This Magic Quadrant evaluates monitored/managed firewall and intrusion detection and prevention
Evidence
Ability to Execute
26 February 2014ID:G00247003
VIEW SUMMARY
Monitored or managed firewalls or intrusion prevention systems (IPSs) Monitored or managed intrusion detection systems (IDSs)
Distributed denial of service (DDoS) protection
Managed secure messaging gateways
Managed secure Web gateways
Security information and event management (SIEM)
Managed vulnerability scanning of networks, servers, databases or applications
Security vulnerability or threat notification services
Log management and analysis Reporting associated with monitored/managed devices and incident response
Gartner customer inquiries and information sharing
related to MSSPs
Analyst interactions with Gartner customers via
inquiries and meetings
Survey of MSSPs
Survey of MSS reference customers
Evaluation Criteria Definitions
Product/Service: Core goods and services offered by
the vendor for the defined market. This includes current
product/service capabilities, quality, feature sets, skills
and so on, whether offered natively or through OEM
agreements/partnerships as defined in the market
definition and detailed in the subcriteria.
Overall Viability: Viability includes an assessment of
the overall organization's financial health, the financial
and practical success of the business unit, and the
likelihood that the individual business unit will continue
investing in the product, will continue offering the
product and will advance the state of the art within the
organization's portfolio of products.
Sales Execution/Pricing: The vendor's capabilities in
all presales activities and the structure that supports
them. This includes deal management, pricing and
negotiation, presales support, and the overall
effectiveness of the sales channel.
Market Responsiveness/Record: Ability to respond,
change direction, be flexible and achieve competitive
success as opportunities develop, competitors act,
customer needs evolve and market dynamics change.
This criterion also considers the vendor's history of
responsiveness.
Marketing Execution: The clarity, quality, creativity
http://www.gartner.com/technology/contact/bac/ -
8/9/2019 Gartner.mq.Global.mssp.2014
2/23
(IDP) functions, as well as log management services, rather than other elements of the services we
have listed. Firewall, IDP and log collection form the core of most MSS engagements. The vendors in
the Magic Quadrant are evaluated on their ability to support customers with global service
requirements.
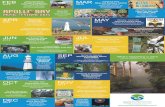
Magic Quadrant
Completeness of Vision
Return to Top
Figure 1.Magic Quadrant for Global MSSPs
and efficacy of programs designed to deliver the
organization's message to influence the market,
promote the brand and business, increase awareness of
the products, and establish a positive identification with
the product/brand and organization in the minds of
buyers. This "mind share" can be driven by a
combination of publicity, promotional initiatives, thought
leadership, word of mouth and sales activities.
Customer Experience: Relationships, products and
services/programs that enable clients to be successful
with the products evaluated. Specifically, this includesthe ways customers receive technical support or account
support. This can also include ancillary tools, customer
support programs (and the quality thereof), availability
of user groups, service-level agreements and so on.
Operations: The ability of the organization to meet its
goals and commitments. Factors include the quality of
the organizational structure, including skills,
experiences, programs, systems and other vehicles that
enable the organization to operate effectively and
efficiently on an ongoing basis.
Market Understanding: Ability of the vendor to
understand buyers' wants and needs and to translate
those into products and services. Vendors that show the
highest degree of vision listen to and understand
buyers' wants and needs, and can shape or enhance
those with their added vision.
Marketing Strategy: A clear, differentiated set of
messages consistently communicated throughout the
organization and externalized through the website,
advertising, customer programs and positioning
statements.
Sales Strategy: The strategy for selling products that
uses the appropriate network of direct and indirect
sales, marketing, service, and communication affiliates
that extend the scope and depth of market reach, skills,
expertise, technologies, services and the customer base.
Offering (Product) Strategy: The vendor's approach
to product development and delivery that emphasizes
differentiation, functionality, methodology and feature
sets as they map to current and future requirements.
Business Model: The soundness and logic of the
vendor's underlying business proposition.
Vertical/Industry Strategy: The vendor's strategy to
direct resources, skills and offerings to meet the specific
needs of individual market segments, including vertical
-
8/9/2019 Gartner.mq.Global.mssp.2014
3/23
Source: Gartner (February 2014)
AT&T
Headquartered in Dallas, and with regional offices in Hong Kong and London, AT&T offers security
monitoring and management services for customer-based and network-based security controls
including wireless in addition to a wide range of other IT and telecommunications services. AT&T
MSSs are based on commercial and self-developed technologies for alert and log collection, real-time
correlation, reporting, and device management. Workflow is supported by the AT&T BusinessDirect
portal. Query and browsing of log data are supported via commercial and self-developed
technologies. AT&T offers log management via on-premises solutions. Log management and MSS
functions must be accessed through separate portals. Integration of these functions into a single
portal remains planned. AT&T's advanced threat offering is the Security Event and Threat Analysis
(SETA) service, which includes correlation and analysis of data from customer devices and the AT&T
network, with customer-specific configuration and response templates. Three SOCs are located in the
U.S., two in Asia/Pacific and one in Europe, and multilingual support is available. Enterprises should
consider AT&T if they require a global service provider with a broad range of service offerings anddeployment capabilities that include premises-based and network-based options. Customers of other
AT&T services that seek MSSs from an incumbent provider should also consider AT&T.
Return to Top
Vendor Strengths and Cautions
Strengths
AT&T has good visibility among Gartner customers, and is often included in competitive MSS
evaluations.
AT&T's network-based security controls are mature security management and monitoring
offerings that are attractive to MSS customers with remote and branch office coverage
requirements.
AT&T is an established and stable service provider, with delivery capabilities in multiple
geographic regions.
Cautions
The MSS portal continues to lack standardized asset reporting as well as the log browsing
capabilities that are available in several competitors' portals.
Log management functions must be accessed from a portal that is distinct from the MSS portal.
The customization features of the MSS portal are not as extensive or self-service-capable as
those in competitors' portals.
Return to Top
markets.
Innovation: Direct, related, complementary and
synergistic layouts of resources, expertise or capital for
investment, consolidation, defensive or pre-emptive
purposes.
Geographic Strategy: The vendor's strategy to direct
resources, skills and offerings to meet the specific needs
of geographies outside the "home" or native geography,
either directly or through partners, channels and
subsidiaries as appropriate for that geography and
market.
-
8/9/2019 Gartner.mq.Global.mssp.2014
4/23
BT
BT is headquartered in London and has offices across the globe, including a regional presence in
Texas and Hong Kong. BT's MSS offerings include monitoring and management of customer premises
deployed devices and network-based security controls as part of its larger portfolio of
telecommunications and IT services. BT uses self-developed technology for log and event collection,
correlation, query, reporting, and device management. Commercial technology supports workflow. In
addition to its MSS, BT offers Assure Analytics, an extension that provides additional analysis and
visualization capabilities. BT has two European SOCs and three Asia/Pacific SOCs staffed 24/7, with
an additional nine SOCs worldwide. Capabilities to detect targeted attacks and provide advanced
analytics are focused on larger customers and delivered via add-on services, including a social mediamonitoring service, Assure Analytics and consulting engagements. Customers of other BT services
that are seeking MSS as well as additional analytics and visualization capabilities should consider BT.
CenturyLinkCenturyLink is based in Monroe, Louisiana, and has offices in Singapore, Hong Kong, London and
throughout North America. It provides MSS as well as infrastructure as a service, software as a
service (SaaS), Web hosting, colocation and network services. MSS customers have primarily been
customers of CenturyLink's infrastructure services. MSS is delivered through a combination of
commercial and self-developed technology for data collection, correlation and analysis, reporting,
and log management. CenturyLink has three SOCs in North America, with an additional SOC in
Europe and one in Asia/Pacific. Advanced analytics to detect targeted attacks are embedded within
the MSS capabilities, and are based on monitoring third-party security technologies. CenturyLink's
infrastructure and network services customers should consider the company for managed security.
Strengths
BT has a broad range of security offerings for MSS globally, as well as for security consulting,
cybersecurity services, secure networking, business continuity, identity and access
management, technology deployment, and integration.
BT gets good marks from users for security expertise in support of its MSS delivery.
Cautions
BT continues to have much lower visibility among MSS buyers in North America and Asia/Pacific
than in Europe.
Customers use the BT Assure Threat Monitoring Web portal for searching, browsing and
reporting security-relevant raw log data, and a premises-based appliance user interface to
access non-security-relevant raw log data.
Return to Top
Strengths
CenturyLink's enterprise and small or midsize business customers for network services can
augment their relationships with CenturyLink via MSSs.
-
8/9/2019 Gartner.mq.Global.mssp.2014
5/23
CSC
CSC is headquartered in Falls Church, Virginia, with regional offices in Sydney, Singapore and the U.
K. CSC delivers its MSS as a stand-alone service, and as a complement to its IT outsourcing and
consulting services to enterprises and government agencies. CSC is in the process of standardizing
its MSS delivery capabilities across all regions using commercial SIEM technology for data collection
and correlation, real-time alert generation, and log management. The self-developed Pulse Portal
provides access to alerts, reporting, ticketing and workflow. CSC has four SOCs in the U.S., two in
Europe and three in Asia/Pacific. New offerings to address advanced targeted attacks are available
and include network and payload analysis. Preliminary endpoint analysis and forensics are available
via managed services, with more in-depth forensics available as a consulting engagement. CSC
outsourcing customers and enterprises, especially those in the defense industrial base and financial
services industries, should consider CSC for MSSs.
CenturyLink's rationalization of security services across its lines of business has enabled a more
focused and consistent delivery of MSSs.
Cautions
CenturyLink does not appear on Gartner customer shortlists for MSSs.
The CenturyLink MSS portal lags competitors' portals in several areas, including customization,
asset tracking, and correlation across data sources and user data.
Return to Top
Strengths
CSC's efforts to standardize MSSs across regions now provide global event visibility to SOC
analysts, and should result in enhanced effectiveness for multiregional customers.
Customers give good marks for the security expertise of CSC's staff, as well as for their
understanding of the customer environment.
CSC's security expertise supports its strong presence in the U.S. federal government and the U.
K. government, in financial services and in critical infrastructure markets.
Cautions
CSC does not fully market its stand-alone MSS. Also, CSC is rarely included on Gartner
commercial customers' shortlists for stand-alone MSS deals.
Organizations considering CSC for MSSs should evaluate the current state and progress toward
the completion of global service standardization to ensure that the capabilities needed in all
regions are available to meet deployment requirements.
Return to Top
-
8/9/2019 Gartner.mq.Global.mssp.2014
6/23
Dell SecureWorks
Dell is headquartered in Texas, and Dell SecureWorks is headquartered in Atlanta, with five regional
offices in the U.S. plus Edinburgh, Scotland, London and Tokyo, with additional offices in Asia/
Pacific and Europe. Dell SecureWorks offers MSSs as well as security consulting, incident response
and threat intelligence services. MSS delivery is based on self-developed technology for log and alert
collection, for real-time correlation and analysis, and for presentation/reporting via portal. Premises-
based log retention and reporting are delivered via commercial SIEM technology. The Dell
SecureWorks Counter Threat Unit provides threat intelligence, malware analysis and analytic support
for MSS operations. Customers may buy threat intelligence services as part of an MSS subscription.
Five SOCs are located in the U.S., with additional SOCs in the U.K., India, Mexico and EasternEurope. Advanced attack detection is offered within existing MSSs and includes threat feeds,
correlation, and analysis of historical events to identify anomalies. Midsize organizations that want to
meet compliance requirements, and enterprises looking for full-featured MSSs, should consider Dell
SecureWorks.
HP
HP is headquartered in Palo Alto, California, with MSS locations in Australia, London and Plano,
Texas. HP has a broad security portfolio of professional and managed services; technologies for
SIEM, application security and network security; and extensive offerings of additional IT products
and services. HP's MSS is based on several self-developed and commercial technologies for data
collection, correlation/alerting, query and reporting. Workflow and ticketing use HP technology, and
Strengths
Dell SecureWorks is very visible to Gartner customers and is typically included in competitive
MSS deals.
Gartner customers offer strong praise for Dell SecureWorks' MSS delivery, security expertise
and relationship management. The security expertise available through the Counter Threat Unit
is often cited as a differentiator.
The MSS portal receives very good marks from customers.
Cautions
Dell's ownership changes offer less visibility into its business operations, including the
positioning and emphasis placed on security products and services.
Although reports of issues to Gartner have been minimal to date, customers should continue to
monitor Dell SecureWorks' service delivery to ensure that MSS geographic expansion and any
shift in Dell's business focus do not dilute its MSS delivery capabilities.
Dell SecureWorks' cautious expansion beyond the Japanese market may result in prospects
having limited references in the Asia/Pacific region, and not as much ready access to presales
interaction.
Return to Top
-
8/9/2019 Gartner.mq.Global.mssp.2014
7/23
tools for customer deployment provide workflow support. HP has two SOCs in the U.S., one in Latin
America, three in Europe and two in Asia/Pacific. HP offers a portal for MSS and uses the HP ArcSight
console for log management. HP offers a separate governance, risk and compliance-oriented portal
for executive dashboards. The HP MSS portal provides role-based access, ticketing and security
reporting features. Log management is delivered via HP ArcSight ESM and ArcSight Logger in hosted
or on-premises deployments. Log management features are available via the HP ArcSight portal.
HP's targeted attack detection and advanced analytics capabilities are embedded in its MSS offerings,
and are supported with threat feeds, vulnerability information, the detection capabilities of HP
ArcSight, and expert analysis. Enterprises and midsize companies with HP IT services or security
technology services should consider HP for MSSs.
IBM
IBM is headquartered in New York, with MSS offices in Atlanta and other geographies. MSSs and a
full range of security consulting and integration services are available as stand-alone services, and as
components of larger infrastructure outsourcing contracts. IBM uses self-developed technology for
data collection, correlation, log query and reporting, and ticketing/workflow. Log management is
offered as a hosted service, and with premises-based IBM QRadar and other SIEM technologies. IBM
has four North American SOCs, two in Europe, two in Asia/Pacific and two more in other regions.
IBM's advanced analytics and targeted attack detection capabilities are embedded in its MSS and
hosted SIEM offerings, and they are supported by IBM technology and third-party technology
deployed by customers. Enterprises with global service delivery requirements, and those withstrategic relationships with IBM, should consider IBM for MSSs.
Strengths
HP is a large, stable provider of MSSs and other security services. It has a multiregional
presence and delivery capabilities.
HP's broad technology and service delivery options enable extensively customized MSS
engagements, including technology bundling and hybrid delivery options.
Cautions
The HP MSS portal lacks the user correlation and asset and vulnerability reporting capabilities
that are available in competitors' portals. Potential customers should validate that HP's current
capabilities and enhancement plans meet their deployment and operations requirements.
Gartner customers report challenges in differentiating and navigating among HP's security
monitoring capabilities, which are available, in differing forms, from HP's product, outsourcing
and discrete MSS delivery organizations.
Prospective MSS customers should validate HP's coverage and monitor ongoing support when
MSS engagement includes security technologies from HP's competitors.
Return to Top
Strengths
-
8/9/2019 Gartner.mq.Global.mssp.2014
8/23
NTT
NTT, which is based in Tokyo, and with London and New York offices, acquired Solutionary in 2013,
adding to prior acquisitions of MSS capabilities in the NTT companies (such as NTT Com Security
formerly Integralis and Dimension Data's earthwave). NTT is included in this Magic Quadrant on
the basis of the combined offerings and scale of the various MSS entities, which it is in the process of
rationalizing. NTT uses a variety of self-developed and commercial technologies to support MSS
delivery across the three organizations. There are multiple SOCs in Asia/Pacific, Europe and North
America. Targeted attack protection is embedded in the MSS offering of each delivery group, and it
differs among the groups, although cross-group data sharing for threat information is now being
done. NTT customers and enterprises seeking a large global service provider with specific regional
strengths should consider NTT for MSSs.
Gartner customers often include IBM in competitive MSS evaluations, and IBM has high visibility
in North American, Asia/Pacific and European markets.
IBM's MSS capabilities include support for customer-deployed SIEM (from IBM and other
vendors) that is integrated into its standard MSS offerings.
IBM is a large, stable provider of security and IT services and products, and it has global
delivery capabilities.
Cautions
Gartner customers report overall improvements and lingering challenges for IBM MSSs in sales,deployment and customer care.
Although IBM's MSS supports multiple security technologies including many from IBM's
competitors in the IPS and SIEM markets MSS customers should monitor planned and actual
MSS support for the security technologies deployed in their environments.
Return to Top
Strengths
Individual NTT MSS groups get good feedback from Gartner customers regarding MSS delivery.
Across the NTT MSS offerings, the capabilities of NTT Com Security, Solutionary, Dimension
Data's earthwave and NTT Data are well-known in Europe, North America, the Middle East/
Africa and Asia/Pacific, respectively, and they appear in MSS deals in those regions.
NTT has a global presence as well as a broad range of security service offerings and delivery
options, in addition to broader telecommunications and IT infrastructure service offerings.
Cautions
MSS operations across the regions are not yet fully integrated. Current MSS customers must
monitor NTT's plans to rationalize its MSS delivery capabilities to ensure that any changes
result in equal or better service delivery levels and options.
-
8/9/2019 Gartner.mq.Global.mssp.2014
9/23
Orange Business Services
Headquartered in Paris, with offices in Atlanta and Singapore, Orange offers a broad range of
telecommunications and cloud-based IT infrastructure services, security consulting and integration
services, and MSSs. Orange MSSs are based on commercial SIEM technology for data collection,
correlation and analysis, reporting, and log management, with self-developed technology for
workflow. Three MSS SOCs are located in Europe, two in Asia/Pacific, one in North America and two
in the Middle East/Africa regions. Advanced threat detection is provided by proprietary technologies
as well as by commercial SIEM and network security products, with additional capabilities planned for
2014. Orange service customers and organizations seeking a large, global and stable Europe-focused
and Asia/Pacific-focused MSS provider (MSSP) should consider Orange.
Symantec
Symantec is headquartered in Mountain View, California, with MSS offices in Virginia, Singapore and
Reading, U.K. Symantec offerings include security monitoring, security intelligence, messaging
security services and a range of security products. Symantec's MSS architecture is based on self-
developed technology for event and log collection, with a combination of self-developed and
commercial technology for correlation, analytics and reporting. Ticketing/workflow and device
management are based on commercial technology. Log query and browsing are enabled via self-
developed technology. Symantec has one SOC in the U.S., one in the U.K. and two in Asia/Pacific,
plus a new SOC in Japan. Log management services are delivered via Symantec log collection
Potential MSS buyers should get binding assurances from NTT regarding the capabilities they
will receive globally and within regions to ensure that NTT's current and planned MSS
capabilities will meet customers' region-specific and global requirements.
Return to Top
Strengths
Orange offers a broad range of network and IT services that can be bundled with MSSs.
Orange is a large, stable service provider with long-standing MSS and security consulting
experience.
Cautions
Orange has lagged several MSS competitors in the introduction of advanced attack detection
and analytics offerings.
Orange rarely appears on Gartner customer shortlists for MSS procurement, and in North
America, Orange has very limited market visibility.
MSS customers in North America often express a preference for a SOC in-region. Although
Orange has a North American SOC, it is not staffed 24/7.
Return to Top
-
8/9/2019 Gartner.mq.Global.mssp.2014
10/23
platform, are stored in Symantec SOCs and are available to customers via the MSS portal. A distinct
service level offers advanced attack detection analytics. Enterprises seeking an established MSSP
should consider using Symantec.
Trustwave
Trustwave is based in Chicago, with offices in London and Sydney. Trustwave has several security
technologiesincluding SIEM, unified threat management (UTM), network access control,
application security, Web application firewall (WAF) and Web security and builds MSSs around
those as well as third-party products. MSSs are based on Trustwave's SIEM technology for data
collection, correlation, alerting and workflow. Security intelligence capabilities are provided by the
Trustwave SpiderLabs group. Trustwave has three U.S.-based SOCs, one in Europe and one in Asia/
Pacific. Targeted attack detection and advanced analytics capabilities are standard components of
Trustwave MSSs, and they are delivered via three Trustwave activities: network monitoring, endpoint
monitoring and managed WAF. Companies in the retail, healthcare and banking vertical industries
and others that are subject to PCI compliance should consider Trustwave for MSSs.
Strengths
Symantec has strong visibility in the MSS market. Gartner customers very often consider
Symantec's MSS offerings in competitive evaluations.
Symantec's Gartner customers generally offer positive reviews of Symantec's MSS delivery, and
of the quality of their interactions with Symantec's SOC analysts.
MSS customers indicate that the DeepSight threat feeds and intelligence reports are
differentiators of Symantec's services.
Cautions
Prospective buyers should evaluate Symantec's optional enterprisewide pricing with realistic
assumptions of the number of monitoring/log sources they can expect to incorporate into the
scope of MSSs. Customer delays in bringing event sources into coverage will result in buyers
paying for coverage that they are unable to receive.
Symantec is rebuilding its security consulting capability. Prospective MSS customers should
carefully evaluate whether Symantec's security consulting services will meet their needs, andwhether they must engage with partner-led security services for service initiation and for
ongoing project work throughout the course of the MSS relationship.
Return to Top
Strengths
Trustwave has an extensive portfolio of security products and associated managed services that
can be packaged as subscription-based solutions for customers with limited capital budgets andsecurity resources.
Trustwave remains a well-recognized provider of services and technologies to support PCI Data
-
8/9/2019 Gartner.mq.Global.mssp.2014
11/23
Verizon
Verizon is headquartered in Basking Ridge, New Jersey, with offices throughout the U.S., Europe,
Latin America and Asia. Verizon offers MSSs and security consulting, as well as a broad range of
telecommunications and infrastructure services. Verizon's MSS architecture is based on self-
developed technologies for event collection, correlation and alerting, with commercial technologies
for reporting and workflow. Log management services are based on a combination of self-developed
and commercial technologies. Two SOCs are located in the U.S., two in Europe and two in Asia/
Pacific. Verizon's Research, Investigations, Solutions, Knowledge (RISK) Team provides threat
intelligence and malware detection signatures that support MSSs, and Verizon's breach response
services inform MSS monitoring efforts. Targeted threat detection services are incorporated into the
standard MSS delivery. They are based on commercial technologies, on Verizon's self-developed
correlation and threat intelligence capabilities, and on network monitoring. A distinct advanced
analytics service is available in the U.S. to governments and enterprises facing specific targeted
threats. Enterprises should consider Verizon if they are looking for an established service provider
that is capable of delivering a broad range of security services in multiple regions.
Security Standard (DSS) compliance.
The Trustwave MSS portal provides extensive language support.
Cautions
Current customers and potential MSS buyers should continue to monitor Trustwave's ability to
meet delivery and road map commitments as it navigates a possible initial public offering.
Potential MSS customers should evaluate whether the split of compliance reporting capabilities
between the MSS portal and the log management portal meets their operational requirements.
The Trustwave MSS portal lags several competitors' portals in providing correlation of useractivities with infrastructure events.
Except for PCI monitoring engagements, Trustwave very rarely appears in MSS deals among
Gartner customers.
Return to Top
Strengths
Verizon's network-based capabilities enable MSS configuration that includes network-based and
premises-based controls.
Gartner customers often include Verizon in competitive MSS evaluations.
Verizon's MSS receives generally positive reviews from Gartner customers for meeting their
expectations for security expertise, and for effective security monitoring and alerting.
Customers also indicate that Verizon's security expertise is a differentiator for MSSs.
Cautions
-
8/9/2019 Gartner.mq.Global.mssp.2014
12/23
We review and adjust our inclusion criteria for Magic Quadrants and MarketScopes as marketschange. As a result of these adjustments, the mix of vendors in any Magic Quadrant or MarketScope
may change over time. A vendor's appearance in a Magic Quadrant or MarketScope one year and not
the next does not necessarily indicate that we have changed our opinion of that vendor. It may be a
reflection of a change in the market and, therefore, changed evaluation criteria, or of a change of
focus by that vendor.
NTT was added to this Magic Quadrant based on its acquisition of Solutionary, and on the prioracquisitions of Integralis (now NTT Com Security) and Dimension Data's earthwave. NTT's
capabilities across these organizations meet the criteria for inclusion in the Magic Quadrant.
Orange Business Systems was added because it also meets the inclusion criteria.
Allstream, Bell Canada, CGI, Clone Systems, Nuspire Networks and Perimeter E-Security (now
named SilverSky) were dropped from this Magic Quadrant because they do not meet the inclusioncriteria for network devices and customers monitored/managed in Europe and Asia/Pacific.
Wipro was dropped because it does not meet the inclusion criteria for customers in Asia/Pacific or
North America.
HCL Technologies was dropped because it is in the process of realigning its MSS capabilities and
currently does not meet the inclusion criteria for this research.
SAIC was dropped because of its split into two companies, SAIC and Leidos, and because the MSS
business of Leidos does not meet the inclusion criteria for customers in Asia/Pacific and Europe.
Verizon's MSS portal lacks the user activity correlation capabilities that are available from
several competitors.
Verizon's log management services currently lag those of its competitors. New capabilities are
planned for 1Q14.
Return to Top
Vendors Added and Dropped
Return to Top
Added
Return to Top
Dropped
Return to Top
-
8/9/2019 Gartner.mq.Global.mssp.2014
13/23
Inclusion and Exclusion Criteria
This Magic Quadrant expands the coverage from MSSPs in North America to include delivery
capabilities in North America, Europe and Asia/Pacific. As a remote service, MSSs can be delivered
via network connectivity to and from any locations with sufficient connectivity, and certainly MSSPs
that have operations in one geographic region can support customers in other regions. Gartner sees
a distinct preference among customers seeking MSSs to first consider MSSPs with a presence in their
region. Among global enterprises, that includes a presence in multiple regions where the enterprises
operate, in order to provide more "local" support and also includes the MSSP's ability to keep
some data in specific regions, provide local business hours, provide access to advanced support, and
provide local language support, among other concerns. In addition, compliance with data residency
and privacy regulations can be addressed in many cases with local operations centers.
This Magic Quadrant includes MSSPs that have met thresholds for scale (expressed as devices
supported and customers) and presence (SOCs) in multiple regions, as well as a threshold for MSS
revenue.
The criteria include a threshold for the number of firewalls or IDP devices under monitoring or
management, and a threshold for the number of MSS customers both distributed across multiple
regions. MSSs refer to remote management and monitoring of security technologies. Several large
infrastructure outsourcing vendors offer other service delivery options (such as staff augmentation)in addition to MSSs, but we don't evaluate these other delivery options. Also excluded from this
analysis are service providers that offer MSSs only as a component of another service offering (such
as bandwidth or hosting), and vendors that provide MSSs only for their own technologies, not for
third-party technologies.
Vendors must have:
Return to Top
2013-2014 Global MSSP Magic Quadrant Inclusion Criteria
The ability to remotely monitor and/or manage firewalls, IDP devices from multiple vendors via
discrete service offerings, and shared service delivery resources
Firewalls/IDP devices under remote management or monitoring for external customers
External customers with those devices under management or monitoring
Reference accounts that are relevant to Gartner customers in the appropriate geographic
regions
A threshold of the number of customers as well as the number of firewalls and IDS/IPS devices
in multiple geographies
A threshold for MSS revenue of $20 million in 2012
A SOC presence in multiple geographic regions
-
8/9/2019 Gartner.mq.Global.mssp.2014
14/23
Inclusion thresholds for firewalls/IDP devices under MSSs are 225 in Asia/Pacific, 1,500 in Europe,
2,250 in North America and 25 in the rest of the world (ROW), in the following possible
combinations:
Inclusion thresholds for MSS clients are 45 in Asia/Pacific, 75 in Europe, 225 in North America and 10
in ROW, in the following possible combinations:
Vendors have:
Evaluation Criteria
Asia/Pacific + Europe
North America + ROW
Asia/Pacific + North America
Europe + North America
Asia/Pacific + Europe
North America + ROW
Asia/Pacific + North America
Europe + North America
Return to Top
2013-2014 Global MSSP Magic Quadrant Exclusion Criteria
Service offerings that are available only to end users that buy other non-MSS services
Services that monitor or manage only their own technology
Services delivered by their own resources and dedicated to a single customer
Return to Top
Ability to Execute
Product or servicerefers to the service capabilities in areas such as event management and
alerting, information and log management, incident management, workflow, reporting, and service
levels.
Overall viabilityincludes the organization's financial health, the financial and practical success of
the overall company, and the likelihood that the business unit will continue to invest in the MSS
offering.
Sales execution/pricingincludes the service provider's success in the MSSP market and its
bili i i l i i i hi l i l d SS i i d h ll
-
8/9/2019 Gartner.mq.Global.mssp.2014
15/23
Source: Gartner (February 2014)
capabilities in presales activities. This also includes MSS revenue, pricing and the overall
effectiveness of the sales channel. The level of interest from Gartner clients is also considered.
Market responsiveness/recordevaluates the match of the MSS offering to the functional
requirements stated by buyers at acquisition time. It also evaluates the MSSP's track record in
delivering new functions when the market needs them.
Marketing executionis an evaluation of the service provider's ability to effectively communicate
the value and competitive differentiation of its MSS offering to its target buyer.
Customer experienceis an evaluation of the service delivery to customers. The evaluation includesease of deployment, the quality and effectiveness of monitoring and alerting, and reporting and
problem resolution. This criterion is assessed by conducting qualitative interviews of vendor-provided
reference customers, as well as by feedback from Gartner customers that are using the MSSP's
services, or have completed competitive evaluations of the MSSP's offerings.
Operationsincludes the MSSP's service delivery resources, such as infrastructure, staffing and
operations reviews or certifications.
Return to Top
Completeness of Vision
Market understandinginvolves the MSSP's ability to understand buyers' needs and to translatethem into services. MSSPs that show the highest degree of market understanding are adapting to
customer requirements for specific functional areas and service delivery options.
Table 1.Ability to Execute Evaluation
Criteria
Evaluation Criteria Weighting
Product or Service High
Overall Viability High
Sales Execution/Pricing Medium
Market Responsiveness/Record Medium
Marketing Execution Medium
Customer Experience High
Operations Medium
k i f l d ff d f h l
-
8/9/2019 Gartner.mq.Global.mssp.2014
16/23
Source: Gartner (February 2014)
Marketing strategyrefers to a clear, differentiated set of messages that is consistently
communicated throughout the organization; is externalized through the website, advertising,
customer programs and positioning statements; and is tailored to the specific client drivers and
market conditions in the MSS market.
Sales strategyrelates to the vendor's use of direct and indirect sales, marketing, service, and
communications affiliates to extend the scope and depth of market reach.
Offering (product) strategyis the vendor's approach to product development and delivery that
emphasizes functionality and delivery options as they map to current and emerging requirements for
MSSs. Development plans are also evaluated.
Business modelincludes the process and success rate for developing features, innovations and
service delivery capabilities.
Vertical/industry strategyand geographic strategyinclude the ability and commitment to
service geographies and vertical markets.
Innovationrefers to the service provider's strategy and ability to develop new MSS capabilities and
delivery models to uniquely meet critical customer requirements.
Return to Top
Quadrant Descriptions
Table 2.Completeness of Vision
Evaluation Criteria
Evaluation Criteria Weighting
Market Understanding High
Marketing Strategy Medium
Sales Strategy Medium
Offering (Product) Strategy High
Business Model Low
Vertical/Industry Strategy Medium
Innovation High
Geographic Strategy Medium
Leaders
-
8/9/2019 Gartner.mq.Global.mssp.2014
17/23
Each of the service providers in the Leaders quadrant has significant mind share among enterprises
looking to buy an MSS as a discrete offering. These providers typically receive very positive reports
on service and performance from Gartner clients. MSSPs in the Leaders quadrant are typically
appropriate options for enterprises requiring frequent interaction with the MSSP for analyst expertise
and advice, for portal-based correlation and workflow support, and for flexible reporting options.
In the Challengers quadrant, Gartner customers are more likely to encounter MSSs that are offered
as components of an IT or network service provider's other telecommunications, outsourcing or
consulting services. Although an MSS is not a leading service offering for this type of vendor, it offers
a "path of least resistance" to enterprises that need an MSSP and use the vendor's main services.
Companies in the Visionaries quadrant have demonstrated the ability to turn a strong focus on
managed security into high-quality service offerings for the MSS market. These service providers are
often strong contenders for enterprises that require frequent interaction with MSS analysts, flexible
service delivery options and strong customer service. MSSPs in the Visionaries quadrant have less
market coverage and fewer resources or service options compared with vendors in the Leaders
quadrant.
Niche Players are characterized by service offerings that are available primarily in specific market
segments, or primarily as part of other service offerings. These service providers often tailor MSS
offerings to specific requirements of the markets they serve.
Context
Prospective MSS buyers with threat management use cases should highly weight MSSPs' threat
research and security intelligence capabilities.
Current and prospective MSS users should require a proof of concept, or a demonstration of MSS
offerings for advanced analytics and big data, to validate effectiveness and value.
Current and prospective MSS users should validate MSSPs' services that are related to monitoring or
Leaders
Return to Top
Challengers
Return to Top
Visionaries
Return to Top
Niche Players
Return to Top
management of third party technologies or their own technologies to address advanced attacks
-
8/9/2019 Gartner.mq.Global.mssp.2014
18/23
management of third-party technologies or their own technologies to address advanced attacks.
Market Overview
The MSS market is mature, and prospective customers have numerous options among MSSPs and
the types of services offered. The primary drivers for MSSs have been consistent for several years:
24/7 threat management and meeting compliance requirements. These may be complemented by
related drivers, such as the desire to redirect existing resources to other security areas, or the need
to engage deeper or broader expertise than is available in-house. An emerging driver is support for
the protection from and detection of targeted attacks through MSSP knowledge of the external threat
environment, through insight gained from monitoring events from a broad and global customer base,
through MSSP-based advanced analytics, or through MSSP monitoring of customer-deployed next-
generation protection and detection capabilities.
The 2013-2014 Magic Quadrant for Global MSSPs reflects multiregional delivery requirements, and
the MSSPs included in the evaluation meet the minimum thresholds for MSS business in two or more
regions. MSSPs with multiregional business typically have a sufficient understanding of region-
specific customer requirements, as well as sufficient service delivery capabilities that can scale to
support global service delivery. Customers with a mix of global delivery requirements and localregulatory requirements related to, for example, data privacy, may require customized services.
MSSPs that do not meet the customer or device thresholds for inclusion in this Magic Quadrant may
still deliver high-quality services within a region, and can typically deliver in multiple regions. When
considering MSSs, Gartner customers should develop evaluation criteria that meet their specific
requirements.
Gartner expects that growing enterprise experience with cloud-based infrastructure and applications
delivered as a service, as well as accommodating the access of consumer technology to corporate
systems, will result in greater acceptance of, and reliance on, cloud-based security-as-a-service
offerings.
In 2013, the global market for security outsourcing was $12 billion, with a forecast compound annual
growth rate of 15.4% through 2017.
Growth in enterprise demand for MSSs is driven primarily by four factors:
Return to Top
Security staffing and budget constraints:Gartner sees continued expectations to reduce
operational costs and capital expenditures, and to avoid staffing increases related to the
monitoring and management of mature security technologies, such as IDSs and firewalls. At the
same time, increased monitoring of infrastructure logs, as well as privileged and application
user activity and next-generation technologies, requires tool and analytical expertise that will
be difficult for many organizations to supply in-house.
Evolving compliance reporting requirements:This involves the evolution of existing
compliance requirements and of corporate governance policies that create a secondary effect
-
8/9/2019 Gartner.mq.Global.mssp.2014
19/23
MSS growth can also be constrained by a few factors:
The services that are core to MSS offerings involve the monitoring of perimeter network security
technologies:
Return to Top
MSS Portfolio
compliance requirements, and of corporate governance policies that create a secondary effect
of stronger requirements for incident monitoring, identification, and response internally and
among business partners. As formal compliance regimes evolve or audit/enforcement activity
increases, organizations consider external service providers to reduce the costs of meeting
compliance requirements. PCI DSS remains an important driver; also, Gartner is starting to see
the U.S. Federal Information Security Management Act's (FISMA's) continuous monitoring
requirements become an increasing factor for U.S. government agencies, for commercial firms
that sell to the U.S. government, and for organizations funded by government grants, such as
universities.
Adoption of security technologies and analytic tools focused on advanced attacks:As
enterprises gain experience with technologies to analyze networks, payloads and endpoints for
advanced attacks, they will look for opportunities to focus internal resources on prevention and
response activities, and to augment those activities with external expertise to monitor and
manage the technologies.
Increased availability and adoption of cloud-based IT services:Increasing use of cloud-
based IT services will drive security controls into those services, and will also lead to greater
acceptance and adoption of cloud-based security services for controls that are best suited for
cloud-based delivery. Gartner expects significant security outsourcing growth in areas adjacent
to MSSs, such as secure Web gateways, email security, and identity and access management.
Enterprise deployment of SIEM technology to provide in-house alerting and log
analysis:MSSPs typically lack deep insight into the customer IT and business environment;
thus, they are less able to determine whether events involving users, administrators, internal
applications and data are inappropriate or unacceptable. Wherever enterprises want close
monitoring of internal activities, they may opt to do it themselves. Some organizations monitor
internal activities and also use an MSSP for external/perimeter monitoring. Such an
arrangement still constrains the growth of MSSs in those organizations.
Core competency:Organizations that provide security technology or services, or position their
technology or services as secure, are likely to forgo outsourced security monitoring. Where
security is a value proposition and a core competence, outsourcing security may not be an
effective option.
Change in strategy to reduce outsourcing:At the enterprise level or within the security
organization, a change in strategy regarding the use of external services can mean that MSSs
are not considered effective options.
-
8/9/2019 Gartner.mq.Global.mssp.2014
20/23
In addition to monitoring, many MSSPs have management services for those technologies. It is
increasingly common for MSSPs to also provide monitoring and log collection from IT infrastructure
such as servers, user directories and applications.
Among organizations that have deployed SIEM technology, Gartner sees increasing interest for
services to monitor or run the SIEM. Several MSSPs have offerings to support customer-deployed
SIEM.
MSSPs may also provide cloud or SaaS-based services, including:
MSSPs offer cloud services directly or via partnerships with other service providers. The degree of
integration of partner-delivered services with MSSP services varies from little more than purchasing
convenience to integration of partner data and management functionality into the MSSP's portal.
Deeper integration can provide operational and vendor management advantages, but may reduce
the ability to "swap out" one cloud-based service for another.
Buyers should take into consideration the degree of integration of any partner-delivered services
with the MSSP's offering, as well as the potential for affecting training, operational efficiency and end-
of-contract switching costs.
Several MSSPs have created research groups to improve their understanding of the threat landscape
that is, the identities, motives, targets and techniques of attackers. MSSPs use their findings to
support their security operations analysts; they may also provide customers with subscription-based
access to this research, or offer customers project-based access to the group for analysis/reverse
engineering of malware. Potential customers of threat intelligence feeds from MSSPs should require
Firewalls
IDSs/IPSs
Multifunction firewalls/UTM services
Next-generation firewalls
WAFs
DDoS protection
Email security
Web filtering
Vulnerability scanning
Network-based firewall/IDP
Return to Top
Threat Intelligence and Advanced Analytics
proof-of-concept access to evaluate the relevance of the information as well as their ability to
-
8/9/2019 Gartner.mq.Global.mssp.2014
21/23
proof of concept access to evaluate the relevance of the information, as well as their ability to
consume and act on it.
Many MSSPs claim capabilities to assist their customers in addressing advanced targeted attacks.
These capabilities may be visible as discrete service offerings or options, or as features embedded in
existing offerings. They may include, for example:
These offerings are now primarily based on the security events monitored by the MSSPs; however,
we expect that several MSSPs will introduce distinct service offerings to acquire, retain and analyze
large volumes of customer data so called "security big data" from IT infrastructure and other
sources. Gartner recommends that customers require a limited pilot or proof of concept to identify
specific areas where relevant, actionable intelligence results from the collection and analysis of the
data, and to identify the service levels required. Based on feedback from Gartner customers, early
adopters should plan for the inclusion of relevant domain experts who are typically outside the
security group, such as line-of-business owners and application owners.
Most MSSPs also offer incident response capabilities to assist customers with investigation and
remediation activities in the event of a breach. These services are typically available on a consulting
basis. Prospective customers should confirm with MSS candidates how much response support is
available within the context of the standard monitoring services, and when a consulting engagement
is required. If the MSSP offers packaged or prepaid hours for incident response activities, then
customers should ensure that those hours are available for other security services if they are not
needed for incident response.
The typical pricing model for MSSs is based on the type and size of the security technology to be
monitored for customer-premises-equipment-based devices, or on the bandwidth or number of users/
endpoints for network-based controls. Log collection is typically priced by the number and types of
sources, or on events per time period (device count pricing includes implicit expectations of event
volumes). There is typically a clear distinction between technology that is monitored in real time, and
subject to alerting service-level agreements (SLAs), and technology that is not that is, where logs
are collected and subject to reporting or querying, but not to real-time correlation and analyst
review. Device management pricing is typically based on the number of configuration changes to be
performed within a period of time.
Correlation of alerts with IP reputation or known bad addresses
Comparison of alerts, activity patterns or state (such as device configuration, registry and so
on) to those of known attacks
Analysis of activity patterns (across an MSS customer base as well as within the customer
environment) to identify outliers, exceptions or deviations from baselines
Return to Top
Pricing Models
During 2014, Gartner expects the trend for common services, such as firewall and IDP monitoring
-
8/9/2019 Gartner.mq.Global.mssp.2014
22/23
During 2014, Gartner expects the trend for common services, such as firewall and IDP monitoring
and management, to decline slightly. Price pressure is coming from new sources for these services,
such as from the technology providers themselves, from other MSSPs and from continued corporate
efforts to reduce IT budgets. In response, MSSPs have introduced new services to monitor and
manage advanced threat detection technologies. MSSPs will continue trying to expand the number of
devices and data sources to monitor, and will differentiate monitoring based on the availability of
additional external intelligence feeds and analysis (such as reputation data, blacklists, behavioral
data and cross-customer activity) that can be correlated with data from customers' monitored
devices.
The basic makeup of the MSSP vendor space has not changed fundamentally. There are three major
types of MSSPs:
This Magic Quadrant reflects the requirements of customers that seek MSSPs with a global presence
and global delivery capabilities. The vendors that meet those requirements fall into the latter two
types of MSSPs.
In general, the MSS portfolios of these providers look broadly similar. Customer satisfaction with
services can be strongly related to customer expectations. Customers occasionally report
dissatisfaction related to objectively poor performance, including missed SLAs. However, it is more
common for dissatisfied customers to express disappointment related to subjective criteria that may
never have been made explicit to prospective providers, or to the MSSP selected.
Gartner customers using MSSPs express differing expectations regarding their type of relationship
with MSSPs. Expectations may range from frequent interactions and knowledge sharing among the
customer security staff and MSSP staff, to almost no interactions beyond the provision of periodic
reports of monitoring activity. Gartner recommends that prospective MSS buyers develop explicit
Return to Top
MSSP Landscape
Pure plays:These are generally smaller, privately held MSSPs that are completely focused on
security services. As seen in 2013, pure-play MSSPs will continue to be acquired by larger
service or IT infrastructure firms that seek to provide MSSs. New pure-play security service
providers often focus on specific vertical markets or regulatory requirements, or on specificanalytic services (such as user activity) or advanced threat detection technologies.
System integrators/business process outsourcers:These are broad IT service providers
that typically manage security devices as part of larger outsourcing deals. Where the integrator
or outsourcer acquired a pure-play MSSP and maintained a discrete MSS delivery capability,
these providers often compete for MSS-only deals.
Carriers and network service providers:These are bandwidth and connectivity providers
that manage network security products. They often provide remote monitoring, premises-based
technologies and cloud-based services through their Internet connections.
-
8/9/2019 Gartner.mq.Global.mssp.2014
23/23




![[XLS] · Web view7540 1/16/2014 7541 1/16/2014 7542 1/16/2014 7543 1/16/2014 7544 1/16/2014 7545 1/16/2014 7546 1/16/2014 7547 1/16/2014 7548 1/16/2014 7549 1/16/2014 7550 1/16/2014](https://static.fdocuments.us/doc/165x107/5b279c517f8b9a65538b64cc/xls-web-view7540-1162014-7541-1162014-7542-1162014-7543-1162014-7544.jpg)