Fact or Fiction: IBM i has Never Been Hacked
Transcript of Fact or Fiction: IBM i has Never Been Hacked
WhyareWeTalkingAboutThis?
An“AS/400”washacked– asdocumentedinthearticle,“smokeontheWater[plant]inthe“DataBreachDigest”fromVerizon.
WhatHappened?
Ahackerwasabletomakeuseofaknownvulnerabilityinthepayment(creditcard)software
Over2.5millionrecordswereexfiltrated
TheAS/400administrator’suseridandpasswordwerestoredincleartext(anddiscovered)inan.inifileonawebserverrunningontheAS/400.ThesewereusedtogainaccesstotheSupervisoryControlandDataAcquisition(SCADA)applicationwhichcontrolsthecommunity’swatersupply.
Themixtureofchemicalsgoingintothewatersupplywasmanipulated,affectingtimestoreplenishwatersupplies
Nonetworksegmentationexisted.Theorganization’sAS/400wasdirectlyattachedtotheInternetandtheinternalnetworkwasexposed.
“IThoughtWeWereAlreadySecure!”
IBM i has a well-deserved reputation as one of the most securable operating systems available.
But, securable does not imply you simply plug in the system and take no further action.
It takes a joint effort by:IBM (who supplies the OS),Your software vendors (who supply the application),And YOU (who has ultimate responsibility for the server and data)
Securable Secure
So,whatwastheCause?
Failureto:UsethefeaturesreadilyavailableinIBMiFollowanysortofsecurity‘bestpractices’
Thewrite-upclearlypointedoutthatthesingleAS/400administratormadenoconsiderationforthesecurityimplicationsoftheconfigurationsettingschosen
KeepapplicationspatchedUsecommonsense!
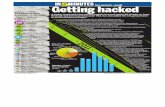
TypesofHackers
Drive-byExploitingknownvulnerabilitiesTargetedattack
Nation-state,Professionalhackers,Hackivists
PonemonInstitute– 2016CostofInsiderThreats
ThreetypesofinsiderthreatsAcarelessornegligentemployeeorcontractorAcriminalormaliciousinsiderAcredentialthief
2016CostofInsiderThreats– Interestingfacts
Totalnumberofbenchmarkedorganizations– 54Totalnumberofinsiderincidents– 874Percentagebytype:
Negligence- 68%(averageperincident$206,933)Criminalinsider– 22%(averagecostperincident$347,130)Credentialtheft– 10%(averagecostperincident$493,093)
ModifiedIBMiProfiles
AdditionalspecialauthoritiesareoftengrantedtoIBMi-providedprofiles:QSYSOPRQUSERQPGMR
Orprivateauthoritiesaregrantedor*PUBLICauthorityischangedto*USEorgranter.
IBMi-suppliedProfileswithaPassword
IBMi-suppliedprofileshaveshippedwithoutapasswordformany,manyyears.WhileQSECOFRmusthaveapassword,theothersshouldnot.Well-knownprofiles:QUSERQSYSOPRQSRVQSRVBASQPGMR
New*ALLOBJProfiles
Nomonitoringorrecognition/approvalofnewprofileswith*ALLOBJ(andotherspecialauthorities)ServiceaccountsCopiedprofilesVendorprofiles
Takecontrolofvendoraccess!
DefaultPasswords
PasswordsthesameastheuserprofilenameProfilecreationprocessServiceaccountsVendorprofilesNopasswordrules
Specify:QPWDRULESandinclude*LMTPRFNAMEand*ALLCRTCHG(V7R2)
ServiceAccounts
Serviceaccountsareoftenautomaticallycreatedwith*ALLOBJ(andoften,allspecialauthorities)becausenooneissurewhatauthorityisrequired.InV7R3,usetheauthoritycollectionfunctiontodeterminetheauthorityrequired.Inpriorreleases,maketheserviceaccountamemberoftheapplicationowningprofileifitneeds*ALLauthoritytoapplicationobjects
Thisisabetteroptionthangrantingtheserviceaccount*ALLOBJspecialauthority.
DevelopmentNotSecuredLikeProduction
Whetherauditorslikeit(ornot)productiondataoftenresidesonDevelopmentLPARs.DevelopmentisrarelysecuredthesameasProduction
Developersoftenhave*ALLOBJObjectauthoritiesrarelymatch
OptionsRCACtomaskthedata(V7R2)
http://www.redbooks.ibm.com/redpieces/pdfs/redp5110.pdfFIELDPROCtoencryptthecolumn(V7R1)
LinomaCryto Complete
TestingWithoutConsiderationtoSecurity
Testingnewfunctionwithoutsecurityinmindthenscaredtochangetheprofilewhenmovingintoproduction(especiallywithdeadlineslooming.)Testprofileswilloftenhavetoomuchauthority– justifiedbecauseyouneedtofirstgettheapplicationtowork– thenyou’llthinkaboutsecurity
Whendoesthathappen….?
AuthoritiesLeftAfterDebuggingaFailure
Failuresareoftenattributedtoan“authorityproblem.”Authoritiesgetaddedtodebugaproblemandneverremovedwhenitprovesnottobetheproblem.
*ALLOBJisadded*PUBLICauthorityisopenedupAuthoritiesareaddedtoanauthorizationlist
NotPatchingKnownVulnerabilities
Integrity/SecurityPTFsJavagroupPTFsAnythingtodowithOpenSourceMovingfromSSLtoTLS1.2
UnencryptedSessions
FTPODBCDDMTelnetPassthruSNAconnections
User:CJWPwd:cjw
Salary:CJWSSN:123-11-1234
WebApplicationsRunningonIBMi
Impressionthatcommonexposurescan’toccuronIBMiorbestpracticesforwebprogrammingdon’tapply.
Fiction!
DoAnyofTheseSituationsApplytoYourOrganization?
Ifso,arethesecuritycontrolsyouhaveinplacesufficienttoprotectthedataandprocessestheorganizationdependson?
SecurityControls
Valueofthedatatoyourorganization
Questions?
www.helpsystems.com/professional-security-serviceswww.helpsystems.com
800-328-1000 | [email protected]