Exercises from Leinster - WordPress.com
Transcript of Exercises from Leinster - WordPress.com

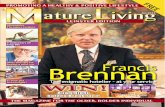
Exercises from Leinster
Michael Weiss
March 10, 2019
In 2017–2018 I participated in a meetup grooup (Cambridge Advanced MathStudies Group) that went through Leinster’s book Basic Category Theory[6]. This file is the end result of that.
I wish to thank all my fellow participants: Ken Halpern, Andras Pap, MattRumizen, Rob Sides, and Elliot Yu (apologies to anyone whose name hasescaped my memory). However, any errors are mine alone.
1 Functors and Natural Transformations
1.1 1.2.24, p.26
There is no such functor Z. We let Z(G) be the center of G for all G.Let T ⊆ S3 be a transposition subgroup on the symmetric group on threeletters, say T = {1, (ab)}. Let C3 be the cyclic group of order three, which isthe unique normal subgroup of S3 (except for S3 and 1). Since S3/C3
∼= T ,and the transposition (ab) 6∈ C3, there is an epimorphism ϕ : S3 → T such
1

1 FUNCTORS AND NATURAL TRANSFORMATIONS 2
thatT
ι↪→ S3
ϕ→ T
gives the identity: ϕι = 1T . (Here, ι is inclusion.) So if there were a functorZ, we would have
Z(ϕι) = Z(ϕ)Z(ι) = 1T
But Z(S3) = 1, so Z(ι) must be the trivial homomorphism, and Z(ϕ)Z(ι) =1T is impossible.
1.2 1.2.29, p.27
(a) Let A be a partially ordered set regarded as a category. If B is asubcategory of A, then b ≤B b′ ⇒ b ≤A b′—this condition is necessary andsufficient. (Informally: we erase some of the elements of A and some of thedirected edges, to obtain B.) For a full subcategory, b ≤B b′ ⇔ b ≤A b′, soB = A|Obj(B).
(b) Subcategories of a group are the monoids contained in the group (withthe same operation, of course). The only full subcategory of a group is thegroup itself.
1.3 1.3.26, p.38
One direction is trivial: if α is a natural isomorphism with β its inverse,then αAβA = (αβ)A = 1GA, βAαA = (βα)A = 1FA.
In the other direction, suppose each αA has an inverse βA (necessarilyunique). We need to show that β is a natural transformation. The nat-

1 FUNCTORS AND NATURAL TRANSFORMATIONS 3
urality square for α, with the β’s indicated:
FA FA′
GA GA′
αA αA′βA βA′
We symbolically indicate the proof of β’s naturality with these diagrams:
• •
• •
αA′ =
• •
• •
αA
so• •
• •
αA′βA =
• •
• •
so• •
• •βA =
• •
• •
βA′
1.4 1.3.28, p.39
(a) (a, f) 7→ f(a).
(b) Using lambda notation: a 7→ λf(f(a)). In other words, a 7→ (f 7→f(a)), where f 7→ f(a) is the function mapping f ∈ BA to f(a) ∈ B. So(f 7→ f(a)) ∈ BBA
, and a 7→ (f 7→ f(a)) maps A→ BBA.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 4
1.5 1.3.29, p.39
FA : B 7→ F (A,B), and if g : B → B′, then F (A,B)F (1A,g)−−−−→ F (A,B′).
FB : A 7→ F (A,B), and if f : A→ A′, then F (A,B)F (f,1B)−−−−→ F (A′, B).
So:
F (A,B) G(A,B)
F (A′, B) G(A′, B)
F (A′, B′) G(A′, B′)
αA,B
F (f,1B) G(f,1B)
αA′,B
F (1A′ ,g) G(1A′ ,g)
αA′,B′
The top and bottom squares commute, so the whole square commutes.
1.6 1.3.30, p.39
The relationship is conjugacy. Suppose f, g : Z→ G are functors, as shownbelow; here, ‘+1’ is the element 1 ∈ Z (i.e., “add 1”) and not the identityfunctor 1Z (which equals 0 ∈ Z).
Z G
• •
g
h
+1
g(+1)
h(+1)
As Leinster suggests, we write just g and h instead of g(+1) and h(+1) andthink of g, h as elements of the group G. A natural isomorphism is a family

1 FUNCTORS AND NATURAL TRANSFORMATIONS 5
of morphisms {αA} indexed by the objects of G, but there’s only one suchobject (which we denote by •), so α : g ⇒ h amounts to a commutativediagram
• •
• •
g
α•
h
α•
i.e., hα• = α•g, i.e., g = α−1• hα•. So g is naturally isomorphic to h iff g is
conjugate to h.
1.7 1.3.31, p.39
(a) For any A,B ∈ B and bijection ϕ : A→ B, we define:
Sym(A) = {α : A↔ A}
Sym(A)Sym(ϕ)−−−−→ Sym(B)
α 7→ ϕαϕ−1
That is, Sym(A) is the set of all bijections of A to itself, and Sym(ϕ) mapsα : A↔ A to β : B ↔ B via conjugation by ϕ.
Define
Ord(A) = {≤A : ≤A totally orders A}
Ord(A)Ord(ϕ)−−−−→ Ord(B)
≤A 7→ ≤Bb ≤B b′ ⇔ ϕ−1(b) ≤A ϕ−1(b′)
That is, Ord(A) is the set of all linear orderings of A, and Ord(ϕ) uses ϕ topull the ordering of A over to B. (Visually, we arrange the elements of A in

1 FUNCTORS AND NATURAL TRANSFORMATIONS 6
a line, and then replace each element of A with the corresponding elementof B.)
(b) We have1A 7→ ϕ 1A ϕ
−1 = ϕϕ−1 = 1B
so identities are preserved. If we had α : Sym⇒ Ord, then we would have,for the special case where ϕ : A↔ A:
Sym(A) Ord(A)
Sym(A) Ord(A)
Sym(ϕ)
αA
Ord(ϕ)
αA
and so
1A αA(1A)
1A αA(1A)
αA
Ord(ϕ)
αA
but if ϕ is not the identity on A, then Ord(ϕ) changes every total order onA.
(c) Both Sym(X) and Ord(X) have n! elements if |X| = n.
1.8 1.3.32, p.40
(a) Assume F : A → B is an equivalence, with G : B → A and α : 1A ⇔GF . First we prove faithfulness, so let f1, f2 : A → A′ be morphisms, andlet F (f1) = F (f2). Then GF (f1) = GF (f2) = h (say), and we have this

1 FUNCTORS AND NATURAL TRANSFORMATIONS 7
situation:
• •
A A′
• •
h
G
f1
f2
F
αA
F
αA′
G
So f1 = α−1A′ hαA = f2.
Next, fullness. Let g : FA → FA′; we need to show there is an f withFf = g, like so:
• •
A A′
FA FA′
Gg=h
G
f
F
αA
F
αA′
G
g
Set h = Gg and set f = α−1A′ hαA. Now, GFf = αA′fα
−1A = h because
α : 1A ⇔ GF . Since G(Ff) = Gg and G is faithful, Ff = g, as desired.
Finally, essential surjectivity. But B ∼= F (GB) because FG⇔ 1B.
(b) Suppose F is full, faithful, and essentially surjective. Since F is essen-tially surjective, for any B ∈ B we can choose an A ∈ A with FA ∼= B; foreach B, set GB = A and choose an isomorphism εB : FA→ B.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 8
Now we need to define Gg for each morphism g : B → B′, defining it in afunctorial fashion. This diagram gives the essentials:
• • •
• • •
B B′ B′′
Gg
F
Gg′
F F
h
εB
h′
εB′ εB′′
G
g
G
g′
G
We set h = ε−1B′ gεB. Since F is full and faithful, F−1 is well-defined. So set
Gg = F−1h. We have the required naturality square with gεB = εB′(FGg),showing that ε : FG ⇔ 1B. To see that G is a functor, look at thiscomputation:
FG(g′)FG(g) = ε−1B′′g
′εB′ε−1B′ gεB = FG(g′g)
1.9 1.3.33, p.40
Composition in Mat is matrix multiplication. Define a functor F : Mat→FDVect by F (n) = kn (recall that k is the field), with F (A) the linearmap determined by the matrix A. This is clearly full, faithful, and es-sentially surjective. F is not canonical; we could, for example, choose annon-standard basis for each kn (say the standard basis in reverse order) andthen declare that A determines the linear map with respect to this basis.
1.10 1.3.34, p.40
Suppose we have A B CF
J
G
H, with 1A ⇔ JF , FJ ⇔ 1B ⇔ HG,
GH ⇔ 1C.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 9
First proof: we use Prop. 1.3.18. All we need to show, then, is that GFis full, faithful, and essentially surjective on objects. This follows almostimmediately from the fact that these three properties hold for F and G.(Essential surjectivity takes a moment of thought, fullness and faithfulnessnot even that.)
Second proof: We have to show that 1A ⇔ (JH)(GF ) and (GF )(JH)⇔ 1C.We compose natural isomorphisms:
1B ⇔ HG
F ⇔ HGF
1A ⇔ JF ⇔ JHGF
Here we first use horizontal composition (Leinster, p.37) followed by verticalcomposition (Leinster, p.30 and p.36) to get 1A ⇔ JHGF . A similarargument shows that GFJH ⇔ 1C.
1.11 Monics and Epics
Monics and epics show up scattered throughout the exercises; this sectioncollects some facts about them for ease of reference. Leinster introducesthese concepts on pp.123, 134–136. See also §2.10, §2.11, and §5.12.
Here are the definitions:
• We say g is monic iff for all x, y, gx = gy ⇒ x = y. We say g is splitmonic iff g has a left inverse, say hg = 1.
• We say g is epic iff for all x, y, xg = yg ⇒ x = y. We say g is splitepic iff g has a right inverse, say gh = 1.
So monic means we can cancel on the left, epic on the right.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 10
Some terminology, borrowed from topology: split monics are also calledsections, and split epics retracts, especially in the case where the rightinverse is an inclusion of sets.
Some easy facts:
1. Split monic ⇒ monic, split epic ⇒ epic. Proof: obvious.
2. Split monic plus epic⇔ isomorphism. Proof: Say g is both split monicand epic. So hg = 1 for some h. Then ghg = g1 = 1g, so cancellingon the right, gh = 1. The converse is obvious.
3. Split epic plus monic ⇔ isomorphism. Proof: duality.
4. Composition of monics is monic, compositions of epic is epic. Proof:for monics f and g, fgx = fgy ⇒ gx = gy ⇒ x = y. Dually for epics.
5. Composition of split monics is split monic, likewise split epics. Proof:if f ′ and g′ are left inverses to f and g, then g′f ′ is a left inverse tofg. Ditto for right inverses. (Note that neither left nor right inversesneed be unique.)
6. A monic composition has a monic on the right. Proof: look at thecontrapositive. If x 6= y and gx = gy, then fgx = fgy, so g not monicimplies fg not monic.
7. An epic composition has an epic on the left. Proof: duality.
8. Faithful functors “pull back” monics and epics. That is, if U is faithfuland Uf is monic/epic, then f is monic/epic. Proof: if Uf is monic,then fx = fy ⇒ (Uf)(Ux) = (Uf)(Uy) ⇒ Ux = Uy ⇒ x = y.Likewise for epics.
9. Functors “push forward” split monics and split epics. That is, if fis split monic/epic, then Uf is split monic/epic for any functor U .Proof: ef = 1 ⇒ (Ue)(Uf) = 1, and likewise for epics.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 11
Two pictures can help you tell your left from your right with monics andepics. Both come from Set.
•
• •
•
fx
y f
• • •
• •
f x,y
y
x
On the left, we have a non-monic f , erasing the difference between x and y:x 6= y but fx = fy. On the right, a non-epic f does the same on the otherside: x 6= y but xf = yf .
In Set, split monic implies injective, and injective iff monic; split epic iffsurjective iff epic. Split monic is almost equivalent to injective, but there isa sole class of exceptions: empty functions to a nonempty set, i.e., f : ∅→A 6= ∅. Such an f is injective but not split monic, since we can’t have afunction from a nonempty set to the empty set. (Proofs of these facts arein §5.15(b).)
A concrete category has a faithful functor to Set. Examples: Monoid,Group, Top. Key point: two morphisms (with the same source and target)have to differ set-theoretically in order to be different. In Top, for example,given f, g : X → Y , if f(x) = g(x) for all x ∈ X, then f = g—topologydoesn’t impose any further constraints.
Say A is a concrete category with faithful functor U to Set. We can drawthe following conclusions:
(a) f split monic ⇒ Uf injective ⇒ f monic.
(b) f split epic ⇒ Uf surjective ⇒ f epic.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 12
Proof: By (8) above, if Uf is monic then f is monic, but monic for Set isthe same as injective. By (9), if f is split monic then Uf is split monic (forall U , not just faithful ones), and split monic implies injective in Set.
So Uf injective implies f monic for a concrete category. Surprisingly oftenthe converse holds: all monics are injective in Monoid, Group, Top, andmany other concrete categories. This is a special case of the general factthat functors with left adjoints preserve limits (see Theorem 6.3.1 (p.159)plus Lemma 5.1.32 (p.124)).
It’s not hard to show directly that functors with left adjoints preserve monics(dually for epics). Suppose that F a U with F : A → B, U : B → A. LetB,B′ ∈ B, and f : B → B′. Assume f is monic. We want to showthat Uf is monic in A, so we consider A ∈ A and x, y : A → UB. (Thebar map is a bijection between A(A,UB) and B(FA,B), so we lose nogenerality in writing arbitary elements of A(A,UB) as x and y.) We nowuse the naturality formula for adjunctions, fx = (Uf)x, in the chain ofimplications
(Uf)x = (Uf)y ⇒fx = fy ⇒fx = fy ⇒x = y ⇒x = y
Done. Recording this fact:
10. A functor with a left adjoint preserves monics, and a functor with aright adjoint preserves epics.
Now let A be Set. So if U : B → Set is a functor with a left adjoint, then fmonic implies Uf monic, i.e., Uf injective. Dually, if U has a right adjoint,then it preserves epics. Right adjoints to forgetful functors are less common,

1 FUNCTORS AND NATURAL TRANSFORMATIONS 13
though not unheard of (see below). Hand-in-hand with this, we find epicsthat are not surjective. Example 5.2.19, p.134 (same as Exericse 5.2.23,p.135, §5.12) gives the examples N ⊆ Z in Monoid, and Z ⊆ Q in Ring.So in neither case can U have a right adjoint.
Another case of interest, in the interaction between epics and adjoints: thefunctor F : Monoid→ Group, sending a monoid to its universal envelop-ing group (see §2.2). This has a right adjoint U , so F preserves epics. Nowwe’ve seen that N ↪→ Z is an epic inclusion in Monoid, so FN→ FZ mustbe an epic morphism in Group. But all epics are surjective in Group (see§2.11). It so happens that FN = Z and FZ = Z and F of the inclusion isthe identity map, so all is well.
Along the same lines, item (8) (faithful functors pull back epics) tells usthis: a monoid epimorphism whose source and target both happen to begroups is surjective. Proof: any such morphism is Uf : UG → UH whereU : Group →Monoid is forgetful. U is faithful, so since Uf is epic, f isepic, and epics in Group are surjective.
Leinster defines regular monics and epics in Exercises 5.2.25 and 5.2.26(pp.135,136). A monic is regular if it is an equalizer (Definition 5.1.11,p.112). Likewise, an epic is regular if it is a coequalizer (Definition 5.2.7,p.129). The most important facts about regular monics and epics:
11. Split monic ⇒ regular monic ⇒ monic.
12. Split epic ⇒ regular epic ⇒ epic.
13. Regular monic plus epic⇔ isomorphism. (This strengthens (2) in onedirection.)
14. Regular epic plus monic⇔ isomorphism. (This strengthens (3) in onedirection.)

1 FUNCTORS AND NATURAL TRANSFORMATIONS 14
15. In Set, split epic ⇔ regular epic ⇔ epic ⇔ surjective. Also, splitmonic ⇒ regular monic ⇔ monic ⇔ injective, and injective plusnonempty source ⇒ split monic.
See §5.14 for proofs of (11), §5.15 for (12), (13), and (14). §5.15(b) has theproofs of (15).
1.12 Monics and Epics in Top
We look at all three varieties of monics and epics in Top, and its full sub-categories Hausdorff (Hausdorff spaces) and CptHff (compact Hausdorffspaces).
Some cross-references. §5.7(c): monics in Top. §5.11(b): a curious exampleof a regular epic. §5.13: quotient objects. §5.14(c): regular monics in Top.§5.15(c): an epic that is regular but not split. §5.16: regular monics inFHaus, and an epic in Hausdorff that is not pullback stable.
Summary of results:
• Monics in Top, or in Hausdorff, are homeomorphisms onto subsetsof a space where the homeomorphic image has a finer topology thanthe subspace topology.
• Regular monics in Top are homeomorphisms onto subspaces.
• Regular monics in Hausdorff are homeomorphisms onto closed sub-spaces.
• Monics in CptHff are all regular, and are homeomorphisms ontoclosed subspaces.
• Epics in Top are surjective maps.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 15
• Epics in Hausdorff are maps with dense images.
• Epics in CptHff are all regular, and are quotient maps.
• Regular epics in Top, or in Hausdorff, are quotient maps.
• Neither all regular monics nor all regular epics are split, in any ofthese three categories.
(In this list, “are” is used in the sense of “if and only if”. For example, amap in Top is regular monic if and only if it is a homeomorphism onto asubspace. Below however “are” is used in the “if-then” sense.)
Some basic definitions/facts from point-set topology:
• If S and T are topologies on the same set, we say S is coarser thanT , and T is finer than S, iff S ⊆ T .
• A quotient map f : X → Y is a surjective map such that V is openin Y iff f−1(V ) is open in X. Note that the ⇒ implication is just thedefinition of continuity. Also note that we can replace “open” with“closed” and have an equivalent definition.
• An open map sends open sets to open sets. A closed map sendsclosed sets to closed sets.
• It follows from the equation f(f−1(V )) = V , true for any surjectivef , that any surjective open or closed map is a quotient map.
• If s, t : X → Y are continuous and Y is Hausdorff, then the solutionset {x ∈ X|s(x) = t(x)} is closed.
• The continuous image of a compact set is compact.
• A compact subset of a Hausdorff space is closed.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 16
• A closed subset of a compact space is compact.
• Putting the last three facts together, any map from a compact spaceto a Hausdorff space is closed. That’s all maps in CptHff !
• Finally, the forgetful functor U : Top → Set is faithful, and has aleft adjoint (the discretization functor) and a right adjoint (the indis-cretization functor). Replacing Top with Hausdorff, we still havethe left adjoint, but lose the right adjoint.
I don’t know of any slick characterization of split monics or split epics inany of these three categories.
The characterizations on our list shower us with boatloads of contrast ex-amples: monics and epics that are not regular, in both Top and Hausdorff.For a non-regular monic, consider any inclusion map i : A ↪→ X, where thetopology of A is (strictly) larger than the subspace topology inherited fromX. For a non-regular epic in Top, consider any surjective map f : X → Ywhere the topology of Y is (strictly) smaller than the quotient topologyinduced by f . Example: f : R→ R, Uf the identity, with the first R giventhe discrete topology and second the standard topology, is both monic andepic in both Top and Hausdorff, but not regular monic or regular epicin either. In Hausdorff, another family of non-regular epics consists ofnon-surjections with a dense images, e.g., i : Q ↪→ R with both given thestandard topologies.
Next on our list of contrast examples, a regular monic that is not split, in allthree of our categories: the inclusion i : {0, 1} ↪→ [0, 1]. If we had f : [0, 1]→{0, 1} with fi = 1{0,1}, this would mean that f−1(0)tf−1(1) was a partitionof [0, 1] into two disjoint nonempty closed sets, contradicting the fact that[0, 1] is connected. (This argument can be rephrased to use the intermediatevalue theorem.) A more sophisticated variant: i : Sn ↪→ Dn+1, the inclusionof the n-sphere in the closed (n + 1)-disk. (The {0, 1} ↪→ [0, 1] example isthe case n = 0.) The homology functor proves that no left inverse exists, for

1 FUNCTORS AND NATURAL TRANSFORMATIONS 17
if fi = 1Sn , then the composition Hn(Sn)Hi−→ Hn(Dn+1)
Hf−−→ Hn(Sn) wouldhave to be the identity, but for n > 0, this is just Z→ 0→ Z.1 Regularityfollows from the characterization given in the list above.
For a regular epic that is not split, consider f : [0, 2π]→ S1 via the identifi-cation of 0 and 2π, i.e., x 7→ eix. This is regular in all three categories sinceit’s a quotient map (closed since it’s from a compact space to a Hausdorffspace). An equation fi = 1S1 is impossible: apply the fundamental groupfunctor π (I apologize for the unfortunate double meaning of the same greek
letter) to get π(S1)πi−→ π([0, 2π])
πf−→ π(S1), or Z→ 0→ Z. (The homologyfunctor H1 could be used instead.) Another example: R→ S1, with x 7→ eix
as before. This works for Top and Hausdorff but not CptHff. The mapis open and hence a quotient map.
We turn to the list of characterizations. First, monics in all three categories.If m : X → Y is injective, then it’s monic, since U pulls back monics in Set(item (8) in §1.11). Conversely, if m is not injective, then it’s not monic:if m(x1) = m(x2), let A = {0} (there’s only one possible topology), andand set s(0) = x1, t(0) = x2. Then ms = mt but s 6= t. (For a moresophisticated proof in Top and Hausdorff, note that U has a left adjointand so preserves monics.)
Since m is continuous, the inclusion m(X) ↪→ Y is also continuous, if wegive m(X) the topology making m a homeomorphism. So the topologymaking m(X) homeomorphic to X is finer than the subspace topology onm(X).
In CptHff, m is automatically a closed map and so the bijection Xm−→
m(X) is a homeomorphism, with m(X) having the subspace topology. Alsom(X) must be closed in Y . So in CptHff, a monic is an imbedding of onespace as a closed subspace of another.
1For n = 0, you get the identity as a composition Z⊕ Z→ Z→ Z⊕ Z. With a littlework, you can show that this is impossible. Using the reduced homology functor avoidsthis niggle. Of course, the case n = 0 has already been treated.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 18
Next, regular monics. Suppose s, t : X → Y . Let S = {x ∈ X|s(x) = t(x)}with the subspace topology. The inclusion i : S ↪→ X equalizes s and t: onthe one hand, clearly si = ti. On the other hand, if f : A → X satisfiessf = tf , then clearly f(A) ⊆ S. Define e : A → S by e(a) = f(a) for alla ∈ A. So ie = f , and clearly e is the unique solution to this equation.
We know equalizers are unique up to isomorphism, so any other equalizerof s and t is a homeomorphism of some space onto S.
So in all three categories, a regular monic is a homeomorphism onto asolution set {x ∈ X|s(x) = t(x)} for some s and t. We now have todetermine what subsets of X can be expressed in this way.
In Top, every subset S of X is a solution set: let Y = {0, 1} with the indis-crete topology, let s(x) = 1 for all x ∈ X and let t = χS, the characteristicfunction of S. Both s and t are continuous because every function to anindiscrete space is continuous, and obviously the solution set for s and t isS. So regular monics in Top are precisely homeomorphisms onto subspaces.
In Hausdorff, all solution sets are closed, as we noted above. We now showthat conversely, all closed subspaces of X are solution sets. Let Xdbl =X t X, i.e., the disjoint union of two copies of X. Glue the two copiesalong S to obtain Y . (A useful mental picture: two copies of a closed disk,glued along a line segment.) In detail, we let X1 and X2 be the two copies,and i1, i2 be the obvious maps from X to X1 and X2 respectively. Formthe quotient space of Xdbl by identifying i1(x) with i2(x) for all x ∈ S. Letq : Xdbl → Y be the quotient map, and let s = qi1, t = qi2. (Mental picture:s takes the disk to the “upper layer”, and t to the “lower layer”, but s and tagree on the line segment.) Let us note that we have a continuous surjectionr : Y → X where we send each y ∈ Y to its “grandparent” x ∈ X, i.e.,we identify s(x) with t(x) for all x ∈ X, getting an identical copy of X.(Mental picture: we flatten the two layers into one.) So rs = rt = 1X .
It remains to show that Y is Hausdorff. Suppose T = s(X) = t(X), the

1 FUNCTORS AND NATURAL TRANSFORMATIONS 19
identified subset, and let y, y′ ∈ Y . Let x = r(y), x′ = r(y′). Case 1:x 6= x′. So there are disjoint open sets U 3 x, U ′ 3 x′. Set V = r−1(U)and V ′ = r−1(U ′) and we have disjoint open sets around y and y′. Case2: x = x′. The only way to have y 6= y′ is if they live in different layers,i.e., x 6∈ S and y = s(x) and y′ = t(x) (or vice versa). Since S is closed,X1ri1(S) and X2ri2(S) are both open in Xdbl, and clearly q sends themto disjoint open sets in Y , one containing y and the other containing y′. SoY is Hausdorff.
Conclusion: the regular monics in Hausdorff are precisely the homeomor-phisms onto closed subspaces.
The same argument works for CptHff, since Xdbl and Y are compact when-ever X is. But we observed above that this also characterizes the monics inCptHff, so in this category all monics are regular.
Very soon we will reuse part of these arguments, so let’s make it into alemma:
Lemma: in Top, any subset S ⊆ X can be expressed as S ={x ∈ X|s(x) = t(x)}, where s, t : X → Y are continuous. Inboth Hausdorff and CptHff, any closed subset S ⊆ X can beexpressed this way. (Proof: see above.)
We turn to epics in Top. Any surjective map is epic, since U pulls backepics, and surjectives in Set are epic (items 8 and 15 in §1.11). On the otherhand, U has a right adjoint I : Set→ Top, where IX is the indiscrete spaceon X. It follows that epics are surjective by item (10).
Here’s a direct proof, in contrapositive form. Suppose f : A → X is notsurjective. Let f(A) = S and let x0 ∈ XrS. By the lemma, S = {x ∈X|s(x) = t(x)} with s, t : X → Y . So s(x0) 6= t(x0) and hence s 6= t, butsf = tf . So f is not epic.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 20
Turning to Hausdorff, we have a similar argument but a different con-clusion. By basic topology, if s and t agree on a dense subset of X, thenthey are equal (provided the target space is Hausdorff). It follows that iff : A→ X has a dense image, then f is epic in Hausdorff because sf = tfmeans that s and t agree on f(A). On the other hand, if f is epic in Haus-dorff, then it has a dense image. For if not, then f(A) is a proper subsetof X. We let S = f(A), and appeal to the lemma. If x0 ∈ XrS, thens(x0) 6= t(x0) and so s 6= t, but sf = tf , all as before. Conclusion: epics inHausdorff are precisely the maps with dense images. (Leinster mentionshalf of this in Example 5.2.20, p.134.)
Finally, for CptHff the same argument works, but since all images inCptHff are closed, we’re back to epic implying surjective. Now we notedin our list of basic topological facts that all maps in CptHff are closed, andthat all surjective closed maps are quotient maps. So epics in CptHff areprecisely the quotient maps.
Next, regular epics in Top. First, we show that regular epic implies quotientmap. Suppose f is regular epic. Then f is epic and thus surjective. Supposef : X → Y coequalizes s, t : A → X. Let Y ′ have the same underlying setas Y but give it the quotient topology induced by f . Let i : Y ′ → Y bethe identity set-theoretically, i.e., Ui = 1UY . Then i is continuous since thequotient topology is finer than the topology of Y . (In detail: V open in Yimplies f−1(V ) open in X implies V open in Y ′.) We let f ′ : X → Y ′ be thesame map as f , set-theoretically (Uf = Uf ′), so since fs = ft, f ′s = f ′t.Since f is a coequalizer, there is a unique j : Y → Y ′ with jf = f ′. Hencein the diagram
Y
A X
Y ′
js
t
f
f ′
i
we have jf = f ′, if ′ = f . So ijf = f and jif ′ = f ′, which means that

1 FUNCTORS AND NATURAL TRANSFORMATIONS 21
ij and ji are identities when restricted to the images of f and f ′. Butthose images are Y and Y ′ since f and f ′ are surjective, so Y and Y ′ areisomorphic (homeomorphic), and Y has the quotient topology, i.e., f is aquotient map.
On the other hand, let’s start with a quotient map f : X → Y . This definesan equivalence relation ∼ on X: x1 ∼ x2 iff f(x1) = f(x2). Let A ⊆ X ×Xbe ∼ regarded as a set of ordered pairs, i.e., A = {(x1, x2)|f(x1) = f(x2)}.We give X × X the product topology and A the subspace topology. Welet p1 and p2 be the projection maps restricted to A. So for all a ∈ A,p1(a) ∼ p2(a) and hence fp1 = fp2. Suppose f ′ : X → Y ′ also satisfiesf ′p1 = f ′p2. We conclude that if x1 ∼ x2, then (x1, x2) = a ∈ A and sof ′(p1(a)) = f ′(p2(a)), i.e., f ′(x1) = f ′(x2). That is to say, f(x1) = f(x2)implies f ′(x1) = f ′(x2). This, and the surjectivity of f , allow us to define(set-theoretically) a function j : Y → Y ′ with jf = f ′: j(y) = f ′(f−1(y)).Moreover j is uniquely determined by the condition jf = f ′. Finally, j iscontinuous because V open in Y ′ implies f ′−1(V ) = f−1(j−1(V )) open in Ximplies j−1(V ) open in X (as f is a quotient map).
How do we adapt these arguments to Hausdorff? In the ⇒ direction, wedon’t know up front that f is surjective, only that its image is dense (becausef is epic). Let Y ′ be the image with the induced quotient topology. Leti : Y ′ → Y be set-theoretically the inclusion map (Ui : UY ′ ↪→ UY ), and letf ′ : X → Y ′ be “the same” as f except for codomain (i.e., f ′(x) = f(x) forall x ∈ X, so if ′ = f ; f ′ is a quotient map). This quotient topology is finerthan the subspace topology inherited from Y (use the identity f−1(V ) =f ′−1(i−1(V ))), implying that Y ′ is Hausdorff and that the map i : Y ′ → Y iscontinuous. The argument then proceeds as before until we reach the pointwhere we said that ij and ji are the identities on the images of f and f ′.Since f ′ is surjective, ji = 1Y ′ . The image of f is dense, so ij agrees with1Y on a dense subset. But in Hausdorff, two continuous functions thatagree on a dense subset are equal. So ij = 1Y , and we conclude both thatf is surjective and that it’s a quotient map.

1 FUNCTORS AND NATURAL TRANSFORMATIONS 22
We can also give a more abstract proof that ij = 1Y , not using that factabout Hausdorff spaces. Consider the diagram
Y
A X
Y
1Yijs
t
f
f
The uniqueness property of coequalizers demands that ij = 1Y . This alter-nate argument proves handy in §5.16.
In the⇐ direction, the argument goes through without modification. How-ever, we can add a remark: the subset A ⊆ X×X is defined by the equationf(p1(a)) = f(p2(a)) (now letting p1 and p2 be the projections from X ×Xto X), and so A is closed.
Finally, a regular epic in CptHff is a quotient map by the exact sameargument as for Hausdorff, and a quotient map is regular epic becauseA is closed and so compact. So the regular epics are exactly the quotientmaps. We noted earlier that this also describes the epics in CptHff.
One caveat: suppose a set A ⊆ X × X represents an equivalence relation∼ on X. For X/∼ to be Hausdorff, it is necessary but not sufficient thatA be closed. This has the following consequence. Say we have s, t : X →Y in Hausdorff. We want to construct the coequalizer of s and t. Asa first step, we construct the smallest equivalence relation ∼ such thats(x) ∼ t(x) for all x ∈ X (see Leinster, pp.129–130). Taking the quotientX → X/∼ can take us out of the category of Hausdorff spaces: X/∼might not be Hausdorff. To finish the job, we need the Hausdorffificationfunctor H : Top → Hausdorff : HY is the “largest” Hausdorff spacefor which there is a quotient map Y → HY (largest in the sense of auniversal property). The construction of the Hausdorffification functor (akaHausdorfization, Hausdorffication) is decidedly nontrivial (see §A.4).

1 FUNCTORS AND NATURAL TRANSFORMATIONS 23
To wrap things up, three sufficient conditions for a surjective f to be aquotient map: (a) f is an open map. (b) f is a closed map. (c) f is splitepic. We observed (a) and (b) in our list of basic topological facts; (c)follows from item (12) in §1.11 (split epic ⇒ regular epic) because regularepic is equivalent to being a quotient map.
Here are some examples to show that these conditions are not necessary.Let Y = R and let X be the subset of R2 consisting of the union of thex-axis and the closed right half plane, i.e., {(x, y)|x ≥ 0}. Let f be theprojection onto the y-coordinate. Then f is split epic with the right inversebeing the inclusion Y ↪→ X. But f is neither open nor closed. For example,intersecting an open disk centered at the origin gives an open subset ofX whose projection is not open. And one branch of a hyperbola, namely{(x, y)|xy = 1}, is a closed subset of X whose projection is not closed. Next,consider again either R or [0, 2π] mapping onto the circle (f(x) = eix). Bothare quotient maps (one is open, the other closed), but as we showed above,neither is split.
1.13 Monics and Epics in Group
Monics in Group are precisely the injective homomorphisms. Injective ⇒monic because the forgetful functor U : Group → Set is faithful, andfaithful functors pull back monics, and in Set the monics are precisely theinjectives (items (8) and (15) of §1.11). Monic ⇒ injective because U has aleft adjoint (the free group functor) and functors with left adjoints preservemonics (item (10)). There’s also an easy direct proof: if f : G → Q is notinjective, then ker f is not 0, so we have two different homomorphisms s, t :ker f → G satisfying fs = ft, namely s the inclusion map ker f ↪→ G and t
the trivial map t(ker f) = 1 (the identity of G): ker f G Qs
t
f.
Epics in Group are precisely the surjective homomorphisms. Surjective ⇒epic: basically the same as injective ⇒ monic. (Faithful functors pull back

1 FUNCTORS AND NATURAL TRANSFORMATIONS 24
epics, and in Set the epics are precisely the surjectives.)
The proof that epic ⇒ surjective is not easy. Here is a proof rewitten fromLinderholm [7]; that reference says, “The present proof closely resemblesone due to S. Eilenberg and J. Moore. . . it seems to be well known to thosewho work with categories.”
Suppose f : A → G is not surjective. We want s, t : G → Q with sf = tfbut s 6= t. Let H = f(A). So we want s|H and t|H to be equal with s 6= t:
H G Qs
t
Hence it’s enough to show that given any proper subgroup H of a group G,there are two different homomorphisms from G that agree on H. Actuallywe will show something stronger: there are two homomomorphisms thatagree on H and disagree on all elements outside of H. Let G/H be theset of all left cosets of H. Let S be G/H plus one more element, whichwe’ll denote by Z. Let ΣS be the group of all permutations of S. Ourhomomorphisms will go from G to ΣS.
Multiplication on the left by elements of G permutes the left cosets of H;let’s write λg : (G/H)→ (G/H) for this permutation. We extend λg to S bystipulating that λg(Z) = Z. Obviously the map g 7→ λg is a homomorphismfrom G to ΣS (adopting the usual convention of right-to-left composition).We let λ : G→ ΣS be this homomorphism.
Let s be the permutation of S that interchanges H and Z (both elementsof S) and leaves everything else fixed. Let σg be the permutation σg(X) =s(λg(s
−1(X))), i.e., we conjugate the permutation λg by the permutations. That is, σg = (λg)
s, adopting a common notation for conjugation in agroup. (Since s2 = 1, we could have just written s(λg(s(X))), but this won’tmatter.) It is evident that σ : g 7→ σg is a homomorphism from G to ΣS:hk 7→ (λhk)
s = (λhλk)s = (λh)
s(λk)s.
Now suppose h is an element of H. Since λh leaves H and Z unmoved, and

1 FUNCTORS AND NATURAL TRANSFORMATIONS 25
s just switches them leaving all the other elements of S unmoved, we seethat λh and s commute. So (λh)
s = λh, and σh = λh. Therefore λ and σagree on H.
On the other hand, let g 6∈ H. Then λg sends H to gH 6= H. We nowcompare λg with σg, or what amounts to the same thing, sλg with λgs. Wehave s(λg(Z)) = s(Z) = H, but λg(s(Z)) = λg(H) = gH. Alternately,compute s(λg(H)) = s(gH) = gH, but λg(s(H)) = λg(Z) = Z. So sλg 6=λgs and σg 6= λg.
So λg = σg precisely when g is in H. QED
Because our target group is finite whenever G is, this proof also worksfor FinGroup. Another common proof, using amalgamated free products,doesn’t enjoy this feature.
In Group, all monics and all epics are regular. Leinster gives the key ideafor epics in Example 5.1.14 (p.114). We repeat the argument. Supposef : G→ Q is epic. We want s, t : K → G such that f is the coequalizer ofs and t. Let K = ker f , let s be the inclusion map K ↪→ G and let t be thetrivial map t(K) = 1. Clearly fs = ft. Suppose g : G → R with gs = gt.In other words, for every x ∈ K, g(s(x)) = g(t(x)), so g(x) = g(1) = 1, soK = ker f ⊆ ker g. This, plus the fact that f is surjective, implies that thefunction
h : Q→ R
h : q 7→ g(f−1(q))
is well-defined. Here’s the diagram:
K G Q
R
s
t
f
g h

2 ADJOINTS 26
It’s routine to check that it’s a homomorphism, that it satisfies hf = g, andthat it’s the unique solution to this equation. So f is a coequalizer.
For a monic f : A → G, we want s, t : G → Q such that f equalizes s andt. In other words, s and t should agree on the image of f , and if that’s alsotrue for g : B → G, then we want a unique h : B → A with fh = g. Letf(A) = H. Diagram:
A G Q
B
f s
t
gh
We showed above that for any subgroup H of a group G, there are homo-morphisms s, t : G → Q such that H = {x ∈ G|s(x) = t(x)}. With thiss and t, we have: s|g(B) = t|g(B) ⇒ g(B) ⊆ f(A). This fact plus theinjectivity of f imply that h = f−1g is well-defined. It’s easy to check thatthis h is a homomorphism and the unique solution to fh = g. So f is anequalizer.
2 Adjoints
2.1 Units and Counits
Leinster simply asserts that units and counits are natural transformationswithout explaining why. Two diagrams help.
I omit parentheses when I can get away with it (e.g., FA′ instead of F (A′)).Assume (F : A → B) a (G : B → A), p : A′ → A. Note that 1FA′ = ηA′ .

2 ADJOINTS 27
The naturality requirement for adjunctions says that:
1FA′ ∈ B(FA′, FA′) A(A′, GFA′) 3 ηA′
Fp ∈ B(FA′, FA) A(A′, GFA)
Fp ◦ GFp ◦
Conclusion: Fp = GFp ◦ ηA′ . Next use 1FA = ηA.
1FA ∈ B(FA, FA) A(A,GFA) 3 ηA
Fp ∈ B(FA′, FA) A(A′, GFA)
◦Fp ◦ p
Conclusion: Fp = ηA ◦ p. Grand conclusion: GFp ◦ ηA′ = ηA ◦ p, soη : 1⇒ GF is a natural transformation. Duality gives the same for ε.
2.2 Free Monoids and Groups
(See also Exercise 2.2.12(b), §2.11.)
Leinster introduces the free functor from Set to Group in Example 1.2.4(p.19) and again in Example 2.1.3(b) (p.44), calling it “tricky to constructexplicitly”. The free functor from Monoid to Group appears in Example2.1.3(d) (p.45), where he says it is “again, tricky to describe explicitly”.I’m not sure if he ever mentions the free functor from Set to Monoid inso many words. In this section (and only in this section), I will decorate Fand U with subscripts as follows: Fg and Ug for the functors between Setand Group; Fm and Um between Set and Monoid; unadorned F and Ubetween Monoid and Group. (Elsewhere I think context makes it clearwhich functors are intended.)

2 ADJOINTS 28
Categories Unit ηA Counit εB
FA B
A GB
GF
FA FA
A GFA
GF
ηA
FGB B
GB GB
εB
GF
Vect
Set
UF
UF (set)liberation(injective)
FU(vector space)evaluation(surjective)
Set
LocConn
DC
DC(loc conn top space)components(surjective)
CD(set)
iso
Top
Set
UD
UD(set)
id
DU(top space)discretization
(bijective)
Set
Top
IU
IU(top space)indiscretization
(bijective)
UI(set)
id
Abelian
Group
UA
UA(group)abelianization
(surjective)
AU(abelian group)
iso
Figure 1: Units and Counits

2 ADJOINTS 29
Categories Unit ηA Counit εB
FA B
A GB
GF
FA FA
A GFA
GF
ηA
FGB B
GB GB
εB
GF
Group
Monoid
UF
UF (monoid)liberation
FU(group)
iso
Monoid
Group
RURU(group)
id
UR(monoid)invertible elements
(injective)
G-set
Set
UF
UF (set)liberation(injective)
FU(G-set)evaluation(surjective)
Set
G-set
MapU
Map(U(G-set))(injective)
U(Map(set))(surjective)
Set
G-set
TrivOrb
Triv(Orb(G-set))orbits
(surjective)
Orb(Triv(set))
iso
G-set
Set
FixTriv
Fix(Triv(set))
id
Triv(Fix(G-set))fixed points(injective)
Figure 2: More Units and Counits

2 ADJOINTS 30
The free group on a monoid has been called the universal enveloping groupor the group completion.
Fm is a piece of cake: call the elements of a set X letters ; then FmX is justthe set of all finite strings of letters, with concatenation for multiplication.(The empty string is the identity; I’ll denote it by ε.) Fg has nearly thesame description: we introduce two letters for each x ∈ X, denoted x andx−1, and consider all finite strings of letters. A string is reduced if no pairxx−1 or x−1x occurs in it. It seems obvious that: (a) the set for FgX is theset of all reduced strings; (b) any string of letters has a unique reduction;(c) multiplication in FgX is concatenation followed by reduction, i.e., weconcatenate the strings and then carry out all possible cancellations; (d)this multiplication is associative. But proving (a)–(d) formally looks like abit of a drag. Bergman [2, §3.4] gives a slick proof of (b) and (d), due tovan der Waerden. Let A be the set of reduced strings, and with any x ∈ Xassociate a permutation of σx of A, as follows:
σx(x−1t) = t for strings beginning with x−1
σx(t) = xt for strings not beginning with x−1
It’s a pleasant exercise to verify the following: (e) For each x ∈ X, σx is apermutation on A. (f) If we associate (σx)
−1 with x−1, then σx−1(ε) = x−1.Now define a mapping s 7→ σs for any string of letters s = l1 · · · ln by settingσs = σl1 · · ·σln , with composition of permutations on the right. (g) If s isreduced, then σs(ε) = s. (h) If s′ is a reduction of s, then σs′ = σs. (i) From(g) and (h) we can conclude (b). (j) Letting s · t denote the multiplicationon A as defined in (c), we have σs·t = σsσt. (k) The mapping s 7→ σs isa monomorphism of A into Symm(A), showing that A is isomorphic to asubgroup of a symmetric group, and thus verifying (d). (l) A is the freegroup on X, i.e., satisfies the required universal property.
Bergman provides another construction, where FgX is a subgroup of a directproduct. (Lang [5, §1.12] gives much the same construction.) Let S be aset of cardinality max(ℵ0, |X|). Let {Gi|i ∈ I} be an indexing of all groups

2 ADJOINTS 31
whose underlying sets are subsets of S. Let G =∏
i∈I∏
f :X→GiGi, so we
have as many copies of Gi in the product as there are ways to map X intoGi. For convenience, we’ll write G =
∏i,f Gif , so all the Gif ’s are equal
to Gi. (Technically, each f maps X into UgGi, but I’ll omit all mention ofUg for most of this paragraph, to reduce clutter without, hopefully, sowingany confusion.) For any x ∈ X, we define η(x) ∈ G by letting the (if)component of η(x) be f(x): η(x)if = f(x). Let H be the subgroup of Ggenerated by the set η(X) = {η(x)|x ∈ X}. H is FgX. Proving that H hasthe required universal property is a breeze. Suppose h : X → K for somegroup K. Let L be the subgroup of K generated by h(X). The cardinalityof L is no more than max(ℵ0, |X|), so we might as well assume that L isone of the Gi’s. Then h must be one of the f ’s for that Gi (or technicallyf : X → Gif = L is a range restriction of h : X → K). By the definitionof η(x), we have h(x) = f(x) = η(x)if = pif (η(x)), where pif : H → Gif
is the projection map G → Gif restricted to H. So pif composed withthe inclusion ι : Gif ↪→ K completes the commutative diagram, and it’seasy to see that ι ◦ pif is the unique such group homomorphism (becauseh specifies the values for all x ∈ X, and η(X) and h(X) generate H andGif = L respectively). (Bergman’s treatment offers more motivation thanI did.) Note that η is, sort of, the unit of the adjunction Fg a Ug; “sort of”because I’ve been cavalier about whether η maps X into FgX or into itsunderlying set UgFgX; the unit of course maps X → UgFgX.
We take another look at this construction in §6.13, relating it to the GeneralAdjoint Functor Theorem (GAFT).
Before we discuss F , it will help to define presentations of groups andmonoids.
A presentation of a group consists of a set of generators plus relations; forexample, 〈x, y, z|xy = yx, zz = x−1〉. More precisely, say X is a set andFgX is its free group; a relation is a pair (s, t) with s, t ∈ FgX, thoughtof as a condition s = t to be satisfied in the presented group. Now saywe have a presentation 〈X|R〉, where R is a set of relations. We recast

2 ADJOINTS 32
s = t as st−1 = 1, and let N be the least normal subgroup generatedby {st−1|(s, t) ∈ R}, i.e., the intersection of all normal subgroups of FgXcontaining all the st−1’s. Then FgX/N is the group presented by 〈X|R〉.
Alternately, the direct product construction of FgX is readily adapted toincorporate relations.
We need to proceed differently for a presentation of a monoid. Again westart with a set X of generators and form the free monoid FmX, but we nolonger have the option of rewriting relations s = t as st−1 = 1. Instead, weinvoke the notion of a congruence: that’s an equivalence relation ≡ on amonoid M with the property that if s ≡ t for s, t ∈ M , then rs ≡ rt andsr ≡ tr for all r ∈M . (It’s enough to check this with r ranging over a set ofgenerators for M .) If ≡ is a congruence on M , then monoid multiplicationis well-defined on the set of congruence classes of M , turning M/≡ into amonoid—the quotient monoid, of course! The natural map M → M/≡ isa monoid morphism. OK, given a presentation 〈X|R〉, with s, t ∈ FmX forall (s, t) ∈ R, we can form the least congruence ≡ such that s ≡ t for allthe relations in R. Since equivalence relations are sets of ordered pairs, thisleast congruence is the intersection of all congruences containing R. But itcan also be described by a more explicit “bottom up” construction; a slightmodification of Remark 5.2.8 (p.129) does the trick. FmX/≡ is the monoidpresented by 〈X|R〉.
Now we are ready to define FM , the free group generated by a monoid M .This is the group with presentation
〈M |{(a, bc)|a = bc in M,a, b, c ∈M}〉
in other words, the generators are the elements of M , and the set of rela-tions is the complete multiplication table of M . Showing that this enjoysthe defining universal property is not difficult. Here’s the diagram, as a

2 ADJOINTS 33
reminder:
M UFM FM
UG G
ηM
∀fUf ∃!f
While congruences aren’t needed to define FM , they’re handy to havearound. For one thing, if 〈X,R〉 is a monoid presentation for M , thenit’s also a group presentation for FM .
Now let’s look at the unit η = UF and counit ε = FU . First observe thatεG is the identity (or at least an isomorphism) for all G: if a monoid alreadypossesses all inverses, so it “is” a group (albeit domiciled in Monoid), thenregarded as a group, it satisfies the universal property for FM . (This iseasily checked.)
In the reverse direction, is ηM injective? Experience with Fg and Fm mightsuggest it is. Alas, no. First, if M does not satisfy the cancellation laws:
(∀a, b, c ∈M)[ab = ac⇒ b = c]
(∀a, b, c ∈M)[ba = ca⇒ b = c]
then ηM will not be injective, since these laws follow immediately fromthe existence of inverses. As a concrete example, let X be a set with twoelements, and let M be the monoid of all functions X → X. Easy exercise:FM is the trivial group, ηM is the morphism to the trivial monoid, ηM is notmonic, and F sends all five morphisms in Monoid(M,M) to the morphism1FM , demonstrating that F is neither full nor faithful. (Hint: M has fourelements: the identity 1, two constant functions, and a function that swapsthe two elements. If a is one of the constant functions, then am = a1 forall m ∈M . Now use cancellation in FM .)
If M satisfies the cancellation laws, is ηM then injective? Not always. Mal-cev came up with an infinite family of laws that all together are necessaryand sufficient for ηM to be injective (see Cohn [3, §VII.3]). Moreover, no

2 ADJOINTS 34
finite subfamily of the Malcev laws suffice. Here is the next simplest law inthis family:
(∀a, b, c,d, e, f, g, h ∈M)
[ab = cd & ce = af & gf = he⇒ gb = hd](*)
According to Cohn, the monoid with the presentation
〈a, b, c, d, e, f |ab = cd, ce = af, gf = he〉
satisfies the cancellation laws but not (*). It’s easy to show that any groupsatisfies (*), though:
gb = ga−1ab = ga−1cd = ga−1cee−1d
= ga−1afe−1d = gfe−1d = hee−1d = hd
So for the monoid with the presentation above, ηM sends the distinct ele-ments gb and hd to the same element of ηMM .
I think this justifies Leinster’s use of “tricky”.
2.3 2.1.13, p.49
The discrete categories have a bijection between their sets of objects. Proof:|A(FA,B)| = |B(A,GB)|, so FA = B iff A = GB because the categoriesare discrete. This means that F = G−1.
2.4 2.1.15, p.50
Since I is initial, |A(I, A)| = 1 for all A ∈ A. In particular, |B(FI,B)| =|A(I,GB)| = 1 for all B ∈ B, so FI is initial.

2 ADJOINTS 35
2.5 2.1.16(a), p.50
Let A be a G-set. First we list functors from [G,Set] to Set. (1) UA is theunderlying set A, i.e., forget the action. (2) Orb(A) is the set of orbits ofA under the action. (3) Fix(A) is the set of fixed points under the action.Defining the effect on morphisms (i.e., G-equivariant maps), and checkingfunctoriality, is routine for all of these.
Next, functors from Set to [G,Set]. Let X be any set. (4) Define the actiontrivially, leaving every element of X fixed; call this Triv(X) (5) Define anaction on G×X by g · (h, x) = (gh, x). Call this FX, so UF (X) = G×X.F is the “free” functor: we think of (g, x) as representing g · x as a “formalexpression”. (6) Let XG be the set of functions from G to X, and definethe action by (g · u)(k) = u(kg) for all u : G→ X and all k ∈ G. Call thisMap(X). We check that this is a left-action2:
(g · (h · u))(k) = (h · u)(kg) = u(kgh) = (gh · u)(k)
Defining the effect on morphisms and checking functoriality is trivial forTriv. With F , we set (Ff)(g, x) = (g, f(x)) for f : X → Y ; the requiredchecks are easy. With Map, we define (Map f)(u) as the composition G
u−→X
f−→ Y . Again the checks are easy.3
F a U . If r : X → UB where B has a G-action defined on it, definer : FX → B by r(g, x) = g · r(x). Easy to check that this is G-equivariant.For s : FX → B, define s : X → UB by s(x) = s(1, x) ∈ UB: technicallys(1, x) ∈ B, but we can regard it as an element of UB without harm. Toborrow some jargon from computer science, we “cast” elements of B toelements of UB, without loss of information. Easy to check that r = r ands = s. Finally, naturality: if p : X ′ → X and q : B → B′, we need to check
2This verification would not have worked if we had used the seemingly more naturaldefinition (g · u)(k) = u(gk).
3Defining Map with GX instead of XG results in a contravariant functor; this problemconcerns only covariant functors.

2 ADJOINTS 36
that rp = rF (p) and qs = U(q)s. Well,
rp(g, x′) = g · rp(x′) = g · r(px′)= r(g, px′) = r(F (p)(g, x′))
= (rF (p))(g, x′)
andqs(x) = qs(1, x) = U(q)s(x)
where the U(q) appears because we’ve cast s(1, x) from B to UB.
U a Map. Let r : A → Map(Y ). This time, A has the action and Y is aplain set. Define r : UA → Y by r(a) = (ra)(1), where 1 is the identityof G. (If we picture ra : G → Y as a G-indexed tuple, then r(a) is thecomponent at 1.)
Let s : UA → Y . Define s : A → Map(Y ) by first setting sa(k) = s(k · a)for all k ∈ G. So sa ∈ Y G. We then set s(a) = sa, making s a mappingfrom A to Map(Y ).
We describe sa another way. The mapping oa : k 7→ k · a (with k ∈ G) isrelated to the orbit of a in A—in fact, the orbit is the range of oa. Pictureoa as a G-indexed tuple of A-elements. Then sa is just the compositionG
oa−→ UAs−→ Y . In other words, we apply s to the tuple component-by-
component. (Also we’ve cast the codomain of oa from A to UA.)
We verify that s is equivariant. The requirement of equivariance is summedup in the “rectangle” diagram:
a 7→ oa 7→ sa
g · a 7→ og·a 7→ sg·a?= g · sa
and the bottom right equation checks out:
og·a(k) = k · (g · a) = kg · a = oa(kg) = (g · oa)(k)sg·a(k) = s(k · (g · a)) = s(kg · a) = sa(kg) = (g · sa)(k)

2 ADJOINTS 37
Note that s(a)(1) = sa(1) = s(1 · a) = s(a). That is, the sa tuple hascomponent s(a) at index 1. (Because the oa tuple has component a atindex 1.) But s(a)(1) is just the definition of s(a). So s = s.
As for r, write ra = r(a), so ra is a G-indexed tuple, and r(a) = ra(1). Sincer is equivariant, we have for any g, k ∈ G
rg·a = g · rarg·a(k) = (g · ra)(k) = ra(kg)
rg·a(1) = ra(g) letting k = 1
Now we compute r(a)(g) for arbitrary a ∈ A, g ∈ G:
r(a)(g) = r(g · a)
= rg·a(1) = ra(g) = r(a)(g)
so r = r.
Naturality: let p : A′ → A and q : Y → Y ′. We need to show that rp = rUpand qs = (Map q)s. The proof just involves unwinding the definitions. Agood deal of currying goes on (e.g., the definition of s as s : a 7→ sa withsa : k 7→ s(k · a)), but the verifications consist of filling in all the argumentsand turning the crank. So to show rp = rUp, we show rp(a′) = rUp(a′)for all a′ ∈ A′—both sides work out to rpa′(1), with our convention thatr(a) = ra. To show qs = (Map q)s, we show qs(a)(k) = ((Map q)s)(a)(k)for all a ∈ A, k ∈ G. Here both sides work out to qs(k · a).
Orb a Triv. Let r : A → Triv(Y ) and s : Orb(A) → Y . Because r isequivariant and G acts trivially on Triv(Y ), r must send entire orbits inA to single elements in Triv(Y ). Of course s does the same. The onlydistinction between r and s is that r “sees” the individual elements of anorbit, but treats them all the same; s “sees” an orbit as a single thing. Thedefinitions of r, s, their duality, and the naturality equations are all verydirect.

2 ADJOINTS 38
Triv a Fix. Let r : X → Fix(B) and s : Triv(X) → B, with B having theaction and X being plain. Because s is equivariant and G acts trivially onTriv(X), the image of s must consist entirely of fixed elements. Abusingnotation, we could write s(X) ⊆ Fix(B). Not abusing notation, we writes : X → Fix(B). In the reverse direction, since r maps X to the fixedelements of B, r is equivariant when regarded as mapping Triv(X) to B;of course, it’s really r that maps Triv(X) to B. (The distinction between rand r being a range restriction plus casting.) All the verifications are easy.
See also §6.2 and §6.9(c).
2.6 2.1.16(b), p.50
Let V be a vector space, and let V be V with a G-action on it. Fix, Triv, U ,F , and Map all have analogs. Fix(V ) is the subspace left fixed by the action;
Triv(V ) is V with a trivial action; U(V ) is the underlying vector space;F (V ) consists of all formal finite sums
∑givi subject to the conditions
g(v+w) = gv+ gw. In other words, we find the subspace generated by theformal sums g(v+w) + g(−v) + g(−w), and divide out by it. (Variations inthis definition are possible, leading to isomorphic representations.) Finally,we make V G into a vector space by defining, for u, v ∈ V G and a a scalar,(u + v)(k) = u(k) + v(k) and (au)(k) = a(u(k)) (for all k ∈ G). The G-action (defined as before) is linear. (Thinking of V G as a vector space ofG-indexed tuples makes all the verifications pretty obvious.)
It is routine to check that Triv a Fix and F a U a Map.
However, we lose Orb. The orbits of V do not form a subspace. Simpleexample: let V = R2 under the action of the rotation group SO(2). Theorbits are circles, plus the origin. The sum gv + hw can lie on any circlebetween the circles for v + w and v − w (assuming |v| ≥ |w|).

2 ADJOINTS 39
2.7 2.1.17, p.50
First I describe the functors, then worry about the adjunctions. I writePresheaf(X) for the category of presheaves on the topological space X,i.e., the functor category [O(X)op,Set]. For this problem, I’ll let F and Gbe objects of Presheaf(X) and I’ll let A and B be sets, with f : A→ B afunction. When Y ⊇ Z are open subsets of X, there’s a unique morphismin O(X)op; call it Y ⊇→Z. Write just FY Z for F (Y ⊇→Z).
We need to know what morphisms in Presheaf(X) look like. As a functorcategory, the morphisms are natural transformations. So a morphism α :F ⇒ G is a family of maps αY : FY → GY making these diagrams commutefor all Y ⊇→Z:
FY GY
FZ GZ
αY
FY Z GY Z
αZ
I’ll use α for such a morphism.
Λ : Set → Presheaf(X): We need to describe a presheaf ΛA for each setA, and a morphism of presheaves Λf for each function f : A → B. LetΛA(∅) = A and let ΛA(Y ) = ∅ for each Y 6= ∅. The morphisms in ΛAare all empty functions except for 1A on ΛA(∅). Letting Λf = α, we needto define αY : ΛA(Y )→ ΛB(Y ) for each Y . Let α∅ = f and let αY be theempty function for all Y 6= ∅.
Π : Presheaf(X) → Set: We need to define a set ΠF for any F , and afunction Πα for any morphism α. Let ΠF = F∅. Let Πα = α∅. Thefunctoriality equation Π(αβ) = Π(α)Π(β) follows from the definition ofcomposition of natural transformations, which says that (αβ)∅ = α∅β∅.
∆ : Set→ Presheaf(X): As defined in the problem statement, ∆A is the
constant functor ∆A(Y ) = A for all Y and ∆AY Z = 1A for all Y ⊇→Z.

2 ADJOINTS 40
Γ : Presheaf(X)→ Set: Similar to Π. Let ΓF = FX. Let Γα = αX .
∇ : Set→ Presheaf(X): Similar to Λ. Let ∇A(X) = A and let ∇A(Y ) =1 for each Y 6= X, where 1 is some arbitrary singleton. The morphismsin ∇A are all “constantly 1” functions except for 1A on ∇A(X). Setting∇f = α for f : A→ B, we let αX = f and let αY be 11 for all Y 6= X.
One more functor from Set to Presheaf(X): ΦA(Y ) is the set of A-valuedfunctions with domain Y , and the morphisms are all restriction maps. (If wegive A a topology, we can ask that all the functions be continuous. With theindiscrete topology, this is automatic.) I’m disappointed that this functordoesn’t show up in this problem.
We have to show that Λ a Π a ∆ a Γ a ∇.
Λ a Π. Suppose α : ΛA ⇒ F . Since ΛA(Y ) = ∅ for all Y 6= ∅, all suchαY : ΛA(Y )→ FY are empty functions. So α is completely determined byα∅, which is a function A → F∅, and α∅ can be any such function. ButΠF = F∅, so α∅ is an arbitrary function A → ΠF . It is now clear thatΛ a Π except for a routine check of the naturality equations.
Π a ∆. Suppose α : F ⇒ ∆A. So for every Y , αY : FY → ∆A(Y ) = A.The naturality squares become triangles:
FY
A
FZ
αY
FY Z
αZ
So αY is determined by αZ , and in particular, all the α’s are determined byα∅. Now we compare with f : ΠF → A, i.e., f : F∅→ A, and we have thedesired 1–1 correspondence. All verifications are routine.

2 ADJOINTS 41
∆ a Γ. Suppose α : ∆A ⇒ F . Similar to Π a ∆—the naturality squaresbecome triangles:
FY
A
FZ
FY Z
αY
αZ
So α is completely determined by αX , and αX can be any function A →FX = ΓF . The rest is straightforward.
Γ a ∇. Very similar to Λ a Π. Let α : F ⇒ ∇A. All αY except for αX areuniquely determined as maps to a singleton, and αX can be any functionFX → ∇A(X) = A. Routine verifications.
See also §6.10.
2.8 2.2.10, p.56
Suppose f(a) ≤ b↔ a ≤ g(b). Now, f(a) ≤ f(a), so a ≤ g(f(a)) (applyingthe → implication). And g(b) ≤ g(b), so f(g(b)) ≤ b (applying the ←implication).
Suppose a ≤ g(f(a)) and f(g(b)) ≤ b, with f and g order preserving.Suppose f(a) ≤ b. Apply g to both sides: g(f(a)) ≤ g(b), so a ≤ g(f(a)) ≤g(b). Suppose a ≤ g(b). Apply f to both sides, so f(a) ≤ f(g(b)) ≤ b.

2 ADJOINTS 42
2.9 2.2.11, p.57
For (a), we have to show that F sends A′ = Fix(GF ) into B′ = Fix(FG)and vice versa for G. The definition of equivalence (1.3.15, p.34) is thensatisfied. For A ∈ A′, we have ηA : A ∼= GFA, so FηA : FA ∼= FGFA.That is, FA is isomorphic to FG(FA) via FηA. The triangle identity saysthat FηAεFA = 1FA, so εFA = (FηA)−1. Therefore εFA is an isomorphism.
For (b), Figs.1 and 2 give us plenty to work with. Start with the cases wherea unit or counit is marked ‘id’ or ‘iso’. (The latter means “canonically iso”,e.g., Orb(Triv(x)) = {x}.) This means that either A′ = A (unit=id/iso) orB′ = B (counit=id/iso). D a U for Set and Top is typical: Set′ = Set,but Top′ are the discrete spaces. (DU(X)→ X is continuous for any spaceX, but is an isomorphism only for discrete spaces.)
Let’s go down the list, looking for isos. For the pair C,D, LocConn′ arediscrete spaces. For U, I, Top′ are indiscrete spaces. For A,U , Group′ arethe abelian groups. For F,U on monoids and groups, Monoid′ are groups.Likewise with the pair U,R. For both (Orb, Triv) and (Triv, Fix) we haveG− set′ being the G-sets where G acts trivially.
Now for the non-iso cases. The F a U pair for Vect and Set is kind ofstrange. FU(V ) has dimension bigger than V , even when V is the zerospace. ηS : S → UF (S) is not surjective for any S. So it looks like Vect′
and Set′ are both empty categories.
It’s the same story for F a U with G-set and Set, except when G = 1. Inthat case, G− set′ = G− set and Set′ = Set, and the equivalence comesfrom forgetting and remembering the trivial action of G, which is the onlypossible one.

2 ADJOINTS 43
2.10 2.2.12(a), p.57
Assume A BF
⊥
G
. Using the notions of §1.11, we can state a stronger
result.
1. G is faithful iff εB is epic for all B ∈ B. (Dually, F is faithful iff ηA ismonic for all A ∈ A.)
2. G is full iff εB is split monic for all B ∈ B. (Dually, F is full iff ηA issplit epic for all A ∈ A.)
As noted in §1.11, if g is both split monic and epic, then g is an isomorphism.With this fact, we see that (1) and (2) imply the exercise. (I leave the dualversions as an exercise. Or just say “duality!” in a dramatic tone of voice.)
It helps to bear the naturality diagram in mind:
FGB B B′
GB GB GB′
εB
G
q
GF
1GB Gq
This means we have a 1–1 correspondence between the qεB morphisms andthe Gq1GB = Gq morphisms. For G to be faithful, we need q 7→ Gq to be1–1; for εB to be epic, we need q 7→ qεB to be 1–1. This is the essence of thefaithful/epic equivalence. For an algebraic proof (next two paragraphs), weuse the equations εB = 1GB and qεB = Gq implied by the diagram.
Epic implies faithful: Gq1 = Gq2 ⇒ q1εB = q2εB ⇒ q1εB = q2εB ⇒ q1 = q2.
Faithful implies epic: q1εB = q2εB ⇒ q1εB = q2εB ⇒ Gq1 = Gq2 ⇒ q1 = q2.

2 ADJOINTS 44
Next, split monic implies full: the key again is the naturality diagram.Suppose h : GB → GB′. We have to find a q with Gq = h. We can treat has going from the leftmost GB to GB′ on the right, along the bottom; thenh will go from FGB to B′, along the top. But we want q just to go from Bto B′. A left inverse λ to εB can cancel out the εB portion of the journey,giving the desired q : B → B′.
Here’s the formal argument. Since εB is split monic, let λεB = 1FGB.Given h : GB → GB′, set hλ = q : B → B′. Then hλεB = h = qεB. Henceh = qεB = Gq, as desired.
Full implies split monic: we want to find a λ making the composition
FGBεB−→ B
λ−→ FGB the identity. Again we appeal to the naturalitydiagram, letting q = λ and B′ = FGB:
FGB B FGB
GB GB GFGB
εB λ
G GF
1GB Gλ
We want λεB = 1FGB = ηGB, and the diagram yields λεB = Gλ, so usingthe fullness of G we choose a λ giving Gλ = ηGB. We then have
λεB = Gλ = ηGB
1FGB = ηGB, therefore
1FGB = λεB
as desired.
2.11 2.2.12(b), p.57
We go further than asked, and see how 2.2.12(a) applies, or doesn’t, formost of figs.1 and 2. See §1.11 for background on monics and epics.

2 ADJOINTS 45
The faithfulness assumption isn’t needed for the “split” implications, butthat won’t matter for this exercise. The assumption holds for all the cate-gories in figs.1 and 2, since the morphisms are all “really” functions subjectto conditions, namely homomorphisms, continuous maps, or equivariantmaps.
We begin with a chain of adjunctions.
Topological spaces: D a U a I. This diagram (not a commutativediagram) lays out the situation for the counit εD of D a U and the unit ηI
of U a I. Note that dashed arrows represent morphisms and solid arrowsfunctors.
DUT T IUT
UT
εDT
U
ηIT
D I
On the top, we have the topological space T sandwiched between the dis-crete space and the indiscrete space obtained from T . The morphisms arebijective—identities in Set—hence epic and monic respectively. This jibeswith part (a) of this exercise, since U is faithful. Left inverses do not (usu-ally) exist, since the set-theoretic inverses are not (usually) continuous. Asexpected, since U is not full—not all functions are continuous.
The diagram for the unit ηD and counit εI looks like this:
IX DX
UIX X UDX
U U
εIX
I D
ηDX
The unit and counit are both the identity function 1X . Both D and I arefull and faithful.
Locally connected topological spaces: C a D. D is full and faithful,

2 ADJOINTS 46
and the counit εX is an isomorphism. (Technically not the identity but thefunction {x} 7→ x.) The unit ηT “collapses components”, i.e., sends x to itscontaining component [x]. So ηX is (usually) not monic, and C isn’t faithful(the “fine details” of f are lost in going to Cf).
But ηT is split epic: let cT be a choice function, with cT ([x]) choosing apoint x ∈ [x] for each component. Then ηT cT = 1DCT . C is full becausegiven g : CT → CT ′ (g : [x] → g[x]), we just set f(x) = cT ′(g[x]) for allx ∈ T (so f sends entire components of T to single points in T ′).
G-sets: Orb a Triv a Fix. The counits of Orb and the units of Fix areisomorphisms:
OrbTriv(X) X FixTriv(X)
Triv(X)
εOrbX
∼=
Triv
ηFixX
∼=
Orb Fix
Triv is full and faithful, so all’s right with the world.
The units of Orb and the counits of Fix come out of this diagram:
Fix(X) Orb(X)
TrivFix(X) X TrivOrb(X)
Triv Triv
εFixX
Fix Orb
ηOrbX
Orb is somewhat but not entirely similar to Components: ηOrbX sends each
x to its orbit [x]. So clearly injectivity fails, and it’s no sweat to bootstrapthis to a failure of monicity. Let G be transitive on X, so ηOrb
X sendsX to a singleton. Now we just need a pair of distinct equivariant mapsf, g : X ′ → X, and we’re home free. To show that Orb is not faithful, takeG is transitive on X with two distinct equivariant maps X → X.

2 ADJOINTS 47
Unlike Components, ηOrbX is not always split epic and Orb is not full. Ex-
ample: let X be a nonempty set, let X1 be X with G acting trivially,and let X2 be X with a G-action that acts without fixed points. (I.e.,(∀x ∈ X)(∃g ∈ G)g · x 6= x.) Then there are no equivariant maps fromX1 to X2, but there is obviously at least one function from Orb(X1) toOrb(X2). So Orb isn’t full. As for ηOrb
X , it’s surjective and hence epic, butnot split epic; X = X2 provides an example.
As for Fix, it’s neither faithful nor full. If f : X → X ′ is an equivariant map,then Fix(f) is the restriction of f to Fix(X). So Fix(f) tells you nothingabout what’s going on with the non-fixed points of X, demonstrating thelack of faith. Suppose G acts without fixed points on X 6= ∅. Then εFix
X
is the empty map ∅ → X, monic but not split monic. Also, there are nomaps X → ∅, but we have the empty function Fix(X) = ∅→ ∅, showingthe lack of fullness. (Mini-exercise: cook up an example with no equivariantmaps X → X ′, but Fix(X) = Fix(X ′) = ∅.) Although not full, Fix is fullon the full subcategory of G-set consisting of those X with Fix(X) 6= ∅.
G-sets: F a U a Map. For the unit of Map and the counit of F we lookat this diagram:
FU(X) X MapU(X)
UX
εFX
U
ηMapX
F Map
The unit ηMapX is x 7→ ox, where ox was defined in §2.5 as the G-indexed tuple
g 7→ g ·x. This is injective and hence monic, but generally not surjective andhence not split epic. (For an easy example, let X be finite and G nontrivial,so |XG| > |X|.)
The theorem says that U must be faithful but not full. Easily checkeddirectly.

2 ADJOINTS 48
The counit εFX is (g, x) 7→ g · x. This is surjective and hence epic, but notinjective and hence not split monic (unless G is trivial). The theorem saysthat U must be faithful but not full, duplicating what we already know fromηMapX .
The unit of F and the counit of Map come out of this diagram:
Map(X) FX
UMap(X) X UF (X)
U U
εMapX
Map F
ηFX
The unit ηFX is x 7→ (1, x). This is injective and hence monic, but notsurjective and hence not split epic (unless G is trivial). So the theorem saysthat F must be faithful but not full. Faithfulness is obvious. To show thatF is not full, we need an equivariant map FX → FY that is not Ff forany f : X → Y . Now, (Ff)(g, x) = (g, f(x)). On the other hand, if h ∈ Gis not 1 and p : X → Y is arbitrary, then (g, x) 7→ (gh, p(x)) is equivariantand not equal to Ff for any f .
The counit εMapX is u 7→ u(1), where u ∈ XG and 1 is the identity of G. This
is surjective (because ox(1) = x) and hence epic, but generally not injectiveand hence not split monic. (Again X finite and G nontrivial provides aneasy example, via cardinalities.)
The theorem tells us that Map is faithful but not full. Faithfulness is easy:if f1, f2 : X → Y are distinct, say f1(x) 6= f2(x), then if u(1) = x, we havef1u 6= f2u, i.e., Mapf1 6= Mapf2.
To show Map is not full, we need an equivariant map MapX → MapY notequal to Mapf for any f : X → Y . When X = Y , we can construct anequivariant map this way: let g ∈ G, and define ug : k 7→ u(gk), and finallyg : u 7→ ug. In other words, we act on the left. This is equivariant because
(h · (gu))(k) = (h · ug)(k) = ug(kh) = u(gkh) = (h · u)(gk) = (g(h · u))(k)

2 ADJOINTS 49
In other words, since g acts on the left and h· on the right, they don’tinterfere with each other and can be applied in either order with the sameresult.
Now we have to insure that g 6= Mapf for all f : X → X. Let X havetwo elements, say X = {0, 1}. Let u be the function taking 1 ∈ G to 1and all other elements of G to 0. Then ug(k) = u(kg) equals 1 iff k = g−1.So if g1 6= g2, then g1 6= g2. So as g ranges over G, we get |G| differentequivariant functions g. On the other hand, there are only four functionsf : X → X, and so only four different Mapf ’s. Thus if |G| > 4, Map isnot full. (With a moment’s thought you can see that this works whenever|X| > 1 and |G| > |XX |.)
Monoids and groups: F a U a R. (See §2.2 for some background.)
Example 2.1.3(d) (p.45) introduced the functor R : Monoid → Group,sending a monoid to its group of invertible elements. R is the right adjointto U . I don’t know a standard term for RM , but I’ll call it the invertiblecore of the monoid. People write M× for it (at least when ‘·’ is used for theoperation of the monoid M), not distinguishing between RM and URM .
We construct the (by now familiar) diagram:
FUG G RUG
UG
εFG
U
ηRG
F R
All elements of a group G are invertible, so ηRG is the identity map on G.It turns out that εFG is too: if a monoid M happens to be a group, thenUFM is just M . As expected, U is full and faithful: if f : M → M ′ isa monoid homomorphism, and M and M ′ happen to be groups, then f isalso a group homomorphism. The “groupness” of the source and targetdon’t impose any additional constraints on f . (Contrast with the forgetfulfunctor from Group to Set.)

2 ADJOINTS 50
Here’s the other diagram:
RM FM
URM M UFM
U U
εRM
R F
ηFM
Start with right hand triangle. F is neither full nor faithful, and ηFM isneither split epic nor monic (in general). First example: ηN : N→ Z, underaddition. Although epic, ηN is not surjective (see Exericse 5.2.23, §5.12)and hence not split epic. F isn’t full, because if p : N → N is a monoidmorphism, then Fp : Z → Z must send 1 to a nonnegative integer, unlikesome group morphisms from Z to Z.
Neither is ηM always monic. The monoid of all functions from a two-elementset to itself furnishes a counterexample (see §2.2), and shows that F isneither faithful nor full.
Turn to the left hand triangle. R isn’t faithful, and εRM isn’t epic for certainmonoids. Simple example: the only invertible element of N is 0, so URN→URN devolves to the trivial morphism from {0} to {0}. But we have amorphism k : N → N, k : n 7→ kn for every k ∈ N. Obviously εRN isn’t
surjective, but it’s also not epic: εRN k = εRN for all k.
Note that εRM is the inclusion morphism, so it’s injective and hence monic,but is it split monic? That is, do we have a morphism ϕ : M → URMthat is the identity when restricted to URM? Not in general. Simplecounterexample: M = (Z, ·). URM = {±1}. A morphism ϕ : M → URMmust satisfy (ϕ0)(ϕ0) = ϕ0, hence ϕ0 = 1, hence ϕ(−1) = ϕ(−1)1 =ϕ(−1)(ϕ0) = ϕ(−1 ·0) = ϕ0 = 1. But −1 ∈ URM , so ϕ restricted to URMisn’t the identity. Variation: let M = G t {0} where G is any nontrivialgroup and we define 0 · g = g · 0 = 0 for all g ∈ G. Then URM = G andthe same argument shows that ϕ : M → G must send everything to 1.
Abelian Groups: A a U . U is full and faithful because homomorphisms

2 ADJOINTS 51
between two groups which both happen to be abelian are just group homo-morphisms. (Just like the forgetful functor from Group to Monoid.) Andthe counit is an isomorphism.
The unit ηX is the canonical epimorphism of X onto the abelianized UAX.A is neither faithful nor full. Thus, ηX is neither monic nor split epic. Notmonic: look at the exact sequences
C2 ⇒ S3
η� C2
There are three transpositions in S3, and so three ways to inject C2 into S3.The commutator subgroup of S3 is A3 = C3, so A(S3) = C2. Therefore thecompositions are all the identity.
I found an example on the internet showing that A is not full. Let Q bethe quaternion group {±1,±i,±j,±k}. The commutator subgroup is {±1}(easy to check, since −1 is in the center and i, j, k have cyclic symmetry).So AQ = C2×C2. There are only two homomorphisms from C2 to Q (since−1 is the only element of order 2), but four homomorphisms from A(C2) toA(Q), i.e., from C2 to C2 × C2.
Liberation: F a U . The remaining two examples from figs.1 and 2 involvea free functor and a forgetful functor, in each case going between a categoryof “algebraic things” and Set. The unit ηX : X → UFX maps a setto the underlying set of the “free algebraic thing”; I call this liberation(instead of freeification). The counit εA : FUA→ A corresponds to a kindof evaluation.
The figures give just two examples, Vect and G-set. Free groups andfree monoids follow the same pattern. G-set by far provides the simplestillustration, and it’s typical. (See §2.5 for definitions.)
Let X be a set; then UFX = G × X and ηX : x 7→ (1, x). We see im-mediately that ηX is monic (≡ injective) but not split epic (≡ surjective),provided G 6= 1. Thus F is faithful but not full. To see these facts ex-plicitly, note that if ϕ : X → Y is a function, then Fϕ : (g, x) → (g, ϕx).

2 ADJOINTS 52
So if ϕ 6= ϕ′ then clearly Fϕ 6= Fϕ′. To show non-fullness, let X = Y ;pick a g0 ∈ G, g0 6= 1, and define ψ : (g, x) 7→ (gg0, x). Verification thatψ is equivariant takes but a moment, and obviously ψ is not Fϕ for anyϕ : X → X.
Let A be a G-set. Then FUA is the set G × A equipped with the actiong · (h, a) 7→ (gh, a), and εA : (h, a) 7→ h · a. We check that εA is equivariant:
(h, a) h · a
(gh, a) gh · a
εA
g· g·
εA
We see immediately that εA is surjective and thus epic, but isn’t injective(for G 6= 1) and thus isn’t split monic. Hence U is faithful but not full.Both these facts can be seen directly without breathing hard.
2.12 2.2.13(a), p.57
Write fA for the image of A ⊆ K, and f ∗B = f−1B for the inverse imageof B ⊆ L. Partition L into I t N with I = fK and N = LrfK. Alsowrite a ≡ a′ if f(a) = f(a′), and let [a] be the equivalence class of a. For
A ⊆ K, let A be the union of the equivalence classes of elements of A; inother words, A = {x|x ≡ a for some a ∈ A}.
The following two computations are routine:
ff ∗B = B ∩ I ⊆ B
f ∗fA = A ⊇ A
Recall that the categories P(K) and P(L) are posets, with a unique mor-
phism S ⊆→T when and only when S ⊆ T . The equations just given show

2 ADJOINTS 53
that we have a unit and a counit:
ηA : A ⊆→f ∗fAεB : ff ∗B ⊆→B
The triangle identities are satisfied automatically, since f and f ∗ are func-tors (i.e., order-preserving) between posets. So by Theorem 2.2.5 (p.53) ofLeinster, f a f ∗.
For the right adjoint to f ∗, we need to find a g : P(K) → P(L) such thatB ⊆ gf ∗B and f ∗gA ⊆ A for all A ⊆ K, B ⊆ L. For any A ⊆ K, defineA◦ to be the union of those equivalence classes that are contained in A, i.e.,A◦ =
⋃[a]⊆A[a]. So A◦ = f ∗f(A◦) = A◦. Also, (f ∗B)◦ = f ∗B.
SetgA = f(A◦) ∪N
(Recall that N is the complement of the image fK, so f ∗N = ∅. Also, theunion is disjoint, but we won’t need that.) We compute:
f ∗gA = f ∗(f(A◦) ∪N)
= f ∗fA◦ ∪ f ∗N = A◦ ∪∅= A◦ ⊆ A
and
gf ∗B = f((f ∗B)◦) ∪N= ff ∗B ∪N = (B ∩ I) ∪N⊇ (B ∩ I) ∪ (B ∩N) = B
So f ∗ a g.

2 ADJOINTS 54
2.13 2.2.13(b), p.57
Notation as in part (a). We write Sx to mean x ∈ S, and xRy to mean(x, y) ∈ R. Since p is onto, N = ∅ and gR = pR◦. So:
pR = S : Sx⇔ (∃y)xRy
p∗S = R : xRy ⇔ Sx
(x, y) ≡ (x′, y′) : x = x′
[(x, y)] = {x} × Y
R◦ =⋃
[(x,y)]⊆R
[(x, y)] : xR◦y ⇔ (∀y′)xRy′
gR = pR◦ = S : Sx⇔ (∃y)xR◦y ⇔ (∃y)(∀y′)xRy′
⇔ (∀y′)xRy′
We’ve made use of the fact that the assertion (∃y)ϕ(x) is equivalent to ϕ(x)if the latter does not mention y.
Units and counits for p a p∗:
x(p∗pR)y ⇔ (pR)x⇔ (∃y)xRy
(pp∗S)x⇔ (∃y)x(p∗S)y ⇔ (∃y)Sx⇔ Sx
So:
R ⊆ p∗pR : xRy ⇒ (∃y)xRy
pp∗S ⊆ S : Sx⇒ Sx
Units and counits for p∗ a g:
(gp∗S)x⇔ (∀y′)x(p∗S)y′ ⇔ (∀y′)Sx⇔ Sx
x(p∗gR)y ⇔ (gR)x⇔ (∀y)xRy
So:
S ⊆ gp∗S : Sx⇒ Sx
p∗gR ⊆ R : (∀y)xRy ⇒ xRy

2 ADJOINTS 55
(Changing dummy variables may make these look a bit nicer: xRy ⇒(∃y′)xRy′ and (∀y′)xRy′ ⇒ xRy.)
2.14 2.2.14, p.57
This is a classic “unwind the definitions” exercise. Since F a G, we have theunit/counit pair η/ε satisfying the triangle identities. We need to constructa unit/counit pair η∗/ε∗ with η∗ : 1[A,S] ⇒ F ∗G∗, ε∗ : G∗F ∗ ⇒ 1[B,S],satisfying the triangle identities.
First we write out what objects, morphisms, functors, natural transforma-tions, and units and counits look like for the functor categories [A,S] and[B,S]. Rather than describe functors in general, we just consider F ∗ andG∗, and how they act on objects and morphisms. Among the natural trans-formations, we consider only the unit and counit. As usual, f : A → A′ isa typical morphism between objects of A, likewise g : B → B′ for B.
Objects: X : A → S Y : B → SMorphisms: α : X ⇒ X ′ β : Y ⇒ Y ′
αA : XA→ X ′A βB : Y B → Y ′BFunctors: G∗X = XG : B → S F ∗Y = Y F : A → S
G∗X : B 7→ XGB F ∗Y : A 7→ Y FAG∗X : g 7→ XGg F ∗Y : f 7→ Y FfG∗α = αG : XG⇒ X ′G F ∗β = βF : Y F ⇒ Y ′FαGB : XGB → X ′GB βFA : Y FA→ Y ′FA
Unit andcounit:
η∗X : X ⇒ F ∗G∗X = XGF ε∗Y : G∗F ∗Y = Y FG⇒ Y
(η∗X)A : XA→ XGFA (ε∗Y )B : Y FGB → Y B

2 ADJOINTS 56
The naturality squares for η∗X and ε∗Y look like this:
XA XGFA Y FGB Y B
XA′ XGFA′ Y FGB′ Y B′
(η∗X)A
Xf XGFf
(ε∗Y )B
Y FGg Y g
(η∗X)A′ (ε∗Y )B′
Compare with the naturality squares for η and ε:
A GFA FGB B
A′ GFA′ FGB′ B′
ηA
f GFf
εB
FGg g
ηA′ εB′
Clearly if we apply X to the square for η, and Y to the square for ε, we getthe squares for η∗X and ε∗Y . So we set
(η∗X)A = XηA, (ε∗Y )B = Y εB
Now we have to check the triangle identities. These involve both horizontaland vertical composition of natural transformations (pp.30, 37), so here arethe formulas for those:
(αβ)A = αAβA, (Fα)A = FαA, (αF )A = αFA
(We need only the special cases of horizontal composition.) We can rewritethe definitions of η∗ and ε∗:
η∗X = Xη, ε∗Y = Y ε
For the original η and ε, the triangle identities read (p.52)
εF Fη = 1F , Gε ηG = 1G

2 ADJOINTS 57
Here is one of the triangle diagrams for η and ε, written at the componentlevel, and the corresponding diagram for η∗ and ε∗:
FA FGFA G∗X G∗F ∗G∗X
FA G∗X
FηA
1FA
εFA
G∗η∗X
1G∗Xε∗G∗X
In the right hand diagram, the arrows all represent natural transformations.We check that it commutes:
(ε∗G∗X)(G∗η∗X) = ((G∗X)ε)(G∗(Xη))
= (XGε)(XηG) = X(Gε ηG)
= X(1G) = 1XG
These equations are all between natural transformations. For example,(ε∗G∗X) is a natural transformation whose components are (ε∗G∗X)B (withB ∈ B). Rewritten at the component level, the computation is longer, butmaybe easier to follow.
((ε∗G∗X)(G∗η∗X))B = (ε∗G∗X)B(G∗η∗X)B
= ((G∗X)εB)(η∗XG)B
= (XGεB)(η∗X)GB
= (X(GεB))(X(ηGB))
= X(GεB ηGB) = X(1GG) = 1XGB
The verification of the other triangle identity is similar.
2.15 Initial Objects in the Comma Category
Among all the comma categories, the slice and coslice categories lend them-selves best to intuition. The category (A⇒ G) lies just a tweak away fromthe coslice category A/A (p.60). So we’ll start with that.

2 ADJOINTS 58
An initial object e : A → A0 of A/A has the defining property that givenany f : A→ B, there is a unique q completing the diagram
A A0
B
e
fq
Obviously 1A : A → A satisfies this condition. Any A0 that is uniquelyisomorphic to A does also.
The category (A ⇒ G) lifts the object B and morphism q to an “index”category B. Think of B ∈ B as a “name” for the object GB ∈ A, and qin B as a “name” for Gq. Instead of starting with an f : A → B (both Aand B in A), we start with f : A → GB. Instead of asking for a uniqueq : A0 → B in A, we ask for a unique q : B0 → B in B. The commutingtriangle still lives in A:
A GB0
GB
e
fGq
Setting B0 = FA and e = ηA, we have the situation of Lemma 2.3.5 (p.60):(FA, ηA) is the initial object of (A ⇒ G), or speaking casually, ηA : A →GFA is.
This lifting to B imposes three constraints. First, the morphism f : A →GB must be to a named object in A. Second, the completing morphism Gqmust be named. Third, the name q must be unique (not the image Gq).Let’s see how these play out in some examples. (Consult figs.1 and 2.)
Topological Spaces. Let’s think about completing the triangle, i.e., find-ing q : FA → B such that f = (Gq)ηA. In all three cases, f determinesq “set-theoretically”. That is, if f is in Set (case D a U) then Uq = f ;

2 ADJOINTS 59
if f is in Top (other two cases) then Uf determines q. In the first twocases (U a I and D a U), f and q are “basically the same” once we ignoretopologies. In the remaining case, we need to do a bit more work: we’regiven f : A → DB (A a locally connected space, B a set), and a ∈ A, andwe need to figure out where q[a] lands (with [a] being the component of a).Chasing the diagram yields q[a] = f(a). The result doesn’t depend on thechoice of a because f is continuous and DB is discrete. Note the criticalrole of the “target constraint”.
In the case D a U , we have a last step: we need to remember the topologyof UB, taking us from Uq to q. All we really need to check is continuity,but this follows from the discreteness of the source: q : DA→ B.
Monoids. Case F a U : given a monoid A, a group B, and a monoidhomomorphism f : A → B, we want a unique group homomorphism q :FA→ B for which f(a) = q(ηA(a)) for all a ∈ A. Not much to say, exceptthat the (non-trivial) construction of FA is designed to insure this. Caveat:ηA might not be injective.
Case U a R: given a group A, a monoid B, and a group homomorphismf : A → RB, we want a unique monoid homomorphism q : UA → B forwhich f(a) = q(ηA(a)) for all a ∈ A. This time ηA = 1A, so q = f , prettymuch. To be picky about it, f is a group homomorphism and q is a monoidhomomorphism, so really Uf = q, but U doesn’t do anything to f exceptchange its official domicile.
Abelian groups. This is practically the same story as U a R for monoids.
G-sets. Orb a Triv. This resembles C a D for locally connected spaces.Given a G-set A, a set B, and an equivariant map A → Triv(B), we wanta unique q : Orb(A) → B making the triangle commute. The target con-straint (that G acts trivially on Triv(B)) forces entire orbits of A to mapto single elements of B. That defines q uniquely.
Triv a Fix. This resembles U a R for monoids, with “fixed point” replacing

2 ADJOINTS 60
“invertible element”. Given a set A, a G-set B, and a function f : A →Fix(B), we want a unique equivariant q : Triv(A)→ B making the trianglecommute. Essentially q = f , more precisely q = Triv(f).
F a U . Given a function f : A → UB with A a set and B a G-set, wewant a unique q : FA → B making the triangle commute. This time the“morphism constraint” plays the decisive role. The unit ηA : A → UFA isan injection a 7→ (1, a). So we have a well-defined f : {1} × A→ UB withf(a) = f(ηA(a)) for all a. The commuting triangle says that Uq extends fto all of G×A. Now, extending f isn’t hard, but it’s the equivariance of qthat makes it unique. The target constraint doesn’t narrow things down atall, since any set can be turned into a G-set.
Vector spaces; groups. Similar to F a U for G-sets. Again it’s the mor-phism constraint that makes things work. For groups, the target constraintdoesn’t really constrain. For vector spaces over R, the target constraintsays that UB must look like Rn for some n. (Of course, we could replace Rwith any other field.)
Final note: Suppose U : C → Set is a forgetful functor, and A is a set.The comma category (A ⇒ U) consists of pairs (C, f : A → UC). If A isa singleton, these are “pointed C objects”. Familiar examples: pointed setsand pointed topological spaces. The category (A ⇒ U) generalizes this to“C objects with A dropped in”. I like to think of the pair (C, f : A→ UC)as a “labeled” object C; f “labels” certain elements of C. Morphisms in(A ⇒ U) are morphisms in C that “respect the labels”, i.e., the morphismtakes any element labeled a to an element also labeled a, for all a ∈ A.Note that the same element of C can carry multiple labels: f needn’t beinjective.
We’ll make use of labeled groups in §6.13.

2 ADJOINTS 61
2.16 2.3.8, p.63
Lemma 2.2.4 (p.52) says:
g = (Gg)ηA; f = εB(Ff)
where f and g are morphisms in A and B respectively. (Since A ∈ Aand B ∈ B are the unique objects of the two categories, the conditionsf : A→ GB and g : FA→ B hold automatically.) Rewrite:
Gg = gη−1A ; Ff = ε−1
B f
Applying G to the equation for Ff , and then using the equation for Ggwith g = f :
GFf = (GεB)−1Gf = (GεB)−1fη−1A
In other words,GFf = (GεB)−1fη−1
A
If f = 1A, we get
1A = (GεB)−1η−1A so ηA = (GεB)−1
and soGFf = ηAfη
−1A
In other words, the group endomorphism f 7→ GFf is the same as the innerautomorphism f 7→ ηAfη
−1A . Likewise, FGg = ε−1
B gεB. It follows that Fand G are group isomorphisms, and moreover F−1 is G composed with aninner automorphism.
2.17 2.3.10, p.63
Let F : A → B, G : B → A, with ηA : A → GFA and εB : FGB → Bisomorphisms for all A ∈ A, B ∈ B (as in Def. 1.3.15 p.34). We have

2 ADJOINTS 62
to show that for any f : A → GB ∈ A there is a unique q : FA → Bcompleting the diagram
A GFA
GB
ηA
fGq
Because ηA is an isomorphism, Gq is determined uniquely by Gq = fη−1A .
Because G is an equivalence, it is full and faithful (Prop.1.3.18 p.36, provedin Ex.1.3.32 §1.8) so q is also determined uniquely.
2.18 2.3.11, p.63
Suppose UA has at least two elements. Let S be a set. Since ηS is aninitial object of (S ⇒ U) (Lemma 2.3.5, p.60), for any f : S → UA we cancomplete the diagram with a function Up:
S UFS
UA
ηS
fUp
If ηS isn’t injective, say ηS(x1) = ηS(x2) for x1 6= x2, then any functionf : S → UA with f(x1) 6= f(x2) makes it impossible to complete thediagram.
Say FS is the free group for a set S. This exercise says that we can regardS as a subset of FS. (Technically, there is a canonical injection of S intoFS, or even more technically, into UFS.) Contrast with the free group FMfor a monoid M , where the map M → UFM isn’t always injective. (Forexample, when cancellation fails in M , i.e., when cx1 = cx2 with c 6= 0 andx1 6= x2, M → UFM isn’t injective.)

3 INTERLUDE ON SETS 63
2.19 2.3.12, p.64
For every A in Par, add a new element ∗A to it to get a set in Set∗. So wehave a mapping FA = A t {∗A} from Par to Set∗. To make F a functor,let f be a partial function f : A 99K B, say f : S → B with S ⊆ A. DefineFf by having it agree with f on S and having it send everything in ArSto ∗B. Also of course Ff sends ∗A to ∗B. For the reverse functor G fromSet∗ to Par, let GA be A with the basepoint removed. If g : A → B is abasepoint preserving function, let Gg be the partial function obtained byfirst restricting g to GA, and then letting Gg(a) be undefined for all a ∈ GAfor which g(a) is the basepoint of B. It is routine to verify that FG andGF are equivalent to the identities on Set∗ and Par.
As for the choice of ∗A, by far the simplest solution is to let ∗A = {A}, sincethe Foundation axiom of set theory forbids a set from being an element ofitself.
To interpret Set∗ as a coslice category, let ∗ be a singleton (say, {∅}).Objects of ∗/Set are functions f : ∗ → A, or basically nonempty sets withbasepoints. Writing A∗ for f : ∗ → A and B∗ for g : ∗ → B, a morphism
A∗ → B∗ is a function h : A→ B such that the composition ∗ f−→ Ah−→ B is
∗ g−→ B, i.e., a basepoint preserving function.
3 Interlude on Sets
3.1 3.1.1, p.73
The right adjoint is the cross-product (A,B) 7→ A × B, the left adjoint isthe disjoint union (A,B) 7→ A t B. The initial object property (Theorem2.3.6, p.61) provides the easiest demonstrations. First, the cross-product:the unit ηA is a 7→ (a, a). We have to verify that for any f : A → B1 × B2

3 INTERLUDE ON SETS 64
we have a unique (q1, q2) : (A,A)→ (B1, B2) with
A A× A
B1 ×B2
ηA
fq1×q2
However, a function f : A → B1 × B2 is basically a pair of functionsf1 : A → B1, f2 : A → B2, so obviously (q1, q2) = (f1, f2) is the uniquecompleting morphism.
Next, disjoint union. The unit maps (A1, A2) → (A1 t A2, A1 t A2), andsends a1 ∈ A1 to (a1, a1), a2 ∈ A2 to (a2, a2). (Here we regard A1 and A2
as subsets of A1 t A2, a harmless abuse of notation.) We want the unique∆q = (q, q) completing the diagram
(A1, A2) (A1 t A2, A1 t A2)
(B,B)
η(A1,A2)
f∆q
Now f : (A1, A2) → (B,B) is just a pair of functions f1 : A1 → B, f2 :A2 → B. There is a unique q completing the diagram
A2
A1 A1 t A2
B
f2
f1
q
defined by q(a1) = f1(a1) for a1 ∈ A1, q(a2) = f2(a2) for a2 ∈ A2. Then ∆qis the completing morphism for the previous diagram.

3 INTERLUDE ON SETS 65
Leinster introduces products and coproducts in Chapter 5, at which pointwe’ll see that the cross-product is the product and the disjoint union is thecoproduct in Set.
3.2 3.1.2, p.73
Let the objects of C be triples (N, 0, s) where X is a set, 0 : • → N is afunction from some arbitary fixed singleton set • to N , and s : N → N is afunction from N into itself. The morphisms of C are commuting diagrams
• N N
X X
0
a
s
x x
r
(N, 0, s) is an initial object in this category. (Note that the two functionslabelled x in the diagram must be the same, i.e., this is part of the definitionof the morphisms. We regard 0 as a function singling out the element zeroof N, likewise a.)
3.3 3.2.14, p.77
(a) Assume F a U . Let S = P(⋃
i∈I UAi). Then |UAi| < |S| for all i. Let
A = FS. If A ∼= Ai, then UA ∼= UAi, i.e., |UA| = |UAi|. But we know that
|UAi| < |S| ≤ |UFS| = |UA|
with |S| ≤ |UFS| because ηS : S → UFS is injective (Ex. 2.3.11 §2.18).
(b) This is trivial: pick a representative Ai from each equivalence class. IfA were essentially small, the Ai’s would form a small family (Ai)i∈I with Ia set. By (a), there is an A ∈ A not isomorphic to any of the Ai’s.

4 REPRESENTABLES 66
(c) Also trivial, since all these categories satisfy the hypotheses of (a).
3.4 3.2.16, p.78
This resembles the chain of adjoints for locally connected topological spaces.For a set S we define the indiscrete small category IS as having all theelements of S as objects, and a unique morphism from a to b for any a, b ∈ S.(So IS is a preorder.) The discrete small category DS has all the elementsof S as objects, and no morphisms except for the identities. Given any smallcategory T , there are unique functors DS → T and T → IS.
Note that if F : T → DS is a functor, and if there is a morphism a → bbetween two objects of T , then we must have Fa = Fb. This inspires thedefinition of CT for a small category T : form the graph whose nodes arethe objects of T , with an undirected edge between any two nodes when amorphism exists between them. Let CT be the set of connected componentsof this graph. It is routine to check that C is left adjoint to D.
For OT the set of objects of T , the adjunctions D a O a I are immediate.
4 Representables
4.1 4.1.27, p.93
The isomorphism HA∼= HA′ means that for any B ∈ A we have an isomor-
phism in Set ηB : HA(B) → HA′(B), i.e., a bijection between Set(B,A)and Set(B,A′). Borrowing notation from adjoints, let’s write f : B → A′
for the function corresponding to f : B → A, and also g : B → A for the
function corresponding to g : B → A′. We have f = f and g = g.

4 REPRESENTABLES 67
The naturality requirement says that for any q : B → B′, this diagramcommutes:
HA(B) HA(B′)
HA′(B) HA′(B′)
ηB
HA(q)
ηB′
HA′ (q)
Now, HA(q) and HA′(q) are both pullbacks, where we compose with q onthe right: HA(q) : f 7→ fq, likewise for HA′(q). So naturality says that:
fq = fq for any q : B → B′ and any f : B′ → A′
gq = gq for any q : B → B′ and any g : B′ → A
We apply the first equation with B = A, B′ = A′, and f = 1A′ ; we applythe second with B = A′, B′ = A, and g = 1A. This gives us:
q = 1A′ q for any q : A→ A′
p = 1A p for any p : A′ → A
where we’ve replaced q with p in the second equation for clarity, since thedomains and codomains are switched.
Note that 1A′ : A′ → A and 1A : A→ A′. So we can set q = 1A and p = 1A′ .This gives us:
1A = pq
1A′ = qp
with q : A′ → A and p = A→ A′. In other words, A ∼= A′.

4 REPRESENTABLES 68
4.2 4.1.28, p.93
For G a group and p a prime, Up(G) = {x ∈ G|xp = 1}. If h : G → His a group homomorphism, then h maps Up(G) into Up(H) since [h(x)]p =h(xp) = h(1) = 1. So we let Up(h) be the restriction of h to Up(G).
As Leinster noted on p.83, there is a unique homomorphism µx : Zp → G forany x ∈ Up(G) determined by setting µx(1) = x (and hence µx(n) = xn);conversely, ϕ(1) ∈ Up(G) for any homomorphism ϕ : Zp → G. (Note:Zp = Z/pZ for us, not the p-adics.) So we have the required bijectionbetween Up(G) and Group(Zp, G), namely x↔ µx. Naturality is expressedby the commutative diagram
x µx
h(x) hµx
Up(h) HZp (h)
or by the equation (for any h : G→ H)
µh(x) = hµx
But for any n ∈ Z, we have
µh(x)(n) = (h(x))n; hµx(n) = h(xn)
so naturality holds. (It would have been enough to check the equation forn = 1, getting h(x) on both sides.)
4.3 4.1.29, p.93
This is virtually the same as Exercise 4.1.28. Exercise 0.13(a) says thatfor every commutative ring R and every element r ∈ R, there is a unique

4 REPRESENTABLES 69
ring homomorphism µr : Z[x] → R defined by µr(x) = r; hence, everyring homomorphism ϕ : Z[x] → R is µr for r = ϕ(x). (Recall that everycommutative ring is assumed to have a multiplicative identity, and everyring homomorphisms is assumed to preserve it: p.2.)
So again we have a 1–1 correspondence r ↔ µr, and to check naturality, wecheck the equation
µh(r) = hµr
which we check by evaluating at x ∈ Z[x], getting h(r) on both sides.
4.4 4.1.30, p.93
Let S = {0, 1} with {1} open and {0} closed. (I think this reverses the usualconvention, but it’s more convenient for this problem.) Let f : X → S becontinuous; then f−1{1} is open. Conversely, if U is an open subset of X,then the characteristic function χU is continuous. So there is a bijectionbetween Top(X,S) and open subsets of X, U ↔ χU .
To show that HS is equivalent to O, we need to check naturality. Leth : X → Y be continuous. Here we are dealing with contravariant functors,so naturality boils down to the equation
χh−1(V ) = χV h (V ⊆ Y );
note that the left hand side is χO(h)(V ), and the right hand side is HS(h)(χV ).We verify that the two functions (both mapping X → S) are the same byshowing they both give the inverse image of {1}. This follows from theseequivalences, for any x ∈ X:
χh−1(V )(x) = 1⇔ x ∈ h−1(V )⇔ h(x) ∈ V ⇔ χV (h(x)) = 1

4 REPRESENTABLES 70
4.5 4.1.31, p.93
Let T be the “arrow category” consisting of two objects 0 and 1 with threemorphisms: 10, 11, and a unique morphism a : 0 → 1. We show that M isnaturally equivalent to HT = Cat(T ,−).
For any small category A, an element of Cat(T ,A) is a functor F : T → A.So it determines objects F0, F1 ∈ A, and a morphism Fa : F0→ F1. (Theidentity morphisms 10 and 11 take care of themselves.) Conversely, givenany morphism f : A0 → A1 in A, we construct a functor F by settingF0 = A0, F1 = A1, and Fa = f . This gives us the required 1–1 mappingαA : HT (A)→M(A). The naturality of α is easily checked.
4.6 4.1.32, p.93
Suppose F : A → B and G : B → A. By definition, F is left-adjoint toG iff for every A ∈ A and B ∈ B, we have a 1–1 correspondence betweenB(FA,B) and A(A,GB) (denoted by in both directions) satisfying
qg = (Gq)g, (g : FA→ B, q : B → B′)
fp = f(Fp), (f : A→ GB, p : A′ → A)
(see pp.41–42, eqs.(4.2.1)–(4.2.3)).
By definition, the functors B(F (−),−) and A(−, G(−)) are naturally iso-morphic iff for every A ∈ A and B ∈ B, we have a 1–1 correspondenceαAB : B(FA,B) → A(A,GB) satisfying certain naturality requirements.By Exercise 1.3.29 (p.39), these requirements are equivalent to two commu-

4 REPRESENTABLES 71
tative diagrams (with p and q as above):
B(FA,B) B(FA,B′)
A(A,GB) A(A,GB′)
q◦−
αAB αAB′
Gq◦−
B(FA,B) B(FA′, B)
A(A,GB) A(A′, GB)
−◦Fp
αAB αA′B
−◦p
Let’s say we write αAB(f) = f for f : A→ GB, α−1AB(g) = g for g : FA→ B.
The diagrams become:
g qg
g (Gq)g = qg
q◦−
Gq◦−
f f(Fp) = fp
f fp
−◦Fp
−◦p
exactly the same as the naturality equations for adjoints.
4.7 4.2.2, p.99
The cornerstone of the Yoneda lemma is the diagram on p.97, for f : B → A:
A(A,A) A(B,A)
XA XB
HA(f)=−◦f
αA αB
Xf

4 REPRESENTABLES 72
evaluated at 1A ∈ A(A,A):
1A f
αA(1A)αB(f) =
Xf(αA(1A))
HA(f)
αAαB
Xf
giving eq.(4.5): Xf(αA(1A)) = αB(f). This tells us that the natural trans-foration α is determined completely by the value of αA at 1A.
Reversing the arrows, we get almost the exact same diagrams. Only changes:f : A→ B instead of f : B → A; HA(f) instead of HA(f); A(A,B) insteadof A(B,A). So we have
[A,Set](HA, X) ∼= X(A)
instead of[Aop,Set](HA, X) ∼= X(A)
4.8 4.2.3, p.99
Let’s writeM for the “categorified” M , i.e.,M has a unique object ∗, andthe morphisms ∗ → ∗ of M are the elements of M .
(a) H∗(∗) is the set of all morphisms ∗ → ∗, i.e., the set of all elementsof M . If m is a morphism, then H∗(m) maps morphisms to morphisms bypre-composition: x 7→ xm. But that’s exactly the definition of M .
(b) Let X be the functor corresponding to the right M -set X. So X(∗) = X,and Xm : X → X is defined by x 7→ x ·m. Now let x be a fixed element ofX, and define αx : M → X by
αxp = x · p for all p ∈M

4 REPRESENTABLES 73
We have αx1 = x·1 = x, as required. An M -set map (i.e., a right equivariantmap) must satisfy
(αxp) ·m = αx(p ·m) for all m, p ∈M
But this just says that
(x · p) ·m = x · (p ·m) for all m, p ∈M
and since p ·m = pm by definition of M , this becomes (x · p) ·m = x · pm,the definition of a right equivariant action. (If you want to get persnickety,in p ·m, we regard p as an element of M and m as an element of M ; in pm,both p and m are elements of M .)
To show αx is uniquely determined by x, suppose α : M → X is a rightequivariant map, and let x = α1. Then for any p ∈ M , equivariance saysthat
αp = α(1 · p) = (α1) · p = x · p
so α = αx.
(c) The Yoneda lemma says that X(∗) ∼= [Mop,Set](H∗, X). On the lefthand side we have all the elements of X (i.e., the underlying set of X),and on the right hand side we have all the α : H∗ ⇒ X. As we saw in(a), H∗ is essentially the same as M , and the α’s are basically just rightequivariant maps from M to X. In (b) we saw that the two sides are in 1–1correspondence. The correspondence is natural in X because if h : X → X ′
is a right equivariant map, then hα : M → X ′ is also a right equivariantmap, with corresponding element (hα)1 = h(α1). So the Yoneda lemma isproven for this case.
(d) Although the exercise didn’t ask for it, let’s look at the Yoneda em-bedding. For any x ∈ M , we have a corresponding αx : M → M definedby
αxp = x · p for all p ∈M

4 REPRESENTABLES 74
Now let’s compose the natural transformation αx and αy for x, y ∈ M ,remembering that a · b = ab for all a, b ∈ M , i.e., the right M -action is thesame as monoid multiplication.
αx(αy(p)) = αx(yp) = x(yp) = (xy)p = αxyp
So αxαy = αxy. Note that x 7→ αx is just the Yoneda mapping H•; we’vejust shown that it preserves the category structure.
(e) Finally we look at the “universal element” corollary, 4.3.2 (p.99). Say uis a universal element, i.e., u ∈ X(∗) = X satisfying (4.6) (p.99):
(∀B ∈M)(∀x ∈ XB)(∃! x :B → A)(Xx)u = x
Since ∗ is the only object of M and the morphisms ∗ → ∗ are just theelements of M , this becomes:
(∀x ∈ X)(∃! m ∈M)(Xm)u = x
But X just sends m ∈M to the right action of m on X, so
(∀x ∈ X)(∃! m ∈M)u ·m = x
This says that the map m 7→ u·m is a bijection from M to X. But that mapis αu. So: if α : M ⇒ X is a representation of M , then we know from (b)that α = αu for some u ∈ X, and αu must be a bijection by the definitionof representation. Thus the universal element property (4.6) holds. In theother direction, if there is a u satisfying (4.6), then αu is a bijection, andwe already know it’s an equivariant map, so it’s a representation.
4.9 4.3.15, p.106
This is entirely straightforward. Being a bit sloppy, if f is an isomorphismin A, then for some h, fh = hf = 1 so J(f)J(h) = J(h)J(f) = 1. (Really

4 REPRESENTABLES 75
we should be fussier about the four different identities in those equations,but you get the idea.) If g is an isomorphism in B, then for some k, gk =kg = 1; since J is full, g and k have preimages in A, call them f and h, soJ(fh) = gk = 1 and J(hf) = kg = 1; but since J is faithful, it follows thatfh = hf = 1. Finally, (c) is an immediate consequence of (a) and (b).
4.10 4.3.16, p.106
(a) Suppose f, g : A→ A′ with f 6= g; we have to show that H•(f) 6= H•(g).Now H•(f) = Hf , and Hf is the natural transformation that for any B mapsHA(B)→ HA′(B) via Hf : p 7→ fp; likewise for H•(g). Letting B = A andp = 1A, we have Hf (1A) = f 6= g = Hg(1A). So H•(f) 6= H•(g).
(b) If α : HA ⇒ HA′ , we have to show that α = H•(f) for some f : A→ A′.Basically we copy part of the proof of the Yoneda lemma. Set f = αA(1A),so f : A → A′. For any g ∈ HA(B), we have to show that αB(g) =(Hf )B(g) = fg. This follows from the diagrams
HA(A) HA(B)
HA′(A) HA′(B)
HA(g)
αA αB
HA′ (g)
1A g
f fg = αB(g)
HA(g)
αA αB
HA′ (g)
(c) Assuming the existence of a universal element u ∈ XA, we have to showthat HA
∼= X, i.e., that there is a natural transformation α : HA ⇒ Xwhere αB : HA(B) → XB is bijective for every B ∈ A. We define thenatural transformation u by:
uB : HA(B)→ XB, uB : f 7→ Xf(u)
For any B ∈ A, the universal element property (4.6, p.99) says
(∀x ∈ XB)(∃! f :B → A)Xf(u) = x

4 REPRESENTABLES 76
or using Xf(u) = uB(f),
(∀x ∈ XB)(∃! f :B → A)uB(f) = x
This says that the map uB : HA(B) → XB is bijective, so we can takeα = u.
4.11 4.3.17, p.106
Let D be a discrete category. Note that for D, contravariant and covariantmeans the same thing! Say X : D → Set is a functor; then X simplyassigns a set XA to each A ∈ D.
Next, let A ∈ D and look at HA = HA: this is defined by
HA(B) = HA(B) =
{{1A} if A = B
∅ if A 6= B
We might almost say that HA is the characteristic function of A. Since allsingletons are isomorphic in Set, we could pick some fixed singleton 1 touse for all A ∈ D; then if χA(A) = 1 and χA(B) = ∅ for all B 6= A, we haveHA∼= χA. I won’t use the χ notation below, but it helps to “forget” that
HA(A) = {1A}—all that matters is that HA(A) is a singleton, for which I’llwrite 1.
Next look at natural transformations α : HA ⇒ X. For all B 6= A, αB mustbe the empty function to XB, so we can put those out of our minds. Asfor αA : 1 → XA, this just amounts to an element of XA. So the Yonedalemma is nearly trivial.
Now we look at the family {HA|A ∈ D}. If A 6= B, then we cannot have anatural transformation α : HA ⇒ HB, since αA would be a function 1→ ∅.On the other hand, there is obviously exactly one natural transformation

4 REPRESENTABLES 77
from HA to itself. So {HA|A ∈ D} is a discrete subcategory of Set, equiv-alent to D. In other words, the map H• is an embedding.
Finally we look at the universal element corollary, 4.3.2 (p.99). We alreadyknow what α : HA ⇒ X looks like. For this to be a representation, α mustbe an equivalence, i.e., XA must be a singleton, and all XB with B 6= Amust be empty. Consider condition (4.6) (p.99) on the universal element u:
(∀B ∈ A)(∀x ∈ XB)(∃! x :B → A)(Xx)u = x
For B 6= A, there can be no x : B → A, so XB must be empty (and makingXB = ∅ satisfies the condition for B). For B = A, the only x : A → A is1A, and X1A = 1XA, so we get:
(∀x ∈ XA)u = x
i.e., XA must be a singleton.
4.12 Function Presheaves; Poset Categories
For some reason, Leinster omits one important special case from his Yonedaexamples: the presheaf of continuous functions on a topological space T .It doesn’t really matter what the target space is; to be concrete, let’s sayreal-valued functions. Let O be the category of open subsets of X, with amorphism iUV for every pair of open sets U ⊆ V . It’s helpful to think ofiUV as the inclusion map. The contravariant functor X is defined by
XU = continuous functions on U
XiUV = restriction from V to U
Observe that restriction is actually composition with the inclusion map:f |U = fiUV .

4 REPRESENTABLES 78
The topology and continuity don’t actually play a role: it’s enough if wehave a family O of subsets of a set T , and for any U ∈ O a family XU offunctions with domain U , such that restrictions work right: i.e., if U ⊆ Vand U, V ∈ O and f ∈ XV , then f |U ∈ XU . We then turn O into acategory by introducing the inclusion maps as morphisms, and make Xinto a contravariant functor as before.
Next generalization: assume only that O is a poset, so that there is at mostone morphism iUV : U → V for any two objects U and V ; we define U ⊆ Vto mean that iUV exists. (Usually, we use ≤ instead of ⊆ for this relation.But I will stick with ⊆, and continue to refer to XiUV as a “restrictionmap”, for evocativeness.) Since O is a poset, U ⊆ V and V ⊆ U imply thatU = V , i.e., O is a skeletal category.
We now recognize that discrete categories (Ex.4.3.17, §4.11) constitute aspecial case of this. Also, monoids (Ex.4.2.3, §4.8) represent, so to speak,the obverse: there we have one object with many morphisms, instead ofmany objects with at most one morphism between each pair of objects.
We start with HA and HA. As in the discrete category case, we will replaceall singletons in Set with a fixed one, denoted 1. So:
HA(U) =
{1 if U ⊆ A
∅ otherwise
HA(U) =
{1 if A ⊆ U
∅ otherwise
Next we look at natural transformations α : HA ⇒ X. Empty functions∅ → XU pose no problems, so we confine our attention to 1 → XU forU ⊆ A. We see that α amounts to chosing an element αU1 ∈ XU for everyU ⊆ A. Naturality demands, for U ⊆ A,
XiUA(αA1) = αU1

4 REPRESENTABLES 79
in other words, the chosen element αU1 is the “restriction” of αA1 to U . Soto determine α, we pick an element of XA and then all other αU fall outfrom that. That proves the Yoneda lemma.
It’s a similar story for natural transformations α : HA ⇒ X. But this timeX is a covariant functor, so if A ⊆ U , then XiAU must “extend” elementsof XA to elements of XU . See the footnote4 for an illustration. For therest of this problem, I’ll look only at the contravariant case.
Next, the Yoneda embedding. When do we have a natural transformationHA ⇒ HB? Precisely when HB(A) 6= ∅, since as we’ve just seen, HA ⇒ Xamounts to an element of XA. So HA ⇒ HB exists when and only whenA ⊆ B, in which case the natural transformation is unique.
Finally, the universal element corollary (4.3.2, p.99). For α : HA ⇒ X tobe a representation, XU must be a singleton for all U ⊆ A and XU mustbe empty for all U 6⊆ A. The universal element condition, on u:
(∀U ∈ O)(∀x ∈ XU)(∃! x :U → A)(Xx)u = x
Now, (∃! x :U → A) is equivalent to U ⊆ A. So for U 6⊆ A, XU = ∅. ForU ⊆ A, we have x = iUA so (Xx)u = x becomes x = XiUA(u), i.e., x isthe restriction of u to U . Since this is true for all x ∈ XU , XU must be asingleton.
4Let F0 be the category of fields of characteristic 0, with the morphisms being inclu-sions. Let the functor P take K ∈ F0 to the set of all polynomial functions on K, i.e., allfunctions given by polynomials in K[x]. Characteristic zero insures that the coefficientsof a polynomial are determined uniquely by its associated function. If K ⊆ L, then anypolynomial function on K obviously has a unique extension to L, namely the functionwith the same coefficients. Note that restricting a function in PL won’t always give youa function in PK, since the former maps L→ L, the latter K → K. (Or look at wherethe coefficients lie.)
It’s a little odd to make the morphisms of F0 just inclusions. A field homomorphismis always a monomorphism (in fact injective), so usually we’d allow all imbeddings ofone field into another. But then F0 wouldn’t be a poset, or even a preorder (because ofnon-trivial automorphisms). Otherwise the example is unaffected: we can always extenduniquely, but not always restrict.

4 REPRESENTABLES 80
4.13 4.3.18, p.106
(a) First we unwind what full and faithful means for maps between functorcategories. The objects of [B, C] are functors F : B → C and the morphismsare natural transformations α : F ⇒ G. Let’s write J for J ◦ −, so J :[B, C]→ [B,D].
For any pair of objects F,G in [B, C], we look at all the morphisms α :F ⇒ G and ask if the mapping J : α 7→ J(α) is 1–1 and onto. J(α) isdefined by this rule: for all B ∈ B, the component αB : FB → GB goesto J(αB) : JFB → JGB. Faithfulness follows immediately: if α 6= β, thenαB 6= βB for some B, so J(αB) 6= J(βB) because J is faithful.
Given γ : JF ⇒ JG, is there an α : F ⇒ G with J(α) = γ? Because J isfull and faithful, for every B there is a unique αB with J(αB) = γB. So weuse that to define α. Naturality follows because if one of the squares for αdidn’t commute, we could apply J to it and have a non-commuting squarefor γ. But γ is a natural transformation, so all its squares commute.
(b) Immediate from Lemma 4.3.8 (p.103, §4.9): since J(G) ∼= J(G′) and Jis full and faithful, it follows that G ∼= G′.
(c) The adjunctions F a G and F a G′ imply that
A(A,GB) ∼= B(FA,B) ∼= A(A,G′B)
naturally in A (and in B, but we won’t use that until the end). SinceA(A,GB) = HGB(A) and A(A,G′B) = HG′B(A), we have isomorphismsin Set, say σA : HGB(A) ∼= HG′B(A), and these are natural in A. Inother words, HGB
∼= HG′B in the category of presheaves of A, which is[Aop,Set], or its subcategory H•(A). which is shorter to type. This meansthat GB ∼= G′B for all B ∈ B.
However, G ∼= G′ says a bit more, namely that G and G′ are isomorphicin the functor category [B,A]. So we apply (b) with J = H• (where H• is

5 LIMITS 81
the Yoneda embedding for A, as above). Just to keep track of the variouscategories:
H• : [B,A]→ [B, H•(A)]
So we need to check that H•(G) ∼= H•(G′); if so, (b) implies that G ∼= G′.
Note that H•(G) = H• ◦G, so
H•(G) : B 7→ HGB
likewise for G′, and HGB∼= HG′B for all B, as we’ve just seen. In other
words, for every B ∈ B there is an isomorphism αB in H•(A) between HGB
and HG′B. Now we use the naturality in B of the original adjunctions,which carries through to make αB natural in B. In other words, the αB’smesh together to form a natural equivalence between H•(G) and H•(G
′).
But that means that H•(G) ∼= H•(G′) in the functor category [B, H•(A)].
So G ∼= G′.
5 Limits
5.1 5.1.34, p.124
Both diagrams say that fi = gi. The equalizer condition says that for anys : A → E with fs = gs, there is a unique s : A → E with is = s. Thepullback condition says that for any s1 : A → X and s2 → Y there is aunique s : A→ E with is = s1 and is = s2. So we must have s1 = s2, andthe two diagrams impose the same demands. So the answer is yes: equalizeriff pullback.
Moral: if you “pry apart” a diagram by duplicating a node, it doesn’t changethe diagram’s meaning.

5 LIMITS 82
5.2 5.1.35, p.124
The pullback lemma fits into the diagram below. Rather than label thearrows, I will indicate compositions by listing nodes along the path; forexample, the pullbackness of the left square says that
(∀AC,AE)[ACF = AEF ⇒ (∃!AB)(ABC = AC & ABE = AE)]
For the right square to be a pullback, we must have
(∀AD,AF )[ADG = AFG⇒ (∃!AC)(ACD = AD & ACF = AF )]
and for the whole square,
(∀AD,AE)[ADG = AEFG⇒ (∃!AB)(ABCD = AD & ABE = AE)]
We assume that the part of the diagram with solid arrows commutes, butmake no assumptions up front about the dashed arrows.
A
B C D
E F G
Assume that the left and right square are pullbacks. Pick arbitrary mor-phisms AD, AE such that ADG = AEFG. First use the pullbackness ofthe right hand square. Let AF be A(E)F , the (E) indicating that we’rejust passing through E, all the right hand square cares about are the nodesAF . We have ADG = A(E)FG, again with the right hand square ignoring

5 LIMITS 83
the (E), so (∃AC)[ACD = AD & ACF = A(E)F ]. Since ACF = AEF ,we can use the pullbackness of the left hand square, which tells us that(∃AB)[ABC = AC & ABE = AE]. So ABCD = ACD = AD. We’veshown that the whole square is a pullback, except for the uniqueness re-quirement. Suppose AB is another morphism satisfying ABCD = AD andABE = AE. We set AC = ABC, and have ACD = ABCD = AD,ACF = ABCF = ABEF = A(E)F , i.e., both AC and AC satisfy thecommutation condition on the right hand square. So by the uniquenesscondition for the right hand square, AC = AC. Now we have ABC = ACand ABE = AE, so by the uniqueness for the left hand square, AB = AB.Done.
Now assume that the whole square and the right square are pullbacks. PickAC and AE such that ACF = AEF . Then AEFG = ACFG = ACDG.So A(C)DG = AE(F )G and by the pullbackness of the whole square, thereis an AB such that ABCD = A(C)D and ABE = AE. We need to showthat ABC = AC. By the pullbackness of the right square, there is a uniquesolution AC to the simultaneous equations ACD = AD and ACF = AF ,for any AD and AF . Here we let AD = ACD and AF = AEF . ThenAC = AC and AC = ABC are both solutions (check!), so AC = ABC. Itremains to show that AB is unique. Assume AB satisfies ABC = AC andABE = AE. We use the pullbackness of the whole square, which says thesolution to ABCD = A(C)D and ABE = AE is unique. But the “wholesquare” two equations follow from the “left square” two equations, so weare done.
It’s natural to wonder about the “other” pullback lemma: if the left squareand the whole square are pullbacks, is the right? The answer is no. Przy-bylek [10] gives counterexamples, and conditions under which it does hold.

5 LIMITS 84
5.3 5.1.36, p.125
(a) We define two cones of shape I thus: (Ah−→ L
pI−→ D(I))I∈I and (Ah′−→
LpI−→ D(I))I∈I. Since pIh = pIh
′ for all I ∈ I, these are the same cone, andthe uniqueness requirement on the limit cone says that h = h′.
(b) Suppose h, h′ : A→ D1×D2, and h(a)1 = h′(a)1 and h(a)2 = h′(a)2 forall a ∈ A. Then h = h′, i.e., (h(a)1, h(a)2) = (h′(a)1, h
′(a)2) for all a ∈ A.
5.4 5.1.37, p.125
Let (fI : A → D(I))I∈I be a cone on D with vertex A. So (Du)fI = fJfor any u : I → J . Define the function f : A →
∏D(I) by a 7→ (fI(a))I∈I
for all a ∈ A. In fact, f maps A into lim←D, because for any I
u−→ J ,
(Du)(fI(a)) = fJ(a) for all a ∈ A, and these are the constraints defininglim←D as a subset of
∏D(I). So range restricting f (and still calling it f),
we have the map between vertices. It remains to check that pIf = fI forall I, but this is just pIf(a) = pI((fJ(a))J∈I) = fI(a) for all a ∈ A, which istrue. Oh yes, uniqueness of f : pIf = fI implies that f(a)I = fI(a) for allI, so our choice of f is the only one possible.
5.5 5.1.38, p.125
(a) The proof resembles that given for the special case of Set (§5.4), oncewe bear in mind that the I-component (or u-component) of a morphism is
its composition with prI (or pru). Let (AfI−→ DI)I∈I be a cone on D with
vertex A. We need to produce a unique g : A→ L with fI = pIg for all I.

5 LIMITS 85
Here is the key diagram:
A L
DI DJ DK∏I∈IDI
∏u:J→K
DK
g
ffI
fJ fKp
Du
s t
The existence and uniqueness of f comes from the definition of the product∏DI. We have:
(prI)f = fI Π DI is a product
(Du)fJ = fK (AfI−→ DI)I∈I is a cone
(pru)s = (Du)prJ definition of s
(pru)t = prK definition of t
Now, if sf = tf , then by the definition of equalizer, we will have a uniqueg : A→ L with pg = f . Because
∏u:J→K DK is a product, sf = tf follows
from (pru)sf = (pru)tf for all u. We compute:
(pru)sf = (Du)prJf
= (Du)fJ = fK
(pru)tf = prKf = fK
So we have a g with pg = f . Two computations seal the deal. First,pIg = prIpg = prIf = fI , as required. Next, suppose pIg = pIg
′, i.e.,prIpg = prIpg
′, for all I. Since∏DI is a product, pg = pg′. Since p :
L→∏DI is an equalizer, g = g′. We have shown there is a unique g with
pIg = fI for all I, so L is a limit.

5 LIMITS 86
(b) This follows from (a) and the fact that binary products plus a terminalobject imply all finite products. The empty product is a terminal object(see Example 5.1.9, pp.111–112); the product of one object X is obviouslyjust X; X× (Y ×Z) satisfies the universal property to be the triple productX × Y × Z (easy exercise); the cases n > 3 follow by induction.
Smith [11, Ch. 11] gives a lucid and thorough treatment of these results.
5.6 5.1.39, p.125
This exercise follows from §5.5(b) once we show that pullbacks plus a termi-nal objects implies binary products and equalizers. First recall the remark(p.115) in the definition of pullbacks (Def.5.1.16): when the southeast cor-ner of a pullback square is a terminal object, the pullback is just a binaryproduct. Exercise 5.1.34 (§5.1) shows that all equalizers are pullbacks.
5.7 5.1.40, p.125
First we remark on the fullness of Monic(A) as a subcategory of A/A. This
simply says that given Xm−→ A, X ′
m′−→ A with m and m′ monic, we includeall morphisms X → fX ′ of A making the triangle commute: m′f = m.But if m′f is monic, then f has to be monic, by item 6 of §1.11 (a moniccomposition has a monic on the right).
(a) If m′f = m, then m(X) = m′(f(X)) ⊆ m′(X ′), so if m ∼= m′ it followsthat the images are equal. Conversely, if the images are equal then we cantreat m and m′ as though they were bijections onto the same set, sincemonics in Set are injective. So we have a bijection between X and X ′
making the triangle commute.
(b) Subobjects in Group are, essentially, subgroups: if m : H → G is monic

5 LIMITS 87
then m is a monomorphism and we might as well treat H as being m(H)—it’s isomorphic to it, and m(H) is a subgroup of G. The same argumentworks for Ring and Vectk
(c) Subobjects in Top of a space X are subsets of X equipped with atopology that is finer than the subspace topology. That is (letting U be theforgetful functor), every subobject of X has a unique representative of theform i : A→ X, where Ui is the inclusion map UA ↪→ UX, and if A is thetopology of A and S is the induced subspace topology on UA, then A ⊇ S.For the proof, see §1.12.
For a regular monic, the topology of A will be the subspace topology. Seethe remark in §5.13.
5.8 5.1.41, p.126
The pullback condition says that
(∀x, y : A→ X)[fx = fy ⇒ (∃!u)(1u = x&1u = y)]
which is clearly equivalent to saying that f is monic.
5.9 5.1.42, p.126
Given x, y : Y → X ′ with m′x = m′y, we want to show that x = y. Sincethe pullback square commutes, we have
mf ′x = fm′x = fm′y = mf ′y

5 LIMITS 88
and since m is monic, f ′x = f ′y. So we have this commuting diagram:
Y
X ′ X
A′ A
x
y
f ′x=f ′y
m′x=m′y
f ′
m′ m
f
Now if we temporarily omit the x and y arrows from the diagram, thepullback condition assures us of an unique morphism Y → X ′ making thediagram commute. Since x and y can both play that role, we have x = y.
5.10 5.2.21, p.135
Suppose f is an equalizer of s and t, and suppose g : X → A has fg = 1X ,gf = 1A. So we have
A X Yf s
tg
Since sf = tf , multiply on the right by g and get sfg = s1X = s, tfg =t1X = t, so s = t.
On the other hand, suppose that s = t and f : A → X is an equalizer.Since s1X = t1X , the definition of equalizer says that 1X can be factoredthrough f , i.e., there is a g : X → A with fg = 1X . We must show alsothat gf = 1A. Now, since sf = tf , we have sfgf = tfgf , and so fgfcan be uniquely factored through f , i.e., there is a unique h : A → A withfh = fgf . Obviously h = gf fills the bill. But since fgf = 1Xf = f , theequation fh = fgf is the same as fh = f and h = 1A also fills the bill. Byuniqueness, gf = 1A.

5 LIMITS 89
The statement about coequalizers is proved by dualizing the argument justgiven.
5.11 5.2.22, p.135
(a) Define x ≡ y by (∃n ∈ N)[fn(x) = y or fn(y) = x]. Another equivalentdescription: treat X as a graph, where we draw an undirected edge from xto f(x) for every x ∈ X. Then the equivalence classes are the connectedcomponents of the graph. Finally, the coequalizer is the function taking xto its equivalence class.
(b) The coequalizer in Top has the same definition, but now we have togive the quotient set X/≡ a topology. We use the quotient topology, thefinest (largest) topology making the coequalizer continuous. In detail, letY = X/≡ and let e : X → Y be the coequalizer. Then V ⊆ Y is openiff e−1(V ) is open in X. Because unions and intersections behave so nicelyunder inverse functions, this gives a topology.
Let X = {z ∈ C : |z| = 1}, the unit circle. Define f to be a rotationthrough an angle θ, so f(eit) = ei(t+θ). It is known that the orbit of f ,{fn(z)|n ∈ Z}, is dense in X for any z if θ is not a rational multiple of 2π(or in degree measure, is an irrational number). So assume that about θ.
Let e : X → X/≡ be the coequalizer, and let Y = (X/≡). Since each orbitis countable, Y is uncountable. Now let y ∈ V ⊆ Y with V open in Y . Toshow that Y is indiscrete, we have to show that V = Y . Let e(x) = y, sox ∈ e−1(V ). Since V is open, e−1(V ) is open in X, so for some ε > 0, allpoints of X within arc distance ε of x also belong to e−1(V ). But then thisis also true for any other x′ in e−1(y), for we get x′ by rotating x through amultiple of θ, and such a rotation preserves orbits (= equivalence classes):e(fn(z)) = e(z) for all z ∈ X and all n ∈ Z. (Also rotations preservedistances.) Since orbits are dense in X, there is an x′ ∈ e−1(y) within ε ofany arbitrarily chosen element of X, and so every element of X belongs to

5 LIMITS 90
e−1(V ). In other words, e−1(V ) = X and V = Y .
As for the cited fact about density, even more is true: the multiples ofan irrational angle are distributed uniformly around the unit circle. Weylgave a proof using Fourier analysis; there’s also a proof using continuedfractions. (See Niven [9, §§6.3–6.4] for both proofs.) The density followsfrom a simple pigeonhole argument. Let the positive integer k be as largeas you like, and divide the circle into k equal arcs. So there exists m andn, m 6= n, both integers, such that the points at mθ and nθ lie in the samearc. So if you rotate the circle through an angle of −nθ, the point at mθends up within (arc distance) 1/k of the point at 0◦. But this rotated pointisn’t at 0◦ because θ is irrational in degree measure, and so we cannot have(m − n)θ = l · 360◦ for any l ∈ Z. So there are points in the orbit of θ asclose, but not equal, to the point at 0◦ as you like. With another integermultiplication you can put such a point as close to any point on the circleas you like.
§1.12 discusses monics in Top in general.
5.12 5.2.23, p.135
(a) Let i : (N,+) ↪→ (Z,+) be the inclusion, and suppose f, g : Z→M aremonoid morphisms such that fi = gi. In other words, f |N = g|N.
Now consider f(−x) for x ∈ N: f(−x) + f(x) = f(0) = 0, and likewiseg(x) + g(−x) = g(0) = 0. Since f(x) = g(x), writing c for the commonvalue we have
f(−x) + c = 0 = c+ g(−x)
so
f(−x) = f(−x) + 0 = f(−x) + c+ g(−x) = 0 + g(−x) = g(−x)
i.e., f ≡ g over all of Z.

5 LIMITS 91
(The last displayed equation is the usual proof that when an inverse existsin a monoid, it’s unique. Note that we can’t just cavalierly cancel c, sincenot all monoids have cancellation.)
(b) Let i : Z ↪→ Q be the inclusion, and suppose f, g : Q → R are ringhomomorphisms such that fi = gi. In other words, f |Z = g|Z.
Now consider f(1/y) for y ∈ Z, y 6= 0. Since f(1/y) · f(y) = f(1) = 1, andlikewise g(y) · g(1/y) = g(1) = 1, we can write
f(1/y) · c = 1 = c · g(1/y)
so
f(1/y) = f(1/y) · 1 = f(1/y) · c · g(1/y) = 1 · g(1/y) = g(1/y)
and sof(x/y) = f(x) · f(1/y) = g(x) · g(1/y) = g(x/y)
for any x, y ∈ N with y 6= 0. So f = g over all of Q.
5.13 5.2.24, p.135
This exercise is the dual of §5.7, sort of. We start by remarking on thefullness of Epic(A) as a subcategory of A/A. This simply says that given
Ae−→ X, A
e′−→ X ′ with e and e′ epic, we include all morphisms X → fX ′
of A making the triangle commute: fe = e′. But if fe is epic, then f hasto be epic, by item 7 of §1.11 (an epic composition has an epic on the left).
(a) The equivalence relations induced by e and e′ are e(x1) = e(x2) ande′(x1) = e′(x2). Suppose we have a morphism f : X → X ′ with fe = e′; thene(x1) = e(x2) ⇒ fe(x1) = fe(e2) ⇒ e′(x1) = e′(x2). On the other hand,suppose e(x1) = e(x2) ⇒ e′(x1) = e′(x2); then we define f : X → X ′ byf(x) = e′(e−1(x)), which is well-defined because the e-inverse image of x is

5 LIMITS 92
sent to a single element of X ′ by e, because e is surjective and e(x1) = e(x2)⇒ e′(x1) = e′(x2). It is clear that with this definition, fe = e′.
It follows that if e(x1) = e(x2) ⇔ e′(x1) = e′(x2), then we have functionsf : X → X ′ and f ′ : X ′ → X with f ′f and ff ′ as solutions to ue = e = 1Xeand u′e′ = e′ = 1X′e
′. Since e and e′ are epic, f ′f and ff ′ are both identities,so e and e′ are isomorphic. Conversely, if e and e′ are isomorphic, then wehave e(x1) = e(x2) ⇔ e′(x1) = e′(x2), so the equivalence relations are thesame.
To cap the argument off, we need to know that for every equivalence relationon A, there is an epic e : A→ X such that e(x1) = e(x2) is that equivalencerelation. We let X be the set of equivalence classes and let e(x) be theequivalence class of x.
(b) The argument given in (a) works without modification up to the finalparagraph (assuming that all epics in Group are surjective; see §1.13 for aproof). It shows that (group) epimorphisms e : A → X ′ and e′ : A → X ′
are isomorphic iff they define the same equivalence relation. However, notevery equivalence relation on A has an associated epimorphism. A equiv-alence relation ≡ is called a congruence when it satisfies the additionalrequirement that x1 ≡ x2 and y1 ≡ y2 imply x1y1 ≡ x2y2. It’s trivial toshow that if e is an epimorphism, then e(x1) = e(x2) defines a congruence;conversely, given a congruence on A, the set of congruence classes forms agroup under the obvious definition of a group operation, with the functione(x) = the congruence class of x being an epimorphism.
We now observe that for an epimorphism e, e(x) = e(y) is equivalent toe(xy−1) = 1, which is (by definition) the same as saying that xy−1 is in thekernel of e. We clinch the argument with the claim that a subgroup of A isa kernel if and only if it’s a normal subgroup. This is standard basic grouptheory (see Lang [5, §1.3] or Bergman [2, §§4.1–4.2]), but is also an easyexercise.

5 LIMITS 93
Leinster remarks, “Arguably, quotient object would be more suitable for anisomorphism class of regular epics. . . ” §1.12, on monics and epics in Top,suggests his meaning. A monic in Top is a continuous injective function,so the subspace topology on the image can be (strictly) smaller than theimage topology (i.e., the one that makes the image homeomorphic to thesource space). An epic in Top is a continuous surjective function, so thequotient topology on the image can be (strictly) larger than the topologyof the target space. With regular monics and epics, this can’t happen. If‘subobject’ should mean “up to isomorphism, a subspace”, and ‘quotient’should mean quotient space in the sense found in most topology textbooks(see Munkres [8, §22], or §1.12), then regular monics and epics serve theseup.
5.14 5.2.25, p.135
See §1.11 for background on monics.
(a) First suppose m is split monic with em = 1A. We let C = B, p = me,and q = 1B, thus:
A B A Bm
1A
e
p=me
q=1B
m
(Warning: the diagram doesn’t commute, but it would if you removed the1B arc; that’s why I’ve made it dashed.) We have pm = mem = m1A = m =1Bm = qm. Now assume f : X → B satisfies pf = qf , so f = 1Bf = mef .So f factors through m via ef , i.e., setting u = ef gives f = mu. We haveto show that u is unique. From f = mu we get ef = emu = 1Au = u, sou = ef is the only possible solution. Thus m is regular monic.
Next, suppose m is regular monic with m : A→ B equalizing p, q : B → C.

5 LIMITS 94
Suppose x, y : X → A with mx = my = f , say. Since pm = qm, we havepmx = qmx, i.e., pf = qf ; likewise pmy = qmy, also giving pf = qf . Sincem is an equalizer, f must factor through m uniquely, i.e., there is a uniqueu : X → A satisfying mu = f . But x = u and y = u both satisfy thisequation, so we must have x = y. Therefore m is monic.
Although Leinster doesn’t ask for it, here are the dual arguments, showingthat split epic ⇒ regular epic ⇒ epic. First split epic ⇒ regular epic.
B A B Aee
p=me
q=1B
m
1A
e
(Same warning: the diagram doesn’t commute, but would if the 1B arc wereremoved, which is why it’s dashed.) We have ep = eme = 1Ae = e = e1B =eq. If f : B → X satisfies fp = fq, i.e., f = f1B = fme, then settingu = fm we have f = ue. To show e is regular epic we need to show finallythat u is unique. But if f = ue, then fm = uem = u1A = u.
Next regular epic ⇒ epic. Suppose e is regular epic with e : B → Ccoequalizing p, q : A → B. Suppose x, y : C → X with xe = ye = f , say.Since ep = eq, we have xep = xeq giving fp = fq; we could have usedy instead of x, giving yep = yeq which also says that fp = fq. Since eis a coequalizer, f must factor through e uniquely, i.e., there is a uniqueu : C → X satisfying ue = f . Since both x = u and y = u satisfy thisequation, we must have x = y. Therefore e is epic.
(b) Suppose f : G → H in Abelian. We prove the implications f monic⇒ (ker f = 0) ⇒ f regular monic. (These are really equivalences becauseregular monic implies monic, as we just saw in (a).)
f monic ⇒ (ker f = 0): set K = ker f , so we have two maps: the zero map0 : K → G sending all of K to 0 ∈ G, and the inclusion map i : K ↪→ G.Now fi = f0, both being the zero map from K to H. If f is monic then we

5 LIMITS 95
can cancel it from fi = f0, so i = 0, i.e., ker f = 0.
(ker f = 0) ⇒ f regular monic: let s : H → H/f(G) be the canonicalepimorphism. Consider
G H H/f(G)f s
0
where 0 is the zero map. We immediately have sf = 0f , and s(x) 6= 0 ifx 6∈ f(G). So if g : L → H has sg = 0g, then g(L) ⊆ ker s = f(G). Ifker f = 0 then f is injective, so f determines an isomorphism between Gand f(G), and so g can be “pulled back along f” to give a map r : L→ G.That is, we have a unique r : L→ G with fr = g. Thus f is an equalizer.
Finally, an example of a regular monic that is not split. The standardexample is the inclusion i : 2Z ↪→ Z. This has kernel 0, so is regular monic.Suppose e : Z → 2Z. For any k ∈ Z, e(k) = k · e(1)—for k > 0, writek as a sum of k 1’s, and for k < 0, we have e(−k) = −e(k) from basicgroup theory. So e(2) = 2 · e(1). Now, if ei is the identity on 2Z, thenwe must have e(2) = ei(2) = 2. But that is inconsistent with the equatione(2) = 2 · e(1): if 2 = e(2) = 2 · e(1), then we cannot have e(1) ∈ 2Z.
(c) As shown in §1.12, the monics in Top are, up to isomorphism, subsetsequipped with spaces that are finer than (larger or equal to) the inducedsubspace topology. The regular monics are, up to isomorphism, just thesubspaces. So any map i : A → X where UA ⊆ UX and the topology ofA is (strictly) larger than the subspace topology serves as an example of anon-regular monic.
5.15 5.2.26, p.136
See §1.11 for background on monics and epics.
(a) By definition, isomorphism ⇒ split epic plus split monic; item 12 of

5 LIMITS 96
A Bf
g
Figure 3: Monic and Epic in Set
§1.11 says that split epic ⇒ regular epic, and item 11 that split monic ⇒monic, so we have the forward implication.
Item 3 shows that split epic plus monic ⇒ isomorphism, so it’s enoughto prove that regular epic plus monic ⇒ split epic. Suppose f : A → Bcoequalizes p, q : X → A. Then fp = fq; since f is monic, p = q. The otherpart of being a coequalizer says that if h : A → Y satisfies hp = hq, thenthere exists a g : B → Y with gf = h. Apply this with h = 1A : A → A;1Ap = 1Aq because as we just saw, p = q. So gf = 1A and f is split epic.
Dualizing all this shows that isomorphism ⇔ split monic plus epic.
(b) In Set, epic and split epic are both equivalent to surjective. This is basicset theory; we start with the implication surjective ⇒ split epic. Ratherthan write out a formal proof, I invite you to look at figure 3.
If f : A → B is surjective, then we have all the → arrows, and for eachb ∈ B, we choose one incoming arrow to reverse. This gives us the ←arrows. (We appeal here to the axiom of choice.) Clearly we have fg = 1B,so f is split epic.
Next, epic ⇒ surjective, which we prove in contrapositive form. If f : A→B is not surjective, then we let p : B → {0, 1} be the characteristic function

5 LIMITS 97
of f(A), and q : B → {0, 1} be the constant function q(b) ≡ 1. Thenpf = qf (constantly 1), but p 6= q (because f is not surjective). So f is notepic.
Since surjective ⇒ split epic ⇒ regular epic ⇒ epic ⇒ surjective, theseare all equivalent. (The middle implications come from dualizing §5.14(a);details below. Note, however, that the implication split epic⇒ epic is nearlytrivial.)
This is a good spot to prove the analogous facts for monics in Set. Wehave split monic ⇒ regular monic ⇒ monic from §5.14(a), so our next stepis monic ⇒ injective. We prove the contrapositive. Suppose g : B → A isnot injective, with g(b) = g(b′). Let p, q : {0} → B be defined by p(0) = b,q(0) = b′. Then gp = gq but p 6= q.
Finally, we’d like to show injective ⇒ split monic, but there is a class ofexceptions: ∅ → A 6= ∅. If B 6= ∅ and g : B → A is injective, thenreferring to our diagram above, we have the ← arrows. Reversing themgives us a partial function f : A → B with fg = 1B. To make f a truefunction, we pick a b0 ∈ B and send all “orphans” (i.e., a ∈ Arg(B))to b0. So g injective with nonempty domain ⇒ split monic. (Picking asingle element from a nonempty set doesn’t require the axiom of choice, butfollows from the basic rules of logic.)
It remains to prove that injective ⇒ regular monic. We just need to dealwith case ∅ → A 6= ∅, showing that such functions are equalizers. Letp, q : A → {0, 1} be the constant functions p(x) ≡ 1, q(x) ≡ 0. Then∅→ A is the equalizer of p and q.
(c) In Group, the simplest example of a non-split epic is f : Z → Zn.(Note: Zn = Z/nZ.) The only homomorphism Zn → Z is the trivial onesending everything to 0, so the equation fi = 1Zn is impossible.
For Top, two examples of non-split regular epics are given in §1.12. First,the covering map of the circle R→ S1, given by x 7→ eix. Second, the same

5 LIMITS 98
MonicRegularMonic
SplitMonic
EpicRegularEpic
SplitEpic
Composition X × X X × XPullbacks X × × × × X
Figure 4: Compositions and Pullbacks
map but restricted to the closed interval [0, 2π].
Worth noting, perhaps: the covering map R→ S1 becomes the group theoryexample upon restricting the domain to 2πZ.
5.16 5.2.27, p.136
The results are summarized in fig.4. First we look at composition, thenpullbacks.
Items (4) and (5) of §1.11 tell us that monics, epics, split monics, and splitepics are all closed under composition.
A composition of regular monics need not be regular. It is regular in Top,Hausdorff, CptHff, and Group, as can be seen from the results in §1.12and §1.13. The following example comes from Adamek et al. [1, §7J]. We saya topological space X is functionally Hausdorff if every pair of distinctpoint can be separated by a real-valued function, i.e., for any a, b ∈ X,a 6= b, there is a continuous f : X → R such that f(a) 6= f(b). FHaus isthe full subcategory of Hausdorff consisting of all functionally Hausdorffspaces and all continuous functions between them.
First we characterize regular monics in FHaus. The argument in §1.12shows that f is a regular monic iff it is a homeomorphism onto a solutionset, i.e., a set of the form S = {x ∈ X|s(x) = t(x)} for some s, t : X → Y .

5 LIMITS 99
A zeroset is f−1(0) for some continuous real-valued f ; we show next thatsolution sets are the same as intersections of zerosets. First suppose S isa solution set for s, t, as above. For each x 6∈ S, we have s(x) 6= t(x)
and so there is an f : Y → R with f(s(x)) 6= f(t(x)), and so g(x)def==
f(s(x)) − f(t(x)) is a real-valued map with g(x) 6= 0. On the other hand,g(S) = 0 (i.e., (∀x ∈ S)g(x) = 0). So if we consider the family of allg : X → R for which g(S) = 0, then S is the intersection of the family ofassociated zerosets.
In the other direction, let S be an intersection of zerosets, say S =⋂α{x ∈
X|fα(x) = 0} for some family {fα : X → R}. Let Y =∏
αR, the productof as many copies of R as there are maps in the family. Define s : X → Yby s(x)α = fα(x), i.e., the α component of s(x) is given by fα(x). Let tbe the constantly 0 map, i.e., t(x)α = 0 for all α. It is clear that S is thesolution set for s and t.
Now we consider X ⊆ Y ⊆ R in FHaus, where X is {1, 12, 1
3, . . .} with the
discrete topology, Y is {1, 12, 1
3, . . . , 0} = X∪{0} with the discrete topology,
and R is R except that we add one new closed set to the standard topologyof R, namely X. Once you add X, you have to add all finite unions of closedsets, in other words all sets of the form F ∪X for F closed in the standardtopology. The family of sets {F |F closed in R} ∪ {F ∪ X|F closed in R}is closed under arbitrary intersections, so it’s the topology of R specifiedvia closed sets. The open sets in R are thus {V |V open in R} ∪ {V rX|V open in R}. Discrete spaces such as X and Y obviously belong toFHaus; likewise, since R is in FHaus and R has a finer topology than R,R is also in FHaus.
We have the set-theoretic inclusion maps X → Y → R (i.e., UX ↪→ UY ↪→UR); we note next that these are inclusion maps in FHaus, i.e., imbeddings.The maps X → Y → R are continuous because X and Y are discrete, andX → Y is obviously a homeomorphism onto its image. Now, Y ⊆ R withthe subspace topology is already “close to” being discrete: the only singletonthat’s not an open set is {0}. We made X closed in R, so Y rX = {0} is

5 LIMITS 100
Figure 5: FHaus example
open in Y ⊆ R with the subspace topology. So X ↪→ Y ↪→ R.
We define X as a zeroset in Y via f(X) = 0, f(0) = 1. So X ↪→ Y isregular monic. It’s easy enough to define Y as a zeroset in R, or even in R:for example, define g : R→ R by g(r) = the distance from r to the closestelement of Y (a piecewise linear function, except at 0). So Y ↪→ R is alsoregular monic.
To finish the example, we demonstrate that X ⊆ R is not an intersectionof zerosets, and so X ↪→ R is not regular monic. This follows from the factthat if h : R → R is continuous, and h(X) = 0, then h(0) = 0. (Looselyspeaking, even though 0 is not in the closure of X in R, it still acts like itis, so far as real-valued functions are concerned. See fig.5.) Proof: supposeon the contrary that h(0) = r 6= 0 but h(X) = 0. Adapting the good oldε-δ definition of continuity to a map from R to R:
(∀ε > 0)(∃U 3 0)(∀x)[x ∈ U ⇒ |h(x)− r| < ε] U open in R
We choose ε < |r|/2. We described the open sets in R above; say U = VrXfor V open in R. This tells us that h(x) is bounded away from 0 for all x“near” 0 but not in X, or more precisely:
(∃δ > 0)(∀x)[|x| < δ&x 6∈ X ⇒ |h(x)| > |r|/2]
But h(x0) = 0 for all x0 ∈ X, and there is certainly an x0 ∈ X with |x0| < δ.Then h cannot be continuous at that x0, since for all x sufficiently near butnot equal to x0, |h(x)| > |r|/2.
As fig.5 suggests, the fact that h(1/n) = 0 for all n > 0 forces |h(x)| to besmall for all x in between 1
nand 1
n+1; the larger n, the smaller |h(x)| for

5 LIMITS 101
1n+1
< x < 1n. So lim |h(x)| = 0 as x → 0, even with x avoiding the points
1/n.
A composition of regular epics need not be regular. It is regular in Top,Hausdorff, CptHff, and Group, as can be seen from the results in §1.12and §1.13. Perhaps surprisingly, regular epics are also closed under compo-sition in FHaus. The arguments in §1.12 for Hausdorff adapt virtuallywithout change5 to show that the regular epics in FHaus are preciselythe quotient maps. Quotient maps are closed under composition; this is aone-line proof.
FHausop comes to the rescue, exhibiting regular epics whose composition isnot regular. Proof: regular epics in FHausop are regular monics in FHausand vice versa. Because this may seem like cheating, here is an examplefrom Adamek et al. [1, §7S, p.131], in Cat. (I don’t know of a topological
example.) We have three categories A A−→ B B−→ C with morphisms (i.e.,functors) A and B; A and B are regular epic but BA is not.
The categories:
1. A is 0a−→ 1, i.e., two objects with one morphism between them. (Also
the identity morphisms, of course.)
2. B is (N,+) as a category. So there is one object, call it ∗, and mor-phisms {bn|n ∈ N} with bibj = bi+j. Note that b0 = 1∗.
3. C is ({0, 1}, ·) as a category. So there is one object, call it ◦, andmorphisms c0, c1 with cicj = ci·j. Note that c1 = 1◦.
5The “abstract” proof that ij = 1Y still works, although the “dense image” one nolonger does.

5 LIMITS 102
The functors A and B are defined by:
A10 = A11 = b0 = 1∗
Aa = b1
Bb0 = c1 = 1◦
Bbn = c0 for n > 0
Proof that A is regular epic: let 1 be the category with one object (call it †)and just the identity morphism. Then A is the coequalizer of P,Q : 1→ Awhere P † = 0 and Q† = 1. Checking this is routine, but amounts to notingthat if K : A → D satisfies KP = KQ, then K0 = K1, and Ka is somemorphism from K0 to K1. The functor A imposes no “conditions” onAa—nothing like, say, (Aa)(Aa) = 1∗—so if we define a functor B → D bybn 7→ (Ka)n, everything is copacetic6.
Proof that B is regular epic: let A′ : A → B be defined by A′a = b2.Trivially we have BA = BA′. Suppose L : B → E satisfies LA = LA′. SoLb1 = Lb2 = `, say. Now b1b1 = b2, so `` = (Lb1)(Lb1) = Lb2 = `, so byinduction `n = ` for all n > 0. This observation makes it easy to see thatB coequalizes A and A′.
Proof that BA is not regular: suppose BA coequalizes S, T : Z → A. SoBAS = BAT , and if F : A → F satisfies FS = FT , then we have a uniquesolution X to XBA = F . Suppose first that for every object z ∈ Z, we
have Sz = Tz. This forces S = T , because if f is the morphism z1f−→ z2 in
Z, then there is only one possible choice for Sf and Tf , namely either a orone of the identities 10 or 11. So if F : A → A is the identity functor, thenFS = FT . But the equation XBA = F is impossible because BA sends 0and 1 to the same object ◦, while F keeps them distinct. (This also worksfor Z the empty category, where S = T = the empty functor.)
Next, suppose that Sz 6= Tz for some z ∈ Z. We let F = A (and soF = B). For all objects z ∈ Z, it’s obvious that ASz = ATz. For a
6fine, hunky-dory, A-OK, etc.

5 LIMITS 103
morphism z1f−→ z2, there are two possible cases for BASf (and it’s the
same story for BATf):{Sz1 = 0 &Sz2 = 1⇒ Sf = a⇒ ASf = b1 ⇒ BASf = c0
Sz1 = Sz2 ⇒ Sf = (10 or 11)⇒ ASf = b0 ⇒ BASf = c1
So if BASf = BATf , then ASf = ATf . But BAS = BAT by hypothesis,so AS = AT . Thus we must have X with XBA = A. Applying this tothe morphism a in A, b1 = Xc0. However, this leads to the contradictionb2 = b1b1 = (Xc0)(Xc0) = X(c0c0) = Xc0 = b1, not true in B. ThereforeBA does not coequalize S and T .
Side comment: Adamek et al. [1, §7.40(6), p.112] remark that the functor Ais a non-surjective epic in Cat. Now there are two forgetful functors Cat→Set, namely Ob, the set of objects, and Mor, the set of morphisms. Ob(A)is surjective, as it has to be: Ob has a right adjoint (§3.4, Exercise 3.2.16,p.78), and functors with right adjoints preserve epics (item 10 of §1.11).But Mor(A) is clearly not surjective.
Next, pullbacks. §5.8 (Exercise 5.1.41) proves that monics are pullbackstable. Split monics are not: Example 5.1.17(b) (p.117) demonstrates thatthe pullback of inclusions X, Y ↪→ Z in Set is the intersection X ∩ Y ↪→X, Y . If X and Y are nonempty but disjoint, then the pullback of Y ↪→ Zalong X ↪→ Z is not split, being ∅ ↪→ X, and the only non-split monics inSet are empty functions to a nonempty set.
Example 5.1.17(b) also holds true for Hausdorff, as is readily checked. Weknow from §1.12 that epics in Hausdorff are maps with dense images. Sothis diagram shows an epic that is not pullback stable:
∅ Q
RrQ R

5 LIMITS 104
For a regular monic whose pullback is not regular, we resort to a techniqueuseful for many counterexamples: a custom-built category. First we expressthe essence of the problem in a diagram:
• •
• • •
a
b d
c
f
g
To make this into a category, we must have, at a minimum, five identitiesplus the following additional morphisms:
da, cb, fc, gc, fd, gd, fcb, gcb, fda, gda
In other words, a morphism for every possible path. However, this set of 21morphisms suffice. They don’t have to all be distinct: we can declare, forexample, that fc = gc, even though f 6= g. Certain equalities imply otherequalities; e.g., fc = gc implies fcb = gcb. But we have great freedom indeciding which equalities should hold.
We declare the following equalities:
da = cb, fc = gc, fcb = gcb
but otherwise none should hold except for the trivial ones involving theidentities. It is readily checked that in this category, c is an equalizer, a isa pullback of c, and a is not an equalizer7. So the pullback of the regularmonic c is not regular.
7Caveats: we have to consider possible solutions of xa = ya for all pairs x, y. It’s notenough to note that only one arrow leads out of the target of a; x = fd and y = gd alsocount. So do pairs like x = y = d. Now, if D is the source of d, then 1D is an equalizerof the d = d pair. But if a were a unique isomorphism, it would also be an equalizer ofd = d. Since a isn’t an isomorphism, we’re good.

5 LIMITS 105
In a similar fashion, the diagram
• •
• • •
a
b df
g c
provides the foundation of a category in which c is a coequalizer but itspullback a isn’t. We declare da = cb and cf = cg, but no other nontrivialequalities hold.
Surprisingly, split epics are pullback stable. Suppose t in this pullbacksquare is split epic, with tu = 1Z :
A Y
X Z
g
f t
s
u
(Possibly ut 6= 1Y , but otherwise the diagram commutes.) We need to finda right inverse for f . Now tus = s = s1X , so since our square is a pullback,there must exist a unique v making the left and top sides of this diagramcommute:
X
A Y
X Z
v
us
1X
g
f t
s
u
So fv = 1X and we are done.

5 LIMITS 106
5.17 5.3.8, p.140
Suppose that binary products X1 × Y1 and X2 × Y2 have been chosen forthe pairs (X1, Y1) and (X2, Y2), and suppose we have a morphism (f, g) :(X1, Y1)→ (X2, Y2) in the category A×A. We need to define a morphismf × g from X1 × Y1 to X2 × Y2. Consider this diagram:
X1 × Y1 X2 × Y2
Y1 Y2
X1 X2
f×g
py1px1
py2
g
f
px2
(I’m using px1, etc., instead of Leinster’s pX1,Y11 , etc.) We have morphisms
from X1 × Y1 to X2 and Y2 obtained by going “down and across”, namelyfpx1 and gpy1. Since X2×Y2 is a product, there is a unique morphism f×gmaking the diagram commute.
To show that (f, g) 7→ f × g is functorial, chase this diagram:
X1 × Y1 X2 × Y2 X3 × Y3
Y1 Y2 Y3
X1 X2 X3
f×g
py1px1
f ′×g′
py2 py3
g g′
f f ′
px2 px3
Hence (f ′ × g′)(f × g) = (f ′f)× (g′g).

5 LIMITS 107
5.18 5.3.9, p.140
Given a morphism f : A → X × Y , define the pair (fx, fy) in A(A,X) ×A(A, Y ) by the compositions fx = pxf , fy = pyf , where px and py are theprojections. In the reverse direction, given (fx, fy) ∈ A(A,X) × A(A, Y ),by the definition of product there is a unique f : A→ X×Y with fx = pxfand fy = pyf . So we have the posited 1–1 correspondence.
A good way to think of this correspondence is as a special case of the firstdiagram in §5.17, with the diagonal morphism prepended. (This is theunique morphism δ : A→ A× A such that p1δ = p2δ = 1A, with p1 and p2
being the two projections from A× A to A.) Thus:
A A× A X × Y
A Y
A X
δ fx×fy
p2p1
py
fy
fx
px
Since fxp1δ = fx and fyp2δ = fy, the map (fx, fy) 7→ f is just (fx, fy) 7→(fx × fy)δ. The naturality in X and Y then falls out from the functorialityof (fx, fy) 7→ fx × fy.
The naturality in A follows from the naturality of the diagonal map A 7→ δA,namely the commutativity of this diagram for any h : A′ → A:
A′ A
A′ × A′ A× A
h
δA′ δA
h×h
We check this by composing with the projections p1, p2 : A × A → A. Wehave p1δAh = 1Ah = h and p1(h × h)δA′ = hp′1δA′ = h1A′ = h, likewise for

5 LIMITS 108
composing with p2, so the diagram commutes. We then have this version ofthe second diagram from §5.17:
A′ A
A′ × A′ A× A X × Y
A′ A Y
A′ A X
δA′
h
δA
h×h
p′2p′1
fx×fy
p2 py
h fy
h fx
p1 px
What’s the point of the diagram? Well, if we start with the pair (fx, fy),this is mapped to (fx × fy)δA. Likewise, (fxh, fyh) 7→ (fxh× fyh)δA′ . Butfrom the diagram, we have this relation between the two values:
(fxh× fyh)δA′ = (fx × fy)(h× h)δA′ = (fx × fy)δAh
and this is exactly what naturality in A means.
5.19 5.3.10, p.140
Suppose F : A → B creates limits of shape I and suppose D : I → A is adiagram.
Using Def.5.3.5 (p.139) of “create limits”, the first bullet says that for anylimit cone M in B on FD, there is a unique cone L on D in A with FL =M—limit cones in B “lift uniquely” to cones in A. The second bullet saysthat the lifted cone is a limit cone. So if we have a cone L on D producinga limit cone FL on FD, then the unique lifted cone is L, which must be alimit cone.

5 LIMITS 109
The “more healthy and inclusive” notion of “creates limits”, given by Lein-ster at the top of p.140, has two clauses; the second says that for every coneL on D, if FL is limit cone then L a limit cone (“every such cone is itselfa limit cone”). This is precisely the meaning of “reflects limits” for coneson D. We can rephrase the “healthy” notion this way: F creates limits ofshape I iff F reflects limits of shape I, and if there exists a limit cone onFD then there is one that lifts to a cone on D (which then must be a limitcone).
Some useful and common terminology for a functor F : A → B: if D is adiagram in A and M is a cone on FD, then M lifts to a cone L on D iffFL = M . F lifts limits of shape I iff every limit cone on a diagram FDof shape I can be lifted to a limit cone. F lifts limits uniquely of shapeI if in addition these lifts are unique, i.e., if L and L′ are limit cones liftingM , then L = L′. F lifts limits iff it lifts limits of all shapes; likewise forlifts limits uniquely.
(We don’t talk about lifting arbitrary cones in B: if any one of the objects ormorphisms of the cone wasn’t the image of an object or morphism ofA, we’dbe dead in the water. Also note that the uniqueness in lifts limits uniquelyderives from two pieces of information: first that FL = FL′, second thatL and L′ are both limit cones. In Def.5.3.5, the uniqueness flows just fromFL = FL′, plus FL being a limit cone.)
We will see in §5.20 that the forgetful functor Top → Set lifts limitsuniquely, but does not reflect limits (and hence doesn’t create them). Alsosee §5.21.

5 LIMITS 110
5.20 5.3.11, p.140
(a) The formula of Example 5.1.22 (eq.5.16, p.121) is (with a slight changeof notation)
lim←D = {(xi)i∈I|xi ∈ Di & u(xi) = xj (u : i→ j)}
(where of course i and u range over all objects and morphisms in I respec-tively, and I’ve written Di for D(i) and u for D(u)).
So it’s the subset of the direct product∏
iDi defined by the equations
u(xi) = xj ∀u : i→ j (1)
Now suppose that D is a diagram in Group, so each Di is a group and eachu a homomorphism. We can still form the direct product
∏iDi, defining
the operations pointwise, and look at the subset defined by eq.1. We needto check that this subset is a subgroup, that each of the projections arehomomorphisms, and that this subgroup limD has the required universalproperty.
For the first check, just note that the u’s are homomorphisms. The second
check is trivial. For the third, suppose Hhi−→ Di is a set of homomorphisms
satisfyingu(hi(y)) = hj(y) ∀i u−→ j, ∀y ∈ H (2)
Thenh : y 7→ (hi(y))i∈I
is a homomorphism from H into the direct product∏
iDi; since eq.2 implieseq.1, it maps into the subgroup limD. If we build the usual commutativediagram out of h, the hi’s, and the projections limD → Di, then it’s trivialto check that diagram does commute, and moreover specifies the homomor-phism H → limD uniquely. So limD is indeed a limit.
The first bullet of Def.5.3.5 (p.139) decrees that this limD is the only wayto lift the limit cone in Set to a cone in Group: that if G is a group with

5 LIMITS 111
UG =∏
i UDi and each projection pi : G → Di a homomorphism, thenG = limD. Let x, y ∈ G, with x = (xi)i∈I and y = (yi)i∈I. Then
(xy)i = pi(xy) = pi(x)pi(y) = xiyi
Likewise for inverses and the identity of G. So the operations are definedpointwise in G and G = limD (not merely isomorphic to it).
(b) The argument of part (a) applies virtually without change. Instead ofone operation8, we have a collection, but we define all of them pointwise toget limD, and homomorphisms must respect all the operations.
(c) Let’s extend the exercise by looking at Top, Hausdorff, CptHff, andthe various forgetful functors among them.
First U : Top→ Set. Each Di is a topological space, each u is a continuousmap, and U(limD) is the subset of the product
∏UDi satisfying eq.1. We
give∏Di the product topology and the subset the subspace topology, thus
defining limD. (This replaces the “pointwise” aspect of (a) and (b).) Whatabout our three checks? Trivially limD is a topological space. All the
projections pi : limD → Di are continuous (easy). Suppose Hhi−→ Di is
a set of continuous maps satisfying eq.2. As before, there is one and onlyone way to make the required diagram commute in Set, namely with thefunction
h : y 7→ (hi(y))i∈I
Again we have h mapping H into limD because eq.2 implies eq.1. Continu-ity of h falls out of the definitions of the subspace and product topologies.That is, a map h : H → limD is continuous iff the all the compositions
Hh−→ limD ↪→
∏Di
pi−→ Di are continuous, but these are just the hi’s.
So limD is a limit. Does it obey the decree of the first bullet of Def.5.3.5?Let’s write L = (limD
pi−→ Di)i∈I for the limit cone, and let’s suppose L′ =
8Or three, if you want to treat inverses and the identity as “built-in” operations ofthe group.

5 LIMITS 112
(Tp′i−→ Di)i∈I is another cone on D with UL′ = UL. That is, UT = U(limD)
and Upi = Up′i for all i. U is faithful, so pi = p′i for all i. Since limD isa limit, we have a continuous h : T → limD with pih = pi for all i, i.e.,the i-th component of h(x) equals the i-th component of x for all i and allx ∈ T . So Uh is the identity.
But this doesn’t rule out T having a finer topology than limD. To go toextremes, we could endow U(limD) with the discrete topology and we’dget a perfectly good cone L′ with UL′ = UL. In short, U does not reflectlimits, and so doesn’t create them. (See §5.19.) However, if we insist thatL′ be a limit cone, then the (set-theoretic) identity between T and limD isa homeomorphism. In the terminology of §5.19, U lifts limits uniquely.
As for the sequence of forgetful functors CptHff ↪→ Hausdorff ↪→ Top,each is a full subcategory of the next. So let’s take the general situation,A ↪→ B with A a full subcategory of B. First thing to note: if UL is a limitcone in B, then L is a limit cone in A. (All the objects and morphisms of Land UL are the same; the ‘U ’ just identifies the surrounding category. Notewhy the fullness assumption matters.)
Next, if UL is a cone on UD and the vertex of UL belongs to A, thenthe whole cone L belongs to A by fullness. Putting all these observationstogether, limits lift uniquely from B to A, provided the vertices lift.
Limits in Top are subspaces of direct products. A direct product of Haus-dorff spaces is Hausdorff; likewise a subspace. So we have unique lifting oflimits from Top to Hausdorff. But there’s a bit more: since the subspaceis defined by the equations (1), limits in Hausdorff are closed subspaces.Direct products of compact spaces are compact, as are closed subspaces, sowe have unique lifting of limits from Hausdorff to CptHff.
It’s obvious that unique lifting is preserved by composition of functors, so wehave unique lifting from Set to all three of our topological categories. Butwe have one last twist: the forgetful functors from CptHff reflect limits,

5 LIMITS 113
and thus create limits. Proof: if L is a cone on D in CptHff and UL is alimit cone, then UL lifts to a limit cone L′ on D. So there is a continuousmap from the vertex of L to the vertex of L′. Set-theoretically this is theidentity map. But by basic topology (see §1.12), any continuous map froma compact space to a Hausdorff space sends closed sets to closed sets, sothe topologies of the two vertices are the same and the vertices are identicalobjects in CptHff.
In contrast, the forgetful functors from Hausdorff don’t reflect limits, bythe same argument we gave for Top.
5.21 5.3.12, p.140
A much weaker hypothesis about the functor F suffices. Suppose that ifthere is a limit cone on FD, then there is a limit cone that lifts to a limitcone on D (see §5.19). Briefly, if M is a limit cone on FD (in B), then thereis a limit cone FL on FD such that L is a limit cone on D (in A).
Both the strict notion of “create limits” (Def.5.3.5, p.139) and the “morehealthy and inclusive” (top of p.140). imply this hypothesis. But it alsoholds if F lifts limits (§5.19). For example, the forgetful functor U : Top→Set lifts limits, but does not create limits in either sense, because it doesnot reflect limits (see §5.20).
Let D : I → A be a diagram of shape I in A. Then FD : I → B is adiagram of shape I in B, so it has a limit cone because B has limits. Sothere is a limit cone L on D by our hypothesis. So A has limits of shape I.
Next, suppose that L is a limit cone in A on D. Then FD is a diagramin B, so by our hypothesis there is a limit cone L′ on D with FL′ a limitcone on FD. Since L and L′ are limit cones on D, they are isomorphic.(See Remark 5.1.20, p.119: limits are unique up to unique isomorphism.)Functors preserve isomorphisms, so FL and FL′ are isomorphic. Since FL′

5 LIMITS 114
is a limit cone, FL is too. So F preserves limits.
Combining this result with §5.20, we conclude that Group and other alge-braic categories are complete; likewise Top, Hausdorff, and CptHff. Theforgetful functor Group→ Set preserves limits; likewise in the chain
CptHff ↪→ Hausdorff ↪→ Top→ Set
the forgetful functors from any category to a later category preserves limits.
5.22 5.3.13, p.140
We spell out the meaning of projective: P ∈ B is projective iff for all epicf : A → B, the map a 7→ fa is surjective. So any morphism from P to anobject B can be factored through any epic to B.
(a) In the diagram below left, we need to show that for any a : FS → Yand any epic f : X → Y , there exists a b : FS → X such that fb = a.We transfer over to Set using the adjunction G, getting the diagram belowright.
FS
X Y
∃b ∀a
∀ epic f
S
GX GY
b a
Gf
It’s safe to write b for the desired map from S to GX: since F a G, everymap S → GX is b for some b : FS → X.
Since G preserves epics, Gf is epic. In Set, every object is projective: bmust satisfy the equation a(s) = Gf(b(s)) for all s ∈ S, but since Gf issurjective, we can achieve this by choosing b(s) ∈ (Gf)−1(a(s)).
Now we have to transfer back to B. By naturality of adjunctions, fb =(Gf)b, which equals a, so fb = a.

5 LIMITS 115
Note that the same proof works if we replace Set with any category where allobjects are projective. Also note this corollary: free algebraic objects (freegroups, free abelian groups, vector spaces over a field k,. . . ) are projective.
(b) In Abelian, the surjective homomorphisms are epic, since the forgetfulfunctor to Set pulls back epics (item (8) of §1.11; the converse is easy toprove, but we won’t need it.) So the canonical epimorphism Z→ Zn is epic.
Let P = Zn, A = Z, B = Zn. The only map P → A, i.e., Zn → Z, is thezero map. So the identity Zn → Zn does not factor through the canonicalepimorphism, and Zn is not projective.
(c) We spell out the meaning of injective, with reference to the originalcategory B: I is injective iff any morphism A→ I can be factored throughany monic A→ B.
Suppose I is a vector space over k and a : A → I is a linear map andf : A → B is a monomorphism. By basic linear algebra, the image f(A)has a complement in B, i.e., B can be written as a direct sum B = f(A)⊕N .The range restriction of f , f ′ : A → f(A), is an isomorphism, so we cancompose its inverse with a to get a map b′ : f(A)→ I. Then b′f ′ = a. Weextend b′ to all of B by letting N be the null space: b(y + n) = b′(y) for ally ∈ f(A), n ∈ N . So bf = a.
In Abelian, Z is not injective, as we see from this diagram for any fixedn > 1:
Z Z
Z
×n
1Z

6 ADJOINTS, REPRESENTABLES AND LIMITS 116
6 Adjoints, representables and limits
6.1 6.1.5, p.146
We let I = {1, 2}. A diagram D : I→ A is just a pair of objects (D1, D2), so[I,A] = A×A and ∆A = (A,A) (as Leinster points out on p.143). A coneon D with vertex A, say a : ∆A ⇒ D, is a pair of morphisms ai : A → Di
(i = 1, 2). (Although this a is a natural transformation, we prefer not touse a greek letter for it.) A limit is a cone p : ∆P ⇒ D (i.e., a vertex Pand morphisms pi : P → Di) such that for any cone a on D with vertex A,there is a unique morphism f : A → P such that pif = ai (i = 1, 2). Inother words, P is a product D1 ×D2 with projections pi.
The functor Cone(−, D) : Aop → Set takes A ∈ A to the set of all coneson D with vertex A, i.e., all the pairs (a1, a2) with ai : A→ Di. This func-tor takes a morphism f : A → A′ to the “morphism of cones” (a′1, a
′2) 7→
(a′1f, a′2f) = (a1, a2). A representation of a contravariant functor X : Aop →
Set sets up natural bijections X(A)↔ A(A,P ) for some P ∈ A. So a rep-resentation of Cone(−, D) should give us bijections Cone(A,D)↔ A(A,P ).By Coro.4.3.2, there is a “universal element” p ∈ X(P ) = Cone(P,D) suchthat for each a ∈ Cone(A,D) there is a unique f : A→ P with Xf(p) = a,i.e., (p1, p2) 7→ (p1f, p2f) = (a1, a2). So a representation is basically thesame as a product (pi : D1 ×D2 → Di)i=1,2. This is Prop.6.1.1 for the caseI = {1, 2}.
Summarizing: we start with a diagram D = (D1, D2) of shape {1, 2}, thenlook at all cones a with all vertices A over D; among these, we find aparticular vertex P , and among the cones of Cone(P,D) we find a particularcone (p1, p2). The universal element property of Coro.4.3.2 (p.99) is thesame as the limit property of Prop.6.1.1 (p.143).
Coro.6.1.2 simply says here that products are unique up to isomorphism.Lemma 6.1.3(a) says that given two products D1 × D2 and D′1 × D′2 and

6 ADJOINTS, REPRESENTABLES AND LIMITS 117
morphisms αi : Di → D′i (i = 1, 2), there is a unique α : D1×D2 → D′1×D′2satisfying the obvious commutation condition αipi = p′iα. Lemma 6.1.3(b)adds that if we have morphisms fi : A → Di and f ′i : A → D′i, then anys : A→ A′ commuting with αi : Di → D′i (i = 1, 2) will also commute withα : D1 ×D2 → D′1 ×D′2.
Prop.6.1.4 says that ifA has all binary products, then (D1, D2) 7→ D1×D2 isa functor from A×A to A, which is right adjoint to the functor A 7→ (A,A).Leinster’s last paragraph points out that we have to make an arbitrarychoice of D1 ×D2 for each pair (D1, D2), but no big deal since all possiblechoices are isomorphic.
Finally, I note that the general case isn’t all that different. We have (Di)i∈Iinstead of (Di)i=1,2, and commutativity conditions flowing from the mor-phisms Df : Di → Dj in the diagram, but these mostly take care of them-selves.
6.2 6.1.6, p.146
Example 1.2.8 (p.22) tells us that a diagram D : I → Set is a (left) G-set.If ∗ stands for the single object in I treated as a category, then D(∗) isthe underlying set of the G-set, and a · x = D(a)x is the action, where themorphism a ∈ I is an element of the group. Example 1.3.4 (p.29) tells usthat a natural transformation α : D ⇒ D′ is a G-equivariant map.
What does the diagonal functor ∆ look like here? Given a set A, ∆(A) isthe functor I → A that sends ∗ to the set A, and every morphism a ∈ Ito the identity function on A. In other words, ∆(A) is A with the trivialaction. In §2.5 (Exercise 2.1.16(a), p.50), this was called Triv.
What is a cone on D? It’s a set X and a function f : X → D(∗) such thatD(a)f = f for every morphism a of I. In other words, a · f(x) = f(x) forevery a in the group and every x ∈ X, so the image of f is left pointwise

6 ADJOINTS, REPRESENTABLES AND LIMITS 118
fixed by the action of the group.
What is a limit cone on D? It’s a cone f : X → D(∗) such that any othercone factors through f ; it’s easy to see that this forces f to be a bijectionbetween X and the fixed points of D, Fix(D).
We now see that Lemma 6.1.3(a) (p.144) says, in essence, that any G-equivariant map D → D′ restricts to a map Fix(D)→ Fix(D′). Prop.6.1.4(p.145) says that the functor Fix : G-set → Set is right adjoint to ∆ =Triv : Set→ G-set, which we saw in §2.5.
Now for the dual. A cocone is a function f : D(∗)→ X such that f(a ·d) =f(x) for every a in the group and every d ∈ D(∗). So each orbit is sentto a single element of X. It’s not hard to see that a colimit is (up toisomorphism) the function d 7→ orbit(d), sending the G-set D to its set oforbits Orb(D). In §2.5 we saw that Orb is left adjoint to Triv.
So Orb a Triv a Fix is a special case of lim→a ∆ a lim
←.
See also §2.5 and §6.9(c).
6.3 The Density Theorem
I found it difficult at first to wrap my mind around the proof of the Den-sity Theorem (Theorem 6.2.17, pp.155–156). Herewith some thoughts thathelped me feel comfortable with it.
First, why do we need the category of elements? Why not just use theYoneda imbedding H• : A → Presheaves(A) as the diagram? But thatdiagram doesn’t depend on the functor X at all, and so we can hardlyexpect its colimit to give us X.
This highlights the key difference between H• and H• ◦ P . An arbitrary

6 ADJOINTS, REPRESENTABLES AND LIMITS 119
A A′A
XA XA′x1 x2 x′1 x′2 x′3EX
PP
HAHA HA′ HA′HA′
H• ◦ P
XA XA′
x1 x2 x′1 x′2 x′3
y1 y′1 y′2
A A′A
X XY Y
Y A Y A′
Presheaves(A)
• •
XA XA′
Figure 6: Density Theorem

6 ADJOINTS, REPRESENTABLES AND LIMITS 120
presheaf X will typically be much “richer” than a representable HA—oftenHA(A) contains only one element for any A ∈ A, but XA typically containsmany elements. (Example: the presheaf X of continuous functions on atopological space—see §4.12.) In the diagram H• ◦ P , the HA’s appear“with multiplicity”: we have as many “copies” of HA as there are elementsof XA.
Fig.6 illustrates this. At the top and the bottom of the figure we have thecategory A, with the two objects indicated by labeled dots. The presheafX has XA = {x1, x2} and XA′ = {x′1, x′2, x′3}. The category of elementsEX has five objects, namely the pairs (A, x1), (A, x2),. . . , (A′, x′3). In thefigure I label these objects more succinctly, and use dashed boxes to groupthe objects according to the A-object they come from. The projection P isshown going from EX to A.
Most of the action takes place in the big middle box, Presheaves(A). Theobjects of this category are presheaves over A, but I have adopted a non-uniform presentation. The diagram H• ◦ P consists of the representablesHA and HA′ , which I display “with multiplicity”. That is, H• ◦ P sendsboth (A, x1) and (A, x2) to the same representable HA, so I display it twice;likewise for the three HA′ ’s.
Note that the “legs” of cocones (and cones) are indexed by the small index
category: (DIlI−→ V )I∈I for a cocone with vertex V on a diagram D : I→ C.
We can have DI = DJ with lI 6= lJ .
I indicate the functors X and Y by showing the sets XA, XA′, Y A, andY A′ as boxes with their elements inside. Arrows from the bottom box tothe middle box suggest the functors X and Y . The “guts” of X and Y are,so to speak, spread out inside the presheaf box.
Now let’s think about the cocone with vertex X and diagram H• ◦ P . Foreach object (A, xi) in EX, we need a leg from its imageHA toX—i.e., a mor-phism in Presheaves(A). In other words, an element of Presheaves(A)[HA, X].

6 ADJOINTS, REPRESENTABLES AND LIMITS 121
The Yoneda lemma says there is a canonical bijection
Presheaves(A)[HA, X] ∼= XA
I indicate the leg (aka morphism aka natural transformation) with an arrowfrom the copy of HA to the displayed element of XA.
Note the 1–1 correspondence between the dashed box of HA’s and the boxXA, likewise for HA′ and XA′. We have the multiplicity of HA’s and HA′ ’sto thank for this (and the Yoneda lemma, of course). That’s why we needthe category of elements.
OK, what about the cocone with vertex Y ? The Yoneda lemma says thatPresheaves(A)[HA, Y ] ∼= Y A, so the requisite legs look like arrows from theHA’s and HA′ ’s to elements in the boxes Y A and Y A′. But then we imme-diately get mappings from XA to Y A, and from XA′ to Y A′: just use theHA’s and HA′ ’s as intermediaries (go up and then down). These mappingsXA → Y A, XA′ → Y A′ meld together to form a natural transformationα : X ⇒ Y .
To relate this to Leinster’s proof: he notates the cocone on Y thus (p.156)(HA
αA,x−−→ Y)A∈A,x∈XA
and uses the Yoneda mapping αA,x 7→ yA,x to define the functions αA : x 7→ yfor each A.
Several things need checking: the commutativity conditions on the cocones,the naturality of α, the commutativity conditions on α, and the uniquenessof α. Fig.7 will guide us through this thicket. I’ve removed some of theclutter of fig.6 to make room for different clutter. I will argue “the generalfrom the particular”: i.e., x2 and x′1 are intended as “typical” elements ofXA and XA′, etc.
First, I’ve used ξA2 and ξA′1 to denote two of the morphisms from the coconeon H•◦P with vertex X. (Leinster would denote these ξA,x2 and ξA′,x′1 .) Two

6 ADJOINTS, REPRESENTABLES AND LIMITS 122
A A′A
XA XA′x2 x′1EX
PP
HA HA′
H• ◦ P
XA
x2 x′1
y1 y′1
A A′A •
X XY Y
Y A Y A′
Presheaves(A)
•
XA XA′
ξA2 ξA′1
f
f
Hf
Xf
Y f
αA αA′
αA′1
αA1
Figure 7: Commutativity Conditions

6 ADJOINTS, REPRESENTABLES AND LIMITS 123
layers are implicit here: ξA2 is a natural transformation HA ⇒ X, whosecomponents are therefore functions (ξA2)B : HA(B) → XB. Fortunatelythe Yoneda lemma tells us that ξA2 is completely determined by the singleelement x2 ∈ XA, so we get away with only a single arrow in the figure.
I’ve used αA1 and αA′1 to denote two of the morphisms from the coconeon H• ◦ P with vertex Y . Also, αA and αA′ denote two components of thenatural transformation α : X ⇒ Y .
We will need two results (both on p.97) from the proof of the Yoneda lemma.First, the fact that a natural transformation τ : HA ⇒ X is determined byits single value τ(1A) ∈ XA. Second, Eq.4.5 that justifies this. With slightlytweaked notation:
τA′(f) = (Xf)τA(1A), (f : A′ → A) (3)
To keep fig.6 simple, I left out any morphisms in EX, but of course thethings we have to check arise from just these morphisms. Fig.7 displays amorphism f : (A′, x′1)→ (A, x2). By definition of EX, this is an f : A′ → Ain A such that (Xf)x2 = x′1. Note that Pf = f , and recall that H• : f 7→Hf , where Hf is defined by
Hf :HA′ ⇒ HA, f : A′ → A
Hf :HA′(B)→ HA(B), B ∈ A
Hf : a 7→ fa, a : B → A′
(The fussy reader will complain that two of those Hf ’s should have been(Hf )B.) The natural transformations ξAi were defined via the Yonedalemma, so we have to verify that they form a cocone. The equation tocheck for f is
ξA2Hf = ξA′1 (4)
ξA2 and ξA′1 are determined by the requirements
(ξA2)A(1A) = x2 ∈ XA, (ξA′1)A′(1A′) = x′1 ∈ XA′

6 ADJOINTS, REPRESENTABLES AND LIMITS 124
To verify (4), it’s enough to evaluate both sides at 1A′ . We use (3) withτ = ξA2, B = A′, and a = 1A′ .
(ξA2)A′Hf (1A′)?= (ξA′1)A′1A′
(ξA2)A′(f)?= x′1
(Xf)(ξA2)A(1A)?= x′1
(Xf)x2X= x′1
So the ξ’s form the legs of a cocone.
The α’s are assumed to form the legs of a cocone with vertex Y . I.e.,
(αA1)A′Hf (1A′) = (αA′1)A′1A′
and evaluating both sides just like for ξ, we conclude
(Y f)y1 = y′1
Now, αA(x2) = y1 and αA′(x′1) = y′1. If you stare at the Presheaves box in
fig.7 for a moment, you’ll see this naturality square:
XA XA′
Y A Y A′
Xf
αA αA′
Y f
So α is a natural transformation.
Finally, we do the commutativity condition and uniqueness of α together.Let’s write HA2 for the “copy” of HA associated with the leg ξA2. Theequation αξA2 = αA1, stemming from (A, x2) ∈ EX, looks like this:

6 ADJOINTS, REPRESENTABLES AND LIMITS 125
HA2
X Y
ξA2 αA1
α
The diagram stands for an equation among natural transformations, whichholds if and only if it holds when evaluated at 1A ∈ HA(A). That evaluationreduces to αA(x2) = y1, and the “go up then down” prescription given forα insures this. So commutativity holds, but commutativity also prescribesthe value of αA(x2) for every (A, x2) ∈ EX, making α unique.
6.4 6.2.20, p.157
(a) In one direction this is easy. Suppose αA monic for all A ∈ A. Letαβ = αβ′ for two natural transformations β, β′ : W ⇒ X. This means thatαAβA = αAβ
′A for all A, and so βA = β′A for all A, i.e., β = β′.
In the other direction, suppose α is monic in [A,S]. By Lemma 5.1.32(p.124) the following diagram is a pullback square:
X X
X Y
1
1 α
α
By Coro. 6.2.6 (p.151), the evaluation functor evA preserves pullbacks foreach A ∈ A. Here we use the hypothesis that S has pullbacks (see Warning6.27, p.151), i.e., all limits of shape P; P is defined in eq.5.14 (p.118), andlooks like a pullback square with the northwest corner missing. Applying

6 ADJOINTS, REPRESENTABLES AND LIMITS 126
evA to the pullback square for α gives
XA XA
X Y A
1
1 αA
αA
So αA is monic by Lemma 5.1.32.
(b) By part (a), α is monic iff αA is injective for all A, and α is epic iffαA is surjective for all A. (Note that we don’t switch monic and epic: theassertion of (a) holds for all small categories A, and so in particular for thesmall category Aop. Observe also that [Aop,Set] 6= [A,Set]op.)
(c) The first direction in part (a) did not use the fact about pointwise limits.It remains to prove the other direction, in contrapositive form. We need toshow that if α : X ⇒ Y has a non-injective αA, then α is not monic. So weneed β, β′ : W ⇒ X such that αβ = αβ′ but β 6= β′.
Since αA : XA → Y A is not injective, we have αA(a) = αA(a′) for somea 6= a′, a, a′ ∈ XA. Let W = HA. By the Yoneda lemma, natural trans-formations HA ⇒ X are in 1–1 correspondence with elements of XA, withβ : HA ⇒ X uniquely determined by the value of βA(1A). Let βA(1A) = aand β′A(1A) = a′. So β 6= β′. However, the compositions αβ and αβ′ arenatural transformations HA ⇒ Y agreeing at 1A, and so αβ = αβ′.
For epics, just dualize.

6 ADJOINTS, REPRESENTABLES AND LIMITS 127
6.5 6.2.21, p.157
(a) First we elucidate the sum of presheaves X + Y . (It’s dual to X × Y ,considered at the top of p.150.) Two equations tell the story:
(X + Y )A = XA+ Y A
(X + Y )f = Xf + Y f
Recall that the direct sum of functions Xf : XA → XB and Y f : Y A →Y B is the function defined by cases on domain XA+ Y A:
(Xf + Y f)a =
{(Xf)a when a ∈ XA(Y f)a when a ∈ Y A
It’s easy to verify directly the compliance of this construction with thecolimit definition of the sum. Alternately, we can appeal to the dual ofTheorem 6.2.5 (p.149)—colimits are computed pointwise.
Assume that HA∼= X + Y , so we have a natural equivalence α : HA ⇔
X + Y . This means that for each B we have a bijection between HA(B)and XB + Y B. In other words, we have a partition of HA(B) for each B;let’s write HA(B) = XB+Y B. Moreover, the naturality squares mean thatHA(f) respects the partitions: if f : B → A, then HA(f) sends XA intoXB and Y A into Y B.
Now we look at 1A ∈ HA(A) = XA+Y A. Suppose 1A ∈ XA. If f ∈ HA(B),i.e., f : B → A, then HA(f) : 1A → f . Since HA(f) respects the partitions,it follows that f ∈ XB. I.e., every element of HA(B) belongs to XB, so allY B = ∅. It follows that all Y B = ∅ as well. If 1A ∈ Y A then all XB = ∅by the same reasoning.
A slight variant on this proof: work directly with the partitions XA+ Y A,instead of transferring them over to HA. Because X + Y is equivalent toHA, we can appeal to Coro.4.3.2 (p.99). The universal element u takes the

6 ADJOINTS, REPRESENTABLES AND LIMITS 128
place of 1A, and the equation (Xx)u = x replaces HA(f) : 1A → f . If ubelongs to XA then all Y B = ∅, etc.
(b) No representable can ever equal the identically ∅ presheaf, since HA(A)always contains at least 1A.
6.6 6.2.22, p.158
Let 1 be a singleton in Set and let X be a presheaf on A. Consider (1⇒ X).Its objects are pairs (A, 1
x−→ XA) with A ∈ Aop. Since XA ∈ Set, 1x−→ XA
can be identified with an element of XA. A morphism in (1 ⇒ X) from
(A′, 1x′−→ XA′) to (A, 1
x−→ XA) is a morphism f : A′ → A in Aop such thatthis diagram commutes:
1 XA
XA′
x
x′Xf
which is exactly the condition that (Xf)x = x′.
6.7 6.2.23, p.158
The category of elements of a presheaf X : Aop → Set consists of pairs
(A ∈ A, u ∈ XA); morphisms (B, x)f−→ (A, u) are morphisms B
f−→ Asuch that (Xf)u = x (Def.6.2.16, p.155). So (A, u) is terminal iff for everyx ∈ XB there is a unique f : B → A such that (Xf)u = x. But this is theuniversal element criterion for a presheaf to be representable (Coro.4.3.2,p.99).

6 ADJOINTS, REPRESENTABLES AND LIMITS 129
A
WA XA
A
XW
•••
• •••
•
awa1 wa2
τA•••
• •wa1 wa2
•T (•)
•T (•)
•T (•)
A
(A,a)T (A,a)
X
τ ∈ Presheaves(A)/X T ∈ Presheaves(EX)
Figure 8: Slice of a Presheaf
6.8 6.2.24, p.158
We will show that [Aop,Set]/X is equivalent to [EXop,Set], where EX isthe category of elements (Def.6.2.16, p.155). For intuition, consult fig.8. (Iwrite Presheaves(C) for the category [Cop,Set].)
In the left half of the figure, we see an object τ of the slice categoryPresheaves(A)/X. Recall that the objects of Presheaves(A)/X are mor-phisms of Presheaves(A), which are natural transformations τ : W ⇒ X.So for any A ∈ A, τA is a function from WA to XA. In the figure, τAis given by horizontal projection. Note that the illustrated τA is neitheronto (the top element of XA has no preimage), nor 1–1. The dashed linesemphasize how τA partitions WA, each partition being an inverse imageτ−1A (a) for some a ∈ XA.
In the right half of the figure, we see an object of the presheaf categoryPresheaves(EX). Recall that the objects of Presheaves(EX) are contravari-ant functors T from EX to Set, and the objects in EX are pairs (A, a) witha ∈ XA. So for any (A, a) ∈ EX, T (A, a) is a set. The dashed box groupsall the objects (A, a) that come from the same A ∈ A.

6 ADJOINTS, REPRESENTABLES AND LIMITS 130
To show that our categories are equivalent, we need functors P and Q fromleft to right and right to left. That is, if τ and T correspond (up to naturalequivalence):
P : Presheaves(A)/X → Presheaves(EX)
P : τ 7→ Pτ ∼= T
Q : Presheaves(EX)→ Presheaves(A)/X
Q : T 7→ QT ∼= τ
The actions of P and Q on morphisms also need defining, but we’ll addressthis later. We also need natural equivalences QP ∼= 1left and PQ ∼= 1right.
The definitions of Pτ and QT can almost be read off the figure. For each(A, a) ∈ EX, Pτ(A, a) is a set, so let
Pτ(A, a) = τ−1A (a)
Pτ is a functor, so we need to define Pτ(f) for any morphism (B, b)f−→ (A, a)
in EX. Pτ(f) will be a function from the set Pτ(A, a) to the set Pτ(A, a).Because τ is a natural transformation, we have the commuting square
WA WB
XA XB
Wf
τA τB
Xf
So
τB(Wf) = (Xf)τA
τ−1B τB(Wf)τ−1
A (a) = τ−1B (Xf)τAτ
−1A (a)
(Wf)τ−1A (a) ⊆ τ−1
B (b)
(Wf)Pτ(A, a) ⊆ Pτ(B, b)

6 ADJOINTS, REPRESENTABLES AND LIMITS 131
(Recall that if (B, b)f−→ (A, a), then (Xf)a = b. We’ve also used the set-
theoretic inequality K ⊆ h−1hK.) So if we restrict Wf to Pτ(A, a), it mapsinto Pτ(B, b). Define
Pτ(f) = Wf |Pτ(A,a)
I leave it to you to check the functoriality of Pτ (i.e., Pτ(fg) = Pτ(f)Pτ(g)).
Defining QT involves more moving parts. QT is a natural transformationW ⇒ X, so we need to define both the (contravariant) functor W (let’sdenote it WT ) and the functions QTA for each A ∈ A. WTA and WTf mustbe specified for each A and each morphism f : B → A in A.
WTA = {(w, a)|a ∈ XA,w ∈ T (A, a)}WTf : (w, a) 7→ ((Tf)w, (Xf)a) f : (B, b)→ (A, a)
QTA : WTA→ XA
QTA : (w, a) 7→ a
Let’s examine these formulas, starting with the definition of WTA. Thefigure suggests collecting all the wai’s as a ranges over XA, i.e., the union⋃a∈XA T (A, a). However, the sets T (A, a) might not be disjoint. By con-
trast, as we saw, the different “strata” of WA—the inverse image setsτ−1A (a)—partition WA. So we tag each wai with its a before combining
the T (A, a)’s. Effectively, we form the disjoint union⊔a∈XA T (A, a).
To understand the formula for WTf , we need to delve into the artful lan-guage Leinster uses to define morphisms in EX. He says (conforming hisnotation to ours) that “maps (B, b) → (A, a) are maps f : B → A in Asuch that (Xf)a = b” (p.155). Now, a morphism in A can’t literally bea morphism in EX. Rather, a morphism in A splits into multiple mor-phisms in EX. For each pair (a, b) ∈ XA ×XB with (Xf)a = b, we havea morphism (B, b)→ (A, a).9 So the morphism (B, b)→ (A, a) is uniquely
9Visually, the single arrow Xf : XA → XB splits into all the arrows from theindividual elements of XA to their targets in XB. The direction of the arrows in EX isreversed, however, because X is contravariant.

6 ADJOINTS, REPRESENTABLES AND LIMITS 132
identified by f in A and a ∈ XA. Writing fa for this morphism, we haveTfa : T (A, a)→ T (B, b). We can also write, more precisely:
WTf : (w, a) 7→ ((Tfa)w, (Xf)a)
Essentially, WTf is defined one stratum at a time, cobbling together theTfa’s for all the a’s in XA.10
The functoriality of WT follows from the functoriality of X and of T .
The definition of QTA is simplicity itself, just horizontal projection in thefigure. The naturality of QT follows routinely from the definitions.
Next, the action of P on morphisms in Presheaves(A)/X, i.e., α : V ⇒ Wmaking this diagram commute:
V
X
W
σ
α
τ
We have σ = τα, and hence for each A and each a ∈ XA
σA = τAαA
σ−1A = α−1
A τ−1A
σ−1A (a) = α−1
A τ−1A (a)
αAσ−1A (a) ⊆ τ−1
A (a)
αAPσ(A, a) ⊆ Pτ(A, a)
10Note that if T (A, a) and T (A, a′) intersect, say containing a common element w,there is no guarantee that Tfa(w) = Tfa′(w). So it’s a good thing we defined WTAusing the disjoint union.

6 ADJOINTS, REPRESENTABLES AND LIMITS 133
So we can define Pα one stratum at a time, i.e.,
Pα(A,a) :Pσ(A, a)→ Pτ(A, a)
Pα(A,a) :w 7→ αA(w)
(Note that Pα : Pσ ⇒ Pτ . I leave it to you to check the naturality of Pα.Also left to you: the functoriality of P .)
Next stop: the action of Q on morphisms in Presheaves(EX). Suppose α :S ⇒ T is a natural transformation (i.e., a morphism in Presheaves(EX)).We will define a natural transformation Qα making this diagram commute:
WS
X
WT
QS
Qα
QT
So QαA is a function from WSA to WTA. We define it by
QαA : (w, a) 7→ (α(A,a)(w), a)
Again we do things stratum-by-stratum: (w, a) belongs to the a-stratum ofWSA, derived from S(A, a). The component α(A,a) of the natural transfor-mation α maps S(A, a) into T (A, a). The tags (i.e., strata) don’t change.To verify that Qα is natural, we check that this square commutes for anyf : B → A:
WSA WSB
WTA WTB
QαA
WSf
QαB
WT f

6 ADJOINTS, REPRESENTABLES AND LIMITS 134
This is just the stratified version of the naturality squares for α, S, and T
S(A, a) S(B, b)
T (A, a) T (B, b)
α(A,a)
Sfa
α(B,b)
Tfa
aggregated over all a ∈ A.
After all this work, the punchline—the natural equivalences QP ∼= 1left andPQ ∼= 1right—come as a bit of an anticlimax. PQT is this functor:
PQT (A, a) = {(w, a)|w ∈ T (A, a)}PQTf(w, a) = (Tf(w), f(a))
i.e., it just tags all the elements of T (A, a) with a, and does “tagged” versionof Tf . So we have the obvious natural equivalence ϕ : 1right ⇒ PQ:
ϕ(A,a) : T (A, a)→ PQT (A, a)
ϕ(A,a) : w 7→ (w, a)
For QP , the story is pretty much the same. If τ : W ⇒ X, then Pτseparates the strata of WA, with w going into stratum τA(w). Q then tagsw with τA(w) and aggregates the tagged elements. So:
τ : W ⇒ X
QPτ : WPτ ⇒ X
QPτA : WPτA→ XA
QPτA : (w, τA(w)) 7→ τA(w)
So the natural equivalence ψ : 1left ⇒ QP is just
ψA : WA→ WPτA
ψA : w 7→ (w, τA(w))
QED

6 ADJOINTS, REPRESENTABLES AND LIMITS 135
6.9 6.2.25, p.158
(a) We will write L for LanF (X). The diagrams below illustrate the uni-versal property of L; we explicate η, β, β, and σ below.
A S
B
F
X
η
L
A S
B
F
X
β β
σ
L
Y
Here η : X ⇒ LF is a natural transformation, yet to be defined. For anynatural transformation β : X ⇒ Y F , we will define a natural transformationβ : L⇒ Y . The desired bijection between natural transformations β : X ⇒Y F and σ : L⇒ Y will be given by
β 7→ β, σ 7→ (σF )η
and we will show that these are inverse, i.e.,
(βF )η = β, (σF )η = σ
(Note that (βF )η and (σF )η involve both horizontal and vertical composi-tion.) Our task splits into these subtasks:
1. Define LB for all B ∈ B.
2. Define Lb for all b : B → B′.
3. Show that L is functorial.
4. Define ηA : XA → LFA for all A ∈ A, and show that this defines anatural transformation η : X ⇒ LF .
5. Given any natural transformation β : X ⇒ Y F , define βB : LB →Y B for all B ∈ B.

6 ADJOINTS, REPRESENTABLES AND LIMITS 136
6. Show that β is a natural transformation L⇒ Y .
7. Show that (βF )η = β and (σF )η = σ for any β : X ⇒ Y F and anyσ : L⇒ Y .
(a1): Leinster defines LB as the colimit of the diagram
(F ⇒ B)PB−→ A
X−→ S
We dissect this, so as to fix some notation. Given B ∈ B we first find allAi ∈ A such that there are morphisms fi : FAi → B, and also look at alla : Ai → Aj satisfying the “triangle condition”:
fi = fj(Fa)
This is (F ⇒ B), with the fi’s corresponding to its objects and the triangleconditions to its morphisms. Next we form the diagram DB in S with nodesXAi and conditions Xa : XAi → XAj, and let LB be the colimit of DB.So there are legs li : XAi → LB satisfying triangle conditions
li = lj(Xa)
We let I be the index set for the fi’s, Ai’s, and li’s, so (fi)i∈I is the familyof morphisms fi : FAi → B and (li)i∈I is the family of legs li : XAi → LB.So basically:
(F ⇒ B) : (fi : FAi → B)i∈I
Colimit cocone : (li : XAi → LB)i∈I
Note that the fi’s are all distinct (indeed, in 1–1 correspondence with I),but the Ai’s may not be. (“Multiplicity”: see the discussion in §6.3.) Also,we should say “a colimit” rather than “the colimit”. We must chose acolimit cocone (call it CB) for each B. The mapping fi 7→ li is the key tothe construction.11
11Why key? Ignoring details, because it moves morphisms from B to S, the chiefaccomplishment of L.

6 ADJOINTS, REPRESENTABLES AND LIMITS 137
(a2): Suppose b : B → B′. So we have a family
(f ′i′ : FA′i′ → B′)i′∈I′
satisfying a set of triangle conditions, and a colimit cocone
(l′i′ : XA′i′ → LB′)i′∈I′
Since fi : FAi → B, we have FAifi−→ B
b−→ B′, and so bfi : FAi → B′ isone of the f ′i′ ’s sending FA′i′ to B′. Here A′i′ = Ai. Set f ′i = bfi, so we havea map
(F ⇒ B)→ (F ⇒ B′)
fi 7→ bfi = f ′i
and therefore (F ⇒ B) maps into (F ⇒ B′). It’s easiest to picture the casewhere fi 7→ f ′i is injective. Then we can say that I ⊆ I ′, Ai is one of theA′i′ ’s, and f ′i is one of the f ′i′ ’s. In general we just have a map I → I ′, butthe rest of the previous sentence holds. (About notation: i′ ranges over I ′,i ranges over I, and f ′i , like f ′i′ , belongs to (F ⇒ B′).)
Each triangle condition of (F ⇒ B) maps to one for (F ⇒ B′): givena : Ai → Aj with fi = fj(Fa), we have bfi = bfj(Fa), i.e., f ′i = f ′j(Fa). Sothe mapping (F ⇒ B) into (F ⇒ B′) is a functor. It follows that DB mapsinto a “subdiagram” of DB′ : each node XAi in DB appears in DB′ , and anyXa : XAi → XAj belonging to DB also belongs to DB′ . So the mappingI → I ′ determines a “sub-cocone” of CB′ , i.e., a cocone on DB with legs l′iand vertex LB′.
Since CB is a colimit cocone, there is a unique Lb : LB → LB′ satisfying
l′i = (Lb)li ∀i ∈ I
(a3) Suppose we have Bb−→ B′
b′−→ B′′. The defining property of L(b′b) is
l′′i = L(b′b)li ∀i ∈ I

6 ADJOINTS, REPRESENTABLES AND LIMITS 138
However,l′′i = (Lb′)l′i and l′i = (Lb)li ∀i ∈ I
sol′′i = (Lb′)(Lb)li ∀i ∈ I
so L(b′b) = (Lb′)(Lb).
Fine point: we have to show that the composition of the mappings I → I ′ →I ′′ is the mapping I → I ′′. This follows from the equations fi
′′ = b′f ′i = b′bfi.
(a4) For any A ∈ A, we have 1FA : FA → FA as a component of thediagram DFA. In other words, there is an index i ∈ I with Ai = A andfi = 1FA; let’s write 1 for that index. So A1 = A, f1 = 1FA, and XA1 = XAis a node in DFA. Hence we have a leg l1 : XA1 → LFA. Set ηA = l1, soηA : XA→ LFA.
Now let’s say p : A→ A′. We have to check the naturality square
XA XA′
LFA LFA′
Xp
l1=ηA ηA′=l′1′
LFp
From the defining property of LFp, we have
l′1 = (LFp)l1
where l′1 is the leg in CFA′ corresponding to f ′1 = (Fp)f1 = (Fp)(1FA) = Fp.
Next observe that Xp : XA→ XA′ belongs to DFA′ , because the morphismp : A→ A′ satisfies the triangle condition
FA FA′
FA′Fp
Fp
1FA′

6 ADJOINTS, REPRESENTABLES AND LIMITS 139
giving rise to the Xp arrow in DFA′ , and therefore a triangle condition inCFA′ :
XA XA′
LFA′l′1
Xp
l′1′
We justify the labels on the downward arrows: we noted above that l′1 isthe leg in CFA′ corresponding to Fp, and of course 1′ is the index in I ′ forwhich A′1′ = A′ and f ′1′ = 1FA′ .
So l′1 = l′1′(Xp). Combined with our earlier equation l′1 = (LFp)l1, thisshows that the naturality square commutes.
(a5) We have (by hypothesis) a functor Y : B → S and a natural trans-formation β : X ⇒ Y F ; we want to define βB for all B ∈ B, withβB : LB → Y B. Our only handle on LB is through the colimit coconeCB, so our only way forward is to construct a cocone on DB with vertexY B. Then βB will be the unique completing morphism between the coconevertices.
We assemble the cocone out of two ingredients. The first is the set ofmorphisms fi : FAi → B of (F ⇒ B); this gives us
Y fi : Y FAi → Y B ∀i ∈ I
The second is the set of morphisms βAi, for which
βAi: XAi → Y FAi ∀i ∈ I
Composing these, we define
yi = (Y fi)βAi: XAi → Y B

6 ADJOINTS, REPRESENTABLES AND LIMITS 140
as desired. To show we have a cocone, we have to check the triangle condi-tions. These follow from the diagram
XAi XAj
Y FAi Y FAj
Y B
Xa
βAiβAj
Y Fa
Y fi Y fj
The top square is the naturality square for β, and the bottom triangle resultsfrom applying Y to triangle condition for a : Ai → Aj with fi = fj(Fa). Soyi = yj(Xa), and we have our definition of β. Let’s write CB for the coconewe’ve just constructed.
Let us note the defining property of β:
βBli = yi = (Y fi)βAi∀i ∈ I
βBli : XAi → Y B
(a6) Given b : B → B′, we need to verify commutativity in the naturalitysquare
LB LB′
Y B Y B′
Lb
βB βB′
Y b
To obtain Lb, we mapped DB into a subdiagram of DB′ , which determineda cocone on DB with vertex LB′. To obtain βB, we constructed a differentcocone on DB, with legs yi and vertex Y B. We next construct a cocone Con DB with vertex Y B′, such that both (Y b)βB and βB′(Lb) are completingmorphisms from the vertex LB (of CB) and the vertex Y B (of C). It followsthat (Y b)βB = βB′(Lb).

6 ADJOINTS, REPRESENTABLES AND LIMITS 141
The cocone C is easiest to picture when I → I ′ is injective, since then Cis a sub-cocone of CB′ . In this case, each Ai belongs to DB′ , each f ′i = bfiand each l′i = (Lb)li, and if we set y′i = (Y f ′i)βAi
, then y′i is the leg of CB′
from the node Ai to the vertex Y B′. So the nodes of C are (Ai)i∈I , withlegs (y′i)i∈I from the Ai to Y B′.
All the triangle conditions hold for C because they hold in CB′ . Also thedefining equations for βB′
βB′l′i′ = y′i′ ∀i′ ∈ I ′
include these equations
βB′l′i = y′i ∀i ∈ I
since I ⊆ I ′. Noting that l′i = (Lb)li, we have
βB′(Lb)li = y′i ∀i ∈ I
and we see that βB′(Lb) is a completing morphism from the vertex LB ofCB to the vertex Y B of C.
On the other hand
y′i = (Y f ′i)βAi= Y (bfi)βAi
= (Y b)(Y fi)βAi= (Y b)yi
so appending the morphism Y BY b−→ Y B′ to the bottom of CB also gives us
C. Thus the defining equations for βB yield
(Y b)βBli = (Y b)yi = y′i ∀i ∈ I
and (Y b)βB is also a completing morphism. Therefore
(Y b)βB = βB′(Lb)
as required.

6 ADJOINTS, REPRESENTABLES AND LIMITS 142
What changes if I → I ′ is not injective? Distinct fi’s can map to the samef ′i , and so two nodes labeled Ai in DB can map to the same node in DB′ .However, I → I ′ still induces a map from DB to DB′ , which is the “toprow” of CB′ . This is all we need to construct C. The rest of the argumentis not affected at all.
(a7) First we look at (βF )η?= β. To prove this, we have to show it holds
at each A ∈ A. Using the definitions of horizontal and vertical composition(see Leinster p.30 and p.37), this becomes
βFAηA?= βA
We consider the cocone CFA, which determines βFA. It has vertex Y FAand legs
yi : XAiβAi−−→ Y FAi
Y fi−−→ Y FA
where the family (Ai)i∈I comes from the family of all (fi : FAi → FA)i∈I .We earlier specified that f1 is the identity 1FA, so A1 = A, and Y f1 =Y 1FA = 1Y FA. Therefore the leg y1 is just βA.
We now appeal to the defining property of β, βFAli = yi. For the specialindex i = 1, we have ηA = l1 and y1 = βA, and the equation reads βFAηA =βA, as desired.
We turn our attention to (σF )η?= σ. We must check this at each B ∈ B.
Let β = (σF )η, so:
η : X ⇒ LF σF : LF ⇒ Y F
σ : L⇒ Y β = (σF )η : X ⇒ Y F
We defined βB via the cocones CB and CB, the latter having legs yi =(Y fi)βAi
for each fi : FAi → B. Since βA = σFAηA for all A, we get
yi : XAiηAi−−→ LFAi
σFAi−−−→ Y FAiY fi−−→ Y B

6 ADJOINTS, REPRESENTABLES AND LIMITS 143
It will prove notationally convenient to let A, f , l, and y stand for Ai, fi,li, and yi for some arbitrary i ∈ I. Now suppose we can show that thisdiagram commutes:
XA LFA Y FA Y B
LB
l
ηA
Lf
σFA Y f
σB
The top row is just the leg y in CB, and the left vertical arrow is the leg lin CB. Thus σB would satisfy the defining condition for [(σF )η]B. Conse-quently, our problem is reduced to proving commutativity of the diagram.We do this by showing that the two subtriangles commute.
By hypothesis σ : L ⇒ Y is a natural transformation, so we have thenaturality square
LFA LB
Y FA Y B
σFA
Lf
σB
Y f
so σB(Lf) = (Y f)σFA. So the right subtriangle commutes.
Our definition of Lf , for f : FA → B, involves looking at the coconesCFA and CB; we have a mapping from the first to the second induced by
the mapping from (F ⇒ FA) to (F ⇒ B). Let’s denote by (fk)k∈K the
morphisms coming from (F ⇒ FA): an object of (F ⇒ FA) is
(Ak, fk : FAk → B)
We let lk be the corresponding leg of CFA, so lk : XAk → LA.
The mapping from (F ⇒ FA) to (F ⇒ B) is given by fk 7→ f fk. Denote
the corresponding leg mapping from CFA to CB by lk 7→ lk. (This was

6 ADJOINTS, REPRESENTABLES AND LIMITS 144
denoted li → l′i in (a2).) So we have:
fk : FAk → FA 7→ f fk : FAk → B
lk : XAk → LA 7→ lk : XAk → LB
The lk’s are some of the legs of CB, though perhaps with different multi-plicities (i.e., the index set mapping K → I may not be injective). Recall
also that the nodes XAk are some of the nodes of CB, though again perhapswith different multiplicities.
The defining property of Lf is
lk = (Lf)lk
(In the notation of (a2), this was written l′i = (Lb)li.)
The morphism f has a double role. On the one hand, it’s a part of (F ⇒ B),
since it goes from FA to B. In this role, f corresponds to l of CB. (Recall
that f and l stand for fi and li, for some i ∈ I.) On the other hand, fdetermines the mapping of CFA into CB.
For a particular index k (denote it by 1), we have A1 = A and f1 = 1FA.We then have
f1 = 1FA 7→ f
l1 = ηA 7→ l1 = l
The equation l1 = ηA follows from the definition of η in (a4). Here, l1 is the
leg corresponding to l1 under the mapping lk 7→ lk.
We now apply the defining property for the special index k = 1, and get:
l = (Lf)ηA
as required.

6 ADJOINTS, REPRESENTABLES AND LIMITS 145
(b) Recall that L is an abbreviation for LanFX. So (a) establishes a 1–1correspondence
[B,S](LanFX, Y ) ∼= [A,S](X, Y F )
with the mappings σ 7→ (σF )η going from left to right, and β 7→ β fromright to left. Our use of β is in keeping with Leinster’s notation for adjoints(p.42); Leinster would also write σ for (σF )η.
It’s worth noting that η, as defined in part (a), is the unit of this adjunction,as we see from this diagram. (The top row belongs to [B,S], the bottom to[A,S].)
LanFX LanFX
X (LanFX)F
1L
−◦F
ηX
LanF
It remains to check the naturality diagrams, (2.2) and (2.3), p.42.
(b1) Diagram (2.2):
X Y F Y ′F
LanFX Y Y ′
(σF )η τF
σ τ

6 ADJOINTS, REPRESENTABLES AND LIMITS 146
We have to verify this for each A ∈ A. Noting that τσ = ((τσ)F )η, wecompute:
[((τσ)F )η]A = ((τσ)F )AηA
= (τσ)FAηA
= τFAσFAηA
[(τF )(σF )η]A = (τF )A((σF )η)A
= τFA(σF )AηA
= τFAσFAηA
So (2.2) holds.
(b2) Diagram (2.3):
X ′ X Y F
LanFX′ LanFX Y
ρ β
LanF ρ β
This must be checked for each B ∈ B.
We see that we need to define LanFρ for a natural transformation ρ : X ′ ⇒X; LanFρ will be a natural transformation LanFX
′ ⇒ LanFX. We start bypicking an arbitrary B ∈ B and looking at (F ⇒ B), i.e., at the family (fi :FAi → B)i∈I . Then LanFX
′(B) is the colimit of (X ′Ai)i∈I , and LanFX(B)is the colimit of (XAi)i∈I , subject to the usual triangle conditions. Let’ssay the legs of the colimit cocones are respectively l′i and li. Define ri as thecomposition
ri : X ′AiρAi−−→ XAi
li−→ LanFX(B)

6 ADJOINTS, REPRESENTABLES AND LIMITS 147
The following diagram shows that this is a cocone (where a : Ai → Aj isthe morphism in a triangle condition of (F ⇒ B), as usual):
X ′Ai XAi
LanFX(B)
X ′Aj XAj
ρAi
X′a
ri
Xa
li
ρAj
rj
lj
So there exists a unique
(LanFρ)B : LanFX′(B)→ LanFX(B)
whose defining property is given by the commutativity of this diagram:
X ′Ai XAi
LanFX′(B) LanFX(B)
ρAi
l′i li
(LanF ρ)B
One must check that the (LanFρ)B combine to form a natural transforma-tion, and that LanF is functorial, i.e., LanF (ρρ′) = LanF (ρ)LanF (ρ′). Ileave these verifications as exericises.

6 ADJOINTS, REPRESENTABLES AND LIMITS 148
It remains to check (2.3). Consider this diagram:
X ′Ai XAi Y FAi
LanFX′(B) LanFX(B) Y B
ρAi
l′i
βAi
li Y fi
(LanF ρ)B
(ρβ)B
βB
The left rectangle commutes by the defining property of (LanFρ)B; theright rectangle, by the defining property of βB. So βB (LanFρ)B satisfiesthe defining property of (ρβ)B, i.e., the entire diagram commutes. Thus(ρβ)B = βB (LanFρ)B, and (2.3) is satisfied. So LanF is left adjoint toY 7→ Y F .
(c) In the diagrams
1 Set
G
F
X
Y
G Set
1
F
X
Y
1 is the category with a unique object ∗ and unique morphism 1∗, and Gis G as a 1-object category (Example 1.1.8(c), p.14)—so the elements of Gcorrespond to the morphisms of G. As we know from Examples 1.2.8 and1.3.4 (pp.22 and 29), functors from G to Set are essentially G-sets, andnatural transformations are essentially equivariant maps. Also a functorfrom 1 to Set is basically a set, namely the image of ∗. Let’s write X andY for these sets/G-sets—on the left X is the set and Y is the G-set, on theright vice versa.

6 ADJOINTS, REPRESENTABLES AND LIMITS 149
On the left, the composition Y F takes ∗ to Y and the morphism 1∗ to 1Y .So basically it takes ∗ to the G-set Y stripped of its G-action. In otherwords, Y 7→ Y F amounts to the forgetful functor Y 7→ UY (from G-set toSet).
On the right, Y F is a G-set with underlying set Y and the trivial action.In other words, Y 7→ Y F amounts to the functor Triv from §2.5.
We described the left and right adjoints to U and to Triv in §2.5: F a U aMap and Orb a Triv a Fix. So left and right Kan extensions give all theseadjoints.
Incidentally, Leinster doesn’t spell out what he means by the dual of part(a). We expressed the pivotal step as a 1–1 correspondence between the fi’sand the li’s:
(F ⇒ B) : (fi : FAi → B)i∈I
Colimit cocone : (li : XAi → LB)i∈I
To dualize, we keep the same basic functor triangle of F , X, and Y betweenA, B, and S (see below). However, the fi’s and the li’s are now specifiedby
(B ⇒ F ) : (fi : B → FAi)i∈I
Limit cone : (li : RB → XAi)i∈I
Here R = RanF is the right Kan extension of F . Tracing through theargument of part (a), we end up with diagrams dual to those of part (a):
A S
B
F
X
εR
A S
B
F
X
β β
σ
R
Y

6 ADJOINTS, REPRESENTABLES AND LIMITS 150
We replace η with ε since the unit has become a counit. Note that thenatural transformations reverse direction, the functors don’t. The argumentof part (b) dualizes to show that RanF is right adjoint to Y 7→ Y F .
See also §2.5 and §6.2.
6.10 6.3.21, p.168
Functors with left adjoints preserve limits, and functors with right adjointspreserve colimits (Theorem 6.3.1, p.159).
(a) The trivial group 1 is a zero object of Group, that is, both initial andterminal. U1 is a singleton set, thus a terminal but not an initial object ofSet. Since terminal objects are limits and initial objects are colimits, limitsbut not colimits are preserved for 1 7→ U1. This accords with Theorem 6.3.1,provided that U has no right adjoint. (And note that U has a left adjoint.)
(b) To show that I from §3.4 (Exercise 3.2.16, p.78) has no right adjoint, weneed a colimit in Set that is not preserved by I. As it happens, I preservesthe initial object ∅. But turning to coproducts, i.e., disjoint unions, wehave our example. I(1 + 1) 6= I1 + I1, since I1 + I1 is the discrete categoryon two objects and I(1 + 1) has morphisms in both directions between itstwo objects.
To show that C has no left adjoint, we need a limit in Cat that is notpreserved by C. We use monics (item 10 of §1.11). Let A be the discretecategory on two objects, and let B be the indiscrete category on two objects.We have an obvious functor F : A → B that is the identity on objects andis an inclusion map on morphisms—B is “the same” as A except with twomorphisms added. F is monic because the functor Mor : Cat → Set thatsends a category to its set of morphisms is faithful12, and Mor(F ) is injective
12Note that the functor Ob = O isn’t.

6 ADJOINTS, REPRESENTABLES AND LIMITS 151
(it’s an inclusion map!), and faithful functors pull back monics (item 8 of§1.11). But CA has two elements and CB has one, so CF isn’t monic.
Curiously, C preserves both terminal objects and products, the other two“go to” examples of limits. This is trivial for terminals, and makes a niceexercise for products.
(c) We recall (§2.7, Exercise 2.1.17, p.50) that X is a topological spaceand Presheaf(X) is the category of presheaves on X. Also, the functorΛ is defined thus: for any set A, ΛA(∅) = A, ΛA(Y ) = ∅ for each openset Y 6= ∅, and the morphisms in ΛA are all empty functions except for1A on ΛA(∅). The functor ∇ has ∇A(X) = A and ∇A(Y ) = 1 for eachY 6= X, where 1 is some arbitrary singleton; the morphisms in ∇A are allconstantly 1 functions except for 1A on ∇A(X). Finally, if f : A→ B, thenthe natural transformation Λf is defined by (Λf)∅ = f and (Λf)Y = theempty function for all Y 6= ∅. Likewise, (∇f)X = f and (∇f)Y = 11 for allY 6= X.
We exclude the case X = ∅. Λ does not preserve terminal objects, hencehas no left adjoint. For if A = 1, then ΛA(∅) = 1 and ΛA(Y ) = ∅ for allY 6= ∅, but the terminal presheaf on X clearly must have a singleton valueeverywhere, i.e., if F ∈ Presheaf(X) is terminal, F (Y ) = 1 for all openY ⊆ X. (The 1’s don’t have to be the same for different Y ’s, but sinceall singletons are isomorphic in Set, that doesn’t matter. Note that thisterminal F is actually ∆1. ∆ has a left adjoint and so preserves terminals.)
Similarly, ∇∅(X) = ∅ and ∇∅(Y ) = 1 for all Y 6= X, while the initialpresheaf (namely ∆∅) has the value ∅ everywhere.
If you insist on not excluding X = ∅, then in that case Λ = ∆ = ∇ andΠ = Γ, so we have two functors that are left and right adjoints of eachother, giving a two-way infinite chain.

6 ADJOINTS, REPRESENTABLES AND LIMITS 152
6.11 6.3.22, p.168
(A)⇒(R): Suppose F a U , so we have a bijection A(FX,A) ∼= Set(X,UA)for all X ∈ Set and all A ∈ A. Let 1 be a singleton in Set. So
A(F1, A) ∼= Set(1, UA) ∼= UA
since, as Leinster often points out, we have a natural 1–1 correspondencebetween elements of a set and maps from a singleton into the set. Thecorrespondence is natural inA because of the naturality property of adjoints.
Since A(F1, A) = HF1(A), this gives an isomorphism between the repre-sentable functor HF1 and U .
Observe that we want HF1 and not HF1, as U is covariant.
(R)⇒(L): This is Prop.6.2.2 (p.148).
(b) We want a left adjoint F to U ∼= HA, with A ∈ A. For a snappier proof,we’ll just let U = HA.
Observer first that for any B ∈ A, A(A,B) = HA(B) = UB ∼= Set(1, UB),where 1 as usual is a singleton. This suggests setting F1 = A. An arbitraryX is the sum of its elements, and A has sums by hypothesis, so we let FXbe the sum of copies of F1 = A, one copy for each x ∈ X.
We nail down the details. Make X into a discrete category. In A, ourdiagram is DX : X → A, with the image of each x ∈ X being A. (So DX
is the diagonal usually denoted ∆A.) We choose a colimit cocone for DX
FX, and denote the vertex by FX and the legs by ix:
FX =(x
ix−→ FX)x∈X
So FX is the sum of |X| copies of A. We do this for each set X. Adaptingthe proof of Prop.6.1.4 (p.145) (or §5.17, ex.5.3.8, p.140), there’s a natural

6 ADJOINTS, REPRESENTABLES AND LIMITS 153
way to define Ff for functions f : X → Y in Set: construct a cocone ondiagram DX with vertex FY by letting the x-leg lx : A → FY be if(x).(That is, the leg from A to FY in F Y associated with y = f(x) ∈ Y .13)Since FX is a colimit, there is a unique Ff : FX → FY such that (Ff)ix =if(x) for all x ∈ X. This makes F into a functor.
We now have to define the 1–1 correspondence A(FX,B) ∼= Set(X,UB).Given a : FX → B, for every x ∈ X we define ax = aix : A → B. (Thinkof it as ax : Ax → B.) So ax ∈ HA(B) = UB, and x 7→ ax is a functiona : X → UB. In the reverse direction, given f : X → UB = HA(B),
since f(x) : A → B, we have a cocone (Af(x)−−→ B)x∈X with vertex B.
Since FX is a colimit, there is a unique f : FX → B making thingscommute. The verifications that ¯a = a and ¯f = f , and of the naturality ofthe correspondence, are all routine.
6.12 6.3.23, p.168
(a) Let A be a preordered set; regarded as a category, we have a uniquemorphism A→ B exactly when A ≤ B, and no other morphisms (Example1.1.8(e), p.15). We let ≡ be the equivalence relation A ≡ B iff A ≤ B andB ≤ A, and let A/≡ be the category whose objects are the equivalenceclasses [A] with [A] ≤ [B] iff A ≤ B, obviously independent of the choiceof representatives A and B. Now let F be the mapping A 7→ [A]; for each[A] ∈ A/≡ choose an A ∈ [A], call it GA. It is easily verified that F and Gare functors, and that GF ∼= 1A, FG ∼= 1A/≡. Lemma 1.3.11 (§1.3) makesthis even easier: since A and GFA both belong to [A], we have GF ∼= 1A;FG[A] = [A], so FG ∼= 1A/≡.
13Personally, I like to picture the |X| copies of A in DX as distinct dots Ax, eventhough they’re all the same A; likewise for the Ay’s in DY . Then the legs ix in FX allhave visually distinct sources, likewise for the iy’s in F Y . Finally, think of lx as if(x)1A,where 1A goes from Ax to Af(x).

6 ADJOINTS, REPRESENTABLES AND LIMITS 154
(b) Let i be the cardinality of I. Recall that the diagram ∆B : I → A sets(∆B)i = B for all i ∈ I. There are 2i different cones on ∆B with vertex A,
since in (Ali−→ B)i∈I , we can choose li = f or li = g independently for each
li. Let a : A→ BI be the completing morphism, so li = pia for each i. (Ofcourse, pi : BI → B is the projection to the i-th factor.) So each cone musthave a different a, and there are at least 2i different morphisms A → BI .Therefore A cannot have a set’s worth of morphisms, i.e., is not small.
(c) From (b) we conclude that the category must be a preorder. From (a)we conclude that it is equivalent to a poset. Having all small products isequivalent, for a poset, to having all small meets. I.e., the poset is complete.
(d) All the arguments of (a)–(c) go through with the sole change of replacing“set’s worth” and “small” with “finite”.
6.13 6.3.24, p.169
(a) Every element of subgroup generated by {ga|a ∈ A} can be written as aproduct of ga’s and g−1
a ’s. If we say a letter is a ga or a g−1a (see §2.2), then
the cardinality of the generated subgroup is at most that of the set of allfinite strings of letters. This cardinality is obviously at most max(ℵ0, |A|).
(b) Suppose G is a group with |G| ≤ |S|. So there is an injection f : G→ S,and we can use f to transfer the group structure of G to f(G). That is,there is a group G′ isomorphic to G whose underlying set is a subset of S.
Now consider the collection of all groups whose underlying sets are subsetsof S. Such a group is specified completely by S ′ ⊆ S and its multiplicationtable, which in turn is the set {(x, y, z)|xy = z} and hence a subset ofS ′ × S ′ × S ′. So starting with S, we form the power set, then for eachelement S ′ of the power set we form the power set of S ′×S ′×S ′, and finallywe consider all possible pairs (S ′, T ) where S ′ ⊆ S and T is a multiplicationtable on S ′. By basic set theory, all these are sets.

6 ADJOINTS, REPRESENTABLES AND LIMITS 155
(c) The comma category (A ⇒ U) consists of all pairs (G, f : A → UG),where G is a group and f is a function from A to UG. In other words,elements of (A ⇒ U) are groups G with the set A “dropped into” G.Something like a pointed set, except that instead of distinguishing just oneelement, we’ve “labeled” an element of G for every a ∈ A. I’ll call f alabeling, and (G, f : A → UG) a labeled group. (§2.15 introduced thisterminology.)
For any labeled group, the subgroup generated by the labeled elements(call it G′) has cardinality at most max(ℵ0, |A|) (by (a)). Let S be a set ofcardinality max(ℵ0, |A|); it follows that for any labeled group G, there is agroup H with UH ⊆ S and with H isomorphic to the generated subgroupG′. So there is a monomorphism H → G; moreover, we can obviouslytransfer the labeling of G over to H, i.e., there is an h : A → UH makingthe obvious diagram commute. So (H, h : A → UH) belongs to (A ⇒ U),and there is a morphism in (A ⇒ U) from the labeled group (H, h) to thelabeled group (G, f).
Slightly extending part (b), we see that the collection of all labeled groups(H, h) with UH ⊆ S is a set; we have a set’s worth of H’s with UH ⊆ S, andfor each such H, a set’s worth of labelings h : A → UH. So the collectionof all such (H, h) is a weakly initial set for (A⇒ U).
(d) All the GAFT hypotheses hold: Group is locally small, small complete,and the forgetful functor U : Group→ Set preserves limits14. So U has aleft adjoint, the free group functor.
(e) Let’s compare this construction of the free group functor with the secondone given in §2.2, the “subgroup of a direct product”; I’ll call this the Titsconstruction, after a remark in Lang [5, p.66] that suggests he invented it.Several points of comparison leap out. The Tits construction begins with
14The last two facts fall out from §§5.20&5.21 (Exercises 5.3.11 and 5.3.12, p.140;5.3.12 is the same as Lemma 5.3.6, p.139). Set has all small limits and U creates limits,so Group has all small limits and U preserves them.

6 ADJOINTS, REPRESENTABLES AND LIMITS 156
a set S of cardinality max(ℵ0, |A|), then looks at the set {Gi|i ∈ I} of allgroups whose underlying sets are subsets of S, and then for each i looks atall possible mappings f : A→ UGi, making a copy Gif of Gi for each suchf . So the set {Gif} is really just the weakly initial set we constructed inthe category (A⇒ U).
The next step in the Tits construction: form the product G =∏
i,f Gif .The free group FA is not G, but the subgroup H generated by η(A), whereη : A→ UG is defined by η(a)if = f(a). So it’s a restricted subgroup of G.Let’s see how the product enters in the proof of GAFT.
Lemma A.1 (p.172) sits at the heart of GAFT: a complete locally smallcategory with a weakly initial set has an initial object. The proof of GAFTapplies this to the category (A⇒ U). A moment’s thought reveals that aninitial object of (A⇒ U) is a free group: (FA, ηA : A→ UFA) is initial iffFA satisfies the desired universal property.
The initial object is constructed as a limit cone (eq.A.1, p.172, adjustingnotation to dovetail with our discussion):(
FApif−→ Gif
)i,f
Now, limits in Group are computed via eq.5.16 (p.121, Examples 5.1.22and 5.1.23) as an equalizer of a product. In this case:
FA = {(xif )i,f |xif ∈ Gif ∀i, f and u(xif ) = xjg ∀Gifu−→ Gjg} (5)
In other words, the limit is the subgroup of the product G =∏
i,f Gif
subject to a bunch of a constraints, namely
u(xif ) = xjg whenever u : Gif → Gjg (6)
We’ve now reached the point where the Tits and GAFT constructions bothserve up subgroups of
∏i,f Gif ; we need to compare the constraints defining
the subgroups. First, GAFT. The u’s in eq.6 are all the homomorphisms

6 ADJOINTS, REPRESENTABLES AND LIMITS 157
that respect labels: u(f(a)) = g(a) for all a ∈ A. (That’s part of thedefinition of morphisms in (A ⇒ U).) Next, Tits. The subgroup H isgenerated by η(A), where η : A→ UG is defined by η(a)if = f(a). Observethat each element of η(A) satisfies all the constraints of eq.6, because theu’s respect labels, and η(a)if = f(a), η(a)jg = g(a). The same is thus trueof the subgroup generated by η(A), because the u’s are homomorphisms.So H is a subgroup of the GAFT group FA of eq.5. (In fact it’s equal toit—we’ll see that soon.) So the Tits construction enforces all the constraintsof eq.6, though indirectly.
Let’s say that Gif dominates Gjg if there is a label-respecting homomor-phism u : Gif → Gjg. If Gif dominates Gjg, then we can throw out the jgcomponent of tuple (xkh)k,h—it’s completely determined by the if compo-nent! In other words, the projection of FA to the product of the undomi-nated Gif ’s is an isomorphism.
Once we know that there is a free group with the required universal property,we are ready for the punchline: there is exactly one undominated Gif !Suppose F is free over A with labeling e : A → F . It’s easy to see thatthe subgroup generated by e(A) also has the universal property, so |F | ≤max(ℵ0, |A|). So there’s a copy of F among the Gif ’s, and it dominatesevery other Gif by the universal property. It follows readily that the Titsgroup H is identical to the GAFT group FA.
§A.4 opines on this and another application of GAFT.

A PROOF OF GAFT 158
A Proof of GAFT
A.1 A.3, p.173
(a) First note that (0uB−→ B)B∈B is a cone on the identity diagram, where
uB is the unique morphism from 0 to B. The commutativity conditionshold because uB is unique. Observe that u0 = 10.
Next, let (VlB−→ B)B∈B be a cone on the identity diagram, so for any
morphism f : A → B we have flA = lB. In particular, setting A = 0 (so
f = uB) we have uBl0 = lB. For (0uB−→ B)B∈B to be a limit cone, we need a
unique g : V → 0 with uBg = lB for all B. We’ve just seen that uBl0 = lBfor all B, so we can set g = l0; this is the only possible choice, as we see bysetting B = 0 in uBg = lB and remembering that u0 = 10.
(b) We have fpA = pB for any f : A → B, so setting A = L and f = pB,we have pBpL = pB for all B. Now we apply the universal property of limitcones, with both cones being (L
pB−→ B)B∈B. Both 1L and pL can serve asthe unique mediating morphism g, i.e., the g that satisfies pBg = pB for allB. So pL = 1L.
Now pick an arbitrary B, and look at the set of all f : L → B. These allsatisfy fpL = pB, or since pL = 1L, f = pB. In other words, for all B thereis a unique morphism from L to B; thus L is an initial object.
A.2 A.4, p.173
(a) (∀x ∈ C)(∃s ∈ S)s ≤ x.
(b) Let m =∧s∈S s. By the definition of meet, (∀s ∈ S)m ≤ s, so for any
x ∈ C, we have m ≤ s ≤ x for some s ∈ S. So (∀x ∈ C)m ≤ x, thus m isthe least element of C.

A PROOF OF GAFT 159
A.3 A.5, p.173
(a) The picture below illustrates the case where I is the category 1 → 2,i.e., we have two objects and a unique morphism from 1 to 2. The diagram
E : I→ B then has two objects with a morphism, B1f−→ B2, and G ◦E has
GB1Gf−→ GB2:
G ◦ E E
A GB1 B1
GB2 B2
a1
a2Gf f
The objects in (A⇒ G) are the pairs (B1, a1) and (B2, a2), and the defini-tion of morphism in (A⇒ G) says that (Gf)a1 = a2, so we have a cone onG ◦ E.
The general case is no different, just lots of these pictures glued together.
(b) To avoid drawing a messy and confusing picture, I will impose uponthe reader’s powers of visualization. Imagine that the B2 in the previouspicture is replaced with a swarm of B2’s (i.e., a diagram in B), and that B1
(with attendent f ’s) is the limit cone.
The (strict) definition of “creates limits” starts with a diagram in (A⇒ G),in other words, just with the diagram of B2’s and the a2’s from A to theGB2’s, forming a cone in A with vertex A. Applying the projection PA givesus the diagram of B2’s in B. As said, we now assume that B1 is the vertex ofa limit cone E in B with the legs being the f ’s. Apply the limit-preservingfunctor G gives us a limit cone G ◦ E in A, with limit GB1.
Because G ◦ E is a limit cone with vertex GB1, and the a2’s are the legsof a cone on the same base with vertex A, there is a unique a1 : A→ GB1

A PROOF OF GAFT 160
making everything commute. The whole commuting shebang—vertex A,morphism a1, GB1, all the GB2’s, all the a2’s and all the Gf ’s—is a limitcone in (A ⇒ G) with vertex (B1, a1). It’s unique because a1 is uniquelydetermined once we know B1, and B1 is determined by the choice of limitcone in B. So we’ve lifted the limit cone in B uniquely to a limit cone in(A⇒ G).
A.4 Another Application of GAFT: Hausdorffification
In Example 6.3.11, Leinster sketches the usual free group construction, andremarks, “But using GAFT, we can avoid these complications entirely.”Here he echoes Mac Lane’s comment [4, p.123], “[O]ur theorem has pro-duced this free group without entering into the usual (rather fussy) explicitconstruction of the elements of FX as equivalence classes of words in lettersof X.” I invite the reader to look at the standard construction as sketchedat the beginning of §2.2. Compare this with all the ingredients to the GAFTproof: the proof of GAFT itself, the verification that the comma categorieshave weakly initial sets, and the verifications that U creates limits and thatSet has them. Now say which is less complicated, more understandable,and better motivated.
At least Leinster hasn’t drunk all the Kool Aid. He also says, “The priceto be paid is that GAFT does not give us an explicit description of freegroups”.
So thumbs down on this application as a justification for GAFT.
Am I saying the GAFT isn’t cool? On the contrary—the GAFT is verycool. And the notion of adjoint functor is way cool. One is almost temptedto resuscitate 60s slang to say how cool it is.
What makes the idea of adjoint functor so groovy is the way it sweeps upsuch disparate constructs into a single bag: free groups, universal envelop-

A PROOF OF GAFT 161
ing algebras, Stone-Cech compactifications, and so much else. That oneexistence theorem covers all these situations—that’s the ice cream on thepie. But in any concrete instance, you’re likely to find a tailored existenceproof more understandable and glean more insight from it.
Here’s another illustration: Hausdorffification. Let U : Hausdorff → Topbe the forgetful functor. We saw at the end of §5.21 that Hausdorff is com-plete and that this U preserves limits. To show that U has a left adjoint H(the Hausdorffification functor) we have to verify the remaining hypoth-esis of GAFT. The category (A⇒ U) consists of pairs (X, f : A→ UX), inother words, maps from a fixed topological space A to an arbitrary Haus-dorff space X. We can always factor f : A → UX as A → f(A) → UX,and we can replace f(A) with any space homeomorphic to it. Since thecardinality of f(A) is at most |A|, we just have to pick a fixed set S ofcardinality |A| and consider all possible Hausdorff topologies on all possiblesubsets of S. This is clearly a set. So (A ⇒ U) possesses a weakly initialset, and GAFT applies.
Here are two other constructions, both more concrete. Let X be a topo-logical space, and say x ∼ y if x and y cannot be separated by disjointopen sets. Since ∼ might not be transitive, let ≈ be the transitive closureof ∼. Let h : X → h(X) be the quotient map. (Let’s call this “the hconstruction”.)
Now, h(X) possesses the desired universal property. Proof: suppose f mapsX to a Hausdorff space Y. We will show that x ≈ y implies f(x) = f(y).This will do the trick, because it means that f maps each equivalence classto a single element of Y ; this makes it obvious that there is a unique functionf : h(X)→ Y such that f = fh. Furthermore f is continuous because h(X)has the quotient topology. The implication x ≈ y ⇒ f(x) = f(y) followsfrom the same implication for ∼, since ≈ is the smallest equivalence relationcontaining ∼, and f(x) = f(y) is an equivalence relation between x and y.We prove this last implication in contrapositive form. Suppose f(x) 6= f(y).Since Y is Hausdorff, there are disjoint open sets U and V around f(x) and

A PROOF OF GAFT 162
f(y). Then f−1(U) and f−1(V ) are disjoint open sets around x and y. Sox 6∼ y.
Hence if h(X) is Hausdorff, then it’s the Hausdorffification of X. But h(X)might not be Hausdorff! Example: start with any Hausdorff space S (e.g.,the real line) and any sequence sn in S converging to an element s. LetX have S as its underlying set but with a coarser topology. Sets are openin X iff they are open in S and they include either all the sn’s or none ofthem. So si ∼ sj for all i and j, but si 6∼ x for any x that is not an sj. The≈-equivalence classes are easy to describe: all the si’s are in one class andevery other x is in a singleton class by itself (since S was Hausdorff). Soall the si’s map to a single element of h(X) and s, in particular, maps to adifferent element. Because sn → s, these two elements cannot be separatedby disjoint open sets.
We proceed via transfinite induction, defining an ordinal sequence of equiv-alence relations ≈α on X and quotient maps hα : X → Xα. We startoff with ≈0 being equality. We define ≈α+1 in terms of ≈α: x ≈α+1 y iffhα(x) ≈ hα(x), where ≈ is the result of applying the h construction toXα. For a limit ordinal λ, define x ≈λ y iff x ≈α y for some α < λ (withx, y ∈ X). Note that each each equivalence relation is a coarsening of allthe previous ones: x ≈α y implies x ≈β y for any α < β.
All the ≈α relations enjoy the same property as ≈: if x ≈α y, then f(x) =f(y) for any f mapping X to a Hausdorff space. This follows by transfi-nite induction. If x ≈α+1 y then hα(x) ≈ hα(y) (definition) which impliesf(hα(x)) = f(hα(y)), where f is the unique map such that f = fhα. Sof(x) = f(hα(x)) = f(hα(y)) = f(y). For a limit ordinal, if x ≈λ y, thenx ≈α y for some α < λ, so f(x) = f(y).
There exists a σ such that ≈σ and ≈σ+1 are the same. Proof: the numberof different equivalence relations on X is at most 2|X|
2(each equivalence
relation is a set of ordered pairs). So there must be a σ < τ with ≈σ and≈τ the same, and hence (since each ≈α is a coarsening of all the previous

REFERENCES 163
equivalence relations), ≈σ equals ≈σ+1. So hσ(X) is Hausdorff, and by whatwe’ve already shown, it has the required universal property.
Now for the second construction. Define x ≡ y iff x ≈ y for every equiva-lence relation ≈ such that X/≈ is Hausdorff. First we prove the universalproperty. Suppose x ≡ y and f maps X to a Hausdorff space Y . Therelation f(x) = f(y) is an equivalence relation on X, call it ≈f , and X/≈fhas an obvious injection into Y , continuous because X/≈f has the quotienttopology. So X/≈f is Hausdorff. So x ≡ y implies x ≈f y, i.e., f(x) = f(y).
Next we show that X/≡ is Hausdorff. Suppose x 6≡ y. By definition then,x 6≈ y for some ≈ with X/≈ Hausdorff. Note that each ≈-equivalence classis a union of ≡-equivalence classes. This gives us a factorization of thequotient map q : X → X/≈ into X
e−→ X/≡ p−→ X/≈, e and p being quotientmaps. Since x 6≈ y, we have q(x) 6= q(y), so there are disjoint open sets Uand V around q(x) and q(y). It follows that p−1(U) and p−1(V ) are disjointopen sets around e(p) and e(y). But e(p) and e(y) are arbitrary distinctelements of X/≡. QED
References
[1] Adamek, Herrlich, and Strecker. Abstract and Concrete Categories:The Joy of Cats. John Wiley and Sons/Open Access, online edition,2004. Available at http://katmat.math.uni-bremen.de/acc.
[2] George M. Bergman. An Invitation to General Algebra and UniversalConstructions. Springer Science, 2nd edition, 2015.
[3] Paul M. Cohn. Universal Algebra. D. Reidel Publishing, revised edition,1981.
[4] Saunders Mac Lane. Categories for the Working Mathematician.Springer, 2nd edition, 1978.

REFERENCES 164
[5] Serge Lang. Algebra. Springer-Verlag, revised 3rd edition, 2002.
[6] Tom Leinster. Basic Category Theory. Cambridge University Press,2014. Available at https://arxiv.org/abs/1612.09375.
[7] Carl Linderholm. A Group Epimorphism is Surjective. American Math-ematical Monthly, 77(2):176–177, February 1970.
[8] James R. Munkres. Topology. Prentice Hall, 2nd edition, 2000.
[9] Ivan Niven. Irrational Numbers. Mathematical Association of America,1956.
[10] Michal R. Przybylek. The Other Pullback Lemma. arXiv, October2014. https://arxiv.org/abs/1311.2974.
[11] Peter Smith. Category Theory: A Gentle Introduction. self. Availableat http://www.logicmatters.net/resources/pdfs/GentleIntro.pdf.