Ethical Hacking Framework
-
Upload
german-delgadillo -
Category
Documents
-
view
217 -
download
0
Transcript of Ethical Hacking Framework
-
8/3/2019 Ethical Hacking Framework
1/1
AU1609_
Tip8/18/043:51PMPage1
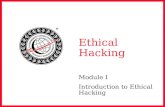
Business
Objectives
Overall
Expectation
ThreatType
AttackType
Required
Knowledge
Imposed
Limitations
Policy
Inherent
Limitations
WhiteTeam
Social
Eng.
Intranet
Data
Dumpster
Diving
e-Mail
HelpDesk
Fraud
Identity
Assumption
People
Fraud
Theft
P
rowling/
Surfing
Internet
Sources
WarDriving
Physical
Security
Domain
Data
News
Groups
Internal
Relations
Observation
Website
Ping
Sweeps
Initial
Discovery
Scans
PhoneLists
Network
Map
Manuals&
Policies
Passwords
Script
Kiddie
Hacker
Uber
Hacker
Input/Output
Initial
Deductions
Partner
Data
War
Chalking
Access
Badges
Network
Map
Account
Data
IP
Addresses
Domain
Information
Password
Change
Partner
Information
Known
Applications
Operating
Systems
Custom
Applications
Phone
Systems
Wireless
Network
Organizational
Structure
Miscellaneous
Data
Incidents
Security
Alerts
Information
Collection
Vulnerablity
Reports
Patches&
Service
Packs
Default
Passwords
Default
Installation
Internet
Vendor
Input/Output
Input/Output
Obtained
Protocol
Standards
White
Team
FeedbackLoop
Network
//
AttackPlan
Thread-1
Windows
Attacks
*nix
Attacks
Web
Attacks
Internet
Intranet
Extranet
Initial
Results
Results
Analysis
Final
Analysis
Expected?
Expected?
QualityLoop
Overall
Expectation
Allresultsmust
beevaluated
against
established
expectationsprior
toprogression
Yes
Yes
No
White
Team
BlueTeam
Deliverable
Integrate
Critical
Warning
Informational
Remedial
Tactical
Strategic
Policy
Mitigation
Test
Pilot
Implement
Validate
Incident
Management
Detect
Identify
Isolate
Erradicate
Defense
Planning
Architecture
Review
Process
Review
Awareness
Existing
Policy
RiskAnalysis
Security
Program
Previous
Test(s)
Business
Type
Teams
RedTeam
SourceFilter
Thread-2
Thread-n
Operating
System
Application
Network
Services
Citrix/X
ACL/FW
SNMP
RMON
Wireless
RAS/
Extranet
FTP/Telnet
HTTP/
SMTP
Custom
Nodes
Mis
c.
Protocols
Appliance
Attacks
Thread
Results
Tools
Group-n
BlueTeam
Logistics&EngagementPlan
No
PLAN
RECONNAIS
SANCE
ENUMERATE
A
NALYSIS
ATTACK
DELIVERABLE
RESULTS
INTEGRATE
Co
llec
tan
dDe
fine:
Leverageexisting
informationsecurityrelated
data,combinewithoverall
businessobjectivesand
establishexpected
outcomeoftest.
Threa
ts
an
dLimita
tions:
Evaluateknownthreats,tactics
andstructureandcompareto
existingin
formationand
expectatio
nstodeviseanattack
type,profileofrequired
knowledge,andimposed
limitations
Managemen
t:Create
teams,provideoperational
andcommunication
protocols,andcreate
metricstoensureclear
measurementofsuccess
orfailurefactors
Learnan
dUse:Basedontheleveland
scopeofrequiredknowledge,thecreationofan
informationandproposedcollectiontacticmatrix
shouldbeusedtoacquireinformationaboutthe
target.Intensityandscopearedefinedbythe
businessobjectivesandthreattype,whichin
turnwillestablishtherolecollecteddataplaysin
theremainderoftheengagement
Ra
tiona
lize:Dependingonthetactic,depth,
provideddata,timeframe,andoverall
vu
lnerabilityofthetargetortheamountoffreely
av
ailableinformation,alldatacanbenormalized
andcomparedtoseekotheropportunitiesto
gaininformationpriortomovingintothenext
phase
Direc
tTec
hn
ica
lInves
tiga
tion:
Byusing
varioustoolsandspecificinformationcollected
fromthepreviousphase,systems,networks,
services,andapplicationscanbequeriedto
gatherempiricaldataoncharacteristicsthatcan
beusedforanattackvector
Vu
lnera
bility
Ana
lys
is:Datafromthe
Internet,productvendorsandeventhetarget
arereviewe
dforanydocumentedalignment
toavulnerability
Attac
kStra
tegy:Basedonthe
informationlearnedaboutthetarget,
overallobjectives,expectations,
limitations,andrestrictionsanattack
plancanbeformulated.Thedatawill
promotetheuseofonesourcepoint
overanother,oranycombinationofthe
threeprimarytypes
Qua
lityLoop:Withoutareview
oftheinitialthreadresultsthereisa
greaterpossibilitytoloosing
valuablevulnerabilityinformationor
affectingthevalueofthetestbased
onpoorvalidationofavulnerability
thread
Groups
ofThrea
ds:Threads
representasingularityofattack
thatcanbecombinedtorepresent
thetotalimpactofacollectionof
threadso
rvulnerability.Multiple
groupsre
presentawebof
vulnerabilitiesfoundedontechnical
aswellasmanagement
vulnerabilities
Always
Comparean
dRev
iew:
ReviewThreadandGroupdataand
combinetoformulateotherattackscenarios
iftimepermits.Additionally,evaluateresults
againstexpectationsandagreedupon
tactics.Ifgroupresultsanalysiscontinueto
notmeetexpectations,youneedtoreview
theexpectationsofthetestotherwiseyou
willnotbepreparedfortheresults
RiskisKey:Theonlymethodfor
ensuringausableengagementdocumentis
toalignwithexistingsecuritypolicy,
understandingofrisk,andoverall
expectations(i.e.comparisonofvalueof
testtothevalueofdata).Definea
interpretationtableandprioritizebasedon
businessdemands,risk,andtime
FixW
ha
tisBro
ke:
Based
onthetests
prioritizedresults,thefirst
orderofbusinessisto
addresstheremedial,
riskreducingelements
Se
tup
for
Long-term
ROI:
Developaclearoperationaland
managementstructureto
supportfullintegrationof
securityrecommendations,
establishanInformationSecurity
ManagementProgram,and
prepareforthenexttest
Response:Developingan
incidentresponseplanwillbe
oneofthefewinvestments
thatgetbetterwithtime.
Create,evaluate,andtesta
responseplan,document
resultsandexpectations,and
preparefortherealthing
Startsw
itha
Po
licy:Fullyunderstandingthesecuritypolicyofanorganizationiscriticalto
theinterpretedvalueofanysecurityproje
ct.
En
ds
witha
Po
licy:Fullyintegratingtheresults,expectationsforfuturesecurity
endeavorsbasedonthetest,andoverallobjectivesintothesecuritypolicyisessentialto
forvaluerealizationandbetterROIonfuturetest
RedTeam
Information
Rationalization
Input/Output
Input/Output
Input/Output