Enterprise Information Systems Security: A Case Study in the Banking Sector
-
Upload
confenis-2012 -
Category
Business
-
view
2.619 -
download
1
description
Transcript of Enterprise Information Systems Security: A Case Study in the Banking Sector

ENTERPRISE INFORMATION
SYSTEMS SECURITY: A
CASE STUDY IN THE
BANKING SECTOR
SEPTEMBER 20TH, 2012 CONFENIS - GHENT, BELGIUM
Sohail Chaudhry, Peggy Chaudhry, Kevin Clark and Darryl Jones
Villanova School of Business, Villanova, PA USA

Agenda
Introduction
Research Approach
Conceptual Model
Phase I – Banking Sector
Results
Future Research

Current Events

Have you had any cases of insider sabotage or
IT security fraud conducted at your workplace?
Source: Cyber-Ark Snooping Survey, April 2011, p. 3.

Research Approach
Focus: Enterprise Information Systems
Security – Internal threats.
Literature Review & Development of Model.
Phase 1: Model tested via personal interviews
of 4 senior information officers in a highly
regulated industry – the Banking Industry.

Information Security Officers Interviewed
Bank A
• Public 100 Years
• 1.1 Bil USD Assets
• 11 Branches
Bank B
• Private, 70 years
• 20 Mil USD in Assets
• 2 Branches
Bank C
• Private, 15 years
• 1.8 Bil USD in assets
• 13 Branches
Bank D
• Private, 8 years
• 550 Mil USD in assets
• 10 Branches

Federal Financial Institutions Examination Council (FFIEC)
Security Process (e.g., Governance issues)
Information Security Risk Assessment (e.g., steps in gathering information)
Information Security Strategy (e.g., architecture considerations)
Security Controls Implementation (e.g., access control)
Security Monitoring (e.g., network intrusion detection systems)
Security Process Monitoring and Updating

The Gramm-Leach-Bliley Act
Access controls on customer information systems
Access restrictions at physical locations containing customer information
Encryption of electronic customer information
Procedures to ensure that system modifications do not affect security.
Dual control procedures, segregation of duties, and employee background checks
Monitoring Systems to detect actual attacks on or intrusions into customer information systems
Response programs that specify actions to be taken when unauthorized access has occurred.
Protection from physical destruction or damage to customer information

Conceptual Framework
Enterprise Information System Security
Security Policy
Security Awareness
Access Control
Top Level Management
Support
Corporate Governance
Implementation

Pillar 1: Security Policy
Set rules for behavior
Define consequences of violations
Procedure for dealing with breach
Authorize company to monitor and investigate
Legal and regulatory compliance

“Information Security Policy is not an option, it’s demanded from the top of the house on down, it’s board approved, accepted by regulators, and executed throughout the organization. ”
Excerpt from interview:

Pillar 2: Security Awareness
Continued education
Collective and individual activities
Formal classes, emails, discussion groups
Employee compliance

“In training, we tell employees
that we are tracking them,
when we are not. It’s a
deterrent. The fact is we have
to use implied security in
addition to actual security. ”
Excerpt from interview:

Pillar 3: Access Control
Limit information
Access linked to job function
Restrict information not relevant to position
Management of access rule changes

Have you ever accessed information on a system that was not relevant to your role?
EMEA % US % C-Level %
Yes 250 44% 243 28% 21 30%
No 313 56% 616 72% 50 70%
Grand Total 563 100% 859 100% 71 100%
Source: Cyber-Ark Snooping Survey, April 2011, p. 2.

Do you agree that majority of recent security attacks have
involved the exploitation of privileged account access?
Source: Cyber-Ark 2012 TRUST, SECURITY & PASSWORDS SURVEY, June 2012
64% 12%
24%
Agree
Disagree
Not Sure

Pillar 4: Top Level Management Support (TLMS)
Transparent support for policies and procedures
Engrain information security into company culture
Effective Communications

“IT governance is a mystery to key decision-makers at most companies and that only about one-third of the managers’ surveyed understood how IT is governed at his or her company.”
Source: Weill, P., and Ross, J., “A Matrixed Approach to Designing IT Governance,” Sloan Management Review, 46(2), 2005, p. 26.

Phase 1 – The Banking Sector

Results
Overall, the Information Security Officers
confirmed the main issues proposed in the
conceptual model.
The four pillars, security policy, security
awareness, access control, and TLMS were
rated as extremely important for each of the
interviewees.

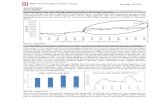
Interview Content Analysis – Agreement

Interview Content Analysis - Dissonance

Future Research
Phase II
Developing and administering a survey to a
larger sample.
Seeking advice on potential sponsorship,
professional affiliations that may be interested
in working with us.

Thank You!
Dankje!
Merci!
Danke!