End-to-End Methodology. Testing Phases Reconnaissance Mapping Discovery Exploitation Repeat… ...
-
Upload
daniella-blankenship -
Category
Documents
-
view
220 -
download
0
Transcript of End-to-End Methodology. Testing Phases Reconnaissance Mapping Discovery Exploitation Repeat… ...

ANATOMY OF A WEB PEN TEST
End-to-End Methodology

Testing Phases
Reconnaissance Mapping Discovery Exploitation Repeat… Report

Reconnaissance
Whois records Architecture diagrams IPs and Hostnames DNS information Google Searches Social Networks Blogs and Other Web Sites

Whois[laa@lobo ~]$ whois generalstatics.com[Querying whois.verisign-grs.com]domain: generalstatics.comowner: Neale Pickettorganization: WoozleWorksemail: [email protected]: 2175 35th Stcity: Los Alamosstate: NMpostal-code: 87544country: USphone: +1.5055004666admin-c: CCOM-411473 [email protected]: CCOM-411473 [email protected]: CCOM-411473 [email protected]: ns1.afraid.org
contact-hdl: CCOM-411473person: Neale Pickettorganization: WoozleWorksemail: [email protected]: 2175 35th Stcity: Los Alamosstate: NMpostal-code: 87544country: USphone: +1.5055004666
source: joker.com live whois service

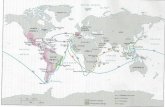
Architecture Diagram

Mapping Port scans Version Checking OS Fingerprinting Spidering Pieces/flow of the application
User/admin/public areasLogin screensConfiguration and ManagementSession identifiers
Learning the various components that make up a web application

Network Scan

Discovery
Focus is on finding issues User interfaces Information leakage Authentication systems Error messages Some exploitation will happen as part of
this stepDirectory browsing

Directory Browsing

Exploitation
Attacking the flaws in an applicationInjectionXSSAuthentication/Authorization bypass
Determine implications of an attackWhat can happen as a result…
What other parts of the application infrastructure are exposed through the attack?

Repeat…
Some knowledge of the application may be gained that wasn’t found in the Recon, Mapping, or Discovery phases
Jump back into the workflow, utilizing the newly discovered information

Reporting Documentation for Reporting is collected
during all phases Executive Summary
Appears first, but written lastAudience is management
IntroductionScope, objectives, personnel
MethodologyStep-by-step, including tools usedSufficient detail to allow verification and repeat of
test

Reporting (2)
FindingsCategorized according to riskInclude recommendations
ConclusionsShort summaryLike Executive Summary, but audience is
technical Appendix
Permission memo, data discovered, tools outputs