Efficient program for decoding the (255, 223) Reed-Solomon code over GF (28 ) with both errors and...
Transcript of Efficient program for decoding the (255, 223) Reed-Solomon code over GF (28 ) with both errors and...

Efficient program for decoding the (255,223)Reed-Solomon code over GF (28) with both errors and
erasures, using transform decodingR. L. Miller, Ph.D., T.K. Truong, Ph.D., and Prof. I.S. Reed, Ph.D., C.Eng., Fel.I.E.E.E.
Indexing terms: Codes and decoding, Fourier transforms
Abstract: To decode a (255, 223) Reed-Solomon code over CF(28), a fast Fourier-like transform overCF(28) has been developed to compute the syndromes and the error-erasure vectors of the transmitted codewords. This new simplified transform decoder is implemented in a program on a digital computer. The(255, 223) Reed-Solomon code over GF(2a) is being proposed as a NASA standard for concatenation witha (7, y) conventional code. In a simulation, random code words were corrupted by random error and erasurepatterns, and decoded whenever theoretically possible. A matrix of execution times for this new transformdecoder under varying sets of errors and erasure patterns is included in the paper. This matrix demonstratesthat the speed of the new decoder is between three and seven times faster than the software R-S decoderdeveloped previously by NASA.
1 Introduction
Recently the authors developed a simplified algorithm2
for correcting erasures and errors of R—S codes over thefinite field GF(pm), where p is a prime and m is an integer.For a space-communication application it was shown3
that a 16-error-correcting R-S code of 255 8-bit symbols,concatenated with a k = l, rate = 1/2 or 1/3, Viterbidecoded convolution^ code, can be used to reduce thesignal/noise ratio required to meet a specified bit-error rate.Such a concatenated code is being considered for theGalileo project, the International Solar Polar Mission, andthe NASA end-to-end data system.
In a concatenated code, the inner convolutional decoderis sometimes able to find only two or more equally probablesymbols. For such a case, the best policy is to declare anerasure of the symbol. If the outer R—S code is able toutilise the additional information that certain erasures haveoccurred, then system performance will clearly be enhanced.
The algorithm given in Reference 2 is used here tocorrect patterns of t errors and s erasures of the words ofthe (255, 223) R-S code, where It + s < 33 and where thesymbols belong to the finite field GF(28). Define thefollowing five vectors:
(co,Ci, . .. , C254) = c, code vector
(r0, rx, . . . , ^254) - —••r> received vector
(ju0, Mi, • • • , M254) = », erasure vector
(e0, ex, . . . , = e> e r r o r vector
(/To, /Tj, . . . , 1 254) = ~, new erasure vector
These vectors are related by r = c + M + e and \x = e + MSuppose that t errors and s erasures occur in the received
vector r of 255 symbols, and assume 2f + s < 3 3 . Then
Paper 81 IE, first received 19th December 1979 and in revised form12th May 1980.Dr. Miller and Dr. Truong are with the Communication SystemsResearch Section, Jet Propulsion Laboratory, Pasadena, California91103, USA, and Professor Reed is with the Department ofElectrical Engineering, University of Southern California, LosAngeles, California 7007, USA
136
following the algorithm in Reference 2 the decodingprocedure consists of these five steps:
(i) Compute the syndromes 5^(1 < A: < 32) of thereceived 255-tuple (r0, rlt ..., r i.e.
254
sh = riai k for k = 1,2,. . . ,32 (1)1=0
where a is an element of order 255 in GF(28). If Sk = 0for 1 < k < 32, then r is a code word and no further decodingis necessary. Otherwise,
(ii) Compute TJ for / = 0, 1, 2, . . . , s from the erasurelocator polynomial
r(x) = Tl (x-Zj) = (2)
where s is the number of erasures in the received vector,and Zj(\ < / < s ) are the known erasure locations. Nextcompute the Forney syndromes T{ for 1 < i < 32 — s fromthe equation
= I (" 1) f o r < » " < 3 2 - s > (3)y=o
where ry(l < / < s) and Sj(l < / < 32) are known.(iii) If 0 < 5 < 3 2 , then use continued fractions4 to
determine the error locator polynomial o(x) from theknown r | s (1 < / < 32 — s). For the special case s = 32, itwas shown5 that it is impossible for any decoder to tellwhether there are zero or more additional errors. Thus, fors — 32, the best policy is not to decode the message at all.
(iv) Compute the combined erasure and error locatorpolynomial from the equation
s + t
T(X) = O(X)T(X) = t-k (4)
IEEPROC, Vol. 127, Pt. E, No. 4, JULY 1980
0143-7062/80/04 0136 + 07 $01-50/0

where o(x) and r(x) are now known. Then compute therest of transform of the erasure and error vector from theequation
s+t
s. - 1 (- for / > 3 2
Note that S25s =S0.(v) Compute the inverse transform of the syndrome
vector (So, Sit . . . , 5254) to obtain the error-erasurevector. That is, calculate
254u-ik for z = 0, 1,2, . . . , 2 5 4
(5)
Finally subtract the error-erasure vectorreceived vector to correct it.
Previously the authors1 implemented the above decod-ing procedure on the Univac 1108 computer. The disad-vantage of this program was that the syndromes in step (i)were computed directly instead of using FFT-like tech-niques. Also, the slower Chien-type search was used to findthe roots of the error polynomial instead of steps (iv) and(v), above. Finally another direct inverse transform of thesyndrome vector was used to obtain the error and erasuremagnitudes.
It was shown6 that a combination of the Chineseremainder theorem and Winograd's algorithm7'8 could beused to develop a fast algorithm for computing thesyndromes needed for decoding an R—S or BCH code.Such a method requires only a small fraction of the numberof multiplications and additions that are required in a directcomputation. More generally, it was shown also in Refer-ence 9 that a modification of Winograd's method could beused to compute (2m — l)-point transforms over GF(2m),where m = 4, 5,6, 8.
In this paper, the methods developed in References 6and 9 are applied to compute the syndromes in step (i) andthe error-erasure vector discussed in step (v). An importantadvantage of this new transform decoder over the previousmethods1'10 is that the complexity of the syndromecalculation is substantially reduced. Furthermore, theChien-type search8 for the roots of the error locatorpolynomial is completely eliminated. These are replaced bythe computation of a 255-point transform using FTT-liketechniques. The result is a simpler and faster decoder thancan be obtained by conventional means.
The simplified transform decoder, was written inFortran V and was implemented on the Univac 1108computer. The matrix of decoding times for correctingerrors and erasures of the (255, 223) Reed-Solomon codeusing this simplified decoder is given in Table 1. Also thematrix of decoding times of the conventional algorithm,described in Reference 1, is provided in Table 2. A com-parison of Tables 1 and 2 shows that the new algorithm isfaster by a factor of from three to seven.
2 A fast technique for computing the error and erasuremagnitudes
The computation of the error-erasure vector in step (v) ofthe transform decoder is based on the methods inReferences 8 and 9. The key is the idea of using FFT-like
techniques over the finite field GF(28). These concepts areused to compute efficiently the expression
255-1
j = £ ataiJ for 0</<254,
1=0(6)
where a is an element of order 255 in GF(2S). To beginwith since n = 255 = 3 x 5 x 1 7 , eqn. 6 can be decom-posed into the following three stages:7'8
Stage 1
3 - 1
A \ixt iv J3) = X fl(ti t i2 f i3 jaJ» y» for 0 < ; 3 < 2
from the Stage 2
5-1
f o r
Stage 3
17-1
SUit Jv ,3) = I S2iiv jjt ,3 )t tJ. A for 0 <j\ < 16 (7)
where a 3 = a 8 S , a2 = a s l , and a , = a 1 2 0 . In eqn. 7,stage 1, stage 2, and stage 3 are 3-, 5-, and 17-pointtransforms, respectively. It was shown9 that these threetransforms can be computed with a minimum number ofoperations by a modification of Winograd's techniques tothe field GF(2m). The detailed algorithms for computingthe 3-, 5-, and 17-point transform over GF(2S) arereproduced in Appendix 7, It follows from these algorithmsthat the number of multiplications needed to compute a3-, 5-, and 17-point transform is 1, 5, and 53, respectively.In a similar fashion, it can be shown that the number ofadditions needed to compute a 3-, 5-, and 17-pointtransform is 5, 17, and 173, respectively. Thus, the totalnumber of multiplications and additions needed tocompute the Aj for 0 < / < 254 is 17 x 5 x 1 + 17 x 5 x3 + 5 3 x 5 x 3 = 1135 and 1 7 x 5 x 5 + 1 7 x 5 x 1 7 +173 x 5 x 3 =4465, respectively. In contrast, using a Chien-type search algorithm, 254(s +1) multiplications and254(s + t) additions are required for a direct computationof the inverse transform at the s + t points correspondingto the s erasure locations and the t error locations.
3 Program design and implementation
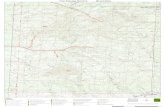
The decoding procedure described in the previous sectionwas implemented on the Univac 1108 computer usingFortran V. This program is used to correct anycombination of t errors and s erasures occuring in a255-symbol R-S code word, where 2t + s<33. Theoverall basic structure of the program is given in Fig. 1. It isdivided into a main program and five major subroutines.
The main program: This is the main driver of the rest of theprogram. It initialises the decoding process and keeps trackof the elapsed c.p.u. time.
JEE PROC, Vol. 127, Pt. E, No. 4, JUL Y1980 137

Tab
le 1
: D
eco
der
exe
cuti
on
tim
es i
n s
econ
ds (
new
met
ho
d)
Err
ors

Tab
le 2
: D
eco
der
exe
cuti
on
tim
es i
n s
econ
ds (
con
ven
tio
nal
met
ho
d)
Err
ors

Input: This subroutine generates a random code vector(polynomial) R(x) for the R—S decoder and then addserrors and erasures E(x) to it.
Step 1: The first 32 syndromes of the received vectors, aswell as the corrected vectors, are calculated in this sub-routine using a combination of the Chinese remaindertheorem and Winograd's algorithm as described inReference 5. In case the corrected received word is not anR—S code word, the subroutine will output the message,'The corrected received vector is not a codeword'. Thishelps to confirm the correctness of the program, as well asto indicate that the number of errors and erasures haveexceeded the limits allowable by the decoder.
Step 2: This subroutine computes the Forney syndromevector T (eqn. 3) from the erasure vector Z. The erasurelocator polynomial T(X) (eqn. 2) is also calculated in thisstep.
Step 3: The error locator polynomial a(x) is calculated fromthe Forney syndrome vector T using the continued fraction
main
determine elapsedCPU time
inputgenerate a random R-Scode vectorthen addrandom errors anderasures to it
step 1
compute syndromesS,,52... . . ,S32 usingthe method in eqn. 6
yes
step 2compute T'(x),compute Forney syndromesfrom T/(x)and S(i) fori=1 2 . . . 32
return
step 3
computecr(x)and S(33),...,S(255) from
step Uuse the method inappendix to computeinverse transformof ( S ^ S ^ . . . ,S? 5 5 )to obtain error anderasure vector and thencorrect received vector
Fig. 1 Basic functional structure of R-S decoding programusing transforms over GF(2B) and continued fractions
algorithm. The product of the error locator polynomialo(x) and the erasure locator polynomial r(x) is nextcomputed (eqn. 4). The coefficients of this erasure anderror locator polynomial are used to compute the remainingterms 5 3 3 , . . . , S2S5.
Step 4: This step directly computes the inverse Fouriertransform of the vector (Si, S2, . . . , S2ss) to obtain theerror and erasure vector. Finally the received vector iscorrected to provide an estimate of the transmitted codeword.
4 Simulation results
The computation times of this new algorithm and the con-ventional method described in Reference 1 for decodingcode words, which were corrupted by many differenterror and erasure patterns, are given in Tables 1 and 2.These results were obtained by performing five trials foreach entry in the tables and then averaging. Along any rowor column, the computation times tend to increase with therow or column indices until decoding failures occur becauseof an excess of allowable errors and erasures. An examin-ation of the decoding times in these two Tables indicatesthat the new decoder operates considerably faster than theconventional decoder described in Reference 1. If thereceived word is the same as the originally transmittedcode word (i.e. if no errors or erasures occurred), the newdecoder will be seven times faster. If the received wordcontains s erasures and t errors, where It + s < 33, the newdecoder will operate about three times faster. Finally, if2t + s>33, then the new decoder will operate abouttwice as fast.
5 Acknowledgment
This work was supported in part by the US Air ForceOffice of Scientific Research under Grant Number AFOSR80—0151 and also in part by NASA Contract NumberNAS 7-100.
6 References
1 MILLER, R.L., TRUONG, T.K., BENJAUTHRIT, B., andREED, I.S.,: 'A Reed-Solomon decoding program for correctingboth errors and erasures'. Deep Space Network Progress Report42-53, Jet Propulsion Laboratory, Pasadena, California, Julyand August 1979, pp. 102-107
2 REED, I.S., and TRUONG, T.K.,: 'A simplified algorithm forcorrecting both errors and erasures of R-S codes.' Deep SpaceNetwork Progress Report 42-48, Jet Propulsion Laboratory,Pasadena, California, September 1978
3 ODENWALDER, J., et al.: 'Hybrid coding systems study finalreport'. Linkabit Corp., NASA CR114, 486, September 1972
4 REED, I.S., SCHOLTZ, R.A., TRUONG, T.K., andWELCH, L.R.,: 'The fast decoding of Reed-Solomon codesusing Fermat theoretic transforms and continued fractions',IEEE Trans., 1978, IT-24, (1), pp. 100-106
5 BERLEKAMP, E.R., and RAMSEY, J.L., 'Readable erasuresimprove the performance of Reed-Solomon codes' IEEE Trans.,1978, IT-24, (5), pp. 632-633
6 REED, I.S., TRUONG, T.K., and MILLER, R.L.,: 'A Fasttechnique for computing syndromes of BCH and Reed-Solomoncodes, Electron. Lett., 1979, 15, (22), pp. 720-721
7 WINOGRAD, S.: 'On Computing the discrete Fourier transform',Proc. Natl. Acd. Sci. USA, 1976, 73,pp. 1005-1006
8 REED, I.S., and TRUONG, T.K.: 'Fast Mersenne-Prime trans-forms for digital filtering', Proc. IEE, 1978, 125, (5), pp.433-440
9 REED, I.S., TRUONG, R.L., MILLER, R.L., andBENJAUTHRIT, B.,: 'Further results on fast transforms for
140 IEE PROC, Vol. 127, Pt. E, No. 4, JUL Y1980

decoding Reed-Solomon codes over GF{2m). For m = 4, 5,6,8'.Deep Space Network Progress Report 42-50, Jet Propulsion,Laboratory, Pasadena, California, January 1979, pp. 132-154
10 BERKEKAMP, E.R.: 'Algebraic coding theory' (McGraw-Hill,1968)
7 Appendix
This Appendix contains the algorithms for computing3- 5- and 17-point transforms over fields of characteristictwo containing the necessary roots of unity. Let a be anelement of order 255 in GF(28).
The 3-point transform is given by
1k for 0<A;<2 ,3-1
Ak = I ana1n=0
where a3 = a8S is a primitive cube root of unity.
Algorithm for 3-point transform:
Sx = ax + a2, Ao = st + a0, m^ = u3su
s2 = Ao +ml, A{ = s2 +0 i , A2 = s2 + a2
Thus the 3-point transform requires only one multiplicationand five additions.
The 5-point transform is given by
5 - 1
= Z «nn=0
for 0<k<4,
where a2 = a51 is a primitive fifth root of unity.
Algorithm for 5-point transform:
Sl — a2 +fl3» 2 = a\ +^4, S3 = #i +^3,
s4 = a2 + c 4 , ss = «! +s 2 , Ao = s5 +a0,
m2 = ( a | + a £ > i ,
= (a2
= s6
A2 =
, s6 = Ao + mu s7 = s6 + m2,
s9 = ms +a2, sl0 = w4 +alt
12 = m4 +fl3, i4j = S8 + S9,
A3 = S7 +Sn, Aa, — S8 + S12
Thus the 5-point transform requires only five multiplicationsand 17 additions.
The 17-point transform is given by
17-1
Ak = Z an<*ik for 0<A:<16n=0
where ocx = a120 is a primitive 17th root of unity.Algorithm for 17-point transform:
Si = Y2 + Y3, s2 = y, + y4> 53 = y, + y3f
54 = y2 + y4, 53 = 53 +s4, NX = ^ s ,
A 2 = (A+BySlt N3 = (C + B)S2,
N4 = (C + A)S3, N5 = (C + A)S4, N6 = E -Yu
N7 = E -Y3, Ns = E • r4> N9 = E - Y2,
S6 = N, +N2, 5 7 = Nr +N3, S8 = S6
S9 = S, + N4, Sl0 = N6 +N5, Sn = S7 +NS
Xx = Sl0 +N9, X2 = S8 +N6, X3 = S10 +NS
where
A =
B =
a!3
al4
«i°a!6
«14
«?
a!0
a{2
\
Q —
/^l5 a?
a!
«?
a}}0
..15
a?
«?
,.15
"V
«f\
(8)
Xa, = [AlA,A2,Aio, Ai6]T,
E = A + B + C + D and, y, through y4 are obtained fromthe expressions for Xx through X4 on replacing each At bya{. Note that the 17-point algoritlim (eqns. 8) requires nine(4 x 4) matrix multiplications.
7
For convenience £ a, a' will be represented as thei 0i = 0
integer ]T a,-2'. Observe that Nt in eqns. 8 can be put in1 = 0
IEE PROC, Vol. 127, Pt. E, No. 4, JUL Y 1980 141

the form
/b\ / 4 4 150 169 195\ /Cl\
145 185
185 193
193 36/
b2
b3
Wwhere
C\ =z a3
150
169
) * 5
+ 0S ^
169
145
185
\-an -
(9)
c2 = al5
c3 = an +a6 +an +a10, al3
a9 + a2,
04 + a16
From (B—8) in Reference 9, one obtains the algorithm forcomputing eqns. 9. That is,'
Sl = C\ + C3, S2 = Ci + C2, S3 = C2 + C4,
S4 = C3 + c 4 , Ss = s2 + s 4 , Mi — 145 x 55,
M2 = 56 x sx, M3 = 40 x s3, Af 4 = 7 x s2,
M5 = 8 0 x s 4 , M6 = 1 3 0 x d , Mn = 2 3 x c2,
M8 = 64 x c 7 , Mg = 205 x c 4 , s6 = f l o x l , ,
s7 = S6 + M 2 , Sg = s7 +TVf4, s9 = s6 +M3,
S10 = S9 + M 4 , Sn = s7 + M S , s12 = .Sg +MS,
bi = s8 +Af6, b2 = s10 + J W 7 , ^3 = s10 +M8)
ba, = Sn +M9, A o = o 0 + s s . Thus, bx = s8 +M6,
b2 = S10 +M7 ) b3 = S10 +M8, ^4 = Sn + M9.
Hence, the total number of Galois field multiplications andadditions needed to compute A^ is 9 and 17, respectively.
The quantities Af,- for i = 2, 3,4, 5 defined in eqns. 8, arecomputed by the same procedure as indicated in Reference9. TTie number of multiplications and additions needed tocompute N,- for / = 2, 3,4, 5 is 9 and 15, respectively.
To compute Nt for i = 6, 7, 8, 9, for example, considerN6=E-Ylti.e.t
/Z>,\ / a 1 7 0 a0 a85 a0
b2
W
170
a85 a0 a170 a0
\a° ,,170 a0 a85/ \aj
(10)
By a procedure similar to that used to compute the matrix(B-8) in Reference 9, one obtains the algorithm for eqns.10 That is,
= al5 S3 =
= 1 x
s4 =
b2 —
Af2 = 215 x st, M3 = 214 x s2,
, ss = M! +M3, ^j = s4 +a3,
b3 = s4 +07, &4 = Ss + fli
Thus, from eqns. 11, the number of multiplications andadditions needed to compute N6 is 2 and 9, respectively.Similarly, the matrix Nt for / = 7 , 8, 9 requires 2multiplications and 9 additions. After combining the aboveresults, the total number of multiplications and additionsneeded to compute a 17 point transform in GF(28) is 53and 173, respectively.
CALL FOR PAPERS
8th international colloquium on automata, languages and programming (ICALP 81)
To be held on 13th—17th July 1981 at the Technion, Haifa, Israel. (Sponsored by EATCS - the European Association forTheoretical Computer Science)
TopicsAutomata Theory, Formal Languages, Analysis of Algorithms, Computational Complexity, Computability Theory, Mathe-
matical Aspects of Programming Language Definition, Semantics of Programming Languages, Program Verification and anyother subject related to theoretical computer science.
Paper submission
Authors are invited to submit four copies of an extended abstract or a full draft paper before 15th November 1980 to theChairman of the Program Committee: Prof. S. Even, ICALP 81, Computer Science Dept., The Technion, Haifa, Israel (Tel.(972)-4-225-182. Telex 46650).
Authors will be notified of acceptance/rejection by 5th February 1981. Final papers are due by 1st April 1981.For further information, please write to: Dr. O. Kariv, ICALP 81, Computer Science Dept., The Technion, Haifa, Israel.
142 IEEPROC, Vol. 127, Pt. E, No. 4, JUL Y1980














![Separating Erasures and Errors in Sublinear Algorithms · Saraf 17, Kopparty Ron-Zewi Saraf Wootters 18] • Only errors, not erasures were previously considered –Not the case without](https://static.fdocuments.us/doc/165x107/6116b8b16389702f01109715/separating-erasures-and-errors-in-sublinear-algorithms-saraf-17-kopparty-ron-zewi.jpg)



