DTCP-HE - WikiLeaks 14052012.pp… · COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED. 9...
Transcript of DTCP-HE - WikiLeaks 14052012.pp… · COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED. 9...

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
Extending DTCP to protect content in IP networks
DTCP-HE

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
2
1. Operator PayTV Evolution
2. DTCP-HE Proposal
3. Summary
Agenda

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
3
DLNALeverage CE standards to extend payTV to connected devices within an Operators Trusted IP Video Network
Certified devices connect to each other regardless of manufacturerRigorously tested for interoperability and performance
No proprietary operating systems to developSecure content with DLNA Premium Video

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
4
• End Goal : enable scalable video delivery from a Source in a trusted IP Video network with DTCP-IP encryption Extend DTCP-IP applicability beyond home networks Allow Source location in a trusted Service Provider
network Reuse DTCP-AKE for key exchange and rule
propagation Offer alternative extra security to prevent un-
authorized access (in place of DTCP-IP localizations)
• Challenges of DTCP IP application Internet Datagram Header TTL constraint Additional Localization via RTT Limitation of the Number of Sink Devices
EXPAND DTCP TO THE NETWORK
Extending DTCP-IP out of the home increases value of the DLNA and DTCP proposition by enabling consumers to watch more premium content on connected DLNA and DTCP-IP terminals
HTTPDLNA TV
VOD VoD
Sink DevicesSink
Devices
Live
Delivery over HTTP with DTCP-IP encryption
Network SourceDevice
Network SourceDevice
Trusted Operator IP Network
DTCP-IP

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
5
CHALLENGES• V1SE 10.2 TTL constraint
For ‘IP datagrams that transport DTCP AKE commands’ … ‘transmitting devices shall set TTL value … no greater then 3’
IP packets traverse > 3 hops between Sink and Network Source (HGW and BSA layer)
• V1SE 10.5 Additional Localization via RTT ‘Source devices will add Sink device’s ID to the Source device’s RTT registry, set the
transmission counter to 40 hours … if the Source device measures a RTT value of 7 ms or less during RTT test.’
Combined latency in the Home Network and in the Access Network > 7 ms
• V1 Annex C Limitation of the Number of Sink Devices ‘Without exception, the number of authenticated sink devices… shall be limited to no more than
34 devices at any time.’
Network Source delivering content to < 35 sinks is not commercially viable

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
6
DTCP SOURCE in TRUSTED IP VIDEO NETWORKApproach
• Relax existing network constraintsRemove TTL limitations for AKE messages
Remove requirement to implement Additional Localization and maintain RTT Registry for DTCP source in IP network
Remove limitation of the Number of Sink Devices < 35
• Replace localization with enhanced content access checks to prevent un-authorized accessDTCP Source authorizes each delivery based on Hash-based Message Authentication
Code (HMAC) token
DTCP Sink presents token to DTCP Source appended to string portion of content URI to prove authorization to access content object

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
7
SECURE HMAC TOKEN• Back-office generates HMAC token compliant with RFC 2104
• Token contains checks for access control
Parameter Description Example
pathURI A path defining name and/or location of content
http://movies.example.com/catch-up/tue/example.mp4http://movies.example.com/movies/*#/movies/*.mp4
expiry Time in sec since 1/1/1970 1293280587
fn Hash function used to encrypt token, default=sha256
sha512

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
8
HMAC TOKEN GENERATION• Back office combines access control parameters in an RFC 3986-compliant percent-
encoded message• Back office creates a common shared Key (shared secret) and shares the Key with
DTCP Source Shared Secret is stored encrypted at the Back Office and periodically rotated Shared Secret is delivered to DTCP Source in trusted SP Network by HTTPS using method at TLS/1.1 Back office can apply additional authentication schemes to validate authenticity of DTCP Source
network authentication and access control scheme DTCP Source X.509 Certificate
• Back office generates HMAC token using message and shared Key HMAC generators are broadly available in many languages Java, JS, PHP, other

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
9
CLIENT AUTHENTICATION SCHEMES• DTCP-IP Source located in a trusted SP Network and is transparent to client authentication
• Token delivery restricted to authenticated clients (DTCP-IP Sink) directly connected to trusted IP network
• Service Provider (SP) acquires content directly from Content Providers (CP) and use own (often proprietary) authentication scheme
Network based access control and authentication (most commonly used by large Telco’s and MSOs) Standard IEEE 802.1X Port-based Network Access Control (PNAC) and Extensible Authentication
Protocol EAP authentication framework) RFC 3748 over RADIUS
802.1X authentication involves three parties: supplicant (client), authenticator, and authentication server
Authenticator is trusted devices in a trusted network, e.g. Access Node or Router, protecting access to the network and authenticating supplicant (client)
Enhanced network security: during DHCP configuration IP address is locked to physical UNI port via DHCP Option 82 (can not be spoofed), anti-spoof filters
SPs may choose with agreement from CPs other authentication schemes, e.g. TLS 1.1 mutual authentication between client and Back-office server using X.509 certificates

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
10
DTCP SINK TOKEN PRESENTATIONDTCP Sink acquires token via one of DTCP V1SE supported methods- Extended HTTP response compliant with V1SE 12.1 Recommended MIME type for DTCP protected
content
application/x-dtcp1;DTCP1HOST=<host>;DTCP1PORT=<port>; CONTENTFORMAT=<mimetype>;DTCPIPTOKEN=<base64 string>
- Extended Content URL compliant V1SE 12.2.1 URI Recommended Format
<service>://<host>:<port>/<path>/<FileName>.<FileExtention>?CONTENTPROTECTIONTYPE=DTCP1&DTCP1HOST=<host>&DTCP1PORT=<port>& DTCPIPTOKEN=<base64 string>
where DTCPIPTOKEN carries HMAC access control token
DTCP Sink presents token to DTCP Source at the first time the content delivery is requested
http://<host>:<port>/<path>/<FileName>.<FileExtention>?DTCPIPTOKEN=<base64 string>
Token is delivered via HTTPS using method at TLS/1.1

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
11
DTCP SOURCE - TOKEN VERIFICATIONDTCP Source extracts token and uses shared secret to check that token
- ‘is valid’
- generated for the content object specified in the request (PathURI matches requested object)
- has not expired (expiry > current time)
- has not already been used by a different IP address
DTCP Source delivers content if the token passed security checks
DTCP Source replies with HTTP 401 ‘Unauthorized’ if the token failed security check or the token is not present

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
12
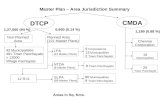
DTCP-HE CONTENT ACCESS CONTROL ARCHITECTURE
IP/MPLS Network
CoreRouter
Video headend
Access
HGW BSAxDSLGPON
Origin Servers
AAA, CMSPortal
DTCP-IP secured HTTP Streaming
Interactive Control(DMC)
DLNA-TV(DMR) DTCP Source
Multi-Service Edge (BNG)
In Home DLNA Discover & Control
Acquire content URI protected with HMAC token
Device Authentication, Content Discovery and Selection: CMS feeds & Control
DTCP Sink
HTTPS Response or URL for device specific content
1
2
3
4 Present URL with HMAC token
URL with HMAC used for access controlDTCP-IP for content encryption
Back Office
5
Pas
s U
RL
to D
TC
P
Sin
k
DTCP Source verifies token using shared secret
Shared Key
Secure distribution options: HTTPS TLS 1.1

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
DTCP-HE HMAC CONTENT ACCESS CONTROL FLOWBack OfficeDTCP Sink DTCP Source
Back office creates shared secret
4
1
Presents URI to DTCP SOURCEhttp://<host>:<port>/<path>/<FileName>.<FileExtention
>?DTCPIPTOKEN=<base64 string>
5
6
Content Discovery and Selection
Generates content URI protected with
HMAC token
2
DTCP AKE FLOW
Passes Content URI, DTCP1HOST, DTCP1PORT, DTCPIPTOKEN to DTCP SINKe.g. application/x-dtcp1;DTCP1HOST=<host>;DTCP1PORT=<port>; CONTENTFORMAT=<mimetype>;DTCPIPTOKEN=<base64 string>
3
Verifies Access control using shared secret

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
14
EXAMPLE NETWORK CLIENT AUTHENTICATIONZoom-in illustration
HomeGateway
BTVBTV
...
Accessnode
IP
BroadbandServicesRouter
BroadbandServices
Aggregator
HGW AAA Server
BTVBTV AuthenticationAuthorisationAccounting Server(RADIUS and EAR Server)
EAP over RADIUS (w/port attribute)
• Household Authentication: Home Gateway
Client Authenticator Authentication Server
Requirement to deliver token to authenticated devices. Transparent to any device authentication used by Telco’s and MSOs.
Device UDID is registered directly with back-office user profile. Only registered device can receive token.
• Device Authentication: Common approaches employed by SP’s
Other scheme selected by SP, e.g. TLS 1.1 mutual authentication using X.509 certificates.
802.1X Home gateway authenticates the device. Only authenticated device can receive token.

COPYRIGHT © 2011 ALCATEL-LUCENT. ALL RIGHTS RESERVED.
15
• DLNA Adoption enables Multi channel Video Program Distributors to more simply leverage home Connected Devices to deliver the next generation of consumer entertainment
• DTCP IP localisations are not well suited for deploying DTCP source in a SP IP network
TTL and RTT constraints, limitation of the number of sinks make implementation impractical
Not designed as conditional access control
Need to relax constraints
• DTCP source in IP network can use HMAC token based access control for increased solution security:
DTCP source is deployed in a trusted SP network
HMAC token provides fine-grained access control
Access to content object, content location, content path or SP defined URI patterns
Time restriction
IP address restriction
HMAC token is a common access control technology for premium content over Internet and CDNs
• DTCP source in IP network with HMAC token access is fully standard based solution using HTTP, HMAC (RFC 2104), string encoding (RFC 3986)
SUMMARY