DFARS 252.204-7012 Cybersecurity for Federal Contractors ... · information provided by or for the...
Transcript of DFARS 252.204-7012 Cybersecurity for Federal Contractors ... · information provided by or for the...

DFARS 252.204-7012
Cybersecurity for Federal Contractors: Now and the Future

We will cover…

What is DFARS 252.204-7012? ◦ FAR (Federal Acquisition Regulation) to be
used by most agencies for procurement planning and contract formation and administration
◦ DFARS (Defense Federal Acquisition Regulation Supplement) – all of FAR ch. 2
◦ DFARS contain first agency-specific regulation of non-classified, sensitive information based on general controls published by the National Institute of Standards and Technology (NIST)
◦ That regulation is intended to be “basic” controls for the safeguarding of contractor information systems that process, store, or transmit Federal information and the core provision is 252.204-7012

Terms
◦ CUI: "Controlled Unclassified Information“ as described in the CUI Registry* and administered by the National Archives and Records Administration (NARA)
◦ CDI: "Covered Defense Information“. DoD CDI is essentially the same as FAR CUI, except CDI has contractual differences defined in the DoD contract
◦ Covered Defense Information System: unclassified information system that is owned or operated by or for a contractor and that processes, stores, or transmits CDI
◦ CTI: A subset of CUI data is further clarified as "Controlled Technical Information"
◦ COTS Software: “Commercial Off-The-Shelf Software” excluded from classification as CUI and not subject to DFARS 252.204-7012
◦ UCTI: "Unclassified Controlled Technical Information”; used by original DFARS
◦ Cyber Incident: Actions taken that result in a compromise of, or an actual or potentially adverse effect on, a Covered Defense Information System and/or CDI
*http://www.archives.gov/cui/registry/category-list.html

History of DFARS 252.204-7012
1
Rising concerns unclassified (non-secret) but sensitive Information being mishandled
2
Increasingly frequent and more sophisticated cyber attacks and intrusions

Motivating Examples
2001 – 2002 Hacker gained access to 97 U.S. military networks while looking for information on UFOs; conveniently left message, “Your security is crap.”
1 2003 – 2008 Mathematician in his 50s gained unfettered access to French aviation company Dassault and stole weapons data for five years before he was caught and cost the company $360 million.
2 Dec. 2014 Records on 21.5 million people stolen from Office of Personnel Management (OPM); Intrusion relied on Chinese-created malware.
3 2003 → ? Titan Rain: coordinated cyber-attack by Chinese military on defense contractors and agencies including DoD, British Defense Ministry, Lockheed, Sandia National Labs, Redstone Arsenal and NASA.
4

Reaction
◦ Consensus developed rules were needed for
baseline security, incident reporting and remedial
actions covering all information system containing
sensitive federal information
◦ Response has been,
◦ General: NIST special publication (sp) 800-171
rev. 1
◦ Specific: Agency and Departmental regulations
or rules some in line with NIST controls, such as
DFARS

Date Event
11/4/2010
Executive Order 13556 – Policy to Protect Controlled Unclassified Information;
program to be run by NARA as executive agent to identify, manage and
protect CUI; all agencies to contribute and comply
11/18/2013 DFARS Final Ruling implementing requirements for safeguarding CTI
8/26/2015 Interim Ruling for safeguarding CDI
12/30/2015 DoD extended deadline for compliance with all NIST 800-171 Controls to
12/31/2017
5/15/2016 FAR Cyber Ruling – Applies subset of 15 controls from NIST 800-171
9/14/2016 NARA Final CUI Ruling; 32 CFR 2002
10/21/2016 DFARS Final Ruling; COTS exemption; Clarification CDI (CUI Registry)
12/7/2017 In Senate testimony DoD Undersecretary Ellen Lord explained that a System
Security Plan (“a simple plan”) by 2018 is compliance with deadline
01/24/2018 NARA: Issued guidance for drafting agreements with non-executive branch
entities involving CUI that will not be covered by upcoming FAR

◦ DFARS 252.204.7008 – Compliance with Safeguarding Covered Defense Information Controls – contract provision making 800-171 mandatory
◦ DFARS 252.204.7009 – Limitations on the Use or Disclosure of Third-Party Contractor Reported Cyber Incident Information – information can only be given to government; personnel have to be covered by NDAs
DFARS Cyber Security Rules for Contractors

◦ DFARS 252.239.7010 – Cloud
Computing Services
◦ DFARS 252.204.7012 – Safeguarding Covered Defense
Information (“CDI”); Cyber
Incident Reporting
◦ Most significant of the four DFARS
on cybersecurity
DFARS Cyber Security Rules for Contractors

DFARS 252.239.7010 – Cloud Computing Services Requires:
◦ Must adhere to the federal Cloud Computing Security Requirements
Guide (SRG)*
◦ DoD data remains in US unless permitted otherwise in writing
◦ Information is confidential
◦ Imaged Hacked Systems retained for 90 days
◦ Notification of Third-party Access Requests
* http://iase.disa.mil/cloud_security/Pages/index.aspx

DFARS 252.239.7010 – Cloud Computing Services (cont.)
Requires:
◦ Reporting: All cyber-incidents have to be reported through
http://dibnet.dod.mil/
◦ DoD access to facilities, personnel, equipment and records
◦ Flow-down of provision to subcontracts

Main provision is DFARS 252.204.7012
◦ Title: Safeguarding Covered Defense Information and Cyber Incident Reporting (Oct 2016)
◦ Requires Adequate Security: “implement NIST SP 800-171, as soon as practical, but not later than December 31, 2017.”
◦ Required Reporting: Contractors and subcontractors must report cyber incidents on information systems with CDI or which affects ability to perform critical support under a contract
◦ Required Response: On discovery, conduct review for evidence; submit to DoD and receive assigned incident report number; provide number to prime/next higher subcontractor; preserve imaged system for 90 days
◦ When to report: within 72 hours directly to DoD via specified portal

DFARS 252.204.7012 (cont.)
◦ Additional cyber incident requirements: provide DoD access to information /
equipment to conducts its analysis; submit malicious software to DoD Cyber
Crime Center (DC3)
◦ Using Cloud Solution:
◦ Cloud Service Provider (CSP) must meet security requirements of the Federal Risk and
Authorization Management Program (FedRAMP), Moderate baseline
◦ CSP must comply with same as contractor for cyber incident reporting, malicious
software, media preservation and protection, access to additional information and
equipment necessary for forensic analysis, and cyber incident damage assessment.

Covered Companies: Who Has to Comply
• 1. Direct or indirect DoD contractor, or
• 2. Work with Covered Defense Information (CDI), or
• 3. DFARS clause 252.204.7008 is in a contract
The DFARS Cover All of the Following Companies:

Flow-down to Subcontractors
Contractors to include clause in solicitations, Purchase Orders and Subcontracts
Specifically applies to contract (i) providing “operationally critical support” and/or (ii) working with Covered Contractor Information System
All subcontractors must meet NIST 800-171 controls
• Unclear contractor / subcontractor responsibility to ensure its contractors and suppliers are compliant

◦ Regulations Not Concerned with Classified
(Secret) Material
◦ Do Not Address Other Privacy or
Confidentiality Regulations, although there
can be an overlap
◦ ITAR (International Traffic in Arms Regulations
– State Department)
◦ EAR (Export Administrative Regulations –
Commerce Department)
◦ HIPAA – Standards for Privacy of Individually
Identifiable Health Information
◦ Gramm-Leach-Bliley – Act Right to Opt-out
of Sharing of Nonpublic Personally
Identifiable Financial Information
Keep in Mind:
Excluded Data Can
Exclude Sub- contractors

What is Covered as CUI/CDI
Definition: Any unclassified information provided by or for
the DoD relating to a contract or collected, developed, received, transmitted, used, or stored by or
for a contractor in performing the contract.
Can be technical, administrative, or operational in nature and is:
• 1. CTI
• 2. Critical information (operations security)
• 3. Export control
• 4. Any other information, marked or identified in the contract, that requires safeguarding or dissemination controls pursuant to and consistent with law, regulations, and Government policies

General Requirements (beyond language of DFARS)
Found in NIST (sp) 800-171 rev. 1
“Protecting Controlled Unclassified
Information in Non-Federal Information
Systems”
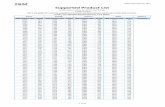
◦ 14 Categories
◦ 110 Controls
◦ Referenced by Sections Numbers in
chapter 3 of publication

NIST 800-171 Cybersecurity Standards (https://nvlpubs.nist.gov/nistpubs/specialpublications/nist.sp.800-171r1.pdf)
3.1 Access Control
3.2 Awareness and Training
3.3 Audit and Accountability
3.4 Configuration Management
3.5 Identification and Authentication
3.6 Incident Response
3.7 Maintenance
3.8 Media Protection
3.9 Personnel Security
3.10 Physical Protection
3.11 Risk Assessment
3.12 Security Assessment
3.13 System and Communication Protection
3.14 System and Information Integrity

Responsibilities of Direct Contractors
and Subcontractors
◦ Adequate Systems Facilities Security
◦ Report Cyber Incidents
◦ Maintain records of compliance as well as breaches
◦ Train and obligate personal
◦ Also, assess and correct vulnerabilities (and demonstrate this
has occurred)
*http:// dibnet.dod.mil

NIST 800-171 Cybersecurity Standards: Assessments Required of
Contractors 3.11 Risk Assessment:
◦ “Periodically assess the risk to organizational operations . .. resulting from the . . . processing, storage, or transmission of CUI.”
◦ ”Remediate vulnerabilities in accordance with risk assessments.”
◦ “Periodically assess the security controls in organizational systems….”
◦ “Develop and implement plans of action designed to correct deficiencies ….“
3.12 Security Assessment:
◦ “Periodically assess the security controls in
organizational systems to determine if the
controls are effective….”
◦ “Develop and implement plans of action . . .
to correct deficiencies and reduce or
eliminate vulnerabilities….”
◦ “Monitor security controls on an ongoing
basis….”
◦ Develop, document, and periodically
update system security plans….”

Compliance Deadlines
Complete DFARS CDI Assessment (current cybersecurity posture) and report your findings to the DoD Chief Information Officer (CIO), within 30 days contract award
1
Prior Interpretation: Correct any gaps documented by an assessment by December 31, 2017
2
Now: Plan of compliance by end of 2017
3

Broader Reach than DoD ◦ May 15, 2016 FAR Cyber Ruling (FAR 52.2014-21, Basic
Safeguarding of Contractor Information Systems Requirements – Applies subset of 15 controls from NIST 800-171, effective June 16, 2016
◦ Covers 300,000± Companies; Has Mandatory Flow-down; no cyber-incident reporting requirement
◦ NRA intends to establish a universal FAR that will supersede DFARS 252.204-7012, use NIST SP 800-171, and expand the scope to all Federal agencies and contractors (such as NASA, DoE, etc.) and not just the DoD
◦ NARA's timing is open, but in press interviews predicted beginning FY 2019

Open Questions ◦ Do CSPs apply just apply FedRamp or to they have to meet 800-171
standards?
◦ What CDI / CUI marking requirements exist?
◦ Is the COTS exemption the same for solicitations as subcontracts
◦ Is a SSP really sufficient for end of 2017 compliance?
◦ When is final compliance deadline
◦ Will there be 800-171 audits?
◦ Enforcement
◦ Who is responsible? DCAA (Defense Contract Audit Agency)?
◦ What are the consequences of failure to comply?

Conducting a DFARS
Assessment
◦ Don’t Delay
◦ Don’t Start Without Company Buy-in Across Functions –
Compliance, Facilities, Finance, IT, Legal, Supply Chain
Management, Engineering, Manufacturing
◦ Senior Management Responsibility, Supervision and
Assessment Focal Point
◦ Understand DFARS and NIST 800-171 or Retain Outside
Expertise
◦ Set Milestones to Avoid Project Drift

Assessment Steps…
◦ Identifying applicable “information systems”*, the
scope of effort, available resources and personnel,
and tasks and milestones
◦ NIST 800-171 chapter 3 (110 controls) full
assessment
◦ Preparation and agreement on a gap analysis and
status of compliance
◦ Preparation and adopt of a remediation plan
◦ From that remediation plan, prepare the required
POA&M (Plan of Action and Milestones)
◦ Institute POA&M, including document storage,
control management and audit solution
◦ Training and monitoring
*Group of components (workstations, servers, VoIP phones, routers, switches, firewalls) in a connected infrastructure, under a single management authority. A separate information system could be segregated by a firewall or logically separated physically or by access, or under a separate management authority

DFARS Assessment Approach
Preliminary
DFARS
Questionnaire
• Preliminary DFARS Assessment
• Interview
GAP Analysis
• Compiling results of preliminary questionnaire, interview, and assessment document
• Preparation and Presentation of 800-171 GAP Analysis
POA&M
• Preparation, Presentation and Tracking of POA&M
• Preparation of Third Party Compliance Certificate

Preliminary Review
◦ Documentation is key throughout process. E.g., during the preliminary
assessment, the DFARS questionnaire is completed with/by the
prospective client.
◦ The initial interview with business stakeholders is carried out following the
completion of the questionnaire.
◦ During the initial interview outside assessor learns about the client’s IT
systems and internal flow of operations.
◦ The goal is to identify current security posture of the business.

Determining the Scope
The results of the interview and
questionnaire are used to create a customized assessment document
In that assessment document, each
control will be clearly defined for the client in
accordance with DFARS requirements
The outside team works closely with the relevant
client personnel to provide clarification on
what each of the 110800-171 controls mandate and how
these controls apply to the client’s business

Research and Gap Analysis
The audit team records the results of each stage into the third-party’s assessment tool.
The tool generates a percentage of compliance.
The audit team identifies and investigates each
control:
Controls met by the client are recorded and verified.
Controls that are not met are recorded and
recommendations to satisfy the control are provided to
the client.
The result is a Gap Analysis specific to that client.

Agreed Remediation ◦ The audit team presents Gap Analysis to the client’s
stakeholders.
◦ The Gap Analysis will spell out in detail the deficiencies identified, as well as recommendations for remediation.
◦ The Gap Analysis enables the client to develop a roadmap, which includes specific goals tied to dates, will allow the client to reach compliance.
◦ This roadmap, reflecting the requirements of 800-171 and the DFARS, as well as the clients’ priorities, will be the client’s POA&M.

Progress Reviews
• The client will drive the timeline to remedy identified deficiencies.
• The outside audit team will continue to track progress toward full compliance as each deficiency is resolved.
• The POA&M is a ‘living and breathing’ document that is used to track implementation of the recommendations and may be amended as circumstances and available solutions change.
• The audit team typically will follow up weekly to track and verify implementation progress until full compliance.

Certification and Benefits of Third-party Assessments
POA&M and DFARS Assessment Tool are used to provide the client the NIST (sp) 800-171/DFARS 252.204-7012 Compliance Certificate
Partial compliance certificate along with POA&M can demonstrate to DoD or Prime Contractor that client is taking steps to be compliant and progress in achieving full compliance
Full compliance certificate will demonstrate compliance as of date of certificate

How Long Does it Take to Complete a DFARS Assessment? ◦ About two man-weeks for SMEs. Larger companies can
take several months.
◦ Variable factors:
- number of unique "Information Systems" that must be assessed,
- number of employees and their computing devices, - number of sites that must be visited during the
assessment, - number of DoD contracts that must be reviewed for
specific requirements, and - definitions of systems, and the overall number of
computing systems in place.

QUESTIONS AND DISCUSSION