COS 413 Day 20. Agenda Assignment 6 is posted –Due Nov 7 (Chap 11 & 12) LAB 7 write-up due...
-
date post
22-Dec-2015 -
Category
Documents
-
view
214 -
download
1
Transcript of COS 413 Day 20. Agenda Assignment 6 is posted –Due Nov 7 (Chap 11 & 12) LAB 7 write-up due...
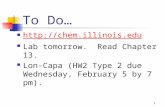
Agenda• Assignment 6 is posted
– Due Nov 7 (Chap 11 & 12)
• LAB 7 write-up due tomorrow• Lab 8 in OMS tomorrow
– Hands-on project 11-1 through 11-4– We will be working in teams
• Capstone proposals VERY OVER Due– I have received only 7 proposals
• Only five have been accepted– Martin, Mitchell, Demers, Southern and Marquis
– 1st progress report over due • You must have an accepted proposal to send a progress report
– proposal and progress reports (on time) are 10% of the grade.
• Finish Discussion on network forensics Chap 11• We will be doing the Chaps 13, 14, 15 & 16 to finish out this class
– Yes that includes mobile devices.
Rest of Semester
• Lectures– Nov 7 Chap 13
• Assignment 6 Due
– Nov 11 Veteran’s Day – No class
– Nov 14 Quiz 3• Chap 12, 12 & 13• Assignment 7 Due
– Nov 18 Chap 14– Nov 21 Chap 14
• Assignment 8 Due
– Nov 25 Chap 15– Dec 2 Chap 15
• Assignment 9 Due
– Dec 5 Chap 16 – Dec 9 Chap 16
• Assignment 10 Due
– Dec 12 Quiz 4 • Chap 13, 14 & 15
• Labs– Nov 5 - LAB 8 network
forensics• LAB 7 due
– Nov 12 – No lab• Lab 8 due
– Nov 19 – Final lab part 1 – Kidnapping case
– Nov 28 – thanksgiving break– Dec 3 – Final lab part 2 –
Kidnapping case– Dec 10 – Final lab part 3 –
Kidnapping case• Final lab will count as two labs
(lab 9 &10) • Write-up will be due Dec 12
• Capstone presentations – Dec 19 @ 1 PM
How Hackers Hack
Many Techniques Social Engineering
Get someone to give you their password Cracking
Guessing passwords A six letter password (no caps)
> 300 million possibilities Merriam-Webster's citation files, which were begun in the 1880s, now contain 15.7
million examples of words used in context and cover all aspects of the English vocabulary.
http://www.m-w.com/help/faq/words_in.htm Buffer Overflows
Getting code to run on other PCs Load a Trojan or BackDoor
Snoop and Sniff Steal data
Denial of Service (DOS) Crash or cripple a Computer from another computer
Distributed Denial of Service (DDOS) Crash or cripple a Computer from multiple distributed computers
DOS attacks
Kill the PC with one packet Exploits problem in O/S
Teardrop WinNuke
Kill the PC with lots of packets Smurf Frag Tribal Flood Network
Attacks Requiring Protection
Denial-of-Service (DoS) Attacks Make the system unavailable (crash it or make
it run very slowly) by sending one message or a stream of messages. Loss of availability
Single Message DOS Attack(Crashes the Victim)
Server Attacker
Attacks Requiring Protection
Denial-of-Service (DoS) Attacks Make the system unusable (crash it or make it
run very slowly) by sending one message or a stream of messages. Loss of availability.
Message Stream DOS Attack(Overloads the Victim)
Server Attacker
Distributed Denial-of-Service Attacks
Distributed DOS (DDoS) Attack:Messages Come from Many Sources
Server
DoS Attack Packets
DoS Attack PacketsComputer with
Zombie
Computer withZombie
Attacker
AttackCommand
AttackCommand
Attacks Requiring Protection Malicious Content
Viruses Infect files
propagate by executing infected program Payloads may be destructive
Worms propagate by themselves
Trojan horses appear to be one thing, such as a game, but
actually are malicious Snakes:
combine worm with virus, Trojan horses, and other attacks
Trojan’s and BackDoors
The trick is get the a backdoor (unauthorized entry) on a machine
Easy way Get the user to load it himself Cracked Software (WAREZ) Free Software (KAZAA)
Hard Way Get a password Create a buffer overflow
Microsoft can teach you how Most Common Trojans and backdoors
SubSeven ServU Netbus Back Orifice
If have download cracked software (illegal) or have loaded KAZAA or downloaded movies (adult or mainstream) chances are that you have been hacked!
Dangers of Wireless Networking
Wi-Fi was designed as an OPEN technology which provides EASE of ACCESS It’s the hacker’s dream environment See wireless_insecurity.pdf Also
http://www.cs.wright.edu/~pmateti/InternetSecurity/Lectures/WirelessHacks/Mateti-WirelessHacks.htm
Common hacks Wardriving Evil twin Cloning Snooping
802.11 (in)Security Attackers can lurk outside your
premises In “war driving,” drive around sniffing out
unprotected wireless LANs In “drive by hacking,” eavesdrop on
conversations or mount active attacks.
Site with 802.11 WLAN
OutsideAttacker
DoonesburyJuly 21, 2002
WiFi (& Cell) Cloning
Since all wireless technologies require broadcasting of some sort all you need to do is listen in Scanner
For any device to “connect” it must Indentify, Validate, verify, provide a code or
some mechanism Ex, MAC’s, EISN’s, SSN, WEP secrets, etc
Since you can “listen” you can also record Record the first part of any connection Replay it You have just “cloned” the original device
Web Bugs
Web Bugs are used to gather information about a users From “bugging” a room
Down by embedding a piece of code monitoring software in a image link Works on WebPages and HTML e-mail Often called Clear gifs
Small 1X1 pixels Transparent Made so that uses don’t see them
Every Time the Web Bugs is loaded it gathers info about the user that activated the web bug and sends it off to a remote server
How Phishing Works
Phishing is “fishing for suckers!” Send a e-mail that mimics the real
thing and get the recipient to give their password
Echelon
Global Electronic Spy network http://www.hermetic.ch/crypto/echelon/echelon.htm
It exists but little is known on exactly how it works The basics
Collect all electronic conversations Crack all encrypted stuff Search all conversations for “key words”
Find the “speakers”
Guide to Computer Forensics and Investigations 25
Using UNIX/Linux Tools (continued)
• Knoppix-STD tools (continued)– john– chntpw resets passwords on a Windows PC– tcpdump and ethereal are packet sniffers
• With the Knoppix STD tools on a portable CD– You can examine almost any network system
• Cheat codes – http://www.knoppix.net/wiki/Cheat_Codes – knoppix vga=788 ; forces 800x600 FrameBuffer for
older monitors
Guide to Computer Forensics and Investigations 27
Using UNIX/Linux Tools (continued)
• The Auditor– Robust security tool whose logo is a Trojan warrior– Based on Knoppix and contains more than 300 tools
for network scanning, brute-force attacks, Bluetooth and wireless networks, and more
– Includes forensics tools, such as Autopsy and Sleuth– Easy to use and frequently updated
Guide to Computer Forensics and Investigations 28
Using Packet Sniffers
• Packet sniffers– Devices or software that monitor network traffic– Most work at layer 2 or 3 of the OSI model
• Most tools follow the PCAP format
• Some packets can be identified by examining the flags in their TCP headers
• Tools– Tcpdump– Tethereal
Guide to Computer Forensics and Investigations 32
Using Packet Sniffers (continued)
• Tools (continued)– Snort– Tcpslice– Tcpreplay– Tcpdstat– Ngrep– Etherape– Netdude– Argus– Ethereal– WireShark
Guide to Computer Forensics and Investigations 36
Examining the Honeynet Project
• Attempt to thwart Internet and network hackers– Provides information about attacks methods
• Objectives are awareness, information, and tools
• Distributed denial-of-service (DDoS) attacks– A recent major threat– Hundreds or even thousands of machines (zombies)
can be used
http://www.honeynet.org/
Guide to Computer Forensics and Investigations 38
Examining the Honeynet Project (continued)
• Zero day attacks– Another major threat– Attackers look for holes in networks and OSs and
exploit these weaknesses before patches are available
• Honeypot– Normal looking computer that lures attackers to it
• Honeywalls– Monitor what’s happening to honeypots on your
network and record what attackers are doing
Guide to Computer Forensics and Investigations 39
Examining the Honeynet Project (continued)
• Its legality has been questioned– Cannot be used in court– Can be used to learn about attacks
• Manuka Project– Used the Honeynet Project’s principles
• To create a usable database for students to examine compromised honeypots
• Honeynet Challenges– http://www.honeynet.org/misc/chall.html – You can try to ascertain what an attacker did and then post
your results online
Guide to Computer Forensics and Investigations 41
Summary
• Network forensics tracks down internal and external network intrusions
• Networks must be hardened by applying layered defense strategies to the network architecture
• Live acquisitions are necessary to retrieve volatile items
• Standard procedures need to be established for how to proceed after a network security event has occurred
Guide to Computer Forensics and Investigations 42
Summary (continued)
• By tracking network logs, you can become familiar with the normal traffic pattern on your network
• Network tools can monitor traffic on your network, but they can also be used by intruders
• Bootable Linux CDs, such as Knoppix STD and Helix, can be used to examine Linux and Windows systems
• The Honeynet Project is designed to help people learn the latest intrusion techniques that attackers are using