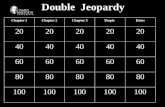
Double Jeopardy Chapter 1Chapter 2Chapter 3PeopleDates 20 40 60 80 100.
Chapter 1Chapter 1 Introduction: Introduction
Transcript of Chapter 1Chapter 1 Introduction: Introduction

Chapter 1: IntroductionChapter 1 IntroductionOur goal: Overview:
get “feel” and terminologymore depth detail
what’s the Internetwhat’s a protocol?network edgemore depth, detail
later in courseapproach:
network edgenetwork coreaccess net physical media
use Internet as example
access net, physical mediaInternet/ISP structureperformance: loss, delayp yprotocol layers, service modelsnetwork modeling
Introduction 1-1

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-2

What’s the Internet: “nuts and bolts” viewmillions of connected computing devices: hosts
router workstationcomputing devices hosts = end systemsrunning network apps local ISP
servermobile
communication linksfiber, copper, radio, satellite regional ISPtransmission rate = bandwidth
routers: forward packets
regional ISP
routers: forward packets (chunks of data)
company
Introduction 1-3
network

What’s the Internet: “nuts and bolts” view
protocols control sending, receiving of msgs
router workstationreceiving of msgs
e.g., TCP, IP, HTTP, FTP, PPPInternet: “network of local ISP
servermobile
networks”loosely hierarchicalpublic Internet versus regional ISPpublic Internet versus private intranet
Internet standards
regional ISP
RFC: Request for commentsIETF: Internet Engineering Task Force company
Introduction 1-4
network

What’s the Internet: a service viewcommunication infrastructure enables fdistributed applications:
Web, email, games, e-commerce file sharingcommerce, file sharing
communication services provided to apps:
Connectionless unreliableconnection-oriented reliable
Introduction 1-5

What’s a protocol?What s a protocol?human protocols:
“ h t’ th ti ?”network protocols:
hi th th “what’s the time?”“I have a question”introductions
machines rather than humansall communication introductions
… specific msgs sent
all communication activity in Internet governed by protocols
… specific actions taken when msgs received, or other events
protocols define format, order of msgs sent and received among network or other events received among network
entities, and actions taken on msg
Introduction 1-6
transmission, receipt

What’s a protocol?What s a protocol?a human protocol and a computer network protocol:
Hi TCP connection
HiGot the
TCP connectionreq
TCP connectionresponseGot the
time?2:00
responseGet http://www.awl.com/kurose-ross
<file><file>time
Introduction 1-7
Q: Other human protocols?

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-8

A closer look at network structure:
network edge:network edge:applications and hostsnetwork core:
routersnetwork of networks
t k access networks, physical media:communication links
Introduction 1-9
communication links

The network edge:The network edgeend systems (hosts):
l run application programse.g. Web, emailat “edge of network”g
client/server modelclient host requests, receives
i f l service from always-on servere.g. Web browser/server; email client/server
peer-peer model:minimal (or no) use of dedicated servers
Introduction 1-10
dedicated serverse.g. Gnutella, KaZaA

Network edge: connection-oriented serviceg
Goal: data transfer TCP service [RFC 793]Goal: data transfer between end systemshandshaking: setup ( f ) d
TCP service [RFC 793]reliable, in-order byte-stream data transfer
(prepare for) data transfer ahead of time
Hello, hello back human
loss: acknowledgements and retransmissions
flow control:H o, h o ac human protocolset up “state” in two communicating hosts
flow controlsender won’t overwhelm receiver
congestion control:mmu gTCP - Transmission Control Protocol
I ’ i
congestion control:senders “slow down sending rate” when network
n st d
Introduction 1-11
Internet’s connection-oriented service
congested

Network edge: connectionless serviceg
Goal: data transfer App’s using TCP:Goal: data transfer between end systems
same as before!DP D
App s using TCP:HTTP (Web), FTP (file transfer), Telnet ( l ) P UDP - User Datagram
Protocol [RFC 768]: connectionless
(remote login), SMTP (email)
connectionless unreliable data transfer
App’s using UDP:streaming media
no flow controlno congestion control
streaming media, teleconferencing, DNS, Internet telephony
Introduction 1-12

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-13

The Network CoreThe Network Core
mesh of interconnected froutersthe fundamental
sti h is d t question: how is data transferred through net?
circuit switching:c rcu t sw tch ngdedicated circuit per call: telephone net
k t it hi d t packet-switching: data sent thru net in discrete “chunks”
Introduction 1-14

Network Core: Circuit Switchingg
End-end resources End end resources reserved for “call”link bandwidth, switch capacitydedicated resources: no sharingno sharingcircuit-like (guaranteed) (g )performancecall setup required
Introduction 1-15

Network Core: Circuit Switchinggnetwork resources
( b d idth) dividing link bandwidth
“ ”(e.g., bandwidth) divided into “pieces”pieces allocated to calls
into “pieces”frequency divisiontime divisionpieces allocated to calls
resource piece idle if not used by owning call
time division
y g(no sharing)
Introduction 1-16

Circuit Switching: FDM and TDMC rcu t Sw tch ng FDM and DM
FDM 4 usersExample:
frequency
4 users
frequency
timeTDM
frequency
Introduction 1-17time

Numerical exampleNumer cal example
How long does it take to send a file of How long does it take to send a file of 640,000 bits from host A to host B over a circuit-switched network?
All links are 1.536 MbpsEach link uses TDM with 24 slots500 msec to establish end-to-end circuit
W k it t!Work it out!
Introduction 1-18

Network Core: Packet Switchinggeach end-end data stream
divided into packetsresource contention:
t divided into packetsuser A, B packets sharenetwork resources
aggregate resource demand can exceed amount available
each packet uses full link bandwidth
d d d
congestion: packets queue, wait for link uset d f d resources used as needed store and forward:
packets move one hop at a time
Node receives complete packet before forwarding
Bandwidth division into “pieces”Dedicated allocationResource reservation
Introduction 1-19
Resource reservation

Packet Switching: Statistical Multiplexingg p g
A C10 Mb/sEthernet statistical multiplexing
B1.5 Mb/s
p g
Bqueue of packetswaiting for output
link
D E
Sequence of A & B packets does not have fixed pattern statistical multiplexing.
In TDM each host gets same slot in revolving TDM
Introduction 1-20
In TDM each host gets same slot in revolving TDM frame.

Packet switching versus circuit switchingg g
Packet switching allows more users to use network!
1 Mb/s linkeach user:
k / h “100 kb/s when “active”active 10% of time
N userscircuit-switching:
10 usersk t it hi
N users1 Mbps link
packet switching: with 35 users, probability > 10 active
Introduction 1-21
less than .0004

Packet switching versus circuit switchingg g
Is packet switching a “slam dunk winner?”
Great for bursty dataresource sharingsimpler, no call setup
Excessive congestion: packet delay and losspr t c ls needed f r reli ble d t tr nsfer protocols needed for reliable data transfer, congestion control
Q: How to provide circuit-like behavior?Q pbandwidth guarantees needed for audio/video apps
Introduction 1-22
still an unsolved problem (chapter 6)

Packet-switching: store-and-forwardg f
R R RL
Takes L/R seconds to transmit (push out)
Example:L = 7 5 Mbits
R R R
transmit (push out) packet of L bits on to link with capacity of R bps
L = 7.5 MbitsR = 1.5 Mbpsdelay = 15 secbps
Entire packet must arrive at router before it can be transmitted it can be transmitted on next link: store and forwardd l 3L/R
Introduction 1-23
delay = 3L/R

Packet-switched networks: forwardingg
Goal: move packets through routers from source to destinationdestination
we’ll study several path selection (i.e. routing) algorithms (chapter 4)
d kdatagram network:destination address in packet determines next hoproutes may change during sessionroutes may change during sessionanalogy: driving, asking directions
virtual circuit network:h k ( l D) each packet carries tag (virtual circuit ID), tag
determines next hopfixed path determined at call setup time, remains fixed h ll
Introduction 1-24
thru callrouters maintain per-call state

Network TaxonomyTelecommunication
networks
Circuit-switched Packet-switchednetworks networks
DFDM TDM Networkswith VCs
DatagramNetworks
• Datagram network is not either connection-oriented or connectionless.• Internet provides both connection-oriented (TCP) and
Introduction 1-25
Internet provides both connection oriented (TCP) and connectionless services (UDP) to apps.

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-26

Access networks and physical mediap y
Q: How to connect end systems to edge router?systems to edge router?residential access netsinstitutional access institutional access networks (school, company)
bil t kmobile access networks
Keep in mind: b d id h (bi bandwidth (bits per second) of access network?
Introduction 1-27
shared or dedicated?

Residential access: point to point accessp p
Dialup via modemD a up a mo mup to 56Kbps direct access to router (often less)Can’t surf and phone at same time: can’t be “always on”
d l lADSL: asymmetric digital subscriber lineup to 1 Mbps upstream (today typically < 256 kbps)up to 8 Mbps downstream (today typically < 1 Mbps)up to 8 Mbps downstream (today typically < 1 Mbps)FDM: 50 kHz - 1 MHz for downstream
4 kHz - 50 kHz for upstream
Introduction 1-28
p0 kHz - 4 kHz for ordinary telephone

Residential access: cable modems
HFC: hybrid fiber coaxHFC: hybrid fiber coaxasymmetric: up to 30Mbps downstream, 2 Mbps upstream
network of cable and fiber attaches homes to ISP router
h m s sh ss t t homes share access to router deployment: available via cable TV companies
Introduction 1-29

Residential access: cable modems
Introduction 1-30Diagram: http://www.cabledatacomnews.com/cmic/diagram.html

Cable Network Architecture: Overview
Typically 500 to 5,000 homes
home
cable headend
cable distribution
Introduction 1-31
cable distributionnetwork (simplified)

Cable Network Architecture: Overview
home
cable headend
cable distribution
Introduction 1-32
cable distributionnetwork (simplified)

Cable Network Architecture: Overview
server(s)
home
cable headend
cable distribution
Introduction 1-33
cable distributionnetwork

Cable Network Architecture: Overview
FDM:
VIDEO
VIDEO
VIDEO
VIDEO
VIDEO
VIDEO
DATA
DATA
CONTROL
Channels
O O O O O O A A L
1 2 3 4 5 6 7 8 9
home
cable headend
cable distribution
Introduction 1-34
cable distributionnetwork

Company access: local area networksp y
company/univ local area network (LAN) connects network (LAN) connects end system to edge routerEthernet:
shared or dedicated link connects end system and routerand router10 Mbs, 100Mbps, Gigabit Ethernetg
LANs: chapter 5
Introduction 1-35

Wireless access networksshared wireless access network connects end system network connects end system to router
via base station aka “access p int”
router
point”wireless LANs:
802.11b (WiFi): 11 Mbps
basestation
( ) pwider-area wireless access
provided by telco operator3G 384 kb3G ~ 384 kbps
• Will it happen??WAP/GPRS in Europe
mobilehosts
Introduction 1-36

Home networksTypical home network components:
ADSL or cable modemADSL or cable modemrouter/firewall/NATEthernetwireless accesspoint
wirelesslaptops
router/f ll
cabled
to/fromcable
wirelessaccess
i t
firewallmodemcableheadend
Ethernet
Introduction 1-37
pointEthernet

Physical Mediay
Bit: propagates betweenTwisted Pair (TP)
two insulated copper p p gtransmitter/rcvr pairsphysical link: what lies b t t s itt &
two insulated copper wires
Category 3: traditional h i 10 Mb between transmitter &
receiverguided media:
phone wires, 10 Mbps EthernetCategory 5: 100Mb Eth tgu ded med a
signals propagate in solid media: copper, fiber, coax
unguided media:
100Mbps Ethernet
unguided media:signals propagate freely, e.g., radio
Introduction 1-38

Physical Media: coax, fibery ,
Coaxial cable: Fiber optic cable:glass fiber carrying light two concentric copper
conductorsbidirectional
glass fiber carrying light pulses, each pulse a bithigh-speed operation:bidirectional
baseband:single channel on cable
high-speed point-to-point transmission (e.g., 5 Gps)
low error rate: repeaters legacy Ethernet
broadband:multiple channel on cable
low error rate: repeaters spaced far apart ; immune to electromagnetic noise
multiple channel on cableHFC
Introduction 1-39

Physical media: radioy
signal carried in electromagnetic
Radio link types:terrestrial microwaveelectromagnetic
spectrumno physical “wire”
terrestrial microwavee.g. up to 45 Mbps channels
LAN (e.g., Wifi)p ybidirectionalpropagation
i t ff t
( g )2Mbps, 11Mbps
wide-area (e.g., cellular) 3G h d d f kbenvironment effects:
reflection obstruction by objects
e.g. 3G: hundreds of kbpssatellite
up to 50Mbps channel (or y jinterference
p p (multiple smaller channels)270 msec end-end delaygeosynchronous versus low
Introduction 1-40
geosynchronous versus low altitude

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-41

Internet structure: network of networks
roughly hierarchicalat center: “tier-1” ISPs (e.g., UUNet, BBN/Genuity/level3, Sprint, AT&T, QWest), national/international coveragenat onal/ nternat onal coverage
treat each other as equals
Ti 1
Tier-1 providers also interconnect
Tier 1 ISPTier-1 providers interconnect (peer)
NAPat public network access points (NAPs)
Tier 1 ISP Tier 1 ISP(p )privately
Introduction 1-42

Tier-1 ISP: e.g., SprintT er ISP e.g., Spr ntSprint US backbone network
Introduction 1-43

Internet structure: network of networks
“Tier-2” ISPs: smaller (often regional) ISPsC i 1 I P ibl h i 2 I PConnect to one or more tier-1 ISPs, possibly other tier-2 ISPs
Tier-2 ISPTier-2 ISPTier-2 ISP pays tier-1 ISP for
Tier-2 ISPs also peer privately with
Tier 1 ISPNAP
tier 1 ISP for connectivity to rest of Internet
tier-2 ISP is t f
each other, interconnect at NAP
Tier 1 ISP Tier 1 ISP
Tier-2 ISP Tier-2 ISP
Tier-2 ISPcustomer oftier-1 provider
Introduction 1-44
Tier 2 ISP Tier 2 ISP

Internet structure: network of networks
“Tier-3” ISPs and local ISPs l h (“ ”) k ( l d )last hop (“access”) network (closest to end systems)
local l llocalISP Tier 3
Tier-2 ISPTier-2 ISP
localISPlocal
ISPlocalISP
ISP Tier 3ISP
Local and tier-3 ISPs are
Tier 1 ISPNAP
customers ofhigher tier ISPsconnecting
Tier 1 ISP Tier 1 ISP
Tier-2 ISP Tier-2 ISP
Tier-2 ISPlocal
connecting them to rest of Internet
Introduction 1-45
Tier 2 ISP Tier 2 ISPlocalISP
localISP
localISP
ISP

Internet structure: network of networks
a packet passes through many networks!
local l llocalISP Tier 3
Tier-2 ISPTier-2 ISP
localISPlocal
ISPlocalISP
ISP Tier 3ISP
Tier 1 ISPNAP
Tier 1 ISP Tier 1 ISP
Tier-2 ISP Tier-2 ISP
Tier-2 ISPlocal
Introduction 1-46
Tier 2 ISP Tier 2 ISPlocalISP
localISP
localISP
ISP

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-47

How do loss and delay occur?How do loss and delay occur?packets queue in router buffers
packet arrival rate to link exceeds output link capacitypackets queue, wait for turn
packet being transmitted (delay)
A
Bpackets queueing (delay)
Introduction 1-48
free (available) buffers: arriving packets dropped (loss) if no free buffers

Four sources of packet delayFour sources of packet delay
1. nodal processing: 2. queueing1. nodal processingcheck bit errorsdetermine output link
2. queueingtime waiting at output link for transmission depends on congestion depends on congestion level of router
A propagation
transmission
Bnodal
i i
Introduction 1-49
processing queueing

Delay in packet-switched networksDelay in packet switched networks3. Transmission delay:
R li k b d idth (b )4. Propagation delay:
d l th f h i l li kR=link bandwidth (bps)L=packet length (bits)time to send bits into
d = length of physical links = propagation speed in medium (~2x108 m/sec)time to send bits into
link = L/Rmedium ( 2x10 m/sec)propagation delay = d/s
N d R
Atransmission
Note: s and R are very different quantities!
A
B
propagation
Introduction 1-50
Bnodal
processing queueing

Nodal delayNodal delayproptransqueueprocnodal ddddd +++=
dproc = processing delayproc p g ytypically a few microsecs or less
dqueue = queuing delayd d tidepends on congestion
dtrans = transmission delay= L/R, significant for low-speed links, g p
dprop = propagation delaya few microsecs to hundreds of msecs
Introduction 1-51

Queueing delay (revisited)Queueing delay (revisited)
R=link bandwidth (bps)R link bandwidth (bps)L=packet length (bits)a=average packet parrival rate
traffic intensity = La/Ry
La/R ~ 0: average queueing delay smallLa/R -> 1: delays become largeLa/R > 1: more “work” arriving than can be serviced average delay infinite!
Introduction 1-52
serviced, average delay infinite!

“Real” Internet delays and routesy
What do “real” Internet delay & loss look like? yTraceroute program: provides delay measurement from source to router along end-end I t t th t ds d sti ti F ll iInternet path towards destination. For all i:
sends three packets that will reach router i on path towards destinationrouter i will return packets to sendersender times interval between transmission and reply.
3 probes
3 probes
3 probes
Introduction 1-53

“Real” Internet delays and routesytraceroute: gaia.cs.umass.edu to www.eurecom.fr
Three delay measements from
1 cs-gw (128.119.240.254) 1 ms 1 ms 2 ms2 border1-rt-fa5-1-0.gw.umass.edu (128.119.3.145) 1 ms 1 ms 2 ms3 cht-vbns.gw.umass.edu (128.119.3.130) 6 ms 5 ms 5 ms
Three delay measements from gaia.cs.umass.edu to cs-gw.cs.umass.edu
g ( )4 jn1-at1-0-0-19.wor.vbns.net (204.147.132.129) 16 ms 11 ms 13 ms 5 jn1-so7-0-0-0.wae.vbns.net (204.147.136.136) 21 ms 18 ms 18 ms 6 abilene-vbns.abilene.ucaid.edu (198.32.11.9) 22 ms 18 ms 22 ms7 nycm-wash.abilene.ucaid.edu (198.32.8.46) 22 ms 22 ms 22 ms8 62.40.103.253 (62.40.103.253) 104 ms 109 ms 106 ms
trans-oceaniclink( )
9 de2-1.de1.de.geant.net (62.40.96.129) 109 ms 102 ms 104 ms10 de.fr1.fr.geant.net (62.40.96.50) 113 ms 121 ms 114 ms11 renater-gw.fr1.fr.geant.net (62.40.103.54) 112 ms 114 ms 112 ms12 nio-n2.cssi.renater.fr (193.51.206.13) 111 ms 114 ms 116 ms13 nice.cssi.renater.fr (195.220.98.102) 123 ms 125 ms 124 ms
link
( )14 r3t2-nice.cssi.renater.fr (195.220.98.110) 126 ms 126 ms 124 ms15 eurecom-valbonne.r3t2.ft.net (193.48.50.54) 135 ms 128 ms 133 ms16 194.214.211.25 (194.214.211.25) 126 ms 128 ms 126 ms17 * * *18 * * * * means no reponse (probe lost, router not replying)
Introduction 1-54
19 fantasia.eurecom.fr (193.55.113.142) 132 ms 128 ms 136 msp (p p y g)

Packet lossPacket loss
queue (aka buffer) preceding link in buffer queue (aka buffer) preceding link in buffer has finite capacitywhen packet arrives to full queue, packet is p f q , pdropped (aka lost)lost packet may be retransmitted by p y yprevious node, by source end system, or not retransmitted at all
Introduction 1-55

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-56

Network ModelsNetwork Models
Using a formal model allows us to deal with g f m mvarious aspects of Networks abstractly.We will look at two popular models
• OSI reference model• TCP/IP model
Both models are based on the concept of Both models are based on the concept of layering.
1-57Introduction

LayeringLayeringDivide a task into sub-tasks and then solve Divide a task into sub tasks and then solve each sub-task independently.Establishing a well defined interface E g f fbetween layers makes porting easier. Major Advantages:j g♦ Code Reuse♦ Extensibility
1-58Introduction

L i E l F d l ELayering Example: Federal ExpressLetter in envelope address on outsideLetter in envelope, address on outsideFedX guy adds addressing information, barcodebarcode.Local office drives to airport and delivers to hub to hub. Sent via airplane to nearest city.Delivered to right officeDelivered to right officeDelivered to right person
1-59Introduction

FedX LayersyLetter Addressed
Envelope
Letter Addressed EnvelopeEnvelope
1-60Introduction

Protocol “Layers”Protocol LayersNetworks are complex!
“ i ”many “pieces”:hostsrouters
Question:Is th h f routers
links of various media
Is there any hope of organizing structure of
network?applicationsprotocols Or at least our discussion
f t k ?hardware, software
of networks?
Introduction 1-61

Why layering?Why layer ng?Dealing with complex systems:
l ll d f explicit structure allows identification, relationship of complex system’s pieces
layered reference model for discussionlayered reference model for discussionmodularization eases maintenance, updating of system
change of implementation of layer’s service transparent to rest of systeme g change in one procedure doesn’t affect e.g., change in one procedure doesn t affect rest of system
layering considered harmful?
Introduction 1-62
y g

Internet protocol stackInternet protocol stackapplication: supporting network
li ti sapplicationsFTP, SMTP
transport: host-host data transfer
application
transporttran p rt h t h t ata tran f rTCP, UDP
network: routing of datagrams from t d ti ti
transport
networksource to destination
IP, routing protocolslink: data transfer between
linklink data transfer between neighboring network elements
PPP, Etherneth i l bit “ th i ”
physical
Introduction 1-63
physical: bits “on the wire”

message
sourceapplicationM
Encapsulationgsegment
datagramframe
pptransportnetwork
linkHtHnHl MHtHn M
Ht M
physicallink
physicalHtHnHl M HtHnHl M
p y
switch
destinationapplicationM
networklinkHtHnHl M
HtHn M
HtHnHl MHtHn M
pptransportnetwork
linkHtHnHl MHtHn M
Ht M physical
router
Introduction 1-64
physical

OSI Reference ModelOSI Reference ModelThe International Standards OrganizationThe International Standards Organization(ISO) proposal for the standardization ofthe various protocols used in computernetworks (specifically those networks usedto connect open systems) is called the OpenS t I t ti R f M d lSystems Interconnection Reference Model(1984), or simply the OSI model.
1-65Introduction

Why a Layered Model?Why a Layered Model?
All People Seem To Need Data Processing1-66Introduction

Layers with Functions Layers w th Funct ons
1-67Introduction

The Seven Layers of the OSI R f M d l Reference Model
The application (upper) layersLayer 7: ApplicationLayer 6: PresentationLayer 5: Session
Th d t fl (l ) lThe data-flow (lower) layersLayer 4: TransportLayer 3: NetworkLayer 3: NetworkLayer 2: Data linkLayer 1: Physicaly y
1-68Introduction

The Application (Upper) LayersThe Application (Upper) LayersApplication
User interfaceUser interfaceExamples – Telnet, HTTP
PresentationHow data is presentedSpecial processing, such as encryptionEx mples ASCIIExamples – ASCII
SessionKeeping different applications’ data separateKeeping different applications data separateestablishes, manages, and terminates sessions between applications.
1-69Introduction

The Data-Flow (Lower) LayersThe Data Flow (Lower) Layers
Transport Reliable or unreliable deliveryError correction before transmitError correction before transmitExamples: TCP, UDP
NetworkProvide logical addressing which routers use for path determinationExamples: IPExamples: IP
1-70Introduction

The Lower Layers (cont )The Lower Layers (cont.)
Data linkCombines bits into bytes and bytes into framesAccess to media using MAC addressAccess to media using MAC addressError detection not correctionExamples: 802.3 (defining the physical layer and
'p g p y y
data link layer's media access control (MAC) of wired Ethernet)
PhysicalPhysicalMoves bits between devicesSpecifies voltage, wire speed, and pinout cablesE l RS 232Examples: RS-232
1-71Introduction

Layering & Headers Layer ng & Headers Each layer needs to add some control information to the data in order to do it’s job. Thi i f i i i ll dd d h This information is typically added to the data before being given to the lower layer.O th l l d li th d t d Once the lower layers deliver the data and control information - the peer layer uses the control informationthe control information.
1-72Introduction

Packet PropagationPacket Propagation
Each router provides its services to support upper-layer functions.pp pp y
1-73Introduction

AddressesAddresses
Each communication endpoint must have an Each communication endpoint must have an address.Consider 2 processes communicating over p mm gan internet:
the network must be specifiedthe host (end-system) must be specifiedthe process must be specified.
1-74Introduction

Addresses at LayersAddresses at Layers
Physical Layer: no address necessaryPhysical Layer: no address necessaryData Link Layer - address must be able to select any host on the network (MAC)select any host on the network (MAC).Network Layer - address must be able to provide information to enable routing (IP)provide information to enable routing (IP).Transport Layer - address must identify the destination process (PORT)the destination process (PORT).
1-75Introduction

Broadcasts
Many networks support the notion of Many networks support the notion of sending a message from one host to all other hosts on the network.A special address called the “broadcast address” is often used.
1-76Introduction

TCP/IP Network Model
Process Process
Interface Protocols
Transport TransportPeer-to-peer
Network Network
pProtocols
Data Link Data LinkData Link Data Link
1-77Introduction

Headers(Encapsulation De-Encapsulation)
DATAProcess ProcessDATA
Transport TransportDATAH
Network NetworkDATAHH
Data Data LinkDATAHHHData Link
Data LinkDATAHH
1-78Introduction

OSI Model and TCP/IP Model OSI Model and TCP/IP Model
1-79Introduction

Differences of the OSI and TCP/IP d l TCP/IP models
TCP/IP combines the presentation and TCP/IP combines the presentation and session layer into its application layer.TCP/IP combines the OSI data link and / mphysical layers into one layer.TCP/IP appears simpler because it has pp pfewer layers.TCP/IP transport layer using UDP does not p y galways guarantee reliable delivery of packets as the transport layer in the OSI
d l dmodel does.1-80Introduction

TCP/IP Protocol GraphTCP/IP Protocol Graph
ICMPICMP&
IGMP
ARP &
RARPRARP
1-81Introduction

PortsPorts
TCP/IP uses an abstract destination point called a protocol port.P id ifi d b i i iPorts are identified by a positive integer.Operating systems provide some mechanism th t t if t that processes use to specify a port.
1-82Introduction

PortsHost AHost A Host BHost B
Process Process
Process ProcessProcess Process
Process Process
1-83Introduction

Port NumbersPort Numbers
1-84Introduction

Chapter 1: roadmapChapter roadmap
1.1 What is the Internet?1.1 What is the Internet?1.2 Network edge1 3 Network core1.3 Network core1.4 Network access and physical media1 5 Internet structure and ISPs1.5 Internet structure and ISPs1.6 Delay & loss in packet-switched networks1 7 Protocol layers service models1.7 Protocol layers, service models1.8 History
Introduction 1-85

Internet History
1961: Kleinrock queueing 1972:
1961-1972: Early packet-switching principles
1961: Kleinrock - queueing theory shows effectiveness of packet-switching
1972:ARPAnet demonstrated publiclyNCP (N k C l switching
1964: Baran - packet-switching in military nets1967: ARPAnet conceived
NCP (Network Control Protocol) first host-host protocol fi il 1967: ARPAnet conceived
by Advanced Research Projects Agency1969: first ARPAnet node
first e-mail programARPAnet has 15 nodes
1969: first ARPAnet node operational
Introduction 1-86

Internet History
1970: ALOHAnet satellite Cerf and Kahn’s
1972-1980: Internetworking, new and proprietary nets1970: ALOHAnet satellite network in Hawaii1973: Metcalfe’s PhD thesis proposes Ethernet
Cerf and Kahn s internetworking principles:
minimalism, autonomy -no internal changes proposes Ethernet
1974: Cerf and Kahn -architecture for interconnecting networks
no internal changes required to interconnect networksbest effort service interconnecting networks
late70’s: proprietary architectures: DECnet, SNA, XNA
best effort service modelstateless routersd li d lXNA
late 70’s: switching fixed length packets (ATM precursor)
decentralized controldefine today’s Internet
architecture
Introduction 1-87
precursor)1979: ARPAnet has 200 nodes

Internet History
Early 1990’s: ARPAnet L t 1990’ 2000’
1990, 2000’s: commercialization, the Web, new apps
Early 1990 s: ARPAnet decommissioned1991: NSF lifts restrictions on commercial use of NSFnet
Late 1990’s – 2000’s:more killer apps: instant messaging, P2P file sharing
commercial use of NSFnet (decommissioned, 1995)early 1990s: Web
h t t [B h 1945 N l
network security to forefrontest. 50 million host, 100
hypertext [Bush 1945, Nelson 1960’s]HTML, HTTP: Berners-Lee
million+ usersbackbone links running at Gbps
1994: Mosaic, later Netscapelate 1990’s: commercialization of the Web
p
Introduction 1-88

Introduction: SummaryIntroduct on SummaryCovered a “ton” of material! You now have:
Internet overviewwhat’s a protocol?network edge core access
context, overview, “feel” of networkingmore depth detail to network edge, core, access
networkpacket-switching versus i i i hi
more depth, detail to follow!
circuit-switchingInternet/ISP structureperformance: loss delayperformance: loss, delaylayering and service modelshi t
Introduction 1-89
history