Building a Security Architecture
-
Upload
cisco-canada -
Category
Technology
-
view
1.480 -
download
2
Transcript of Building a Security Architecture

Jamey Heary
Cisco Distinguished Systems EngineerCCIE 7680
May 2016
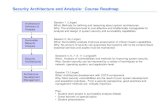
Building a True Security Architecture One Capability at a Time

AgendaCurrent State of Security
Cisco Security
Security as an Architecture- Stories
Summary

State of Security

Cyberwar is Raging!!

Why is the Security Industry Approach Failing?
• It is not a fair fight to begin with
• People, Process and Technology Issues• Hacking People, Malicious Insiders
Security Technology Issues
• Silo’d Point Products. Nothing works together!
• Bolt on security, whack a mole strategy
• We are designing in complexity on purpose!
• Hyper focused on Prevention = anemic detection/scoping & Incident Response
• Lack of real network and security visibility

Architecture Fail
Working together Fail
Bolt-on Fail

Cisco Security
Cisco Security Homepage Cisco.com/go/security

Cisco Security is Rockin it!
Best Security Company, 2016
Cisco’s Security Everywhere …“that’s pretty brilliant”
“Cisco’s strength in its Security business shows it is not an ‘old’ tech company”
“Network security architects … need to adopt new products and/or services that will enable the network to be an integral part of a strategy that focuses on detecting and responding to security incidents.”
“Vendors Like Palo Alto, FireEye Are Selling Legacy Technology”
“Cisco is making all the right moves… software-focused, cloud-friendly portfolio with double-digit growth in Security and acquisitions like OpenDNS”
CIO Survey’s 1st in Customer Preference

Cisco Security Execution and Investment
ThreatGRIDacquired
SourcefireAcquired
Active Threat
Analytics
Black Hat 2014: Talos
Integrated Threat Defense
Vision
AMP Everywhere w/Threat Grid
Incident Response Service
Cisco ASA w/ FirePOWER Services for Mid-Size and
Branch environments
Global Security Sales Organization
Cisco ASA w/ FirePOWER
Services
ACI + FirePOWER Services
RSAC: AMP Everywhere; OpenAppID
Security and Trust
OrganizationSecurity
Everywhere
2013 2016
Portcullis acquired
OpenDNS
Acquired
OpenDNS/
Threat Grid
Integrated
LancopeAcquired
Neohapsis
Acquired
Security Everywhere
Extended
Firepower
NGFW and
Security
Advisory
Service for
Segmentation unveiled
CognitiveAcquired
Invested ~$5B in last 36 months!

2010 2012 2013 2014 20152011
100
98
96
94
92
90
88
86
84
82
NGFW
NGIPS
BDS (Cisco AMP)
NGFW(test average)
NGIPS(test average)
A Track record of Best-of-Breed Security Effectiveness Best of Breed Efficacy in NSS Labs testing Year after Year
Cisco
Test Average

Magic Quadrant Ranking
NGIPS “Leader” since 2006
Email Security “Leader” since 2005
Network Access Control (NAC) “Leader” since 2011
Web Security “Leader” 3 of past 4 years
Network Performance Monitoring and Diagnostics “Leader” (Lancope)
Enterprise Network Firewalls / UTM “Challenger”
SSLVPN (no longer updated) “Leader”

Comprehensive Best-of-Breed Security Capabilities
Cisco Confidential
WWW
DNS
Network Fabric, Threat Intelligence and Analytics
NGFW/
NGIPS
Advanced Threat
and AnalyticsPolicy and
Access
Web and
DNS
Email Endpoint
Capabilities Working Together
Simple | Open | Automated | Effective

The Cisco Advantage
Best of Breed Portfolio
Architectural Approach
Only Cisco can build a true E2E security architecture

Without an Architecture it is a mess of complexity!What makes an Architecture an Architecture?
Just Three things IMHO
1. Capabilities/Solutions (Ideally best of breed)
2. That work well together
3. Effectively

Cisco is building the Industry’s first Threat-Centric Security Architecture
INNOVATION

SAFE Simplifies SecurityMethod Overview
1. Identify your goals
2. Break down your network into manageable pieces
3. Criteria for success of the business (requirements in each PIN/domain)
4. Categorize your Risks, Threats and Policies
5. Build the Security SolutionA. Capabilities Phase
B. Architecture Phase
C. Low-level Design Phase
Format: Whiteboard, Diagrams and/or Presentation

Security Capabilities Design – Branch Example
Host-based Security
Wireless WirelessIntrusionPrevention
Posture Assess-ment
Access Control +TrustSec
Flow Analytics
L2//L3 Network
L2//L3 Network
Host-based Security
Posture Assess-ment
Access Control +TrustSec
Flow Analytics
Web Security Services
Firewall Next-Gen Intrusion Prevention System
Anti-Malware
Flow Analytics
AVC-Application Visibility Control
Threat Intelligence
VPN
Wireless ManagerWeb browsing
Wired Clerk processingcredit card transaction
Wireless Controller
Switch Next-Generation Firewall/Router
To Data Center
To Cloud
WAN
• Use Best Practices to identify applicable security capabilities
• No Products and No Devices in this phase; that comes next
• Identify security capabilities that best mitigate threats, risks and policy

Management
Security
Services and
Applications
Security
Services
Platform
Infrastructure
Element
Layer
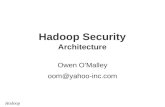
Cisco Platform-Based Security ArchitectureHardware Agnostic, Integrated and 3rd Party Friendly
Common Security Policy & Management
Common Security Policy and Management
Orchestration
Security Management APIs
Cisco APICAPIs
Platform APIs
Cloud Intelligence APIs
Physical Appliance Virtual Cloud
Access Control
Context Awareness
Content Inspection
Application Visibility
Threat Prevention
Device API: OpenFlow, OpenStack, Rest, Yang
Cisco Networking Operating Systems (Enterprise, Data Center, Service Provider, Cloud)
Route–Switch–Compute ASIC Data Plane Software Data Plane
APIs APIs
Cisco Security Applications Third-Party Security Applications
APIs

Web AccessNGIPS Adv. Malw
WAF SaaS VisibAnti-Virus FPCNAC DLPDDoS
Integrated Management
SERVICES
LAYER
ANALYTICS
LAYER
Global & Local Threat Intelligence
Raw Data (Cisco + 3rd Party) Threat Research Analytics Engines
ENFORCEMENT
LAYER
Partnerships Cisco Portfolio
FW/NGFW
TELEMETRY
INTELLIGENCE
Polic
y Auto
matio
n, A
PIs
and C
ontro
ller In
tegra
tion
Network Platforms
Security Platforms
Router / Switches / Server
Cloud Platform
OpenDNS, Email, CWS,
Stealthwatch, Defense Orchestrator
Endpoint Platform
AnyConnect
AMP
Umbrella
Cisco Integrated Threat Defense ArchitectureStuff simply works together

Control
Cisco
AnyConnect®FirePowerCisco CWS
WWW
Cisco WSACisco ASACisco ESA
Visibility
WWW
Web
Endpoints
Devices
Networks
IPS
Difference between a paperweight and a NGFW?
Best-of-Breed Global Threat Intelligence Cloud
24x7x365
operations
40+ languages
More than US$100 million
spent on dynamic research
and development
Info
rma
tio
nA
ctio
ns
Cisco® Collective Security IntelligencePervasive across Portfolio
www.talosintel.com
Threat Intel

See the UnseenUnprecedented Intel Breadth & Depth
Daily Security IntelligenceDaily Threats Blocked
Deployed Security Devices
Daily Malware Sandbox Reports
120TBSecurity
Intelligence
1.6MDeployed
Devices
19.7BThreats
Blocked
150,000Micro-
applications
1,000Applications
93BDaily Email
Messages
35%Enterprise
13BWeb
Requests
150MDeployed
Endpoints
3-5 minUpdates
Cisco Security Intelligence
Global VisibilityGlobal Footprint
5BDaily Email
Connections
4.5BDaily Email
Blocks
14MDeployed
Access
Gateway
75,000FireAMP
Updates
6,000New Clam
AV Sigs
1.1MSandbox
Reports

Cisco Talos Research
Finding Bad Guys,
one 0-day at a time

Prevention Says easy, Does hardCriminals only have to find one vuln; Be prepared
BEFOREDiscover
Enforce
Harden
AFTERScope
Contain
Remediate
Attack Continuum
Detect
Block
Defend
DURING
Shared Context & Security Intelligence

The power of a Cisco Security Architecture
A collection of stories

Malicious Code
Launches
Alice, the contractor,
Clicks a Link or
Malvertising
Ransomware
Payload
Malicious
Infrastructure
Story 1: Ransomware

How Cisco Protects Customers
OpenDNS Next-Gen Firewall AMP Lancope
OpenDNS blocks the DNS request
NGFW blocks the connection/file
Web Security w/AMP blocks the file
AMP for Endpoint blocks the file &
communication back to home
OpenDNS blocks the request
NGFW blocks the connection
Lancope detects the activity

OR
Ransomware
Payload
Bob Downloads
Malicious Email
Attachment

OR
Email Security w/AMP
blocks the file
OpenDNS Email Security AMP Lancope
AMP for Endpoint blocks
the file & communication
back to home

Cisco TrustSecBuilding block of a true security architecture
• TrustSec is a context-based TAG firewall/access control solution
• Cisco ISE is the central policy engine for Trustsec
• Classification of systems/users based on context
(user role, device, location, posture, threat, access method…)
• The context-based classification propagates using SGT tags
• SGT used by firewalls, stealthwatch, routers and switches to make intelligent
forwarding or blocking decisions in the DC
Users,
Device
Switch Router DC NGFW DC Switch
HR Servers
Enforcement
SGT Transport
Fin Servers SGT = 4
SGT = 10
ISE DirectoryClassification
SGT:5

30© 2013-2014 Cisco and/or its affiliates. All rights reserved.
Architecture: Network & Security working together
WLAN
ControllerVPN Remote
Access Access Switch
Firewall
ISE
Policy Server
Business Data
App / Storage
Corp Asset
Endpoints
Corp Network
Device Type: Apple Mac
User: Mary
AD Group: Employee
Asset Registration: Yes
Posture: Compliant
Physical Location: Lobby
Policy Mapping SGT: Employee
Source Destination Action
IP SGT IP SGT Service Action
Any Employee Any Biz Server HTTPS Allow
Any Suspicious Any Biz Server Any Deny
Firewall Rules
• Differentiated Network Access based on Context
• Security Group Tag is added to every packet from
host
• Massive Firewall rule simplification
• Policy Enforcement regardless of IP address/vlan
• Accelerated service provisioning
• Consistent policy assignment regardless of
access method

Architecture: Rapid Threat Containment
WLAN
Controller
Quarantine is based on MAC Address
preventing compromised device accessing
from other location / access methods
NGFW
Policy
Server
Business Data
App / Storage
Compromised
Endpoint
10.10.10.10 (aa:bb:cc:dd:ee:ff)
Corp Network
Source Destination Action
IP SGT IP SGT Service Action
Any Employee Any Biz Server HTTPS Allow
Any Suspicious Any Biz Server Any Deny
Firewall Rules
NGFW StealthwatchEvent: Malware
Source IP: 10.10.10.10/32
Response: Quarantine
OS Type: Windows 8
User: Mary
AD Group: Employee
Asset Registration: Yes
Posture: Non-Compliant
Physical Location: Lobby
MAC Address: aa:bb:cc:dd:ee:ff
Policy Mapping SGT: Suspicious
PXGRID: EPS Quarantine: 10.10.10.10
Access Switch

Story 2: Security Automation – Dynamic Segmentation
32

Enabling Network-Wide Identity & Context SharingCisco Platform Exchange Grid – pxGrid
INFRASTRUCTURE FOR A ROBUST SECURITY ECOSYSTEM
• Single framework – develop once, instead of to multiple APIs
• Control what & where context is shared among platforms
• Bi-directional – share and consume context at the same time
• Extremely Scalable
• Integrating with Cisco SDN for broad network control functions
AD
Single, Pub/SubOpen Framework
Real-time & Secure
pxGridContext
Sharing

NGFW
Story 3: Security Automation – Rapid Threat Containment
VPN
Bob

Cisco NGFW cutting-edge AutomationNot your grandma’s NGFW
Context Rich
Creates a host profile Internally, ISE pxgrid,
3rd party host scan data
Impact Assessment
Threat correlation reduces actionable
events by up to 99%
Automated Tuning
Adjust IPS policies automatically
based on traffic profile
App Identification you can trust
OpenAppID

Demo

• Breaches will happen. Be Prepared.
Scenario
• Zero-day Malware gets through and infects Bob’s wireless PC and then spreads to a single server in the DC he has access to
• AMP sees the unknown file and sends it to the sandbox
• Malware tries to spread from Bob and the server.
Story 4: Security Retrospection– Scope, contain, remediate

Web
Filtering and
Reputation
Security
Intelligence
File Type
Blocking
Application
Visibility &
Control
Indicators of
CompromiseTraffic
Intelligence
File
ReputationCognitive
Threat
Analytics
XXX X
After
www.website.com
X
File
Retrospection
Roaming User
Reporting
Log Extraction
Management
Allow Warn BlockPartial
Block
NGFW/
Meraki
AMP
ApplianceWSA/CWS ESA AMP EndpointAdmin
Cisco Security Architecture
Threats
File
Sandbox
X
AMP Everywhere
Integrated

A New Layer of Breach ProtectionIndustries first recursive DNS Security Solution
Threat PreventionDNS is common to almost all threats
Protects On & Off NetworkNot limited to devices forwarding traffic through on-premiseappliances
Partner & Custom IntegrationsBlock based on malware analysis (Threatgrid, FireEye, etc.)
Block by Domains for All Ports No added latency
Incredibly easy to POV/Deploy30min deploy time
UMBRELLA & Investigate
DNS Protection and Intel

• Previous automated Software defined segmentation drastically limits the attack surface available to the malware to spread
• OpenDNS prevents C&C connection
• Stealthwatch (flow behavior analytics) alerts on C&C and host lock
The Cisco Security Architecture Goes to Work

Card Processor
Hacked
Server
POS Terminals
ASA
Firewall
Private
WAN
(truste
d)
Credit Card
Processor
ASA
Firewall
Stores Data CenterU
pd
ate
s f
rom
PO
S S
erv
er
HT
TP
S
Credit Card Processing HTTPS
Internet
ISR G2
Routers
ISR G2
Routers
Wireless
AP
Wireless POS
C3850
Unified
Acces
s
Network as a Sensor– Host Lock Violation and Suspect Data LossHost Lock Violation - CTD
Public
InternetCompromised
Server
StealthWatch FlowCollector
StealthWatch Management
Console
Cisco ISE
Command and
Collect

• Stealthwatch uses pxGrid to have ISE change the SGT to compromised
• Hosts are now in quarantine and ISE posture assessment can start self-patching
• Within <5mins AMP returns a malicious verdict on the file. All AMP devices are now alerting and dropping file. AMP on endpoint will kill the process and shutdown the malware on infected hosts
• All domains discovered by AMP threatgrid are passed to OpenDNS for blocking providing an umbrella of threat coverage
• Both AMP and Stealthwatch can be used to investigate and scope breach
The Cisco Security Architecture Goes to Work

© 2014 Cisco and/or its affiliates. All rights reserved. Cisco Confidential 43
When Malware Strikes, Have Answers - AMP
Where did it come
from?
Who else is
infected?
What is it doing? How do I stop it?
Device Trajectory
File Trajectory
File Analysis Automated Remediation

Near Future: Threat Centric NAC: ISE 2.1*EndPoints based on Incidents and Indicators

ISE Threat Centric NAC
Network as
a Sensor
and
Enforcer,
and
Integrated
Threat
Defense

Story 5: Cisco ACI Security

EPG
“Internet”EPG
“Web”
Solving the inline problem elegantly– Service graphs & chaining
FireSIGHT Management
CenterAlerts
Network Visibility
Policy Management
Analytics
Remediation
Application Policy
Infrastructure
Controller (APIC)
Service Graph
Contracts
NGIPS/NGFW
Advanced Malware Protection
Policy and events
Basic configuration
and health
Intelligent Remediation

VRF1 pod1net
ASA and Firepower Insertion into ACI
Web host
Web EPG
App host
App EPG
DB host
DB EPG
NGIPS
ASA5525 ClusterRouted L3FW Context
Dynamic Routing to vPCGoTo
ASA virtualRoutedL3FW Context
GoTo
ASAv
Firepower 7010Inline NGIPS
GoThrough
Outside host
Outside Network
NGFW Cluster
FabricPerimeter
Outside
Router
L3out3
ASA DP 1.2.3.4Firepower DP 1.0.1

So much more I’d like to tell you,So many more use cases
Reach out to your Cisco account team

In Summary

Simple, Effective, Integrated & Open Security
Cisco SecurityLeapfrogging the Market

Our Approach is Unique

Strategy is for amateurs.

Execution is for professionals.


Appendix

Cisco’s Comprehensive Best-of-Breed Security Portfolio
WWW
Threat Intelligence and Analytics
Open | Simple | Integrated | Automated
NGFW/
NGIPS
Advanced
Threat
Policy and
Access
Web Email Endpoint
Building Blocks Working Together as an Architecture

10I000 0II0 00 0III000 II1010011 101 1100001 110
Working Together to Create a True Security Architecture
Cisco FTD
ASA w/ FPCisco Web &
Email SecurityCisco
NGIPS
Common Identity, Policy and Context Sharing
Malware Prevention /
Sandboxing
10I000 0II0 00 0III000 II1010011 101 1100001 110
110000III000III0 I00I II0I III0011 0110011 101000 0110 00
101000 0II0 00 0III000 III0I00II II II0000I II0
100I II0I III00II 0II00II I0I000 0II0 00
Context-aware
SegmentationNetwork Integration
Context Visibility
Cisco AMP Client
AMP
OpenDNSTrustsec
ISE
PxgridNaaS
NaaE
Cisco
Pervasive & Integrated
Across the Portfolio
Remediation

Pervasive & Integrated Across Cisco
Across the whole Attack Continuum
Attack Continuum
Network-Integrated,
Broad Sensor Base,
Context sharing and
Automation
Continuous Advanced
Threat Protection, Cloud-
Based Security Intelligence
Leading products working
together as a system
Built for Scale, Consistent
Control, Management
Visibility-Driven Threat-Focused Integrated
BEFOREDiscover
Enforce
Harden
AFTERScope
Contain
Remediate
Detect
Block
Defend
DURING

How to Build a Security ArchitectureSAFE Simplifies SecurityMethod Overview
1. Identify your goals
2. Break down your network into manageable pieces
3. Criteria for success of the business (requirements in each PIN/domain)
4. Categorize your Risks, Threats and Policies
5. Build and model the Security Architecture
A. Capabilities Phase
B. Architecture Phase
C. Low-level Design Phase
Format: Whiteboard, Diagrams and/or Presentation

Reference Architectures

ISE 2.1 Feature List Guest and SSO Enhancements
Microsoft Intune & SCCM Integration
ACS to ISE Migration Features
Smart Licensing
Third party NAD Support
EasyConnect
Streamlined Visibility
Context directory
Customizable Dashboard
Expanded Profiling Capabilities
Threat Centric NAC
TrustSec Workflow Enhancements
TrustSec / ACI Policy Plane Integration
New Posture Compliance Check

Cisco Meraki

Cisco Meraki: Cloud-managed Networks
Meraki MS
Ethernet Switches
Meraki SM
Mobile Device
Management
Meraki MR
Wireless LAN
Meraki MX
Security
Appliances

Meraki MX Security Appliances
6 models scaling from small branch to campus / datacenter
Complete networking and security in a single appliance
Zero-touch site to site
VPN
WAN optimization
NG firewall
Content filtering
WAN link-bonding
Intrusion Prevention
Feature
highlights
Future support for:
• AMP
• IPFIX

Systems Manager Mobile Device Management
Device Management controls iOS, Android, Mac, and Windows devices
Cloud-based - no on-site appliances or software, works with any vendor’s network
Free for up to 100 seats
Centralized app
deployment
Device security
Rapid provisioning
Backpack™ file sharing
Asset management
Feature
highlights
AMP
IPFIX
Future
support

“Yellow” Retail
WAN
Data Centre
“Yellow” Retail
3rd-party supplier
“Blue” RetailStore
Core Network
(Transit)
“Yellow” RetailStore
“Yellow” Retail Router: TAG everything “yellow”
Allow “Yellow” & “Purple”
DC Router:
Allow yellow to yellow Allow blue and
Yellow to purple
Tag “Yellow” apps “Yellow”
Tag “Shared” apps “Purple”
“Blue” Retail Router: TAG everything “Blue”
Allow “Blue” & “Purple”
SharedApps
RetailApps
Simplify: Segmenting traffic with SGTSecurity Domain Level classifications
6
7
“Blue” Retail
WAN
“Blue” Retail
3rd-party supplier
SGACL
SGACLSGACL

Cisco Security Solution PartnersCombined Program – Over 60+ Partners
Combined API Framework and Integration Points
BEFOREPolicy and
Control
AFTERAnalysis
and Remediation
Identificationand Block
DURING
Infrastructure & Mobility
RemediationVulnerability Management
SIEMVisualizationNetwork Access Taps
Custom Detection Incident ResponseFull Packet Capture
IAM/SSO