AXE Testing 1
Transcript of AXE Testing 1

AXE System Testing 1Exchange Data


1
Table of Contents
1. Call Handling in AXE 5
Introduction 5The Data Structure 6Ringing and Supervision 10Chapter Summary 16
2. Size Alteration 17
Introduction 17Initial Setting 18What is a Data file? 21Chapter Summary 24
3. Device and Route Data 25
Chapter Introduction 25Definition of Regional Processor 25Definition of Extension Module 28Definition of Routes 30Chapter Summary 37
4. Analyses, a Survey 39
Introduction 39Analysis of B-number 39Chapter Summary 44
6. Route Analysis 45
Introduction 45Analyses in General 45The Basic Principles of Route Analysis 46Chapter Summary 57
7. Hundred Groups 59
Introduction 59

Exchange Data
2
What is a Hundred Group? 59Specification of Area Code 60Change of Hundred Groups 62Chapter Summary 63
8. Charging 65
Introduction 65Pulse Metering and Toll Ticketing 65Function Blocks in CHS 67Analysis Tables, Survey 68Traffic Activity Analysis 69Charging Case Branching Analysis 71Charging Program Analysis 72Extended Charging Analysis 73Tariff Class Analysis 74Switching Class Analysis 74Tariffs 76Operational Instructions 77Other Charging Related Services 77The Calendar Function 79Chapter Summary 81
9. B-number Analysis 83
Introduction 83Pre-analysis of B-number Information 83Example of an Analysis Table 85
10.End-of-Selection Analysis 97
Introduction 97The Purpose of End-of-Selection Analysis 97End-of-Selection Codes 98The Analysis in Block RA 99Actions Possible to Initiate in the EOS Table 100Branching in the EOS Table 102Commands 103Chapter Summary 103
11.Access Barring and Time Supervision 105
Introduction 105

Table of Contents
3
Access Barring in General 105Destination Codes 105Access Barring Analysis 107Time Supervision in general 109Chapter Summary 110
12.A-number Analysis 111
Introduction 111Pre-Analysis of A-number Information 111Why is A-number Analysis Performed? 112Analysis Results 113Loading and Changing Data 114Chapter Summary 118
13.Equal Access Analysis 119
Introduction 119Survey 119Subscriber category and signalling system 120Carrier Access Code not Dialled 120Carrier Access Code Dialled by the Subscriber 122Example of an Analysis Table 123Commands 123Chapter Summary 124
14.Service Screening Analysis 125
Introduction 125The Analysis 125The Services that can be Barred 126The Commands 126Chapter Summary 126
15.ISDN-Specific Analyses 127
Introduction 127Telecommunication Service Analysis 127Service Indicator Analysis 130Chapter Summary 132
16.Semipermanent Connections 133

Exchange Data
4
Introduction 133General about Semipermanent Connections 133Command Survey 140Chapter Summary 140

5
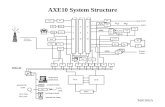
1. Call Handling in AXE
Figure 1.1
1.1 IntroductionThe internal interwork of an AXE exchange is impossible to “see”. This creates a problem as errors in program and data are difficult to find as compared with analog exchanges. This chapter describes how ordinary calls are handled by the software of AXE. Although the description is simplified, the information given will greatly facilitate the handling of exchange data.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the block interwork during an internal call
• describe the block interwork during an outgoing call using MFC and CCITT No 7 signalling.

Exchange Data
6
1.2 The Data StructureBefore studying the traffic handling inside the AXE software, we must take a look at the internal data structure. The data structure and the interrelationship between data and hardware are important features of the AXE software. Please study Figure 1.2.
Figure 1.2The structure of one function block
If a block has hardware, like the block LI in the figure, there are of course hardware circuits inside the magazines. The regional software in the RP or the EMRP controls the hardware and takes care of the routine tasks. Any changes in operation points are reported to the central software by means of a signal that includes information about the affected device.
The central software contains a program and some data. The data is divided into records where each record represents one hardware circuit. Each record contains variables which are used to store data about the device. Information like state of device and number of disturbances is stored in the variables. The number of records in the data of block LI must be equal to the number of hardware devices.
Blocks (such as RE and CJ) that do not contain hardware may also have records. In this case one record is used to store the call data for one call. The number of records required inside the blocks is dependent on the size and the traffic volume of the exchange. If the block RE contains 100 records, it can take part in the setting-up of 100 simultaneous calls.
When the different traffic cases are described in this chapter, each block is illustrated by a box with the block name inside. The box represents the program and the data of the block. However, it must be noted that one record inside the block is specially reserved for the call. All records belonging to the same call are linked to each other by means of pointers. The pointers point from one record to another, creating “chains” of records
Hardware
LIC
Regional software
LIR
Central software
LIU
Program Data
One recordper LIC

Call Handling in AXE
7
inside the software. These chains must be intact as long as a call is established. During disconnection of the call, the chains are broken and the participating records are set to idle again.
1.2.1 Connection of RegisterIn this document the call handling in AXE is described by means of a number of figures with explanatory text. Only the hardware and the central software of the blocks are shown. Please study Figure 1.3.
Figure 1.3Connection of register and sending of dial tone
When a subscriber lifts the handset, this is detected by the line interface to which he/she is connected. The regional software of block LI sends a message to the central software indicating the event. Next, block CJ is contacted in order to coordinate things inside subsystems SCS and SSS. The following is then done in the software (the numbers refer to the figure):
1. Block CJ, combined junctor, sends a signal to block SUA, subscriber analyses, and block SC, subscriber categories. SC is the block that stores all the categories of all subscribers in the exchange and block SUA handles analyses and some logic functions related to the traffic handling. SC checks if the subscriber is allowed to make a call and if subscriber services are activated (e.g. fixed destination call).
2. Some categories relating to analyses (e.g. origin for charging and routing analysis) are fetched in SC and then sent to block RE, register. This block will coordinate all work until the call has been established. One record in block RE is then seized for the call. This record will, among other things, store all digits dialled by the subscriber.
3. When a register record has been seized, block CJ is noted about this event. CJ can now order other blocks inside SCS and SSS to prepare for the call.
LI TS KR
CJ
RE
LICEMTS
KRC
LI TS KR
CJ
RE
1
2
3
4
Subscriber Switching Subsystem
Subscriber ControlSubsystemTraffic ControlSubsystem
SUA/SC

Exchange Data
8
4. A KRC has previously been connected to the LI via the time switch. A dial tone is now ordered from the hardware. The tone is generated in the time switch and sent towards the subscriber.
In the next phase, the subscriber dials the digits. Figure 1.4 shows how a digit is handled inside the software of the system.
Figure 1.4Reception of a digit
1. The digits are received by the KRC (key-set code reception circuit) which sends them to the central software of the block. Block KR will then send them to CJ which supervises the time between the dial tone and the first digit. In some cases, subscriber services should be activated if no digits are dialled.
2. CJ does not store the digit but sends it immediately to RE for further handling.
3. The register record reserved for the call stores each incoming digit and immediately sends them, one by one, to block DA (digit analysis) for analysis. Block DA delivers analysis results depending on the digits dialled and the data inside the B-number analysis table. A table is specified for each exchange because the routing plan and numbering plans determine its contents. Examples of analysis results are information about how the call is to be routed and charged, and in some cases how the number is to be modified.
1.2.2 Identification of B-subscriberWhen all digits have been received, the register knows that the call is a terminating call in the exchange. This information has been delivered as an analysis result from block DA after the analysis of some digits. Figure 1.5 shows the sequence when the B-subscriber is identified and seized.
RE
LI TS KR
CJ
RE
LICEMTS
KRC
LI TS KR
CJ
RE2
3
1
Subscriber Switching Subsystem
Subscriber ControlSubsystemTraffic ControlSubsystem
DA

Call Handling in AXE
9
Figure 1.5Identification and seizure of B-subscriber
1. The register (block RE) orders blocks SUA and SC to check if the B-subscriber has any subscriber services activated. Examples of services checked are all variants of diversion services (e.g. immediate diversion).
2. If no services are activated, the state of the subscriber is checked. Block LI is requested to seize the B-subscriber if he/she is idle at the moment.
3. If the B-subscriber was idle, the state changes to busy and a signal is sent back to SC. If the subscriber was busy, some subscriber categories had to be checked in SUA/SC. Services like transfer on busy and call waiting are affected by the state “busy”.
When the register gets the signal indicating that the B-subscriber is seized, the call establishment can continue.
LI TS KR
CJ
RE
LICEMTS
KRC
LI TS KR
CJ
SUA/SC RE1
23
Subscriber Switching Subsystem
Subscriber ControlSubsystemTraffic ControlSubsystem
LIC
A
B

Exchange Data
10
1.3 Ringing and SupervisionFigure 1.6 shows the last part of the call establishment.
Figure 1.6Through-connection to the B-subscriber
1. Block RE orders CJ to seize a record for the B-subscriber and to set up a connection through SSS. Note that there is one CJ record for the A-subscriber and one for the B-subscriber.
2. Block JT, junctor terminal, is requested to seize a channel from the subscriber stage to the group switch. A channel is reserved for both the A and B-subscriber.
3. Block TS, time switch, is ordered to connect the subscribers to the selected JT channels. A path is established for both the A and B-subscriber.
4. The charging has to be prepared for and block CHMON, charging monitoring, is included in the call. This block co-ordinates the functions inside the subsystem CHS. Depending on the charging method used, various blocks in subsystem CHS are included in the call.
5. Block GS, group switch, is requested to set up a path between the two selected JT-channels.
6. All preparations are now completed and block LI is requested to send a ring signal to the B-subscriber. A ring control tone is sent to the A-subscriber at the same time.
When the call has been established, the register (block RE) has fulfilled its task and can leave the call. The call will be handed over to block CLCOF, which will supervise and disconnect it (disconnection means that all the
LI TS KR
CJ
RE
LICEMTS
LI TS JT
CJ
RE
23
Subscriber Switching Subsystem
Subscriber ControlSubsystemTraffic ControlSubsystem
LIC
A
B
KRGS
KRCHMON
EMTS
GS
Group Switching Subsystem
Charging Subsystem
14
56
SUA/SC

Call Handling in AXE
11
devices involved resume idle state). The charging is handled by block CHMON. Figure 1.7 shows the principle.
Figure 1.7Call supervision by block CLCOF and charging coordinated by block CHMON
1.3.1 Outgoing Call, Route AnalysisAn internal and an outgoing call start in exactly the same way. A subscriber dials some digits which are stored in the register and sent for analysis in block DA. The point where an outgoing call starts to differ is when the B-number analysis in block DA indicates that the call is an outgoing call. This is indicated to the register by means of a so-called routing case. The routing case must be further analysed in order to see which outgoing route should be selected. The outgoing route to be used may depend on a large number of factors such as subscriber categories and time and date. Figure 1.8 shows the block interwork during the analysis of the routing case.
LI TS KR
CJ
LICEMTS
LI TS JT
CJ
CLCOF
Subscriber Switching Subsystem
Subscriber ControlSubsystemTraffic ControlSubsystem
LIC
A
B
KRGS
KRCHMON
EMTS
GS
Group Switching Subsystem
Charging Subsystem

Exchange Data
12
Figure 1.8Analysis of routing case
1. A digit is sent to the register from block CJ.
2. The digit is as usual sent to block DA for analysis. The result of the analysis is a routing case (RC). Each RC has a number which defferentiates it from other RCs. The RC is returned to the register for further processing.
3. Block RA, route analysis, is requested to analyse the routing case. Depending on a large number of factors, which will be studied in chapter 6 of this book, an outgoing route is selected. The identity of the route is sent back to the register together with some more parameters used to control the signalling.
1.3.2 Connection of Code SenderThe call establishment is completely controlled by the register which has information about routes, categories etc. For the establishment of calls to other exchanges, the register is controlled by the so-called sending program. The sending program was delivered from block RA at the same time as the identity of the outgoing route was indicated. The sending program tells the register when to seize the route, when to call the other exchange and finally which digits to send to the other exchange. Figure 1.9 shows the next part of the setup phase for an outgoing call.
LI TS KR
CJ
SC RE
LICEMTS
KRC
LI TS KR
CJ
DA RE1
2 3
Subscriber Switching
Subscriber Control
Traffic Control RERA

Call Handling in AXE
13
Figure 1.9Seizure of route and connection of Code Sender
1. The register requests block BT to select an outgoing device in a specified route. BT stands for both-way trunk and this is the block that handles the channels in the PCM systems from a traffic handling point of view.
2. When a device in the route has been selected for the call, RE orders block GS to reserve a path from the JT channel to the outgoing device. The path is only reserved in software.
3. Block BT checks the data related to the route and finds that a code sender must be used for the register signalling. Block CSR, code sender and receiver, is requested to select a deviceto be used as a code sender.
4. When a device has been selected, it must be connected to the selected channel. The tones in this signalling system are sent “in band”, which means that the information is sent on the speech channel before the speech. Block CSR will therefore request block GS to setup a path immediately.
5. All preparations for the sending of the first digit are now completed. Block CSR orders the regional software of the block to send the digit from the hardware. The digit, which is coded by two mixed tones, is sent through the group switch to the selected channel. This channel will later on be used for the speech connection as well.
6. Block BT request block ET to send a line signal to the other exchange. The signal is a “seizure signal” telling the other exchange that a call is coming. The seizure signal will be sent on channel 16 if a 32-channel PCM system is used.
LI TS KR
CJ
SC RE
LI TS GS
CJ
SC RE
23
Subscriber Switching
Subscriber Control
Traffic Control
LIC
KRET
EMTS
GS
Group Switchin
Trunk and
Signalling
1
56
ETC
CSR
KRBT
KRCSR4

Exchange Data
14
In the other exchange, the line signal on channel 16 will be detected by block ET, and block BT will be notified. Block BT will request a code receiver and the CR is connected through the group switch. After that, a register record is reserved for the call. The CS in exchange A can now “talk” to the CR in exchange B. Please study Figure 1.10.
Figure 1.10Connection of code receiver in exchange B
1.3.3 Outgoing call using CCITT No. 7If another signalling system is used for the call, the signalling will be slightly different. In this chapter, a call with CCITT No. 7 will be studied. Figure 1.11 shows the signalling network used.
Figure 1.11Example of signalling network when CCITT No 7 is used
As Figure 1.11 shows, the speech and the signalling information are sent on separate routes. The STP, signalling transfer point, will read the destination address included in the message and send it on to exchange B. Figure 1.12 shows the block interwork for an outgoing call.
GS ETC ETC GS
CSR
Exchange A Exchange B
CSR
STP
A BSpeech
Signalling

Call Handling in AXE
15
Figure 1.12Outgoing call with ITU-T No. 7
1. The register orders selection of an outgoing device in the route indicated by the route analysis (the same principle as in Figure 1.8).
2. As the call is an outgoing call, block C7BTC requests “help” from block C7OTH (C7 outgoing traffic handling).
3. The register delivers all call data to block C7OTH. The data includes the A-number, and B-number and the category of the A-subscriber.
4. When all data has been assembled, a message is sent to block C7DR2 (C7 distribution and routing). This block contains tables of all the defined destinations in the signalling network. In this case, the “address” of the message will be exchange B (see Figure 1.11).
5. The message, which now has the standardized ITU-T No 7 format, is sent to block C7ST2 (C7 signalling terminal). This block “owns” the hardware, i.e. the signalling terminals used to send the messages. The message will be sent to the signalling transfer point and then rerouted to exchange B. The rerouting in the STP is handled by block C7DR2.
LI TS KR
CJ
SC RE
LI TS GS
CJ
SC RE
3
Subscriber Switching Subsystem
Subscriber ControlSubsystemTraffic ControlSubsystem
LIC
C7BTC
EMTS
GS
Group Switching Subsyste
Trunk and Signalling Subsystem
1 5
6
ETC
ST-7
4
ETC
PCDD
To STP
Speech
C7OTH
C7ST2
C7DR2
Common ChannelSignalling Subsystem
2

Exchange Data
16
1.4 Chapter SummaryFrom this chapter you should remember these points:
• Records inside the blocks are reserved for each call.
• The records reserved for a call are linked to each other by means of pointers.
• The pointers create chains in the software of the system.
• The register, block RE, is responsible for the establishment of all types of calls.
• Block CJ coordinates events inside subsystems SCS and SSS.
• Block CLCOF supervises and disconnects established calls.

17
2. Size Alteration
Figure 2.1Chapter Objectives
2.1 IntroductionSize alteration is the name of the function used to change the file sizes in the data store of the central processor. The changes are normally initiated by a change in the size of the exchange or in the traffic intensity of the exchange. Examples of changes in the size of the exchange are addition of more subscribers or more trunk lines added. If the traffic intensity is increasing, the extension of the number of register individuals have to be changed. This chapter describes the commands used to perform size alterations in the AXE software.
When a size alteration is made, the affected part of the AXE system is the data store in the CP. In this store, the data related to all the blocks are stored. The size of the data, i.e. the number of data individuals, is changed by the function size alteration. The program store is not affected by this function as there is no change of the function of the system. If new or modified functions are loaded into the exchange, the process referred to as function change is used. Figure 2.2 shows the difference between these two methods.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the main principles of size alterations
• perform size alterations
• generate and interpret printouts related to size alteration
• explain the use of size alteration events
• find the correct size alteration events in the B-module.

Exchange Data
18
Figure 2.2The parts in the exchange affected by the functions Size Alteration and Function Change
2.2 Initial SettingThe initial size of the data records in the data store is set when the exchange is installed. The information about the sizes to set originates from the customer in the form of filled in data forms or similar information. The information is referred to as exchange requirement. The document exchange requirement is the input to the department inside Ericsson that produces the initial data. The process is referred to as data transcript. One of the activities included in the data transcript, is the setting of the file sizes in the software of the exchange. The output from the data transcript is a command file with commands related to size alteration and also other functions described later on in this Module. The commands with size alterations are loaded as one of the first files when loading the exchange data. This has to be done because no other data can be loaded before the file sizes in data have enough space for storage of the data. Figure 2.3 shows the principle.
Figure 2.3The production of the initial exchange data for one exchange
Central ProcessorProgram
StoreDataStore
FunctionChange: Size
Alteration:New or modifiedfunction More data
created forone function
Customer Ericsson
ExchangeRequirement
Data Transcript
PTT
Size of exchange:- number of trunk lines- number of subscribers- traffic intensity- services
Command file with the initial exchange data. Commands for Size Alteration included.

Size Alteration
19
2.2.1 Extension with HardwareIf the number of trunk lines in an exchange is extended, there is usually requirements that more hardware is installed as well. This means that more ETC boards (or magazines for older types of ETCs) have to be installed in the exchange. For each channel in the PCM system (24 or 32 channels per ETC), there is some data in the data store that defines e.g. the state of the device and to which route it belongs. This fact, that there is data related to each hardware unit, require that the file sizes in the data store is changed by means of a size alteration. Please study Figure 2.4.
Figure 2.4Extension of hardware requires change of file sizes in the data store
When the hardware is installed in the exchange, various operational instructions have to be used depending on hardware type (the names of the instructions are “Connection of ....”). These operational instructions describe the commands and actions required to connect the new hardware in software.
2.2.2 Extension by using more Software IndividualsIn most cases of size alteration, only software is affected. Here are some examples of changes that only affect software:
1. If the traffic intensity (Erlang) is increasing in the exchange, more Register individuals are required to handle more simultaneous call setup. In this case, no additional hardware is required as the block RE is implemented in software only.
2. If more subscribers would like to have a certain subscriber service (e.g. call transfer), more data individuals are required in order to handle more call transfers at the same time. Also the storage capac-ity of the service must probably be increased (e.g. the C-number in case of call transfer). Also in this case, only software is affected as all subscriber services are implemented in software only.
RP
CP
New hardware
Existing hardware
Data Store
More data required

Exchange Data
20
3. Analysis tables have space for a limited number of analysis cases. The size of the analysis tables are set by means of a size alteration. Examples of such tables are the analysis table for the B-number analysis and the charging analysis table. If more analysis cases are to be introduced (e.g. more charging cases or new B-number series), a size alteration is used to create more space in the table.
Figure 2.5 gives an example of a change when only software is affected.
Figure 2.5New register individuals are defined by means of a Size Alteration
If only a size alteration is to be made in the exchange, the operational instruction “Size Alteration of Data Records” has to be followed. Note that this instruction also will be used for reduction of data files.
Program Store Data Store
Program ofblock RE
Register individualsin Data Store
New individualscreated

Size Alteration
21
2.3 What is a Data file?A size alteration is affecting a data file consisting of data records (referred to as an individual in some cases). What, then, is a data record? Please study Figure 2.6.
Figure 2.6Records and data files in one function block
The hardware located in the EM’s must have some data related to it in the data store. For the same type of hardware in one block, the same type of data can be used. At design, one record is described by the designer of the function block. The “record” is the data required for one device. If the block contains 16 devices for one exchange, the number of records must also be 16. These 16 records make up one “data file” and the size of that file is in this example 16. If more hardware devices are to be added to the block, a corresponding change of the number of records in the data file is required. The change of the number of records is made by using commands belonging to the function size alteration. As already mentioned, most cases of size alteration involves no hardware. Only the file size in the data store will have to be affected in order to increase the number of devices.
It should also be noted that one function block usually contains more than one file. As an example, one type of record is used to store data related to the devices inside the block and one type of records is used to store the data related to the routes defined in the block. This means that the block has two different files in the data store that can be changed independently of each other.
2.3.1 The use of Size Alteration EventsIn order to find the block or the blocks that are affected by a size alteration, the AXE system uses a numbering of the size alteration cases.
Variable 1
Variable 2
Variable n
GS
FileOne record per device
Logical data structure:
New hardwaremeans newrecords in data

Exchange Data
22
This number is referred to as “size alteration event” or just SAE. The SAE is used as a parameter in all the commands related to the size alteration function. Also the documentation in the B-module uses the SAE number in various documents and lists.
There are two different types of size alterations in the AXE:
• Global size alteration eventThese events will affect files in more than one block. An example is the number of routes in the exchange. Several blocks in the system store information about each route and all these blocks require the same file size (e.g. blocks for statistics and supervision).
• Local size alteration eventThese events will only affect one block in the exchange. Examples of such events are the number of devices inside one block.
The size alteration events (the numbers) are allocated in a special way in order to make it possible for the system to know which system (APT or APZ) and which type of event it is (local or global). The following numbering has been used inside the system:
• Global events:
− APT: 000-299
− APZ: 300-499
• Local events:
− APT: 500-799
− APZ: 800-999
This means that all SAE higher than the number 499 are local events. This is important to know as the parameters included in the commands related to the function are affected. More about that in next chapter.
2.3.2 Commands Related to Size AlterationThere are only three commands related to the function for size alteration. The three commands are:
• SAAIIThe command is used to increase the files in a size alteration event.
• SAADIUsed when decreasing the file sizes in one SAE.
• SAAEPUsed when printing the number of individuals currently defined for the SAE.
The two commands for changing the file size (SAAII and SAADI) have an optional parameter “BLOCK=block”. This parameter must be used if the SAE is a local event (499). The reason for having this parameter is that the local SAEs (e.g. SAE=500) use the same SAE number for several blocks. As an example, all the blocks that have telephony devices use

Size Alteration
23
SAE=500 for changing the number of devices in the block. If the operator wishes to change the number of BT1 devices, the format of the command is:
SAAII:SAE=500,BLOCK=BT1,NI=XX;
The parameter “NI=XX” in the command is the parameter indicating the total number of records after the change. Note that the total number is stated, not the number of records added.
When the change has been ordered by the operator, the system will reallocate the data store in order to create more space for the variables included in the records. This reallocation will take some time to perform as much of the data has to be moved in the store. The work has to be done at a low priority in the system as traffic is handled at the same time. The time is takes i usually 5 to 10 seconds but it could take several minutes for a global event affecting several blocks. The result of the size alteration is sent to the operator in the result printout called DATA FILE INFORMATION. Figure 2.7 shows the format of the printout.
Figure 2.7The result printout for the Size Alteration
How, then, should the SAE numbers be found in the exchange library? This number is required in all the commands for the Size Alteration Function and it must be found before the work can start. There are two ways to find the SAE number:
1. In the application information of the block affectedThis method is used if the block is known and the SAE number is wanted. In the application information, all the SAE numbers related to the block can be found.
2. In the parameter list in the last part of B14This list is sorted in numerical order starting with SAE=0. The list contains information on the block/blocks affected by the event as well as information about how to calculate the number of individu-als. This method is used when the SAE number is known and the block or the information about the event is wanted.
Figure 2.8 shows the principle.
DATA FILE INFORMATION
SAE BLOCK NI NIU FCODE500 UPDN3 128END

Exchange Data
24
Figure 2.8Two ways to find the SAE numbers in the exchange library
2.4 Chapter SummaryFrom this chapter you should remember these points:
• Size alterations have to be made if more devices are connected to the exchange or if the traffic intensity is increasing.
• The function creates more records in the data store for a specific function.
• The global SAE affect more than one block and requires no parameter BLOCK=block in the commands.
• The local SAE affect one block only and requires the parameter BLOCK=block in the commands.
• The application information of the block indicates the SAE numbers for the block.
Block is known SAE number
ApplicationInformationfor the block
(B14)
SAE number
Parameter List(B14)
Block (andmore information)is known

25
3. Device and Route Data
Figure 1.1Chapter Objectives
3.1 Chapter IntroductionAll hardware in the AXE system are controlled by regional processors and stored in extension modules. In case of extension in the exchange, new processors and extension modules have to be defined. Routes are used to interconnect exchanges and to define entry points to functions inside the AXE exchange. Routes must first of all be defined in data by means of commands. When they are defined, the function of the route can be changed by adding route data with commands. This chapter shows the commands required for defining routes as well as some useful printouts related to routes.
3.2 Definition of Regional ProcessorIf the exchange is extended with new hardware, there might be a need for new regional processors for the control of the new equipment. However, if some RPs have spare capacity (not all EMs used), that RP pair can in some cases be used for the extension. Figure 1.2 shows how the regional processors and the extension modules are interconnected to each other.
Chapter Objectives
After completing this chapter, you will be able to:
• define a regional processor
• define an extension module
• define a new route and modify existing route data
• connect devices to routes and generate and interpret printouts of the specified data.

Exchange Data
26
Figure 1.2Extension of the control system of AXE
First of all, the RP pair must be connected in hardware and the power must be connected to the magazine. However, this is not enough as the RP pair must be defined in data as well. This means that some initial data is loaded into the system and that the parts that take care of the maintenance of the RPs, are noticed of there location. The location of the RP pair is determined by an address strap on one of the boards in the RP and that address must always be used when using commands related to the RP. The operational instruction “Connection of RP” describes the actions required for the definition. The first command used for the definition of an RP pair is the command EXRPI. The command has the following parameters:
EXRPI:RP=rp,RPT=rpt,TYPE=type;
The parameters RP and RPT are used to indicate to the system the addresses allocated to the RPs with the address strap. The parameter TYPE is used to indicate the version of the RP as both old and new RPs can be connected to the same exchange. The command description of the command EXRPI contains a list with valid RP types.
When the RP pair has been defined, next step will be to define which software units (programs) that should be loaded into the RP pair when they are deblocked. The programs loaded into the RP should be some operating software and the regional software of the blocks connected to the RP (e.g. regional software of block BT is referred to as BTR).
The command used to define that is EXRUI. This command will build up a table inside the APZ related to each RP pair. The table can be used by the APZ when reloading them, e.g. at deblocking. At deblocking, the software indicated in the table is sent to the program store of the RPs in the RP pair. This also means that a copy of all regional software units must be available in the CP as a backup. In those cases when new equipment is installed in the exchange (e.g. a new type of BT devices), the new RP program has to be loaded into the CP by means of command LAEUL.
EM
RP
CentralProcessor
RP
EM
EM
RP RP
EM
RP Pair NewRP Pair

Device and Route Data
27
The parameters included in command EXRUI are RP and SUNAME or SUID. The parameter RP is used to indicate one of the RPs in the RP pair (only one has to be specified). The parameters SUNAME and SUID are used to indicate the name or the identity of the software units that should be included in the RP pair. Which parameter to use is determined by the following:
• SUNAMEThis parameter is used if there is only one version of the software unit loaded in the CP. An example of a software unit name is BTR.
• SUIDIf there are more than one version of the RP program loaded into the CP, this parameter must be used to indicate which version to use. This parameter is used if the version of a regional software unit is changed because of software update or function change. An example of the parameter is “5/CAA1052105/1R2A02”. The correct identities can be printed by using command LAEUP.
When the loading table has been defined, perhaps using several commands EXRUI, the RP pair can be put into service by deblocking them. The deblocking is made by using command BLRPE and the command includes first a test of the RP and then a reload of the software units specified in the table. Please study Figure 1.3.
Figure 1.3The new RP programs are loaded into the CP and defined for the RP pair
All the data related to an RP pair can be removed by using the command EXRPE. This command is used if the RP pair is to be removed from the exchange. When the data is specified, the command EXRPP can be used to check the data specified. Please study Figure 1.4.
RP RP SP
PS12
PS12
CP LAEUL:...;Already loadedRP program
New RP program
Loading tabledefined byEXRUI
Loading of RPduring deblocking

Exchange Data
28
Figure 1.4Printout of RP state
3.3 Definition of Extension ModuleWhen the new RPs have been defined, it is time to define the equipment they should control. As probably known, this equipment is located in extension modules using the same type of interface towards the RPs. Figure 1.5 shows the principle of connecting two different types of EMs to the EM bus.
Figure 1.5The two types of extension modules available in AXE
When the EMs are defined, data in both the APZ and in the blocks that own the hardware is updated with various type of information. The data in the block that controls the hardware, is updated with information about the address of the hardware (RP and EM addresses). This information is required when sending signals to the hardware for initiating functions in the hardware.
<EXRPP:RP=36;
RP DATA
RP STATE TYPE TWIN STATE DS MAINT.STATE 36 WO RPM6A 37 WO 4096 IDLEEND
Extension ModuleExtension Module
1 EM per board
RP4Boards with EMinterface anddevices
Boards with EMinterface anddevices
RPB
1 EM per board1 RP-pair
RP4
RP/EM-busin backplane
RP/EM-busin backplaneof magazine
EM-bus
Or:

Device and Route Data
29
The command used to define the EMs is EXEMI and the following parameters are included for a normal definition:
EXEMI:RP=rp,RPT=rpt,EM=em,EQM=eqm;
• RPIndicates the RP that controls the EM in normal cases.
• RPTIndicates the stand-by RP. This RP must be the twin RP in an RP pair.
• EMAddress of EM (address strap is used)
• EQMUsed to indicate the equipment type and identity of the devices in the EM. Example: EQM=UPDN3-32&&-63.
When the EM has been defined, it can be deblocked by using command BLEME. This means that the EM is put into service from a control point of view. The devices in the EM is probably still blocked as more data related to the devices have to be specified.
If an EM is to be removed from the exchange, the command EXEME is used. When the data has been specified, the print command EXEMP can be used. Figure 1.6 shows an example of a printout with command EXEMP.
Figure 1.6Printout of state of extension modules
<EXEMP:RP=36,EM=ALL;
EM DATARP TYPE EM EQM TWIN CNTRL PP STATE 36 RPM6A 0 TSM-0 37 PRIM WO 36 RPM6A 1 TSM-0 37 PRIM WO 36 RPM6A 2 TSM-1 37 SEC WOTWIN 36 RPM6A 3 TSM-1 37 SEC WOTWIN 36 RPM6A 4 TSM-2 37 PRIM WO 36 RPM6A 5 TSM-2 37 PRIM WO 36 RPM6A 6 TSM-3 37 SEC WOTWIN 36 RPM6A 7 TSM-3 37 SEC WOTWINEND

Exchange Data
30
3.4 Definition of RoutesBefore we discuss how routes are connected and defined in the software of AXE, the route concept in AXE should be studied. In AXE, the concept “route” has been extended slightly if compared with other, analog, systems. There are basically three types of routes in the system:
1. External routes, e.g. routes to other exchanges
2. Internal routes, e.g. routes to code senders and announcing machines
3. Software routes, e.g. routes to subscriber services or routes for register individuals.
Figure 1.7 shows the three variants of the route concept.
Figure 1.7The three types of routes used in AXE
All three types of routes require “route data” in order to function in a specified way. The route data is as the name says, data related to a route in the exchange. Examples of route data for an external route is type of signalling system used, function of route (incoming or outgoing) and the number of devices connected to the route. The route data is stored in the block to which the hardware belongs. The operational instruction “Connection of routes for BT” is one of the instructions available that describes the commands that should be used. In this chapter, only the commands and most common parameters are described.
How, then, is the route data defined in the exchange? The answer is the two command EXROI and EXRBC. The two commands have the following meaning:
EXROI:R=r,DETY=dety,FNC=fnc;
The command is used to initiate the route for the very first time. The parameters included in the command are (not all shown):
AXEHardware
SoftwareCTR RE
Internalroutes
Softwareroutes
External routes
Exchange A
Exchange B
ETC
ETC
CSR
DAM

Device and Route Data
31
• Route nameThis parameter gives the route a name consisting of up to 7 letters. Characters like #, % and + can be used in the route name to distinguish between incoming and outgoing routes.
• DETY, device typeThe device type is indicating the type of devices used in the block. The parameter should be the same as the block name of the block used for the route (e.g. BT1).
• FNC, function codeThe function code is used to indicate the function of the route. The meaning of the parameter must be fetched from the application information of the block indicated in DETY. For external routes, the parameter is usually used to indicate the traffic direction of the route.
EXRBC:R=r,....;
This command is used when more route data is to be assigned to the route. Also existing routes can be changed by using this command. The command has several parameters (20) of which only a few are explained here:
• R1, register signalling routeThis parameter is used to indicate if another route must be used for the register signalling. If MFC signalling is used, the route name of the code sender route is indicated here. Figure 1.8 shows the principle.
Figure 1.8Register signalling route defined with parameter R1
ETC
CSR
R1=CSROUTE
GS Route usingMF signalling

Exchange Data
32
• RG, route groupThe route group parameter is used to prevent the traffic from one exchange to be returned to the same exchange (also referred to as “return blocking”). By giving all routes to and from the same exchange, the same RG value, the system will not route the traffic back to thesame destination. Please study Figure 1.9.
Figure 1.9Return blocking defined with parameter RG
• RO, Origin for route analysisFor incoming routes, this parameter can be used if the route analysis should be made differently for this route compared with others. More about that in the chapter describing route analysis.
• PRI, prioritySome incoming routes can be given priority. This parameter can be used in various analyses in the exchange.
• MB, modification of B-numberThis parameter can be used to add or delete digits from the B-number.
• TTRANS, transmission characteristicsThe parameter is used to specify if a digital 64kbit/s connection can be established or not. This type of information is vital to ISDN calls. The parameter can also be used to specify n x 64 kbit/s.
As already mentioned, there are several other parameters included in the command EXRBC. Please study the command description and the application information for the blocks concerned for more details.
When all the route data has been specified for the route, and if the route should be put into service, it should be deblocked by using the command BLORE. Note that only outgoing routes can be blocked or deblocked with this command. Incoming routes are blocked by blocking all the devices in the route. The command BLORP is used to check if any outgoing routes are blocked.
Exchange A
Exchange B
Exchange C
Congestion
Notpossible
RG=5
RG=6
RG=5

Device and Route Data
33
3.4.1 Connection of Devices to the RouteWhen all the route data has been specified, it is time to connect devices to the route. However, before that is done, the devices should be connected to the group switch. How that is made is not described in this chapter.
Before this step is started, the route has been properly defined by means of EXROI and EXRBC. However, no devices are connected to the route. The command EXDRI is used to make a connection in data between the devices and the route. The parameters required are:
EXDRI:R=r,DEV=dev;
Figure 1.10 shows what the command is doing in the software of the block.
Figure 1.10Example of how command EXDRI connects devices to a route in data
When all the devices have been connected to the route, they should be taken into service by using the command EXDAI. This command will change the state of the devices from a “pre-post service” to “service”.
Finally, the devices can be deblocked by using command BLODE. That will make it possible for the system to used the devices in traffic handling.
In most cases, the supervisory functions should be connected to the route in order to have functions like “blocking supervision” active. In case of an extension of an existing route, the data related to the supervisory functions should be changed (number of devices included in the route has changed). This subject is studied in another part of the course.
3.4.2 Printout of Device and Route DataWhen the data has been defined, and also during the definition, the data loaded can be printed by using print commands. Here are some of the most useful commands shown.
EXDEP is used to print the route to which the device is connected to. The printout also indicates the SNT (switching network terminal) which is used when the device is connected to the group switch. Please study Figure 1.11.
RouteData
DeviceData
New route New devicesEXDRI:...;

Exchange Data
34
Figure 1.11Printout of device data
EXDRP is used to print the regional processor and extension module identity of the device. Please study Figure 1.12.
Figure 1.12Printout of data about RP and EM connection for one device
STRSP means state route survey print. The printout shows gives a survey over the state of the devices in a route. The columns indicate total number of devices in the route (NDV), number of busy devices (NOCC), number of idle devices (NIDL) and number of blocked devices (NBLO). The last column indicates if network management functions have made any restrictions regarding traffic on the route. “NORES” means that no restrictions have been made. Please study Figure 1.13.
<EXDEP:DEV=UPDN3-1;DEVICE DATA
DEV R HNB SNT/DEVP MUP UAUPDN3-1 ISUP1AO UPETN3-0 NC ISUP1AI
DEV MISC1 MISC2 MISC3 MISC4 ADMSTATE R SNT S EMUPDN3-1 1 1 C C C CEND
<EXDRP:DEV=UPDN3-1;DEVICE RP/EM DATA
DEV R RP EMG EM ADMSTATE R SNT S EMUPDN3-1 ISUP1AO 48 0 C C C C ISUP1AIEND

Device and Route Data
35
Figure 1.13Printout of device state survey for one route
STRDP can be used if one route should be examined regarding device states. All devices in the route are listed and the state of each device is indicated. In the beginning of the printout is a state survey printed. Please study Figure 1.14.
Figure 1.14Printout of device state details for one route
EXROP is used to print the route parameters loaded with commands EXROI and EXRBC. Parameters not included in the printout are not set by any command (if for example TTRANS=0, it is not included in the printout as it is regarded as a default or initial value). Please study Figure 1.15.
<STRSP:R=ISUP5AO;DEVICE STATE SURVEYR NDV NOCC NIDL NBLO RSTATISUP5AO 30 5 25 0 NORESEND
<STRSP:R=ISUP5AO;DEVICE STATE SURVEYR NDV NOCC NIDL NBLO RSTATISUP5AO 30 5 24 1 NORESDEVICE STATE DETAILSDEV STATE BLS FTYPE ADM ABS LSTUPDN3-65 IDLE H’02 -UPDN3-66 BUSY H’0A -UPDN3-67 IDLE H’02 -UPDN3-68 BLOC MBL H’00 -UPDN3-69 IDLE H’02 -UPDN3-70 IDLE H’02 -......UPDN3-95 IDLE H’02 -END

Exchange Data
36
Figure 1.15Printout of route data for one outgoing route using ISUP signalling
Figure 1.16Printout of route data for one outgoing route using TUP signalling
<EXROP:R=ISUP5AO;
ROUTE DATAR ROUTE PARAMETERSISUP5AO DETY=UPDN3 TTRANS=1 FNC=3 R=ISUP5AI LSV=1 SI=ISUP4 SP=2-10END
<EXROP:R=ITUP1AO;
ROUTE DATAR ROUTE PARAMETERSISUP5AO DETY=C7BTI3 TTRANS=3 FNC=3 DPC=10 R=ITUP1AI LSV=3 MIS1=1 MIS2=31 ST=1 CCH=0END

Device and Route Data
37
3.5 Chapter SummaryFrom this chapter you should remember these points:
• Commands EXRPI and EXEMI are used to define new RPs and EMs in the exchange.
• The AXE system have both software and hardware routes.
• Routes are defined with the commands EXROI and EXRBC.
• Devices are connected to routes with command EXDRI.
• Printout of route data is made with command EXROP.
• Printout of device data is made with commands EXDEP and EXDRP.
• Route state can be printed with command STRSP or STRDP.

Exchange Data
38

39
4. Analyses, a Survey
Figure 2.1Chapter Objectives
4.1 IntroductionAs more and more functions are combined in the same exchange, the amount of analyses required for traffic handling increases. For ordinary POTS service (plain old telephony service), the amount of analyses is rather limited. Analysis of B-number, routing case and charging case were the most important analyses performed in older versions of AXE. In the latest version of the system, the POTS and ISDN have been combined and the number of analyses tables has increased. This chapter gives a survey of the analyses associated with traffic handling and traffic control.
4.2 Analysis of B-numberAlmost all types of analyses in AXE originate from the analysis of the dialled B-number. However, before the B-number is analysed, some pre-analyses are performed. The analysis to be performed depends on the type of calling subscriber. In other words, a POTS subscriber and an ISDN subscriber are analysed differently.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the relationship between the B-number analysis and other analyses in the system
• describe the differences in analysis between a POTS and an ISDN subscriber.

Exchange Data
40
Figure 2.2 shows the analyses performed before the B-number analysis.
Figure 2.2Analyses performed before the B-number analysis
The three analysis tables are explained below:
• Telecommunication service analysisThe purpose of this analysis is to see if the requested service is supported by the network. The requested service is sent over to the network in the SETUP message originating from the ISDN terminal.
• Pre-analysis of B-number informationAn ISDN network must be able to communicate with many different types of networks, which may have different numbering plans. For example, the numbering plan of a data network may differ from the plan used in the telephony and ISDN network. The parameter NAPI, numbering plan indicator, is used in this analysis in order to get a starting point in the B-number analysis table. Parameter BNT, B-number type, is also used and the output is origin for B-number analysis, OBA.
• B-number analysisThe entry point in the table is given by the pre-analysis and the digits are analysed one by one. Various parameters are sent back to block RE, register function, and will either be used as input to other analysis tables or stored for later use.
POTS
ISDNTelecommunicationServiceAnalysis
ANTEP
Pre-analysis ofB-numberInformation
PNBSP
OBA B-numberAnalysis
ANBSP
Analysisresults

Analyses, a Survey
41
Figure 2.3 shows the other important analysis tables related to traffic handling.
Figure 2.3The most important analysis tables related to traffic handling
4.2.1 Route AnalysisThe input to the route analysis is the parameter RC, routing case. The routing case is analysed and the result is usually the identity of an outgoing route. In most cases, the analysis includes a compatibility check which checks that the service requested by the subscriber is compatible with the transmission medium and the signalling system.
4.2.2 Charging AnalysisThe name “charging analysis” is used in this book as a collective name for a large number of analyses. The charging system contains some 8 different analysis tables. The input to these tables is the parameter CC, charging case. In most cases, the information given by an analysis table is a tariff. The tariff states the time in seconds between the charging pulses as well as the number of start pulses at start of charging.
RouteAnalysis
ChargingAnalysis
Time SupervisionAnalysis
AccountingAnalysis
Equal AccessAnalysis
Access BarringAnalysis
Service IndicatorAnalysis
Service ScreeningAnalysis
B-categoryAnalysis
End-of-selectionAnalysis
RC
CC
TI
A
CAC
D
SIC
SSC
TE
ES
B-numberAnalysis
A-numberAnalysis
A-number

Exchange Data
42
4.2.3 Accounting AnalysisAccounting is part of the charging subsystem and must be used when more than one operator is involved in the call. The function registers the call duration and/or number of calls between operators in the network. The input to the analysis is the parameter A, accounting case.
4.2.4 Time Supervision Analysis This analysis is only used if the number length of a dialled number is unknown. This could be the case for international calls to countries with unknown numbering plan. The time supervision between digits is shortened in order to determine when the last digit is dialled. The input to the analysis is the parameter TI, time supervision case.
4.2.5 Access Barring Analysis If a subscriber is barred from making long-distance calls, this analysis checks whether the call is allowed or not. The input to the analysis is the parameter D, destination code.
4.2.6 End-of-selection Analysis This analysis is used for redirection of calls after detection of an error or, for example, a subscriber service. Although the table is primarily used for handling errors, it can also be used for any type of redirection. For example, the route analysis can generate a so-called end-of-selection code as the last alternative if all other routes to a specific destination are busy. The end-of-selection analysis can redirect the call to an announcing machine. The input to the table is parameter ES, end-of-selection code.
4.2.7 B-category Analysis This function is used when the B-subscriber has been identified by means of the parameter TE, terminating call, which is generated by the B-number analysis. The analysis checks whether the B-subscriber is allowed to receive calls and whether the combination of A and B-subscriber categories is allowed. There is no analysis table for this type of analysis which can be changed by command (set by parameters in the program). The analysis is performed by block SUA.
4.2.8 Service Indicator Analysis ISDN subscribers are connected to the network via a powerful signalling system referred to as DSS1, digital subscriber signalling system no. 1. This signalling system can contain all information about the service requested by the subscriber. Non-ISDN subscribers can communicate with the network only by means of digits. By dialling a specific code, the non-ISDN subscribers can request ISDN services. After the analysis, the “telecommunication service analysis” is requested to check that the network can offer the service. The input to the analysis is parameter SIC, service indicator code.

Analyses, a Survey
43
4.2.9 Service Screening Analysis The number of services in ISDN networks is great but the introduction and charging of the services may vary between different operators. One type of service may be available in one network but not in another. The services can also be incompatible with each other. The purpose of the service screening analysis is to remove certain services from a call depending on the destination of the call. The service “x” can be used together with operator “A” but should be suppressed for all calls to operator “B”. The input to the analysis is the parameter SSC, service screening case.
4.2.10 Equal Access AnalysisIn a near future it will be possible to select any carrier for long-distance calls. This can be made by subscribing to an operator or by dialling a prefix before the area code. Regardless of the method used, the equal access analysis will provide the required information. The input parameter is CAC, carrier access code.
4.2.11 A-number AnalysisThe A-number analysis is only used together with charging. In some cases, the number of the calling subscriber must be analysed in order to determine the cost of the call. The result is input either to the charging analysis or to the accounting analysis. The input to the table is the A-number (identity of the calling subscriber).

Exchange Data
44
4.3 Chapter SummaryFrom this chapter you should remember this about B-number analysis:
• There are three analysis tables:
− Telecommunication service analysis.
− Pre-analysis of B-number information.
− B-number analysis.
You should also remember these important analysis tables related to traffic handling:
• Route analysis.
• Charging analysis.
• Accounting analysis.
• Time supervision analysis.
• Access barring analysis.
• End-of-selection analysis.
• B-category analysis.
• Service indicator analysis.
• Service screening analysis.
• Equal access analysis.
• A-number analysis.

45
6. Route Analysis
Figure 3.1Chapter Objectives
6.1 IntroductionRoute analysis is used to select the route to be used for a specific destination. The routing case, which is obtained from the B-number analysis, corresponds to a specific destination. The route analysis indicates the route to be used to the specified destination. A large number of parameters may affect the routing (for example origin, subscriber categories, and time of day).
6.2 Analyses in GeneralMaking analyses inside the AXE system just means looking up data in tables. Perhaps the word “analysis” reminds the reader of some advanced and complex calculation, but this does not apply to analyses made inside the software of the AXE system. Examples of analyses are “route analysis”, “charging analysis” and “B-number analysis”.
The input to the analysis tables is mainly of three types:
1. External data such as B-number digits and A-number digits
2. Internal data such as subscriber categories and route data
3. Results from other analysis tables, e.g. routing cases.
Figure 3.2 shows the general principles of the analyses made inside the AXE system.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the general principles of analyses in AXE
• describe the interwork in the system when a route analysis is made
• print and interpret basic information in the route analysis table
• describe how the sending program affects the selection of outgoing circuits
• describe how branching can be used in the route analysis
• describe and use the commands related to route analysis
• specify a routing switch in data.

Exchange Data
46
Figure 3.2The general principle of traffic analysis in AXE
6.3 The Basic Principles of Route AnalysisEarlier in this module, we described how new devices and new routes where defined in the system. If a new route is to be defined in the exchange, the next step will be to define the route analysis for the new route. Existing data in the route analysis can be modified by using the commands described in this chapter.
The route analysis in the AXE system is implemented in central software in a function block called RA, route analysis. The block RE, register, interworks with block RA as described in Figure 3.3.
Figure 3.3The general principle for the interaction between digit analysis and route analysis
The different steps showed in the figure are briefly explained below (numbers refer to the numbers in the figure):
External datae.g. B-number
Internal datae.g. subscribercategories
Analysistable Result
e.g. Routing Case
Analysistable
Internal datae.g. route data
Resulte.g. route identity
B-number digitsBlock RE
Block DA
Block RA
B-number analysistable
Route analysistable
RC=xx, R=ABC
0-12 RC=xx
5
4
32
1

Route Analysis
47
1. The B-number is sent to the register from other blocks in the system. The digits are stored inside the register for future use.
2. The digits are sent for analysis in block DA, digit analysis, which contains the B-number analysis table.
3. In some cases is the result from the B-number analysis table a routing case, RC. The routing cases are numbered, e.g. RC-40. The RC number is sent back to the register which stores the information in the register record reserved for the call.
4. The routing case is sent to block RA together with more information such as subscriber categories or route data (depending on the origin of the call). In RA, the route analysis table indicates the route to be used for the call.
5. The identity of the route indicated in the analysis is sent back to the register.
The route analysis inside the block RA is in the form of a table that can be printed by means of the command ANRSP. Figure 3.4 shows an example of a printout of a small part of the route analysis table.
Figure 3.4Example of a routing case
Some of the most important columns in the printout are briefly explained below. For a detailed description, see the printout description for the printout “ROUTING CASE DATA”.
• RC, routing caseThis column is used for the number of the routing cases. The RC number will be the input position to the table.
• CCH, compatibility checkIf YES is stated, the compatibility between the selected route and the requested service is compared (regarding signalling and bearer demands).
• BR, branchingThe routing cases can give different results depending on different
<ANRSP:RC=15&16;ROUTING CASE DATAOPERATINGRC CCH BR ROUTING SP COT EST SI ESS ESR BNT FCP15 YES WSIG-0 &&-2 P01=1 R=ETSI1O 665 0 0 0 0 0 1 0 P01=2 R=ETSI0O 665 0 0 0 0 0 1 0 P01=3 ES=11416 YES P01=1 R=R2INT0O 665 0 0 0 0 0 1 0 P01=2 ES=114
END

Exchange Data
48
input parameters (e.g. subscriber class). More about that later on in this chapter.
• RoutingUnder this heading, the different routing alternatives are listed. If an RC has several “lines”, this means that there are more than one alternative for that Routing Case. Each RC can have up to 25 “routing programs” denoted P01 to P25. Within each routing program, up to 8 alternatives can be specified. The alternatives are indicated by 1 to 8 (P01=1, P01=2 .... P01=8). The parameter “R=...” indicates the route name for the alternative. The route names specified with command EXROI should be used.
• SP, sending programThis information is used to indicate when an outgoing circuit is to be seized. The parameter is described in detail in the next chapter.
The other columns are used for special cases and for international exchanges (e.g. handling of echo suppressors).
6.3.1 The Sending ProgramThe column marked “SP” in the printout depicted in Figure 3.4 indicates when different actions should be taken for seizure of an outgoing circuit and for digit transmission. The sending program consists of 3 parts whose meanings are explained in Figure 3.5.
Figure 3.5The meanings of the three digits in the sending program
As can be seen in the sending program, the events initiated on the outgoing side are determined by the incoming digits. As the register controls the call setup, the events are related to when the digits are received by the register. If the sending program in Figure 3.5 is used (SP=553), seizure of an outgoing circuit is initiated when the register has received the 5th digit of the B-number. The seizure signal to the other exchange is also sent after the 5th digit and the third digit is transmitted as the first. Figure 3.6 shows how the sending program is used by the outgoing exchange in a call between two exchanges.
SP = 5 5 33rd digit is transmittedfirst.
A seizure signal is sent afterreception of the 5th digit
An outgoing device in theindicated route is seized afterreception of the 5th digit

Route Analysis
49
Figure 3.6Example showing how a sending program is used to control the digit sending
The information in the sending program is determined by the administration (traffic engineering department) and the values written in the sending program depend on several factors:
1. Signalling systemIf an old (usually slow) signalling system is used on the route, the start position for seizure should come early in order to have time to transmit the digits. If, on the other hand, a fast signalling system is used, e.g. ITU-T No. 7, the seizure position is usually on the very last digit.
2. DistanceFor international calls, the outgoing exchange does not know what signalling system is used in the other country, and consequently the start position usually comes as early as possible.
3. Numbering planThe value written in the last digit of the sending program is determined by the numbering plan of the network.
4. Post dialling delayThe time between the dialling of the last digit until ring control tone is heard by the calling subscriber is referred to as post dialling delay. The maximum values set by operators and ITU-T for this parameter may affect the sending program.
In some cases, no digits should be transmitted to the outgoing route. Examples are routes to subscriber services and announcing machines. In this case, the sending program is specified in a special way. The following examples show how the sending program can be specified for special cases:
R=ABC, SP=553A B
065
0
1
3
2
3
Seizure after 5 digitsThe 3rd digit is sent first (5)
Time
06-501323
(0)(1)(3)(2)(3)

Exchange Data
50
• SP=330If the last digit in the sending program is set to zero, no digits at all will be transmitted to the route. If all digits are to be transmitted, a “1” should be specified.
• SP=300If also the middle digit in the sending program is also set to zero, no seizure signal will be sent on the route.
• SP=MM5If the number length is unknown, and if seizure should be made on the last digit, the letter “M” is used to indicate “maximum”.
• SP=AA3The letters A to F can be used in the sending program to represent the values 10 to 15 (same as hexadecimal).
6.3.2 Routing Case with Branching on Route OriginBranching is used if the analysis result from the table should be affected by some other parameter, such as the origin of the call or the time of day. In this chapter, the function “branching on route origin” is examined. This means that the origin of the call, i.e. the identity of the incoming route, affects the analysis in the Route Analysis.
Why, then, should that be necessary? The answer is that the traffic engineering department would like to give traffic from different areas a limited number of alternative routes to other destinations. The traffic from “this” exchange (in which the analysis is made) should perhaps have several alternatives for a given destination, as compared with the incoming traffic from another area. The other area might already have other routing alternatives not going through “our” exchange. Figure 3.7 shows a simple network with “our” exchange as exchange A.
Figure 3.7Routing using the branching facility (route origin)
In the figure, the traffic from C to B has two alternatives: either the direct route or via “our” exchange A. For traffic from A to B, there also exist two alternatives: either the direct route or via the transit exchange T. If the same routing case is used for this traffic case, some type of branching on
AB
CD
T
1:st
2:nd
Only 1 alternativefrom C to B

Route Analysis
51
route origin must be made in exchange A. The route analysis in exchange A will be as follows:
“Traffic from A to B should have two alternatives while traffic transiting from D should only have one alternative.”
To do this in exchange A, the following actions must be taken:
1. Change the route data for the incoming route from exchange D. The parameter changed is the RO, route origin. It should be given a value different from zero, e.g. RO=1.
2. The route analysis for the affected routing case should be changed in order to only give traffic from RO=1, only one alternative to exchange B.
The route origin is changed by means of command EXRBC and the specification in the Route Analysis is done with the following commands:
ANRPI:RC=44;
ANRSI:BR=RO-0,P01=1,R=ABO,SP=773,COT=0;
ANRSI:BR=RO-0,P01=2,R=ATO,SP=551,COT=0;
ANRSI:BR=RO-1,P02=1,R=ABO,SP=553,COT=0;
ANRPE;
The commands ANRPI and ANRPE are used to initiate and terminate a so called “procedure”. Procedures must be used in case of branching as several commands have to be used for specifying a single routing case. When the command ANRPE is given, the program can analyse the data specified and check that no parameters are faulty or illogical. The commands for the branching will create the printout depicted in Figure 3.8.
Figure 3.8Printout of branching on origin, example
As can be seen in the figure, there are two lines with two alternatives for traffic originating from “RO-0”. The traffic from “RO-1”, on the other hand, has one alternative. This specification gives the wanted traffic control in the route analysis.
<ANRSP:RC=44;ROUTING CASE DATAOPERATINGRC CCH BR ROUTING SP COT EST SI ESS ESR BNT FCP44 YES RO-0 P01=1 R=ABO 773 0 0 0 0 0 1 0 RO-0 P01=2 R=ATO 551 0 0 0 0 0 1 0 RO-1 P02=1 R=ABO 553 0 0 0 0 0 1 0
END

Exchange Data
52
6.3.3 Routing Case with Branching on Subscriber ClassAnother way of branching is to use the subscriber category to control the traffic. When talking about subscriber category in this chapter, the TCL category is referred to. This category, often called “type of class”, is the only category that can be transferred in the network by most signalling systems. In other words, this category can be used for various traffic control functions and checks in the network. The TCL category can have a value between 1 and 15. Each value represents a certain type of subscriber. Examples of subscriber types are operators, ordinary subscribers, coin boxes and test equipment. The exact value for each type of subscriber is set by the network operator and varies considerably from country to country.
If, for example, coin boxes should be barred from a certain traffic destination, the branching on subscriber class can be made in the route analysis. Figure 3.9 shows an example where a traffic destination leading to a special service is barred for traffic originating from coin boxes. Instead, these calls are redirected to an announcing machine telling them that they do not have access to the service.
Figure 3.9Branching of subscriber class (coin box in this example)
In order to make a specification in the route analysis table for this traffic case in exchange B, the following commands should be used (coin box has TCL category 11 in this example):
ANRPI:RC=65;
ANRSI:BR=CL-1&&-10&-12&&-15,P01=1,R=SERV55,SP=111,COT=0;
ANRSI:BR=CL-11,P02=1,R=ANSW30,SP=110,COT=0;
ANRPE;
Calls having a TCL category other than 11 will access the route leading to the service (R=SERV55). Calls originating from subscribers with TCL=5 will instead be directed to a route leading to an announcing machine (R=ANSW30). Figure 3.10 shows how a printout of this routing case looks like after the specification.
RouteAnalysis
Coin boxTCL=11
TCL=11 is sentwith the signallingsystem
Exchange B
Service not allowed for coin boxes
Announcingmachine
A
B

Route Analysis
53
Figure 3.10The branching implemented in the route analysis table
6.3.4 Other Branching ConditionsSo far we have studied two ways of using the branching function inside the route analysis. However, there are other parameters that also can be used for branching purposes. Note also that the branching conditions can be combined with several parameters (e.g. origin and TCL category). Below follows a short description of the parameters available:
• PR, priority (0-3)Both subscribers and incoming routes can be assigned a priority. This parameter can be used as a branching parameter.
• RA, random switchThis function allows the operator to distribute the traffic at random in steps of 10% to different routes. By combining random switches with each other, it is possible to have the distribution specified in steps of 1%. Figure 3.11 shows the principle.
Figure 3.11Example of a random switch
<ANRSP:RC=44;ROUTING CASE DATAOPERATINGRC CCH BR ROUTING SP COT EST SI ESS ESR BNT FCP65 YES CL-0 &&-10 &-12 &&-15 P01=1 R=SERV55 111 0 0 0 0 0 1 0 CL-11 P02=1 R=ANSW30 110 0 0 0 0 0 1 0END
Traffic todestination B
Randomswitch
50%
20%
30%
National orinternational
transit network
A B

Exchange Data
54
• SW, routing switch (0-3)This function allows the operator to manually affect the branching by means of a command-controlled routing switch. The operation of the switch can also be scheduled. More about this subject in the next chapter.
• LOD, language or discriminating digit (0-15)Only used in international exchanges as language digits are not used in the national network.
• AL, exchange alarm state (0-3)By means of a command, the exchange can be set in different alarm states (normal, alarm state 1 and 2). The routing can be affected by the alarm state.
• SAT, satellite connection (0, 1 or 2)The parameter is used to indicate the number of satellites connected on the incoming side. For speech calls, only one satellite is allowed. For data calls, up to two satellites are allowed.
• EA, emergency area (0-15)The emergency area is a subscriber class which may affect the routing.
• WSIG, wanted type of signalling (0-15)The parameter is an output from the “telecommunication service analysis” and states the signalling requirements throughout the call. Two of the values state “no preference” and “ISDN signalling required”.
• TMR, transmission medium required (0-255)This parameter is valid for ISDN calls requiring for example a 64 kbit/s connection. Two examples of parameter values are “speech” and “64 kbit/s unrestricted digital information”.
6.3.5 The Use of Operating and Non-operating AreaMost analysis functions inside the traffic handling part of the AXE system use two tables: one for the actual analysis and the other for performing changes. The two tables are referred to as “operating area” and “non-operating area”, abbreviated OP and NOP respectively. This method has several advantages over the use of a single set of tables:
1. Major changes or extensions require several commands. In most cases, all commands must be specified before the analysis is made.
2. The new data, loaded into the NOP area, can be tested, printed and changed before it is used in traffic.
3. When existing analysis data is changed, the old data is kept in write-protected state for 24 hours. If the new data is faulty, it is possible to revert to the old data by entering a single command.
4. Changes in the NOP areas can be made during traffic handling. Even major changes can be made without disturbing the traffic.
In case of route analysis, the commands used to handle the analysis tables begin with the letters ANRxx. Figure 3.12 shows how an existing routing

Route Analysis
55
case is changed by specifying data in the NOP area, after which the data is activated.
Figure 3.12Example of how the operating and non-operating areas are handled for a routing case
Operatingarea, OP
Non operatingarea, NOP
NOP area iscleared byANRZI
New RC=55is entered inNOP area by
ANRSI
New RC=55is activated by
ANRAI
In case of errors:switch back toold RC=55 by
ANRAR
RC CCH BR .........55 YES .......
RC CCH BR .........55 YES RA-1...
RC CCH BR .........55 YES .......
RC CCH BR ...............
RC CCH BR .........55 YES .......
RC CCH BR .........55 YES CL-1&&...
RC CCH BR .........55 YES CL-1&&...
RC CCH BR .........55 YES .......
RC CCH BR .........55 YES .......
RC CCH BR .........55 YES CL-1&&...
Old data inNOP area
NOP areais empty
New data forRC=55
Old RC=55 keptin NOP area asback-up
Old data restoredfrom NOP area

Exchange Data
56
6.3.6 The Commands Used to Define Routing CasesWe have already studied some of the commands used to specify routing cases. This chapter describes the commands related to this function and indicates what each command does. For detailed information about parameters and correct syntax, see the command description in the exchange library.
• Commands for specification and deletion of RC:
− ANRSI, specifies new RCs in the NOP area.
− ANRSE, deletes RCs from the OP area. This is only possible if there is no reference to the RC from the B-number analysis table.
• Commands for initiating and terminating procedures:
− ANRPI, initiates a procedure
− ANRPE, ends an initiated procedure
• Commands for handling of OP and NOP areas:
− ANRZI, clears the NOP area for all or specified RCs
− ANRAI, activates the specified RCs
− ANRAR, deactivates specified RCs and reverts to the old data if such data is available (change of existing RC).
6.3.7 Routing SwitchA routing switch is a function used to manually, or automatically, control the traffic flow for one or several routing cases. The switch can either be controlled by command or by a time table. Figure 3.13 shows an example where a routing switch can be useful.
Figure 3.13Example of when a routing switch can be useful
The routing case for the traffic from A to B must be modified in order to have the routing switch function included. This is done by using the switch position as a branching condition in the route analysis. The commands required for this specification are:
Exchange A hastwo alternativesfor traffic to B:1st A to B2nd via T to B
A
T
B
Route has to beswitched off formaintenance athours

Route Analysis
57
ANRPI:RC=52;
ANRSI:BR=SW-0,P01=1,R=ABO,SP=553,COT=0;
ANRSI:BR=SW-0,P01=2,R=ATO,SP=331,COT=0;
ANRSI:BR=SW-1,P01=1,R=ATO,SP=331,COT=0;
ANRPE;
When RC-52 is activated, the switch can be operated in two different ways:
1. Manually operated switchThe command ANSSI:RC=52,SW=1; is used to set the routing switch in position 1. This means that only one alternative, the alternative via exchange T, can be used for traffic from A to B. The parameter “SW=0” is used to reset the switch to its original position.
2. Automatically operated switchIn this case, a time table tells the system how the switch should be changed during the week. The principle is similar to the specification of time-differentiated charging (switching class). For more information, see the description of the charging function. Here are the commands required (example):
ANSPI: RC=52;
ANSSI: SW=0&1,DCAT=0,TIME=0700&1800;
ANSSI: SW=0&1,DCAT=1,TIME=0900&1500;
ANSSI: DCAT=2;
ANSPE;
6.4 Chapter Summary• The routing case is the input to the routing analysis and various
parameters can be used for branching in the analysis.
• The sending program is the parameter delivered from the analysis that controls the digit transmission between the exchanges.
• When specifying a routing case, you must work with an operating and a non-operating area.

Exchange Data
58

59
7. Hundred Groups
Figure 4.1Chapter Objectives
7.1 IntroductionHundred groups is the term used to describe the internal numbers defined in an AXE exchange. All subscriber numbers in a local exchange must be defined by means of a command. The definition sometimes includes a definition of the area code tied to the subscriber number. This chapter describes how new number series are defined and how the area code is handled.
7.2 What is a Hundred Group?A “hundred group” is, as the name indicates, a group of hundred subscriber numbers. The subscriber numbers must be defined in a local exchange in order to tie the subscriber number to a data record. The records are located in the function block SC, subscriber categories, and the number of records is set by means of a size alteration. The size alteration creates data storage space for a specified number of subscriber numbers in the exchange. However, the numbers defined in the exchange have to be specified with the command EXNSI. When the internal numbers have been defined, the subscriber number can be connected to the line interface. The connection is made with the command SULII. Figure 4.2 shows the principle.
Chapter Objectives
After completing this chapter, you will be able to:
• explain how hundred groups are used inside the AXE system
• define a new hundred or thousand group
• define hundred groups with and without area codes
• define an implied area code
• print the internal number series as well as the area code
• change internal number series.

Exchange Data
60
Figure 4.2Logical connection between line interface and subscriber number
The parameters in the command SULII are DEV=dev and SNB=snb. These parameters point out the device in block LI and one record in block SC which represents the subscriber number. The disconnection of the subscriber is made by breaking this link. That is done with command SULIE.
7.3 Specification of Area CodeIn most cases, one and the same area code is used for all subscribers connected to the exchange. If the exchange is located in a small town, all subscribers in that town probably have the same area code. However, if one exchange serves a large area by means of remote subscriber switches (RSS), different area codes might be used for the different subscribers. This means that the AXE exchange must know to which “area” a specific subscriber belongs.
Another case where more than one area code is required is when the AXE exchange uses an RSS in another town (with another area code). The reason could be that the other town, the one without AXE, has an old analog exchange which will be changed in a couple of years. In that case, some large subscribers (PABXs) might complain to the PTT that no services are available to them (they pay the same price as the ones connected to the modern AXE exchange). To cope with this situation, the PTT can use one or two RSS to provide AXE connection to a limited number of subscribers located in the other town. The AXE must then be able to handle more than one area code. Figure 4.3 gives an example.
LIC
Software
Hardware
LI SCSULII
One recordper LI device
One record persubscriber number

Hundred Groups
61
Figure 4.3Three area codes handled by one and the same exchange
7.3.1 One Implied Area Code DefinedIf only one area code is to be defined in the exchange, this is easily done with the command EXIAI. Example:
EXIAI:AREA=020;
This means that all the subscriber numbers defined in the exchange belong to area 020. The area code is not used in the B-number analysis, because there is no need to differentiate between the subscribers. However, in case of calling line identification (the A-number is requested by another exchange), the data specified in the area code is added to the A-number (020xxxxxx is sent as A-number to the other exchange).
7.3.2 Different Area Codes Defined in the same ExchangeIn a network as of the type depicted in Figure 4.3, the AXE exchange must be able to differentiate between the different areas. The area code is tied to the subscriber numbers when the number series are defined. The definition is made with command EXNSI which has the following parameters:
EXNSI:HU=hu...,SNB=snb,L=l;
The parameter HU stands for hundred group and this number is only used for consecutive numbering of the different numbers defined in the exchange. Usually, thousand numbers are defined at the same time and numbered in consecutive order (e.g. HU=0&&-9). The parameter SNB stands for subscriber number and this is the first number in the hundred or thousand group. If an area code is to be tied to the subscriber numbers, it is written in front of the subscriber number. In this case, the parameter “L” indicates the number of digits in the area code. Example:
EXNSI:HU=0&&-9,SNB=020450000,L=3;
Area 020
Area 021
Area 022
Number series:020 xxx xxx021 xxx xxx 022 xxx xxx
AXE

Exchange Data
62
The command defines 10 hundred groups which belong to area code 020. Parameter L=3 indicates that the first three digits in the subscriber numbers belong to the area code (020 in this case). The ten hundred groups start with subscriber number 450 000 and end with 450 999.
When the hundred groups have been loaded, they can be printed by means of the command EXNSP. Figure 4.4 shows a printout of hundred groups 0 to 10. The printout is based upon the hundred groups loaded in the example above.
Figure 4.4Printout of number series defined in the exchange
All area codes in the exchange can be printed by using the command EXACP. The command will look through the complete table of number series and read out the area codes used in the exchange. Figure 4.5 shows an example.
Figure 4.5Printout of area codes, example
If there is an implied area code in the exchange (defined with command EXIAI), the parameter L should be omitted. This means that all number series in the exchange have the same area code.
7.4 Change of Hundred GroupsIf number series are changed in the network, the command EXNSI has to be used again. However, to avoid disturbing the traffic handling by disconnecting and reconnecting the subscribers, we use the parameter “SNBCH” which indicates a change of the subscriber numbers. Suppose that the number series loaded earlier in this chapter should be changed. The existing thousand group starts with number 450 000 but suppose digit “3” should be added in front of the numbers in order to change the
<EXNSP:HU=0&&-10;NUMBER SERIES DATAHU SNB L HU SNB L HU SNB L 0 020450000 3 1 020450100 3 2 020450200 3 3 020450300 3 4 020450400 3 5 020450500 3 6 020450600 3 7 020450700 3 8 020450800 3 9 020450900 3 10 020451000 3END
<EXACP;AREA CODESAREA AREA AREA AREA020 021 022
END

Hundred Groups
63
numbers in the exchange to 7-digit numbers. In that case, the following command is given:
EXNSI:HU=0&&-9,SNB=0203450000,L=3,SNBCH;
When the calling line identification requests the A-number, the new A-number is sent (starting with a “3”). However, the B-number analysis is not affected until the B-number analysis table is changed and activated. This means that it is possible to change the number series without disturbing the traffic.
7.5 Chapter SummaryFrom this chapter you should remember these points:
• One record in block SC corresponds to one subscriber number.
• The total number of records is set with a size alteration.
• The internal number series are defined with command EXNSI.
• If one area code is valid for all subscribers in the exchange, the command EXIAI is used.
• If several area codes should be handled by the exchange, the parameters SNB and L in command EXNSI are used.
• If a number series is to be changed, the new number series is defined with command EXNSI using parameter SNBCH.

Exchange Data
64

65
8. Charging
Figure 5.1Chapter Objectives
8.1 IntroductionThe charging subsystem (CHS) gives the operator a powerful and flexible set of charging functions. It must contain functions which make it possible to charge all types of calls and which give statistics and information to the operator. The statistics are used to analyse the effect of changes in tariffs and charging programs. Charging should be determined by distance (the destination), subscriber services, the usage of interworking units (IWU) and, finally, the result of a subscriber procedure (successful or not).
Subscribers demand accurate charging as well as access to services related to the charging function. For example, the cost of a call can be displayed in the window of the phone/subscriber terminal.
8.2 Pulse Metering and Toll TicketingThere are two basic charging methods:
• Pulse metering, PMIf pulse metering is used in the exchange, each subscriber has a counter that is stepped according to the pulses generated by the tariff. At regular intervals, the counter value is read (copied to a disk/tape) and an external computer generates a bill according to the counter value. In the current version of AXE, each subscriber has up to four counters implemented in software in one of the blocks in the charging subsystem.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the two variants used for charging
• describe the whole sequence required for a complete charging analysis
• interpret basic information included in the printouts of charging data
• describe the basic functions of the calendar function.

Exchange Data
66
• Toll Ticketing, TTWhen this method is used, the charging subsystem will record information about each call such as the A and B-numbers, start and stop time of the call and the destination of the call. At the end of the call, this information is copied to a disk/tape and an external computer can generate a detailed bill from this information. Please study Figure 5.2.
Figure 5.2The general principle of pulse metering and toll ticketing
For pulse metering, the block CHSUB inside the charging subsystem contains the pulse meters of the subscribers in the exchange. The counters are stepped upon order from block CHCHARG that contains information about the tariffs in the exchange. At regular intervals, the pulse counters are copied to a disk or a tape and sent to an external computer for generation of bills.
When toll ticketing is used, the block CHDATA records all the information required. When the call is terminated, the information is sent to block CHOFTT that formats the data according to the requirements of the operator. This information is then sent to a tape or a disk for storage. At regular intervals, the files on the disk/tape are sent to an external computer for post-processing and generation of bills.
Different operators use different pulse metering methods. The two most common methods are referred to as “the Karlsson principle” and “the modified Karlsson principle”, named after the inventor, a Finn.
The method to be used in an exchange is determined by the operator when the application system is assembled. The applicable method is chosen by setting some parameters in the program of one of the blocks in the charging subsystem. This means that the selected charging method cannot
A-no.B-no.Start timeStop timeNo of pulses
One set of countersper subscriber (max. 4)
One record generatedfor each call
Post-processing inexternal computer
Post-processing inexternal computer
Pul
se M
eter
ing
Toll
Tic
ketin
g

Charging
67
be changed by command. The basic principles of the two variants of pulse metering can be seen in Figure 5.3.
Figure 5.3The charging principles used for pulse metering
8.3 Function Blocks in CHSThere are a large number of function blocks in CHS and explaining all of them would not be practicable here. Instead, we are going to study groups of blocks and some of the central parts of CHS. Figure 5.4 shows the groups of blocks in CHS.
Figure 5.4Blocks in subsystem CHS (not all blocks shown)
Original Karlsson Method
Modified Karlsson Method
Pulse
Call duration (2 pulses)
Pulse at B-answer
Call duration (3 pulses)
Time
Time
Optional suppression of first pulse
1)
1)
Core Blocks Optional Blocks
Immediate Service Charging Check
Call Meter Reading
Charging Statistics
High Cost/Long Duration
Private Meter
Common Charging Output
Accounting
IS ISC CHAC CHACT
MRO MRC
CHAS CHASP
CHIDA
CCC
CHOFTT CHOD
ACA ACC
ACR
CHMON CHCOOR
CHSUB CHAB
CHAP
CATA
CHCHARG
CHDATA

Exchange Data
68
8.3.1 Core blocksThere are some 16 blocks in the core part of CHS. The blocks shown in the figure participate in the charging analysis during call establishment. The blocks are described briefly below:
• CHMONThis is the only block that is linked into the software call chain. The block monitors the events in the call and sends signals to the other blocks in the charging subsystem.
• CHCOORA central block which co-ordinates events in the subsystem.
• CHSUBThe block stores the call meters of all the subscribers in the exchange.
• CHABThe block performs the branching analysis of the charging analysis function.
• CHAPThe block performs the charging program analysis.
• CHCHARGThe block generates the pulses for the call according to the tariff used.
• CATAThe block performs the traffic activity charging analysis.
• CHDATAThe block collects data about the call related to the A and B-subscribers.
8.3.2 Optional blocksThe optional blocks will not be described here as some of the functions are described in Other Charging Related Services at page 77. If working with the functions, the block name of the blocks implementing the function must be known if looking for documents related to the function. For example, the block has to be known to find the document application information in the B-module.
8.4 Analysis Tables, SurveyThere are a large number of analysis tables in the charging subsystem. All tables are related to each other as in most cases the output from one table is used as input to the next. The reason for having so many tables is that the charging analysis is very complicated and affected by a large number of parameters. Figure 5.5 shows a survey of the analysis tables and the following chapters explain one analysis table each.

Charging
69
Figure 5.5The analysis tables in the charging subsystem
When specifying new data in an exchange, one has to start with the data that is referenced first. This principle in AXE which applies not only to the charging functions. In the figure above, the specification of new data should start by introducing new tariffs. Data has to be specified from right to left in the figure. In the text, however, we describe the analysis from left to right as that is the order used in traffic handling.
8.5 Traffic Activity AnalysisThe main purpose of this analysis is to:
• Check how the call was initiated
• Check the type of service requested
• Check which subscriber procedure the calling subscriber used.
• Check the result of the procedure (success or failure).
Depending on the result of the analysis, the charging case (CC) originating from the B-number analysis can either be left unchanged or modified. By using branching parameters, the network operator can set up conditions like:
“If the subscriber activates the service immediate diversion, CC=302 should be used if the activation is successful. In other cases, CC=300 should be used.”
An example of the analysis table can be seen in Figure 5.6.
TrafficActivityAnalysis
B-numberAnalysis
ChargingCase Branching
Analysis
ChargingProgramAnalysis
ExtendedChargingAnalysis
TariffClass
AnalysisTariffData
CC CHP
EAE
TC
SWC
TCC=xx
SwitchingClass
Analysis
CC
TC
orNCC

Exchange Data
70
Figure 5.6Example of Traffic Activity Analysis
In the example, the parameter SSI, subscriber service indicator, is used as a branching parameter. This parameter specifies the service requested, i.e. SSI=3, which denotes immediate diversion. The second level of branching is the parameter SSP, subscriber service procedure, which shows the procedure used. The example shows SSP=2 which is “activation of service”. Finally, the parameter RSSP, result of subscriber service procedure, is used as a branching parameter. Depending on the result of the subscriber procedure (successful or not), the charging case is changed to either 300 or 302.
All the codes in this analysis (SSI, SSP, and RSSP) can be found in the document “Traffic Activity Code, Changeable Exchange Adaptation”.
8.5.1 CommandsThe following commands have to be used to change the traffic activity analysis:
• CHIZI Zero the non-operating area
• CHISI Specify data
• CHIPI Initiate procedure in case of branching
• CHIPE End procedure
• CHIAI Activate the data in the non-operating area
<CHISP:CC=5;
TRAFFIC ACTIVITY DEPENDENT CHARGING CASE DATA
OPERATING
CC BC NCC
5 SSI-3
SSP-2
RSSP-1 302
RSSP-2 300
RSSP-3 300
SSP-3 ...
...
END

Charging
71
8.6 Charging Case Branching AnalysisThe purpose of this table is to branch on up to six different parameters. The most important branching parameters are:
• CO, charging originOriginates from the A-subscriber’s categories and the value is set by command SUSCC.
• ACO, origin for charging from A-number analysisAn A-number analysis is used when the origin of the call must be determined before the tariff can be calculated. For example, towns that belong to different areas in the network but are geographically close to each other, might have reduced tariffs.
• CL, type of classThe parameter originates from the A-subscriber category and is set by command SUSCC.
• VPN, virtual private networkSubscribers belonging to a VPN must be treated differently in the charging depending on whether the call is inside or outside the private network.
If no branching is done, a charging program is referenced immediately. An example of the analysis table can be seen in Figure 5.7.
Figure 5.7Example of charging case branching analysis
The parameter CO, origin for charging, is used as branching parameter here. The column marked CHP gives references to different charging programs depending on the CO parameter.
8.6.1 CommandsThe following commands have to be used to change the charging case branching analysis:
• CIBZI Zero the non-operating area
<CIBSP:CC=1&2;
CHARGING CASE DATA
OPERATING
CC BC CHP
1 CO-0 2000
CO-1 10
CO-2 500
2 CO-0 2000
CO-1 10
CO-2 500
END

Exchange Data
72
• CIBSI Specify data
• CIBPI Initiate procedure in case of branching
• CIBPE End procedure
• CIBAI Activate the data in the non-operating area
8.7 Charging Program AnalysisThe purpose of this analysis is to determine how the charging is to be done. The most important information that can be obtained from this analysis is:
• Which exchange is going to handle the charging?
• Who is going to pay for the call (A, B or nobody)?
• Which charging method should be used (pulse metering, toll ticketing or a combination of both)?
• Which call meter should be stepped (one of up to four meters)?
• Which tariff class should be used for the call?
All the parameters for the charging program analysis can be printed by using the command CIPSP. Figure 5.8 shows an example of a printout.
Figure 5.8Example of Charging Program Analysis
8.7.1 CommandsThe following commands have to be used to change the charging program analysis:
• CIPZI Zero the non-operating area
• CIPSI Specify data
• CIPAI Activate the data in the non-operating area
• CIPSE Remove data
<CIPSP:CHP=10;CHARGING PROGRAM DATAOPERATINGCHP CD CP TC REG ITI CMA CS MIS1 EAE MIS3
CHM TC1 ML OTI IS MIS2 PRI
10 3 AP 7 0 1 2 5TTD 0 0 3
END

Charging
73
8.8 Extended Charging AnalysisIn ISDN, the exchange can insert so-called interworking units, IWU, for conversion of the data communication. For example, if a subscriber wants to communicate with a packet-switched data network, an IWU has to be connected for the conversion from circuit-switched to packet-switched mode. The connection of the IWU may be charged by the operator of the originating network. The extended charging analysis can be used for this type of charging as well as for other purposes such as initiation of the services call specification and immediate service for the B-subscriber.
If branching is used, the parameters NCT, network conversion type, and CHT, B-subscriber charging type, can be used. The extended charging analysis can change almost all the parameters in the charging program analysis. This means, for example, that another tariff class may be indicated or the charging method be changed from pulse metering to toll ticketing. Figure 5.9 shows a printout of one part of the extended charging analysis table.
Figure 5.9Example of extended charging analysis
8.8.1 CommandsThe following commands have to be used to change the extended charging analysis:
• CHEZI Zero the non-operating area
• CHESI Specify data
• CHEPI Initiate procedure in case of branching
• CHEPE End procedure
• CHEAI Activate the data in the non-operating area
<CHESP:EAE=5;EXTENDED CHARGING ANALYSIS DATAOPERATINGEAE/BC CD CP TC REG ITI CMA CSB CHM TC1 ML OTI ISB MIS1 MIS2 MIS35 CHT-0&-2&&-150 0 0
CHT-1 3 NP 0 0 NOCHM 0 0
END

Exchange Data
74
8.9 Tariff Class AnalysisFrom the extended charging analysis, or from the charging program analysis, a so-called tariff class is indicated. The purpose of the tariff class is to:
• State the tariff used (in combination with switching class).
• State the tariff used if time-differentiated charging is not used.
This means that the so-called switching class has to be combined in order to see the tariff used. However, the switching class is nothing but a time table based upon a clock and categories of days (weekday, day before holiday and holiday). The switching class will be examined in the next chapter. If time differentiated charging is not used (the cost is the same regardless of day and time), a tariff is stated in the tariff class data. Figure 5.10 shows an example of a printout of tariff class data.
Figure 5.10Printout of tariff class data
8.9.1 CommandsThe following commands have to be used to change the Tariff Class:
• CHCZI Zero the non-operating area
• CHCSI Specify data
• CHCPI Initiate procedure in case of time-differentiated charging
• CHCPE End procedure
• CHCAI Activate the data in the non-operating area
8.10 Switching Class AnalysisIn most cases, operators use time-differentiated charging. This means that the charging is affected by the day and time. The main reason for introducing this type of charging is to move traffic from the busy hour to low-traffic hours. This will ensure a better utilization of the total network resources as the network has to be dimensioned according to the maximum traffic load.
When defining time-differentiated charging, the operator specifies that the tariff should be changed at specific points in time during normal working
<CHCSP:TC=7&8;TARIFF CLASS DATAOPERATINGTC SWC CPT DCAT T 7 1 PPC 0 3 4 1 2 3 4 5 6 7 8 9 3 8 1 PPC 0 4 5 1 2 3 4 5 6 7 8 9 4
END

Charging
75
days. In most cases, a lower tariff is used during holidays and days before holidays. The classification of days has necessitated the introduction of so-called “day categories” in AXE 10. Please study The Calendar Function at page 79.
Figure 5.11Printout of switching class data
To see how the tariff class and the switching class have to be combined, a 24-hour clock can be used. One clock is drawn for each day category. Figure 5.12 shows an example with tariff class 8 shown in Figure 5.10.
Figure 5.12Example of day categories and tariffs used for one tariff class
As the figure shows, tariff 4 is used between midnight and 8.00 AM. During working hours, until 17.00 PM, tariff 5 is used. After that, the “low tariff” 4 is used again. During days with day categories 1 and 2, the tariff 4 is used throughout the day.
8.10.1 CommandsThe following commands have to be used to change the Switching Class:
• CHSZI Zero the non-operating area
• CHSSI Specify data
• CHSPI Initiate procedure
• CHSPE End procedure
• CHSAI Activate the data in the non-operating area
<CHSSP:SWC=1;SWITCHING CLASS DATAOPERATINGSWC DCAT TIME 1 0 0800 1700 1 2 3 4 5 6 7 8 9END
DCAT=0 DCAT=1 DCAT=20000 0000 0000
08001700
T=4
T=5
T=4
T=4 T=4

Exchange Data
76
8.11 TariffsFinally, the tariff can be defined. The tariff specifies two pieces of information:
• The time in seconds between the pulses. The time may vary between 0.01 and 3276 seconds; the application information for the block MP gives more information about the accuracy.
• The number of start pulses at B-answer or when charging starts.
There are no operating area and no non-operating area for tariffs. Figure 5.13 shows a printout of some tariffs.
Figure 5.13Printout of tariffs
The parameter TDS, time duration in seconds, gives the number of seconds between the pulses. The number of start pulses given when the charging starts is stated with the parameter NSP, number of start pulses.
8.11.1 CommandsThe following commands have to be used to change the tariff data:
• CHTSI Specify tariff data
• CHTSE Remove tariff data
<CHTSP:T=1&&6;TARIFF DATAT TDS NSP IDS NPP 1 180 1 1 2 540 1 1 3 20.600 1 1 4 55 1 1 5 25.900 1 1 6 1 0 1END

Charging
77
8.12 Operational InstructionsThe following operational instructions apply to charging-related services and functions:
• Change of charging case data
• Change of charging program data
• Change of extended charging analysis entries
• Change of register charging data
• Change of switching class data
• Change of tariff class data
• Change of tariff data
• Modification of event charging case
8.13 Other Charging Related Services
8.13.1 AccountingAccounting has traditionally been used only in international telephony. However, the trend with privatization and a large number of private operators has changed the scope of the accounting function which is now used on a national basis, too.
The accounting function in AXE 10 is used to determine how a charged call is to be divided between the operators participating in the call. The subscriber usually pays only one of the network operators but the charged money has to be divided between them. In AXE 10, this function is handled by the central software blocks in subsystem CHS. Three of the central blocks are ACA, ACC and ACR.Figure 5.14 shows an example of a call which involves accounting.
Figure 5.14Example of accounting
In the example, the call is charged by the A-subscriber´s own operator. Accounting functions in the exchanges of operator B and C calculate the
Operator AOperator B
Operator C
A-subscriber
Total chargedamount
xx%xx%xx%

Exchange Data
78
amount of money they should receive from the charging operator. Agreements settle the percentage of the charged duration. Counters in the accounting functions can count:
• total number of charging pulses
• total number of calls
• total conversation time
8.13.2 Immediate ServiceThis subscriber service gives the subscriber the cost of the call after the call has been completed. The service sends information about the charged call to an I/O terminal, from where it may be sent further on, for example, to a hotel via a modem. The service is given to the subscriber by means of a subscriber category (IS) set by command SUSCC.
8.13.3 Charging CheckIf a subscriber complains about the amount charged for a specific period, the charging check function can be started. This function can be compared to advanced toll ticketing as a large amount of information is assembled for each call and stored on file. The operator consults the stored information to see whether or not the subscriber’s complaint is justified. The service is given to the subscribers by means of a command.
8.13.4 Call Meter ReadingIf the exchange has pulse metering, this function makes it possible to read the values of the call meters in the exchange. The reading can be directed to a file device or fed out on paper. Figure 5.15 shows the meter reading for one subscriber in the exchange. To read out several hundred groups, the command CHSOP is used.
Figure 5.15Output of call meters for one subscriber
<CHSIP:SNB=700000010;
WO MARIEFRED AT-2 TIME 960304 1320 PAGE 1CALLMETER VALUES READING
INDIVIDUAL READING
SNB TCM A CMV1 CMV2 CMV3 CMV4 TYPE700000010 4 00009823 00000003 00000089 00000000 MCV1 MCV2 CACV ADCV 00000007 00000000 00001278 00000000END

Charging
79
8.13.5 Charging StatisticsIf an operator changes his charging programs, it is of course interesting to know how the customers have been affected by the change. The function for charging statistics can give this type of information to the network operator. The results obtained can be the number of started charged calls and the total number of pulses during the recording period. The recordings can be set on tariff classes or day categories within tariff classes.
8.13.6 High Cost/Long DurationThis function can issue an alarm if a call is charged with more than a preset number of charging pulses. The number of pulses and the time can be set with command CHHSI/CHLSI (between 0 and 32000 pulses or between 2 and 10 hours).
8.14 The Calendar FunctionThe calendar function in AXE is controlled by a clock that is handled by the operating system in APZ. The clock is used by several functions in the system that require a real time clock. Examples of such functions are charging, routine tests and traffic recording. The clock can be printed at any time by using the command CACLP. Figure 5.16 shows the printout received.
Figure 5.16A printout of the system clock
The clock is controlled and incremented by the APZ. Over a long period of time, the clock may start losing or gaining. This fact makes it necessary to check and (in some cases) adjust the clock at regular intervals. However, the adjustments should not be more than a few seconds over a time period of several month. The command CACLC is used to adjust the clock. Here is an example of the command:
CACLC:TDSF=5;
The command orders a 5-second forward adjustment of the clock. The time it takes before the clock has been adjusted is twice the adjusted time.
Of course, the clock in AXE must be adjusted in countries using summer time and winter time. The adjustment is one hour in either direction. To adjust the clock we use the command CACLC:
<CACLP;TIMECLOCK TYPE RTU STATEREAL TIME CLOCK NOT CONNECTED
DATE TIME DAY DCAT960228 130245 WED 0END

Exchange Data
80
CACLC:DATE=960323,TIME=0200,TDSF=3600;
This command will put the clock forward one hour at 0200 hours on March 23, 1996. The use of the parameters DATE and TIME makes it possible to order the adjustment in advance.
The day categories used in the switching class are set by command. When the exchange is installed, the day categories are set according to the requirements of the operator. This information can be printed by using the command CACAP. Figure 5.17 shows an example of the printout received.
Figure 5.17Printout of day categories
Days that deviate from the standard day categories, for example, Christmas and other public holidays in the middle of the week, must be specified manually by the operator. If Christmas is in the middle of the week, the days with day category DCAT-1 and DCAT-2 must be defined to the system by using command CACAS. An example of the command is:
CACAS:DATE=961225,DCAT=2;
If day categories are to be removed from the list, the command CACAR has to be used.
<CACAP;CALENDARDAY DCATMON 0TUE 0WED 0THU 0FRI 0SAT 1SUN 2
DATE DCAT960404 1960405 2960408 2
MAXIMUM VALUE OF DCAT: 9END

Charging
81
8.15 Chapter SummaryFrom this chapter you should remember these points:
• Pulse metering or toll ticketing, or a combination of both, can be used as charging method.
• There are some core blocks in the subsystem and, depending on the functions requested by the customer, a number of optional blocks.
• The “traffic activity analysis” is used when charging subscriber service procedures and similar traffic cases.
• The “charging case branching analysis” is used to adapt the charging to different parameters.
• The “charging program analysis” determines among other things the tariff class to be used.
• The” extended charging analysis”, which is optional, is used when charging special events such as connection of IWU.
• The “switching class analysis” is a time table for handling of time differentiated charging.
• The “tariff data” specifies all the tariffs in the exchange. The time in seconds between the pulses as well as number of pulses at B-answer are two important parameters.
• Accounting is used when more than one operator is involved in the call. The purpose of accounting is to determine how the operators should split the revenue of each call.
• The calendar function, which is an APZ function, specifies day categories which control the charging function (as well as other functions).

Exchange Data
82

83
9. B-number Analysis
Figure 6.1Chapter Objectives
9.1 IntroductionThe B-number analysis table is the table that analyses the dialled B-number. The table delivers a large number of analysis results which are used in other analysis tables, e.g. Route and charging analysis. The contents of the table reflect the network environment of the exchange such as the numbering plan and the charging plan. Prior to the B-number analysis is a pre-analysis performed. This chapter describes how data can be loaded, printed and changed in the analysis tables.
9.2 Pre-analysis of B-number InformationBefore the actual B-number analysis can be started, the type of B-number must be analysed. The main reason for this analysis is that an ISDN network may communicate with various types of networks having their own numbering plans and ways of numbering their connected terminals or subscribers. An ISDN terminal can indicate the B-number type, and for international calls the B-number type can be sent along with the signalling system. Three parameters are used in the analysis:
• BO, origin of B-number analysisThis is a subscriber category or route data set for an incoming route.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the data included in the pre-analysis
• describe the data included in a simple B-number analysis table
• describe the interwork inside the system when digits are analysed in the B-number analysis table
• use the commands related to the function for changing data in the table.

Exchange Data
84
• NAPI, numbering plan indicatorDifferent values are assigned different numbering plans. Examples of existing numbering plans:- NAPI=0, unknown- NAPI=1, ISDN and telephony (E.164/E.163)- NAPI=2, data network (X.121)- NAPI=3, Private Numbering Plan- NAPI=4, telex numbering plan- NAPI=5-15 are spare.
• BNT, B-number typeThis parameter specifies the type of B-number. Examples:- BNT=0, reserved- BNT=1, international number- BNT=2, unknown- BNT=3, subscriber number- BNT=4, national significant number- BNT=5, network specific number.
These parameters are entered into the pre-analysis of B-number analysis table. The data specifies one of two possible output parameters:
• OBA, origin for B-number analysisThis parameter is used as a “start position” in the B-number analysis. It also means that the original parameter BO has been changed by the analysis.
• ES, end-of-selection codeThe parameter will be used in the end-of-selection analysis described further on in this book.
Figure 6.2 shows an example of a pre-analysis of B-number information table.
Figure 6.2Pre-analysis of B-number, example
<PNBSP:BO=ALL;
PRE-ANALYSIS OF B-NUMBER INFORMATION
OPERATING AREABO NAPI BNT RESULT0 1 1 OBA=2000 1 2 OBA=2000 1 3 OBA=2000 1 4 OBA=3000 2 1 OBA=4000 2 2 OBA=4000 2 3 OBA=400END

B-number Analysis
85
9.3 Example of an Analysis TableWe are now, finally, going to look at the analysis table that has supplied all the information for the other analysis tables. From the B-number analysis table we have received the routing case and the charging case. To illustrate the principle of B-number analysis, we are going to use a simple network with a few exchanges. The B-number analysis table that we are going to study is located in the exchange A. Please study the simple network in Figure 6.3.
Figure 6.3Example of a simple network
As can be seen, our exchange (A) has 100 subscriber lines connected to it. The number series starts with 12000 and ends with 12099. Internal calls are charged according to CC=4. The other exchanges, B, C, D and E, form the local network. RC=11 applies to calls to exchange B which has a number series starting with 31xxxx. RC=13 applies to calls to exchange C with a number series starting with 32xxxx. RC=10 applies to exchanges D and E with number series starting with 65xxxx and 67xxxx, respectively. All calls to the local network are charged according to CC=3. Long-distance calls with area codes “01” and “02” are charged according to CC=1 and CC=2 respectively. RC=10 also applies to long-distance calls.
What, then, does the B-number analysis table look like in exchange A? The answer can be seen in Figure 6.4.
12000 12099
31xxxx 32xxxx
65xxxx67xxxx
RC=11 RC=13
RC=10
AB C
DET
Local callsCC=3
Internal callsCC=4
Trunk calls01 => CC=102 => CC=2

Exchange Data
86
Figure 6.4The B-number analysis table in exchange A
Note that this is the minimum contents for handling the traffic described earlier. As will be described later, subscriber services etc. require more data. Each column is described below:
• B-NUMBERThis column contains two items: the origin and the B-number. Origin, which is the digit to the left, is used to divide the whole B-number analysis into different parts (different branches in the tree). The origin is either affected by the pre-analysis or by the subscriber category “OBA” (set by command SUSCC). For incoming routes, the command EXRBC:R=....,BO=xx; can be used. The B-numbers are then listed in numerical order. The number of digits included for each group of numbers depends on how many digits the administration wants to analyse.
• MISCELLThis column contains various types of parameters such as destination codes, number modifications and traffic destination codes. If more than one area code is defined in the exchange, the column indicates the area code tied to the number series. By means of various parameters, the table can order the register to request information from the incoming side of the call. Examples are A-subscriber class, A-number and satellite information.
• F/NThis column is used to make jumps in the analysis table. Two parameters can be used here: “F” for first and “N” for next. First means that the analysis is started from the first digit in the origin stated after
<ANBSP:B=ALL;B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER MISCELL F/N ROUTE CHARGE L A0-0 N=10-1 CC=4 L=80-120-120 TE0-3 CC=3 L=60-31 RC=110-32 RC=130-6 RC=10 CC=3 L=60-650-671-1 RC=10 CC=1 L=8-131-2 RC=10 CC=2 L=8-13
END

B-number Analysis
87
the parameter. Next means that the analysis is continued with the next digit in the stated origin.
• ROUTEThis column contains references to routing cases, RC, and terminating traffic, TE.
• CHARGEThe column gives references to charging cases.
• L, number lengthThis column indicates the length of the B-number. If the length is unknown, the minimum and maximum values of the number length is specified (min-max, e.g. 9-15).
• A, accounting caseFor references to accounting cases.
9.3.1 An Outgoing CallWe will now study an example of how the analysis table depicted in Figure 6.4 is used and how the register controls the analysis of the digits.
A subscriber in exchange A wants to call a subscriber in exchange C with number 321069 (refer to the network diagram in Figure 6.3). The subscriber lifts the handset and dials the digit “3”. The digit is received in the subscriber switch (by LIC or KRC) and the digit is forwarded in the software to the register in subsystem TCS, traffic control subsystem. The digit “3” is stored in the register and is then sent to function block DA where the B-number analysis table is situated. Figure 6.5 shows the principle.
Figure 6.5Analysis of the first digit dialled by the subscriber
Traffic Control Subsystem, TCS
Digit “3”
"3" Analysisresult
Routeanalysis
B-numberanalysis
Charginganalysis
Block RE

Exchange Data
88
What results could be expected? As shown in Figure 6.3, the call could be addressed to exchange B or C. Both exchanges have two things in common:
• Same charging case (CC=3)
• Same number length (6 digits).
This means that some data is available after the first digit. This information can also be obtained from the B-number analysis table in Figure 6.4 if the line “0-3” is studied (origin 0 and digit 3). Under the heading CHARGE we find CC=3, and under the heading L, we find the number length L=6.
What, then, happens to the analysis result? The information about the number length is stored in the register to indicate the expected number of digits. The information indicating the charging case is immediately sent on to subsystem CHS for the charging analysis. The result from the charging analysis consists of data showing how the call is to be charged, such as the tariff class (TC). Figure 6.6 shows how the digit 3 is analysed in the system.
Figure 6.6Analysis of the first digit and the charging case, CC
After a short while, the subscriber dials the second digit, the digit “2”. The digit is sent, as usual, to the register for storage and is then sent to the block DA for B-number analysis. In this case, the digit 2 indicates to which exchange the call is directed. By looking at line 0-32 in the B-number analysis table (Figure 8), we find RC=13 under the heading ROUTE. The analysis result sent back to the register is a routing case. The register will immediately send the routing case to block RA for route analysis. The result from the route analysis is, among other things, the identity of the outgoing route and the sending program. Figure 6.7 shows the signalling inside the system.
Traffic Control Subsystem, TCS
Digit "3"
"3" CC=3L=6
Routeanalysis
B-numberanalysis
Charginganalysis
Block RE
CC=3
TC=xx

B-number Analysis
89
Figure 6.7Analysis of the second digit and the routing case, RC
As will be seen from the B-number analysis table, no more analysis results can be obtained (no more digits in this part of the analysis as 0-32 is followed by 0-6 in the table). The block DA will indicate that to the register by entering “end of analysis” as the last analysis result. This implies that the remaining four digits dialled by the subscriber will not be analysed. They will, however, be stored in the register. The next action to be taken by the register is determined by the data in the sending program.
At this point, the following information is stored inside the register:
• number length: 6 digits
• tariff class
• identity of outgoing route
• sending program
• digits in B-number: 3 and 2.
9.3.2 An Internal CallThis study case will describe an internal call inside the exchange A. As can be seen in Figure 6.2, only one “hundred group” is specified in the exchange. The numbers are defined in the exchange with the command EXNSI and the subscriber number is associated with a line interface circuit by using command SULII.
A subscriber lifts the receiver and dials the number “1”. As will be seen from the network data, this must be an internal call (12000-12099 defined as internal numbers). The B-number analysis table shows that the number length 5 can be found under the heading “L” in the table (look at line 0-1). Also the charging case 4 is indicated under the heading “CHARGE” as all internal calls have this charging case.
Traffic Control Subsystem, TCS
Digit "2"
"2"
Routeanalysis
B-numberanalysis
Charginganalysis
Block RE
RC=13End of analysis
RC=13
R=
"AB
C"
SP
=xy
z

Exchange Data
90
The subscriber then dials the digit “2”. In this case, the B-number analysis table delivers no result at all as nothing is indicated on the line 0-12 in the table.
The third digit dialled by the subscriber is the digit “0”. In this case, the parameter “TE” is indicated under the heading ROUTE. That parameter is used to indicate a terminating call. But why is TE not indicated when the first digit is analysed? The answer can be found in the internal structure of the system. It is not possible to indicate TE until the analysis has reached the “thousand” or “hundred” group level. The reason for this is that the register has the possibility to add the last part of the B-number and then translate the B-number into internal numbering, referred to as the SC pointer. The SC pointer is composed of the hundred group number and the last two digits in the subscriber number.
9.3.3 Parameters in the Analysis TableSubscriber services often use procedures that the subscribers have to dial in order to activate, deactivate and use the service. Examples of subscriber procedures are activation of call transfer (*21* b-no #) and deactivation of don't disturb (#26#).
These digits and codes (* and #) are dialled by the subscriber and analysed as ordinary digits. The two codes * and # are represented in the analysis table as follows:
• * #11
• # #12
This means that the digits *51# will be written in the analysis table as #1151#12.
Another parameter which is rather common is the parameter “M” that can be found under the column MISCELL. The parameter M is used for modifying the B-number and it may consist of one or two sub-parameters. The following two examples illustrate the use of the parameter:
• M3Three digits are deleted from the B-number. Can be used to delete the trunk prefix as the deletion is made from the first digit dialled by the subscriber.
• M3-045Three digits are deleted from the B-number and the digits “045” are added in front of the number instead. If M0-045 is used instead, no deletion is made.
Here are some more parameters which have not been mentioned before. For more information, please the study command description for command ANBSI.
• DT, dialling toneThis parameter can be used if a second dialling tone is wanted. In some

B-number Analysis
91
countries, a second dialling tone is given after, for example, the country code.
• NE, number endFor subscriber procedures, the button # on the telephone is used to indicate the end of the procedure. In the B-number analysis table, the parameter NE is used to indicate that the complete number has been received.
• TN, table test numbersThis parameter is described in more detail in the chapter "Test of not Activated Data" on page 95.
• TRD, traffic destination codeThis parameter is used for statistics on destination (traffic destination recording).
9.3.4 CommandsWhen introducing changes in the B-number analysis table, an operating and a non-operating area have to be used. The principle is similar to the OP and NOP areas used for routing cases and charging cases. However, the handling of the OP and NOP areas differs in some respect.
When a routing case was specified in the NOP area, it was handled as one unit in the commands. One RC could be cleared in the NOP area, one RC at a time could be activated and one RC could be deactivated. The same thing applied to charging cases and tariff classes. When working with the B-number analysis table, the whole table has to be seen as one unit. This means that the whole table is activated and deactivated. Figure 6.8 shows the principle.

Exchange Data
92
Figure 6.8The commands for specifying new data in the B-number analysis table
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER0-00-1......END
B-NUMBER ANALYSIS DATANOT OPERATINGB-NUMBER0-00-010-02...END
Operating area, OP Non-operating area, NOP
NOP area is cleared by ANBZI
OP area copied into NOP area by ANBCI
New data is specified in NOP area by ANBSI
New data activated by ANBAI
Return to old data possible by ANBAR
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER0-00-1......END
B-NUMBER ANALYSIS DATANOT OPERATINGB-NUMBER
END
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER0-00-1......END
B-NUMBER ANALYSIS DATANOT OPERATINGB-NUMBER0-00-1......END
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER0-00-1......END
B-NUMBER ANALYSIS DATANOT OPERATINGB-NUMBER0-00-1...10-5 CC=2310-55 TE...END
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER0-00-1...10-5 CC=2310-55 TE...END
B-NUMBER ANALYSIS DATANOT OPERATINGB-NUMBER0-00-1......END
Initial state, old data in NOP area
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER0-00-1......END
B-NUMBER ANALYSIS DATANOT OPERATINGB-NUMBER0-00-1...10-5 CC=2310-55 TE...END

B-number Analysis
93
The commands are described briefly in the text that follows:
• ANBZIThe command is used to clear the NOP area. Note that the whole area is cleared.
• ANBCIThe command copies the entire B-number analysis table from the OP area into the NOP area. This means that the operator can “edit” the existing table in the NOP area by means of commands.
• ANBSIThis command is used to introduce new data into the NOP area of the table.
• ANBSEThe command is used to delete data from the NOP area.
• ANBAIThe command activates the whole NOP area and makes it operating. The old data, previously in the OP area, is now in the NOP area and write protected for 24 hours.
• ANBARIf the data is faulty, a single command need be entered to return to the old analysis table. After change with ANBSI and/or ANBSE, the table can be activated again with ANBAI.
• ANBLIThe command can be used to remove the write protection on the NOP area. The command should not be used in normal cases as the “back-up” of the analysis table might be destroyed.
• ANBSPThe command prints the operating or the non-operating areas of the table. For a real exchange, the table is very large (could be more than 25 pages). Parameters may then be used to print parts of the table.
Here are some examples:
• ANBSP:B=ALL; prints the whole table
• ANBSP:B=0; prints origin zero
• ANBSP:B=20,RC=ALL; prints all B-number series with routing cases in origin 20
• ANBSP:B=ALL,CC=ALL; prints all B-number series with charging cases in all origins.
• ANBSP:B=ALL,TE; prints all number series in all origins which terminate in the exchange.
• ANBSP:B=ALL,COMP; prints the differences between the operating area and the non-operating area.
The command will search for the specified conditions and only print the parts that meet all the requirements. The search time may be quite long and the text “WAIT” is printed while the program is searching (done on a lower priority level than the traffic handling). Note also that the parameter

Exchange Data
94
NOP must be added if the non-operating area is to be printed (ANBSP:B=ALL,NOP;).
9.3.5 Specification of Area CodeIn chapter 7 “Hundred Groups”, the definition of internal number series was studied. The command EXNSI was used to define new hundred series in the exchange, If an area code was to be defined in the exchange, this could be done in two different ways:
1. One implied area code defined with command EXIAI.
2. Several area codes defined together with the number series in command EXNSI.
In the first case (one implied area code), no special actions are required when defining the B-number analysis table. However, if more than one area code is used in the exchange, the area code must be specified in the B-number analysis table as well. This can be done in two different ways, with parameter “AREAL” or “AREA”. The first parameter indicates the length of the area code in number of digits. Figure 6.9 shows an example.
Figure 6.9Area codes 020 and 021 defined in the analysis table
In this case, the complete number is specified, including area codes “020” and “021”. When the thousand group level is reached, the parameter “TE” indicates that there is a terminating call. The parameter “AREAL=3” indicates that the first three digits belong to the area code (020 and 021). This information makes it possible for the register to remove the area code when making the internal “SC pointer”.
<ANBSP:B=ALL;B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER MISCELL F/N ROUTE CHARGE L A...0-0200-02040-020450-020450 AREAL=3 TE......0-0210-02150-021550-021551 AREAL=3 TE......END

B-number Analysis
95
The specification in the analysis table could also be made with the parameter “AREA”. This requires that the analyses for the different area codes are made in different origins. The parameter “AREA” indicates to which area code the number belongs. Figure 6.10 shows an example.
Figure 6.10Definition of area code by using parameter AREA
A jump to origin 10 and 20 is made for the different area codes. In these two origins, the analysis continues. When the thousand group level has been reached, the parameter “TE” indicates that the call is terminating. The parameters “AREA=020” and “AREA=021” indicate to which area code the number series belong.
Note that the specifications in Figure 6.9 and Figure 6.10 have the same function.
9.3.6 Test of not Activated DataBefore extensive changes are activated in several analysis tables, the data can be tested and checked by making test calls that fetch the data from the non-operating areas. This is possible thanks to the use of certain test numbers. The test numbers are dialled and the system will set up a normal call with the data stored in the NOP areas. The following test numbers are used:
1. TN=BP, test of B-number pre-analysis
2. TN=B, test of B-number analysis
3. TN=EA, test of equal access analysis
4. TN=R, test of route analysis
<ANBSP:B=ALL;B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER MISCELL F/N ROUTE CHARGE L A...0-020 N=100-021 N=20......10-4 L=910-4510-450 AREA=020 TE......20-5 L=920-5520-551 AREA=021 TEEND

Exchange Data
96
5. TN=AP, test of A-number pre-analysis
6. TN=E, test of end-of-selection analysis
How can the test numbers be reached? The answer is simple. By, for example, stating the parameter TN=B in the B-number analysis table under a certain prefix, the numbers are used if the prefix is dialled by the operator’s staff but the ordinary subscribers are barred from this number by means of the destination code (D=12-0). Please study the access barring analysis in chapter 11 for more information. Number modification is used to delete the prefix dialled. Figure 6.11 shows an example from a B-number analysis table.
Figure 6.11Specification of test number for the B-number analysis, example
9.3.7 Chapter SummaryFrom this chapter you should remember these points:
• The entry point, the so-called origin, in the B-number analysis is determined by the function pre-analysis of B-number.
• The B-number analysis table has one operating and one non-operating area.
• The area is handled as one unit and cannot be partly copied, activated, deactivated or erased.
• The origin is the entry position of the table and jumps can be made between different origins by means of the parameters F and N.
• The digits * and # dialled in subscriber procedures are indicated with #11 and #12 in the table.
• The parameter M can be used to modify numbers.
• The parameters AREA and AREAL have to be used if more than one area code is required in the exchange.
• Test numbers can be used to test the data in the non-operating area before it is put into service.
<ANBSP:B=ALL;B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER MISCELL F/N ROUTE CHARGE L A...0-099 TN=B D=12-0 M=3......END

97
10. End-of-Selection Analysis
Figure 7.1Chapter Objectives
10.1 IntroductionEnd-of-selection is a telephony term indicating that the B-subscriber has been identified and that the selection of a path has been concluded. In the AXE system, the scope of the term has been expanded to include an analysis table. The purpose of the analysis table is to specify the actions to be taken in case of congestion, technical faults and other abnormal events during a call. The analysis table is also used for redirecting calls to announcing machines or subscriber services. This chapter describes how the table is interpreted and how it can be changed by means of commands.
10.2 The Purpose of End-of-Selection AnalysisIn general telephony terms, End-of-selection is the point in a call setup sequence where the selection is completed and ringing signal is sent to the B-subscriber. However, the setup of a call may be affected by several types of events. Examples:
• Technical faults in any part of the network
• Congestion in any part of the network
• The B-subscriber has services activated that affect the call
• B-subscriber is busy.
What, then, should be done when abnormal events like these are detected? The answer is found in a function referred to as “end-of-selection analysis”. Basically, there are two ways to handle errors in the system:
Chapter Objectives
After completing this chapter, you will be able to:
• explain the purpose of the end-of-selection analysis inside the AXE system
• explain the use of end-of-selection codes in the system
• find the end-of-selection codes in the B-module
• print, interpret and change the end-of-selection analysis table
• describe the most common actions ordered from the EOS table.

Exchange Data
98
• Tones are sent to the subscribers (e.g. busy tone or congestion tone)
• Announcements from announcing machines are sent to the subscribers.
Most of the required actions are decided on by the network operator. This means that the function must be flexible in order to permit changes. The solution is, of course, a table that decides on the action to be taken in each case. The table can be changed by means of commands.
Inside the AXE system, the end-of-selection analysis is also used for normal events. When subscribers have services activated (e.g. Call Transfer), the block inside AXE that detects this uses the end-of-selection analysis for redirecting the call to the function that controls the service.
The end-of-selection analysis can also be used for advanced routing programs in co-operation with the route analysis. It is possible to have delayed seizure in routes or to block routes for traffic without priority. For ISDN subscribers, a cause code can be generated. The cause code is sent back to the calling terminal and can be translated to a text string or message on the computer screen (for example “Connection failed due to errors in the called LAN”).
On completion of subscriber procedures for activating and deactivating services, the end-of-selection analysis function is also used to redirect the subscriber to an announcing machine indicating that the service is activated / deactivated.
10.3 End-of-Selection CodesIn order to identify all occurrences that are detected in the system, these are given unique numbers, so-called “end-of-selection codes” (EOS codes). When a function detects an abnormal event, e.g. congestion or technical fault, an end-of-selection code is generated and sent in a signal to block RE, register, as this block is responsible for all actions taken during call establishment. The register will forward the EOS code in another signal to block RA, route analysis, which contains the end-of-selection analysis table. Please study Figure 7.2.
Figure 7.2General principle for handling of end-of-selection codes
Block X
Signal withEOS code
Traffic Control Subsystem, TCS
Block RE
EOS code
Result
Block RAEOS ANALYSIS DATAOPERATING AREAES BE1 ...2 ...3 ......END

End-of-Selection Analysis
99
Remember that since each occurrence defined in the system has a unique number, many EOS codes defined in the system today. In total, some 2000 codes have been defined. The B-module contains information about the meaning of the EOS codes and the block that generate them. There are two ways to find the EOS codes in the B-module:
1. In the Application Information of the block that generates the EOS code. It is the block that detects the occurrence or state that generates the code. If block SC finds that a subscriber is barred for incoming traffic, it is SC that generates the EOS code.
2. In a numerically sorted list at the end of B14.
If the Application Information is used, all the EOS codes that can be generated by the block are listed. The numerically sorted list contains also information about recommended action. Figure 7.3 shows the two possibilities.
Figure 7.3Two ways to find data about the EOS codes in the B-module
10.4 The Analysis in Block RAAs said before, the actual analysis table is located in block RA, route analysis. This block has been studied before in this part of the book as the route analysis (routing cases) is performed here as well. The analysis is made in a large table that contains one position for each EOS code used in the exchange. The layout of the table can be seen in Figure 7.4.
Block known
ApplicationInformation
EOS code
EOS codeknown
Parameter list
Block and some moreinformation about eachEOS code

Exchange Data
100
Figure 7.4End-of-selection analysis table, example
The different columns are described below:
• ES, end-of-selection codeEach defined EOS code is listed in this column. Note that the list might have numbers left out as some blocks are not included in the Application System.
• BE, branchingBranching can be used if some traffic cases or subscribers should be handled differently in the analysis. Several parameters can be used for the branching; see description in the last part of this chapter.
• M, modification of B-numberIn some cases, the B-number is modified in order to redirect the call (to an announcing machine or to a subscriber service). In that case, the parameters in this column are used to indicate how the number is to be modified. The parameter is specified x-yyy where “x” is the number of digits to be deleted and “yyy” are digits added before the remaining digits in the B-number.
• EOSRESThis column is used to specify the actions that should be taken for each occurrence (EOS code). The parameters found under this heading are further described in the next part of this chapter.
10.5 Actions Possible to Initiate in the EOS TableSome 14 different actions can be specified under the heading EOSRES in the table depicted in Figure 7.4. Some of the most common alternatives are described in this chapter.
<ANESP:ES=1&&-5;
END-OF-SELECTION ANALYSIS DATAOPERATING AREA
ES BE M EOSRES1 EO-0 ESS=5,CAU=0-51 EO-1 ESS=5,CAU=0-522 COS=143 3-015 F=04 ESS=95 ESS=9
END

End-of-Selection Analysis
101
1. ESS, end-of-selection signalThis means that a signal is sent to the subscriber or to the incoming exchange. In case of signals to subscribers, the subsystem SSS will translate the internal signal into a tone that is sent to the subscriber. Which tone to send is determined by the administration as different variants exist in different countries. An example of an ESS signal is ESS=3, “busy subscriber”. The application information for block RA lists the possible values.
2. COS, congestion signalA signal is sent to the subscriber or the incoming exchange. The congestion signal is used to indicate congestion, technical faults and time release. In this case too, the SSS will translate the signal into a tone that is sent to the subscriber. For an incoming call, the block that handles the signalling will translate the COS signal into a register signal. An example of a congestion signal is COS=6 meaning “technical fault”.
3. FRE, forced releaseThis means that the call will be disconnected immediately. This action can be taken when no signal can be sent to the subscriber, e.g. as a result of technical faults in the subscriber switch.
4. F and MThese parameters are used to indicate that a new B-number analysis should be performed. The parameters are used together with the B-number modifying parameter in the column “M”. When “F” is used, the B-number analysis should start from the first digit again. The digit after the parameter F (e.g. F=99) indicates the origin in the B-number analysis table. If rerouting is made to a subscriber service, F is used and the B-number is modified by adding some digits before the original B-number. The digits added have no meaning as they are used for the rerouting only.
5. SR, new seizure attempt in the same routeThis parameter is used if the administration wants to have a second try in the same route for one routing alternative.
6. DSR, delayed seizure attempt in the same routeSame as for SR but there is a delay before the new attempt is made. The delay is two to three seconds.
7. CAU, cause codeIn ISDN traffic, tone sending is replaced by text strings displayed on terminals. Within the network, the reason for an error is represented by a cause code. The code is translated into text by the subscriber’s terminal. The application information for block RA lists the possible values.

Exchange Data
102
10.6 Branching in the EOS TableAs in the route and charging analysis, it is possible to perform branching on various parameters. Branching permits different handling of some routes or subscribers in the end-of-selection analysis. The parameters available for branching are:
• EO, origin for EOS analysis (value 0-255)This parameter is used for incoming routes. The incoming route is given an EO parameter with the command EXRBC.
• PR, priority (value 0-3)Subscribers or number series can be given priority. Subscribers are given priority with command SUSCC, while number series get their priority in the B-number analysis table.
• CL, traffic class (value 0-15)The TCL category, which is the category transferred with the signalling system, can be used as a branching parameter. It is set with command SUSCC.
• AL, alarm state (value 0-2)The exchange can be set in alarm state by means of a command. In normal cases, alarm state zero is valid.
• NA, number of previous connection attempts (value 0-3)This parameter is used when a number of connection attempts should be made before, e.g., a congestion signal is sent.
• NRA, number of redirections (value 0-3)If specific action is to be taken after a specific number of redirections, this parameter is used together with parameters F and M.
• TONETone protection can be used as a branching parameter. Tone protection is used on data calls where no tones should be sent.
When this branching is specified, a procedure must be used. As you will remember, this applies to charging and routing analysis as well. The procedure commands enable the system to check if the branching condition is logical or not. Here is an example:
ANEPI:ES=234;
ANESI:BE=EO-0,ESS=14;
ANESI:BE=EO-1,ESS=15;
ANEPE;

End-of-Selection Analysis
103
10.7 CommandsUnlike earlier versions of AXE, the end-of-selection analysis is now divided into an operating and a non-operating area. The principle is the same as for B-number analysis or route analysis. The commands for changing and inserting data in the end-of-selection analysis table are:
• ANESISpecifies new data for the specified ES code. Data can be overwritten if something is specified already.
• ANESERemoves data from the table for the specified ES code.
• ANESPPrints the whole or part of the table.
• ANEPIInitiates a procedure (mandatory if branching is used)
• ANEPETerminates a procedure.
• ANEAIActivates the data in the NOP area
• ANEARReturns to old data for a changed EOS. Please note that due to the 24 hour protection time, the command only works within 24 hours. After this time, the data in the NOP area is cleared.
10.8 Chapter SummaryFrom this chapter you should remember these points:
• All abnormal calls are analysed in the end-of-selection analysis table in order to see how the call should be treated.
• Normal calls can use the function for diversion to services or announcing machines.
• The EOS analysis table is located in block RA.
• A procedure has to be used if the end-of-selection analysis includes branching.
• An operating and a non-operating area are used.

Exchange Data
104

105
11. Access Barring and Time Supervision
Figure 8.1Chapter Objectives
11.1 IntroductionThe destination code originates from the B-number analysis table and the purpose of the code is to make it possible to mark the destination of a call. The destination can then be used for different purposes such as network management functions, traffic recordings and access barring. In this chapter, the access barring function is studied.
11.2 Access Barring in GeneralThe purpose of the access barring function is to restrict the traffic from some subscribers to certain areas in the network. As an example, a subscriber can be barred from calling international numbers. The function is also used to prevent ordinary subscribers from calling certain test numbers used by the PTT only.
11.3 Destination CodesThe key to the access barring function is the “destination code” that originates from the B-number analysis table. In the B-number analysis, a certain destination code is tied to a specific B-number in the network (e.g. a trunk prefix). As an example, if the international prefix (00 in most countries) is dialled by a subscriber, it can be determined that he/she would like to make an international call. If the subscriber is barred from such traffic, this is easily detected by specifying a certain destination code for that number in the B-number analysis table. Figure 8.2 shows a B-number analysis table with some destination codes.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the principles of access barring in the system
• print and change the access barring analysis table
• understand how time supervision analysis is performed.

Exchange Data
106
Figure 8.2Destination codes in the B-number analysis table
The codes, found under the heading “MISCELL”, are given numbers according to certain rules. A destination code consists of two parts: D=x-y where “x” is the main destination code and “y” is the sub-destination code. The allocation of main codes should follow the numbering that can be seen in Figure 8.3.
Figure 8.3Allocation of the main destination code
B-NUMBER ANALYSIS DATAOPERATINGB-NUMBER MISCELL F/N ROUTE CHARGE L A0-20 RC=101 CC=5 L=8 D=4-00-21 RC=107 CC=6 L=8 D=4-00-24 RC=121 CC=9 L=8 D=4-00-31 RC=155 CC=7 L=8 D=6-00-32 RC=161 CC=7 L=8 D=6-00-33 RC=178 CC=7 L=8 D=6-0
END
Destination Code Meaning0 - - - - - - - Seizure of RE1 - - - - - - - Own B-subscriber2 - - - - - - - Own local area type 13 - - - - - - - Own local area type 24 - - - - - - - Interurban traffic type 15 - - - - - - - Interurban traffic type 26 - - - - - - - International traffic type 17 - - - - - - - International traffic type 28 - - - - - - - Traffic to operator in other exchange9 - - - - - - - Traffic to subscriber service in other exchange type 110 - - - - - - Traffic to subscriber service in own exchange11 - - - - - - Traffic to special service in own exchange12 - - - - - - Traffic to test equipment13 - - - - - - Traffic to subscriber service in other exchange type 214 - - - - - - Traffic to operator in own exchange15 - - - - - - Spare

Access Barring and Time Supervision
107
If more destination codes are required by the administration, the sub-destination code can be used. As the sub-destination code can have a value range between 0 and 15, up to 16 new destination codes can be defined per main destination code.
11.3.1 Subscriber Category CBA and Route Parameter TDCLIf a subscriber would like to have the access barring function, the administration must change his/her CBA category. The CBA category is changed by using command:
SUSCC:SNB=snb,SCL=CBA-x;
Also incoming routes can be barred by giving them a specific route parameter. The parameter is referred to as TDCL, trunk discriminating class, and is given to the route by the command EXRBC. The only routes that should be changed are incoming test routes from test equipment. These routes are usually given a TDCL value which gives them full access to all numbers.
11.4 Access Barring AnalysisWhen the B-number is analysed in block DA, the destination code might be one of the analysis results sent back to the register. If this is the case, the register will send the destination code for analysis in block DA (a table other than the B-number analysis table). The analysis is made in a table specified by command.
In the table, the destination code is translated into a trunk discrimination class, TDCL, that is used to see if the call is allowed or not. Figure 8.4 shows an example of the table called “access barring data”.

Exchange Data
108
Figure 8.4Printout of access barring data, example
What, then, determines whether the call is allowed or not? To check that, the CBA value from the subscriber is compared with the TDCL value derived from the destination code. If they are equal, the call is not permitted. Figure 8.5 shows the principle.
Figure 8.5The principle of access barring analysis
The access barring data in Figure 8.4 show that not even ordinary subscribers with CBA=0 can call numbers with destination code 12. This code (12) is used for indicating traffic to test equipment belonging to the operator. In order give the operator’s test telephones access to this equipment, their CBA categories should have the value 3.
<ANDSP;
ACCESS BARRING DATAD TDCL
1-0 142-0 33-0 34-0 2 36-0 1 2 38-0 38-1 39-0 310-0 3 410-1 3 412-0 0 1 2 4 5 6 7 8 9 10 11 12 13 14 1512-1 15
END
DestinationCode (D)
Block DAAccess BarringData
TDCL=CBA
TDCL=CBAPermittedtraffic case
Not permittedtraffic case
Subscriber category (CBA)
D => TDCL

Access Barring and Time Supervision
109
The access barring is handled with the following commands;
• ANDSP Prints the “access barring data”
• ANDSI Initiates new data into the table (per destination code)
• ANDSE Removes data in the table (only possible if there are no references to it from the B-number analysis table)
• SUSCC Changes the CBA category for local subscribers
• EXRBC Changes TDCL for incoming routes.
11.5 Time Supervision in generalAll networks have a so-called “numbering plan”. Numbering plans are prepared for the international network, national networks, and regional networks. Examples:
• International network:
− 44: UK
− 45: Denmark
− 46: Sweden
− 47: Norway
• National network in Sweden:
− 011: Norrköping
− 013: Linköping
− 016: Eskilstuna
Within each area, the numbering plan connects a defined (open) number series to a specific exchange. In some networks, a fixed number length is used (for example in the US). In other networks, for example in Sweden, the length of the subscriber number varies between 5 and 8 digits.
When setting up a call to a remote network, perhaps in another country, the number length might be unknown. Usually, the maximum and the minimum length of the number is known. In the B-number analysis, the parameter L is set to 8-10 for example. This means that the length of the expected B-number is at least 8 digits and not more than 10. What should the exchange do when 8 digits have been received from the subscriber? Should more digits be entered, or has the last digit been received? The only way to determine this is by measuring the time it takes for the subscriber to dial the next digit. In normal cases, the time supervision between the digits is set to some 15-30 seconds. If we reduce this time to about 5 seconds, the exchange will know when the last digit is dialled. If no more digits are entered after the 5 seconds, it is assumed that the last

Exchange Data
110
digit has been dialled. Please note that it is possible to let the receiving exchange determine the length of the number by indicating it in a backward signal. However, some signalling systems cannot do this and in such cases the time supervision analysis has to be used.
11.5.1 The Analysis TableWhen a time supervision analysis should be performed, the parameter TI is delivered by the B-number analysis. Figure 8.6 shows an example of a time supervision analysis table.
Figure 8.6Example of time supervision analysis
The parameter “NTS” stands for normal time supervision while “DTS” stands for decreased time supervision. The first column, origin 0, is used for local subscribers. The other origins can be used if required as the route data for an incoming route can specify another value for the time supervision origin.
The time supervision analysis is handled by the following commands:
• ANTSI, specification and change of time supervision cases
• ANTSE, removal of time supervision case
• ANTSP, printout of data.
11.6 Chapter SummaryFrom this chapter you should remember these points:
• The destination code from the B-number analysis is used as input to the access barring analysis.
• Subscribers are barred to specific destinations by changing their CBA category.
• Incoming routes can be given TDCL categories.
• Access Barring Data is printed with command ANDSP.
<ANTSP:TI=ALL;
TIME SUPERVISION ANALYSIS DATATI ES TSRES(TO 0-3)0 NTS NTS NTS NTS1 DTS NTS NTS NTS2 NTS DTS DTS DTS
END

111
12. A-number Analysis
Figure 12.7Chapter Objectives
12.1 IntroductionB-number analysis was studied in chapter 9. The result of the analysis indicates where the call is directed and how it is to be charged. In some cases, the routing and charging of a call depends on the origin of the call. As we have seen, the origin can be set as route data belonging to the incoming route. In this chapter, we are going to study how the A-number can be used to determine the origin of a call and how it can affect the routing and the charging of the call.
12.2 Pre-Analysis of A-number InformationLike the B-number analysis, A-number analysis is preceded by a pre-analysis. The purpose of the pre-analysis is to determine the type of number (national or international) and to check the NAPI, numbering plan indicator. The output from the analysis is an origin for the A-number analysis. The data is specified with command PNASI and an example of a printout can be seen in Figure 12.8.
Chapter Objectives
After completing this chapter, you will be able to:
• describe why A-number analysis is made
• change data in the A-number analysis table
• interpret a printout of an A-number analysis table
• handle the operating and the non-operating areas of the A-number analysis table.

Exchange Data
112
Figure 12.8Pre-analysis of A-number, example
12.3 Why is A-number Analysis Performed?In order to explain why an A-number analysis is performed, we are going to study a simple network. Figure 12.9 shows a part of a network.
Figure 12.9Part of a national network
PNASP;
PRE-ANALYSIS OF A-NUMBER INFORMATION
OPERATING AREANAPI ANT RESULT 0 OAA=0 1 OAA=0 2 OAA=0 3 OAA=0 4 OAA=0 5 OAA=0 6 OAA=0 7 OAA=0 8 OAA=0 9 OAA=0 10 OAA=0 11 OAA=0 12 OAA=0 13 OAA=0 14 OAA=0 15 OAA=0END
Area 032 Area 031 Chargingdeterminingpoint
4x xx xx 6x xx xx 3x xx xx 6x xx xx 1x xx xxLowtariff Normal
tariff
AB

A-number Analysis
113
The figure shows two areas of the national network. Area “031” has three local exchanges and one transit exchange. Exchange A, whose number series begins with 3xxxxx, is geographically close to exchange B in the other area. The network operator will therefore use a lower tariff between these two exchanges. The other exchanges in area “031” will be charged according to the normal tariff. In this example, the transit exchange is the “charging determining point”, which means that the transit exchange will take care of the charging or send information about the tariffs to be used to the local exchanges.
To solve this “problem” we use the A-number analysis in order to separate the traffic originating from exchange A from other traffic. The traffic from A is “marked” with an origin for charging and this information is then used in the charging analysis. Different tariff classes are pointed out depending on the origin for charging. Figure 12.10 shows the general principle.
Figure 12.10The origin for charging is changed as a result of the A-number analysis
12.4 Analysis ResultsCharging is not the only function that can be affected in the A-number analysis. Here follows a list of parameters that can be changed in the A-number analysis:
• ACO, charging origin from A-number analysisSee the previous chapter.
• RO, routing originThis parameter can be used to route traffic that is dependent on origin. Note that this can also be used for traffic on incoming routes as they can be marked with a specific route origin. However, if the traffic originates from different areas in the network, but is received on the same route, then the A-number is the only way to differentiate the traffic.
• AO, accounting originThis is mainly used in international exchanges in order to control the accounting function. The accounting function resembles the charging
Incoming A-no.3x xx xx
Register
"3" ACO=2
ChargingAnalysis
New originfor charging
A-NUMBER ANALYSIS DATAOPERATIMG AREAA-NUMBER ACO L ...0-1 60-3 AC0=2 6
Pre-Analysis

Exchange Data
114
function but is used to control the charging when different operators are involved in the same call.
• ES, end-of-selection codeAn EOS code can be generated for some A-number series and used to perform number modifications or to send recorded announcements to barred subscribers (e.g. subscribers who are not allowed to generate automatic international traffic).
• NAPI, numbering plan indicatorBy analysing the A-number, a specific NAPI value can be set.
• L, number lengthThe number length is specified if the signalling system is not capable of sending the “number end” signal. Just as in the B-number analysis table, a minimum and a maximum length can be specified.
12.5 Loading and Changing DataThe loading and changing of data in the A-number analysis table is very similar to the handling of the B-number analysis table. As a matter of fact, they are performed in the same block (DA) and the commands they use are identical, except for the third letter. For example, command for changing the B-number analysis is ANBSI, and the corresponding command for the A-number analysis is ANASI. This applies to all commands related to the A and B-number analysis tables. Please study the table below.
The command ANASI can be given with the parameters specified in the previous chapter. If the simple analysis in Figure 12.10 is to be loaded, two ANASI commands are required:
ANASI:A=0-1,L=6;
ANASI:A=0-3,ACO=2,L=6;
These commands will “open” the number series 1 and 3 with all numbers following these digits. The only information loaded for the number series
B-no. analysis A-no. analysis Function
ANBSI ANASI Specify in NO area
ANBSE ANASE Delete from NO area
ANBSP ANASP Print data
ANBZI ANAZI Zero NO area
ANBCI ANACI Copy from OP to NO
ANBAI ANAAI Activate NO area
ANBAR ANAAR Revert to old area
ANBLI ANALI Remove write protection

A-number Analysis
115
1 is the number length. For number series 3, the “charging origin from A-number analysis” is changed to 2.
12.5.1 Printout of the Analysis TableThe analysis table is printed with the command ANASP. See example in Figure 12.11.
Figure 12.11Printout of A-number analysis
The leftmost column contains the A-numbers defined in the table. The maximum number of digits in the table is 10 (10 digits is the maximum analysis depth) but the total size of the table is only limited by a size alteration event (SAE=109). The other columns have the following meaning:
• ROUTEINFThis column contains the route origin or the ES codes defined for the A-numbers.
• ACOThe charging origin from the A-number analysis is indicated here.
• AOOrigin for accounting is indicated in this column.
• LThe length of the A-number is indicated in this column. If the number length varies, minimum and maximum number lengths are specified (e.g. L=5-7).
• MISCELLThis column may contain the parameters “NE” (number end) and “NU” (number unknown). The parameters are used in special cases only.
<ANASP:A=0;
A-NUMBER ANALYSIS DATAOPERATING AREAA-NUMBER ROUTINF ACO AO L MISCELL0-10-2 12 60-30-40-5 40-60-70-80-9
END

Exchange Data
116
12.5.2 Handling of OP and NOP AreasAs mentioned already, the handling of the operating and the non-operating areas is very similar to the handling of the B-number analysis table. Figure 12.12 shows some of the commands related to the function and how the status of the areas are changing.

A-number Analysis
117
Figure 12.12Handling of OP and NOP areas
A-NUMBER ANALYSIS DATAOPERATINGA-NUMBER0-00-1......END
A-NUMBER ANALYSIS DATANOT OPERATINGA-NUMBER0-00-010-02...END
Operating area, OP Non-operating area, NOP
NOP area is cleared by ANAZI
OP area copied into NOP area by ANACI
New data is specified in NOP area by ANASI
New data activated by ANAAI
Revert to old data possible by ANAAR
A-NUMBER ANALYSIS DATAOPERATINGA-NUMBER0-00-1......END
A-NUMBER ANALYSIS DATANOT OPERATINGA-NUMBER
END
A-NUMBER ANALYSIS DATAOPERATINGA-NUMBER0-00-1......END
A-NUMBER ANALYSIS DATANOT OPERATINGA-NUMBER0-00-1......END
A-NUMBER ANALYSIS DATAOPERATINGA-NUMBER0-00-1......END
A-NUMBER ANALYSIS DATANOT OPERATINGA-NUMBER...0-5 ACO=4......END
A-NUMBER ANALYSIS DATAOPERATINGA-NUMBER...0-5 ACO=4......END
A-NUMBER ANALYSIS DATANOT OPERATINGA-NUMBER0-00-1......END
Initial state, old data in NOP area
A-NUMBER ANALYSIS DATAOPERATINGA-NUMBER0-00-1......END
A-NUMBER ANALYSIS DATANOT OPERATINGA-NUMBER...0-5 ACO=4......END

Exchange Data
118
Note that the ANAZI command is only used in case of faulty data or the first time the analysis table is loaded. In normal operation, the command ANACI is used to copy the operating area into the non-operating area. This command will clear the non-operating area before the copying is made.
12.5.3 Blocking of A-number SeriesNote that some A-number series can be blocked if the data is specified in a faulty way. This problem concerns the B-number analysis table as well. Suppose the number series 1, 2 and 3 are opened by specifying:
ANASI:A=0-1;
ANASI:A=0-2;
ANASI:A=0-3;
This means that all numbers starting with any of these three digits are available (listen in the analysis table). For instance, 34512 will be accepted because it begins with the digit “3”.
Suppose we want to “deepen” the analysis so as to include the second digit in the number series starting with “3”. Example:
ANASI:A=0-1;
ANASI:A=0-2;
ANASI:A=0-3;
ANASI:A=0-32;
ANASI:A=0-33;
This means that only numbers starting with “32” and “33” are listed in the table. All other A-numbers starting with 3 are not listed. The numbers starting with “30”, “31” and “34” to “39” are not listed in the table.
12.6 Chapter SummaryFrom this chapter you should remember these points:
• Pre-analysis of A-number information is performed in order to find the A-number type.
• A-number analysis is performed in order to differentiate traffic from different destinations.
• The analysis is performed in block DA, digit analysis.
• The commands are similar to those used for handling the B-number analysis table.
• An operating and a non-operating area are used.
• Care must be taken not to bar certain A-numbers when specifying data in the table.

119
13. Equal Access Analysis
Figure 13.1Chapter Objectives
13.1 IntroductionThe removal of monopoly in various parts of the world has introduced new features in the network. The equal access function is one of these features. The purpose of the function is to allow subscribers to choose national and international long distance operators. This has been used in the US for some time and will be introduced in the countries of the EC.
13.2 SurveyIf you are calling someone in another part of the country, or in some other part of the world, your call is set-up through a large number of exchanges. Traditionally, these calls have been handled by the PTT of the country/countries involved in the call. However, due to changes in legislation in many countries, competition has been introduced in this area. As a subscriber, you can choose which operator to use. Figure 13.2 shows the principle.
Figure 13.2Two operators can be used to reach the same destination
Chapter Objectives
After completing this chapter, you will be able to:
• Describe the main function of the equal access analysis
• Understand the relationship between the B-number analysis table and the equal analysis table.
Operator A
Operator B

Exchange Data
120
From a subscriber’s point of view, the selection is done in two ways:
1. Pre-selected carrierIf the subscriber leases a national or international carrier, the selection in the network is done automatically.
2. Carrier selection by means of a codeBy dialling a so-called “equal access prefix” and a so-called “carrier access code” prior to the B-number, the subscriber can select the carrier from call to call.
Whether one or both of these methods should be available, is mainly determined by the operator and/or local legislation.
13.3 Subscriber category and signalling systemIf a pre-selected carrier access code (CAC) is used, it must be specified by command:
SUEAC:SNB=...,NCAC=...;
NCAC stands for national carrier access code, while ICAC is the, the international carrier access code. It is possible to change the CAC by means of a subscriber procedure but that will be dependent on a subscriber category specified by command SUSCC:
SUSCC:SNB=...,SCL=PCAC-n;
The value “n” specifies whether the subscriber can change the CAC by means of a subscriber procedure or not. If set to 1, only the operator can change it by command. If set to 2, the subscriber can change the CAC by means of a procedure (for example *SC*ICAC#).
Some signalling systems, such as ISUP4, can transfer information about the CAC through the network. This means that the B-number is sent unchanged through the network and so-called “transit network selection” is included in the IAM message (IAM stands for initial address message and is the first message sent by the signalling system when establishing a call).
If an older signalling system is used, the equal access prefix (EAPREFIX) and the carrier access code (CAC) are added in front of the original B-number. This means that the information changes the B-number and that the receiving exchange has to analyse this information.
13.4 Carrier Access Code not DialledIf a subscriber as a pre-set CAC, he/she will only dial the ordinary national or international number. The network will route the call to the operator specified by command SUEAC. Figure 13.3 shows how this is handled by the system and how the different analysis tables interwork.

Equal Access Analysis
121
Figure 13.3Handling of carrier access code
Points 1-7 in the figure are explained below:
1. After pre-analysis, the B-number is sent for B-number analysis. In the B-number analysis table, the parameter CAC=ICAC or CAC=NCAC is set. This means that the subscribed carrier access code should be fetched.
2. The block CAC handles the carrier access codes and stores the subscribed carriers for the subscribers in the own exchange.
3. A new B-number analysis is performed but the parameter F=OR states that the analysis should start again with a new pre-analysis.
4. The pre-analysis is performed again.
5. B-number analysis is performed with the added CAC. In the B-number analysis table, the parameter CAC=nnn states that a specific carrier should be used for the call.
6. The CAC value is analysed and the output from the table is usually a new origin for the B-number analysis.
7. The remaining digits in the B-number are analysed in the new origin.
When the analysis is completed, a routing case is pointed out. Depending on the route characteristics of the route, the equal access prefix and the carrier access code are sent along with the signalling system, or the information is included in the B-number. The parameter CACB in block RA determines this.
Pre-analysisof B-number
B-numberAnalysis
Equal AccessAnalysis
B-number1
2
34
5
6
7

Exchange Data
122
13.5 Carrier Access Code Dialled by the SubscriberThere are no major differences between this way of handling the carrier access code and the one described in the previous chapter. However, see Figure 13.4.
Figure 13.4Handling of equal access prefix (EAPREFIX) and carrier access code (CAC) when dialled by the subscriber
Points 1-7 in the figure are explained below:
1. After pre-analysis, the B-number is sent for B-number analysis. In the B-number analysis table, the parameter CAC=BNUM is set. This means that the carrier access code is part of the B-number. An example from Sweden could perhaps help illustrate this:
− 009 is dialled when using Telia as international carrier. The two zeros (00) represent the equal access code and the nine (9) is the carrier access code.
− 007 is dialled when using Tele2 as international carrier. The two zeros (00) represent the equal access code and the seven (7) is the carrier access code.
2. The block CAC stores the EAPREFIX and the length of the carrier access code. This information is sent back for storage.
3. A new B-number analysis is performed but the parameter F=OR states that the analysis should start again with a new pre-analysis.
4. The pre-analysis is performed again.
Pre-analysisof B-number
B-numberAnalysis
Equal AccessAnalysis
EAPREFIX1
2
34
5
6
7
CACB-number

Equal Access Analysis
123
5. B-number analysis is performed with the added CAC. In the B-number analysis table, the parameter CAC=nnn states that a specific carrier should be used for the call.
6. The CAC value is analysed and the output from the table is usually a new origin for the B-number analysis.
7. The remaining digits in the B-number are analysed in the new origin
13.6 Example of an Analysis TableThe equal access table is not very complicated. An example of a table can be seen in Figure 13.5.
Figure 13.5Example of an analysis table for equal access
13.7 CommandsThe following commands are used to handle the equal access:
• EACZI, the command zeroes the non-operating area.
• EACCI, the command copies the operating area to the non-operating area.
• EACAI, the command activates data in the non-operating area (and saves the previously operating data in the non-operating area).
• EACAR, the command resets the non-operating area if the protection period has not elapsed.
• EACSI, the command specifies data in the non-operating area.
• EACSE, the command erases data in the non-operating area.
The operational instruction “Equal Access Analysis Administration” should also be studied.
<EACSP:BO=ALL;EQUAL ACCESS ANALYSIS DATAOPERATING AREA
EAPREFIX LCAC00 1
BO CAC RESULT120 7130 9
END

Exchange Data
124
13.8 Chapter SummaryFrom this chapter you should remember these points:
• Equal access means the freedom of selecting a long distance carrier.
• The long distance carrier could be a national or international carrier.
• A national carrier is identified by a national carrier access code, NCAC
• An international carrier is identified by the international carrier access code, ICAC.
• A subscriber can either have a pre-selected carrier or select the carrier by means of a code.
• The B-number analysis and the equal access analysis interwork closely.

125
14. Service Screening Analysis
Figure 14.1Chapter Objectives
14.1 IntroductionThe number of services in a mixed POTS and ISDN network is enormous. This may also create commercial problems to operators when subscribers use other networks and their services. By means of agreements, operators can decide to bar or restrict the internetwork use of services. This means that information about a service is not transferred in the network from one operator to another. An example of such a service is “user-to-user signal-ling”. The reason could be charging problems or overload in signalling links.
14.2 The AnalysisThe input to the service screening analysis is the parameter SSC, service screening case, which is delivered from the B-number analysis. It is speci-fied as any other analysis result in the table. The total number of service screening cases is 255 and the same screening case can be used for several destinations. Figure 14.2 shows the main principle.
Figure 14.2The main principle of service screening analysis
Chapter Objectives
After completing this chapter, you will be able to:
• Understand how service screening analysis is initiated
• Understand how service screening interacts with the B-number analysis.
B-number Analysis Service Screening Analysis
Barred services
B-NUMBER ANALYSISB-NUMBER......n-nn SSC=x
SERVICE SCREENING ANALYSISSSC......SSC=x "AA" "BB" "CC"

Exchange Data
126
14.3 The Services that can be BarredThe following services can be barred or restricted in the service screening analysis:
• Call deflection during alerting
• Call deflection immediate response
• Call forwarding on busy, on no reply, and unconditional
• Calling line identification
• Closed user group with outgoing access
• Closed user group without outgoing access
• Mobile subscriber not reachable
• Redirection with reason unknown
• User-to-user services (several different types)
• Virtual private network call.
14.4 The CommandsThe following commands are used to handle the service:
• ANSRIThe command is used to specify new screening cases.
• ANSRCThe command changes already loaded data.
• ANSREThe command is used to remove screening cases.
14.5 Chapter SummaryFrom this chapter you should remember these points:
• Service screening is used when operators belonging to different networks would like to restrict the use of services.
• The analysis is initiated when the B-number analysis delivers the parameter SSC, service screening case.

127
15. ISDN-Specific Analyses
Figure 15.1Chapter Objectives
15.1 IntroductionISDN places new and more advanced demands on the network, a fact which is reflected by the analyses required in ISDN. This means that the network has to analyse more information on bearer services, protocols etc. The necessary analyses are described briefly in this chapter.
15.2 Telecommunication Service Analysis
15.2.1 IntroductionWhen an ISDN call is requested by a subscriber or by another exchange, the information about the requested service is included in the message sent by the signalling system. If the call originates from a local subscriber, the name of the message is SETUP (message in DSS1, digital subscriber signalling system no. 1). If the call originates from another exchange, the information is included in the IAM, initial address message.
By analysing the information in the messages, the AXE system can determine which “telecommunication service code” is requested by the subscriber. This analysis may also indicate that the requested service is not supported by the network. Figure 15.2 shows the general principle.
Chapter Objectives
After completing this chapter, you will be able to:
• describe the ISDN-specific analyses in the AXE system
• describe the fundamental principles of the telecommunication service analysis
• describe the fundamental principles of the service indicator analysis.

Exchange Data
128
Figure 15.2The requested service is analysed in the telecommunication service analysis
15.2.2 SurveyWhen a call is requested, a large number of parameters included in the SETUP or IAM message are sent to the telecommunication service analysis in block TECA. The combination of parameters in the message is analysed and the requested service is found and given a so-called TSC, telecommunication service code. The TSC will then be used in another table and the demands on the network regarding signalling and restrictions in breaks in the transmission and sending of tones is set. For example, a data call should not be interrupted by means of call waiting as the tones sent as a reminder may disturb the modem communication.
The first analysis table in this analysis can be seen in Figure 15.3.
Figure 15.3Example of the telecommunication service analysis
The columns have the following meanings:
• TSERV, teleservice capabilityThe requested teleservice is stated here. Examples of teleservices are telephony, fax group 1-3, fax group 4 teletex.
IAM
SETUPTelecommunicationService Analysis
TSC
Local Exchange
<ANTEP:TSC=3;
TELECOMMUNICATION SERVICE ANALYSIS DATA
TSC 3TSERV TMODE TCAP LAY1 LAY2 LAY3 URATE ATSC BTSC TSI CS DIG 2 2 3TPHY CS DIG ALAW 2 2 7TFX23 CS DIG ALAW 2 2 11END

ISDN-Specific Analyses
129
• TMODE, transfer modeThe alternatives available are either circuit (CS) or packet-switched (PS).
• TCAP, transfer capabilityThe parameter states if speech, digital or restricted digital is wanted.
• LAY1 to LAY3The parameters are used to identify the protocol identifiers on the three lowest levels of the OSI model.
• URATE, user transmission rateIf rate adaptation is wanted, the parameter specifies the rate of the user.
• ATSC, telecommunication service code for A-subscriber
• BTSC, telecommunication service code for B-subscriber
• TSI, telecommunication service identifier
When all the parameters in the setup or IAM message have been analysed, a check is made to see if the network can support the service. If it can, the result of the analysis is the TSC. The TSC is then taken to next type of analysis which will deliver some analysis results. An example of this analysis, referred to as “telecommunication service code data”, can be seen in Figure 15.4.
Figure 15.4Example of data loaded for the telecommunication service codes
The important information obtained from this table is:
• WSIG, wanted signallingShows whether the telecommunication requires ISDN signalling or not. If it does, the parameter ISRE is used (ISDN signalling required). The other parameter (ISPR) states ISDN signalling preferred.
<ANTCP:TSC=ALL;
TELECOMMUNICATION SERVICE CODE DATATSC WSIG TBP CHAN TONE TCL ES NOTE 1 ISPR NO NOSIG YES SPEECH 2 ISPR NO NOSIG YES AUDIO 3 ISPR YES NOSIG NO UNRDIG 4 ISPR YES NOSIG NO AUDIO7 5 ISPR NO NOSIG YES TLPHY 6 ISRE YES NOSIG NO TLPHY7 7 ISPR YES NOSIG NO FAX23 8 ISPR YES NOSIG NO FAX4 9 ISPR YES NOSIG NO TELETX 10 ISPR YES NOSIG NO VIDOTX 11 ISRE YES NOSIG NO VIDTL1 12 ISPR YES NOSIG NO VIDTL2
END

Exchange Data
130
• TBP, transmission break protectionIf the call is a data call, the transmission may not be broken by, for example, an operator.
• CHAN, signalling channelIf the D-channel has to be used for the service, it is stated here.
• TONE, tone informationSame as parameter TBP. No tones should be sent in data calls (for example tones for call waiting).
• NOTEThe parameter is simply a reminder about the service connected to the TSC value.
15.2.3 CommandsThe following commands are used to change the analysis tables:
• ANTCIThe command defines a telecommunication service code with associated data.
• ANTCEThe command removes a telecommunication service code. Note that the analysis data has to be removed first with command ANTEE.
• ANTEIThe command defines data for the telecommunication service analysis.
• ANTEEThe command removes the analysis data.
• ANTECThe command can change already loaded data related to the telecommunication service analysis.
15.3 Service Indicator Analysis
15.3.1 IntroductionThe service indicator analysis is used when a non-ISDN subscriber wants to use an ISDN service or when an ISDN subscriber wants to modify the bearer and teleservice information included in the SETUP message. To do this, the subscriber has to dial a code which is analysed in the B-number analysis table as any other number. The code will generate an analysis result from the B-number analysis table which is referred to as “service indicator case”, SIC. The result of the analysis could be a TSC, telecommunication service code, or information about the modem type to be used for converting the analog subscriber.
The analysis can also be performed on the terminating side of the call. This is done if the call terminates on an ISDN subscriber but it does not carry any bearer capabilities. The reason is that the call originates from a POTS subscriber. Here the analysis is based upon the new subscriber category

ISDN-Specific Analyses
131
DSIC, default service indicator code. Figure 15.5 shows the general principle.
Figure 15.5General principle of service indicator analysis
15.3.2 SurveyOnce the subscriber has dialled the code or prefix, the B-number analysis generates the service indicator case, SIC. The SIC will then be sent to the service indicator analysis in block TEDA for further analysis. An example of an analysis table can be seen in Figure 15.6.
Figure 15.6Example of service indicator analysis table
Service indicator 1 is printed in the above example. The TCAP, transfer capability, is set to “unrestricted digital”. For conversion of the call to correct format, a modem has to be used. The MTI, modem type information, is set to 3. The modem is defined with the command EXMTI.
15.3.3 CommandsThe following command are used to change data related to the function:
• ANSIIThe command is used when defining new service indicator cases in the analysis.
• ANSIEThe command is used when deleting service analysis cases from the
POTS
B-numberAnalysis
SICServiceIndicatorAnalysis
TSC
Modem type
DSIC
ISDN(B-subscriber)
<ANSIP:SIC=1;
SERVICE INDICATOR ANALYSIS DATASIC 1TCAP TSC TMODE TSERV MTI LAY1 LAY2 LAY3 BTSC TSI DIG 3
END

Exchange Data
132
table. Note that the SIC must first be removed from the B-number analysis table before it can be removed here.
• EXMTIThe command is used when defining new modem types.
• EXMTEThe command is used when removing a modem type.
15.4 Chapter SummaryFrom this chapter you should remember these points:
• The telecommunication service analysis is initiated when a call is started. The data originates from information in the SETUP or IAM messages.
• The reason for having the analysis is that the exchange must find the demands for the requested service.
• The service indicator analysis is used when ISDN and non-ISDN subscribers want to change the bearer and teleservice information included in a call. For non-ISDN subscribers, it sets initial data.

133
16. Semipermanent Connections
Figure 16.1Chapter Objectives
16.1 IntroductionSemipermanent connections are used to connect any incoming device with any outgoing device. The connections are used in the network e.g. for modem connection of computers. In the network, this is referred to as “leased lines” as the subscriber pays for a line from one point to another in the network. This chapter describes the commands required to establish a semipermanent connection through an exchange.
16.2 General about Semipermanent ConnectionsThe semipermanent line is regarded as a permanent path through the exchange and can only be disconnected by means of a command. The permanent path is reserved in each exchange required to interconnect the two points in the network. If four exchanges are required, four separate semipermanent connections must be set up. One path has to be set up through each exchange. Figure 16.2 shows an example.
Figure 16.2Example of a leased line through four different exchanges
Chapter Objectives
After completing this chapter, you will be able to:
• name the blocks responsible for semipermanent connections
• use the commands required to reserve, connect and disconnect a semipermanent connection.
Semipermanentconnections

Exchange Data
134
Why not call the other subscriber number and have a path while the data communication is active? The reason for preferring a leased line could be one of the following:
• A semipermanent connection is more permanent as it “survives” a system restart in the AXE system.
• If the transmission network is old, the PTT can select the path with the best transmission characteristics (e.g. digital transmission point-to-point). This means that the line can be used for higher data rates (more than 2400 bit/s).
• PTT can select another rate for the charging as the charging is made “manually” without using the ordinary tariff.
In AXE, a semipermanent connection can be established between almost any devices in the exchange. It is also possible to include other devices in the path. Examples are echo suppressors and inter working units (modems for ISDN-PSTN communication). Examples of semipermanent connections are:
1. LIC to BT
2. LIC to LIC (local connection)
3. BT to BT (transit).
16.2.1 The Blocks InvolvedThe complete administration of semipermanent connections is handled by four blocks. Two of the blocks handle the commands and printouts related to the function, while two connect, supervise and release the connections. Please study Figure 16.3.
Figure 16.3Blocks handling semipermanent connections
LIC
EMTS GS ETC
LI TS JT GS ET/BT
SECAS SECA
SECODA/SECOM
PrintoutsCommands

Semipermanent Connections
135
The blocks SECA and SECAS establish the connections by ordering the traffic handling blocks to reserve devices and paths. Block SECAS handles the semipermanent path through the SSS subsystem. The incoming and outgoing devices must be manually blocked, and BT devices must be removed from service. If required, other types of equipment are connected as well (e.g. echo suppressors). The blocks SECODA and SECOM are designed exclusively for the handling of commands and printouts.
16.2.2 Example of a ConnectionIn this section are we going to study the commands and printouts used when setting up a semipermanent connection. The complete procedure is described in detail in the operational instruction “Establishment of semipermanent connection”.
The complete procedure for establishing a connections is divided into three main phases:
1. The incoming and outgoing devices are blocked and removed from service.
2. The path through the exchange is reserved and other devices are connected if required.
3. The reserved path is through-connected and can be used by the user of the leased line.
The list below shows all the commands required to establish a connection between a line interface circuit (LIC) and an outgoing device (BT).
1. Block the LIC device (BLODI)
2. Block the BT device (BLODI)
3. Remove the BT device from service (EXDAE)
4. Remove the BT device from the route (EXDRE)
5. Insert the BT device into a semipermanent route (EXDRI)
6. Reactivate the BT device (EXDAI)
7. Start a procedure to specify the path (EXSPI)
8. Specify the LI device (EXSSI)
9. Specify the BT device (EXSSI)
10. Terminate the procedure
11. Activate the reserved path.
In this study case, a semipermanent connection is established between devices LI3-133 and BT6-55. All actions are taken from the operational instruction mentioned before. The first actions are to block the LIC and the BT. The BT device must also be removed from service. The devices are blocked with command BLODI, and the BT6 device is removed from service with command EXDAE. The BT6 device is then disconnected from the existing route and inserted in a special route used for semipermanent connections. That is done with EXDRE and EXDRI. After that, the BT6

Exchange Data
136
device is reactivated with command EXDAI. It is now possible to start the reservation of the path by using the command EXSPI. Figure 16.4 shows the command and a printout.
Figure 16.4The procedure has been initiated
The command EXSSP prints all procedures that are still “open”. The semipermanent connection is given a name in the command EXSPI. This name is used in many commands and alarms related to the path. The name consists of two main parts, each containing up to 15 characters. After the name, a number between 1 and 65535 can be given. The names will be used to identify the path in the network.
The next step of the procedure will be to state the two devices that were blocked earlier. This is done by stating the device names, but the parameter SNB (subscriber number) can also be used if an LIC is included. Figure 16.5 shows the commands and a printout of the loaded data.
<EXSPI:NAME=STOCKHOLM-LONDON-12EXECUTED
<EXSSP;
SEMIPERMANENT CONNECTION PROCEDURE DATA
NAME MISC
STOCKHOLM-LONDON-12
END

Semipermanent Connections
137
Figure 16.5The two devices included in the path are stated
In the printout, the name and the two devices are indicated. However, the path is not yet connected as this procedure only reserves the path. The procedure initiated with command EXSPI must be terminated before the path can be connected. Figure 16.6 shows how the procedure is terminated as well as a printout of the state of the path.
<EXSSI:SNB1=441005;EXECUTED
<EXSSI:DEV2=BT6-55;EXECUTED
<EXSSP;
SEMIPERMANENT CONNECTION PROCEDURE DATA
NAME
STOCKHOLM-LONDON-12
SIDE 1
SNB=441005
SIDE2
DEV=BT6-55
END

Exchange Data
138
Figure 16.6Termination of procedure and printout of data
The state of the path, which is found under the heading “CSTATE”, is “reserved” (RES). In this state, the path can wait until an order is received to connect the path. Figure 16.2 shows an example of a path using four different exchanges. This procedure is required in all four exchanges and the PTT might postpone the through-connection until all exchanges have been prepared (this work is rather complicated in an analog exchange).
When the reserved path is to be through-connected, the command EXSCI is used. Figure 16.7 shows an example of the command and the resulting printout.
<EXSPE; EXSPE<; EXECUTED
<EXSCP:NAME=STOCKHOLM-LONDON-12;
SEMIPERMANENT CONNECTION DATA
NAME CSTATE DISTC MISCSTOCKHOLM-LONDON-12 RES 0
SIDE1 SSTATE BCH DIPS SIGDEV=LI3-133 RESSNB=441005
SIDE2 SSTATE BCH DIPS SIGDEV=BT6-55 RES
END

Semipermanent Connections
139
Figure 16.7The path is though connected
The result of the connection attempt can be seen under the heading “RESULT”. The path is now through-connected and can be used by the user of the leased line. In a new printout, the only difference (as compared with Figure 16.6) will be that ACT (activated) is entered in the CSTATE column.
A more interesting example is perhaps a call path tracing printout initiated by the command CTRAI. Figure 16.8 shows such a printout.
Figure 16.8Call path tracing of a semipermanent connection
Devices in the blocks SECA, SECAS and SECOM have been reserved for the path. These software records supervise the path and will be busy until the path is disconnected. The path can be disconnected with the command EXSCE.
<EXSCI:NAME=STOCKHOLM-LONDON-12; EXSCI:NAME=STOCKHOLM-LONDON-12;<; ORDERED
WO TRX-B AT-3 TIME 960327 1349 PAGE 1
SEMIPERMANENT CONNECTION ACTIVATION RESULT
NAME RESULTSTOCKHOLM-LONDON-12 SUCCESSFUL
END
<CTRAI:DEV=BT6-55;CALL PATH TRACINGSWDEV DEV MUP LINK MUP LI3-133SECAS-8 JT-52 GS-0-276 GS-000001-16SECA-4 BT6-55 GS-1-23SEDEBRANCH-01SECA-4SECOM-4END

Exchange Data
140
16.3 Command SurveyHere follows a short survey of all the commands used to handle semipermanent connections:
• EXSPI, Initiates a procedure for reserving a semipermanent connection.
• EXSPE, Ends a procedure.
• EXSSI, Defines one side at a time of a semipermanent connection (can only be used inside a procedure).
• EXSSE, Removes data in the procedure (can only be used inside the procedure).
• EXSSP, Prints loaded data in a procedure (can only be given inside the procedure).
• EXSCI, Activates a reserved path.
• EXSCE, Disconnects a semipermanent connection.
• EXSCP, Printout of one or more semipermanent connections.
16.4 Chapter SummaryFrom this chapter you should remember these points:
• Semipermanent connections survive system restarts.
• Devices must be manually blocked and removed from service before they can be used in a connection.
• The command EXSPI initiates a procedure for the reservation of a path.
• The command EXSCI connects a reserved path.

141
Aaccess barring 105access barring analysis 42, 107accounting 77accounting analysis 42accounting case 87analysis, of end of selection 99A-number analysis 43, 113A-number series, blocking of 118application information 23area code 60area code, in B-number analysis 94
BB-category analysis 42block
C7BTC 15C7DR2 15C7OTH 15C7ST2 15CATA 68CHAB 68CHAP 68CHCHARG 66, 68CHCOOR 68CHDATA 66, 68CHMON 10, 68CHOFTT 66CHSUB 66, 68CJ 7CLCOF 10CSR 13DA 8, 11ET 13GS 10JT 10KR 8LI 7RA 12, 46, 98RE 7SC 7, 59SECA 135SECAS 135SECODA 135SECOM 135SUA 7TS 8, 10
blocking supervision 33B-number analysis 40, 44B-number type 84branching, in end of selection analysis 100, 102branching, in route analysis 47
Ccalendar 79call meter reading 78carrier access code 120cause code 98, 101charging analysis 41charging case 87charging case branching analysis 71charging check 78charging origin 71charging program analysis 72charging statistics 79command
ANAAI 114ANAAR 114ANACI 114ANALI 114

Exchange Data
142
ANASE 114ANASI 114ANASP 114ANAZI 114ANBAI 93ANBAR 93ANBCI 93ANBLI 93ANBSE 93ANBSI 93ANBSP 86, 93ANBZI 93ANDSE 109ANDSI 109ANDSP 109ANEAI 103ANEAR 103ANEPE 103ANEPI 103ANESE 103ANESI 103ANESP 100, 103ANRAI 56ANRAR 56ANRPE 51, 56ANRPI 51, 56ANRSE 56ANRSI 51, 56ANRSP 47, 51ANRZI 56ANSIE 131ANSII 131ANSIP 131ANSPE 57ANSPI 57ANSRC 126ANSRE 126ANSRI 126ANSSI 57ANTCE 130ANTCI 130ANTCP 129ANTEC 130ANTEE 130ANTEI 130ANTSE 110ANTSI 110ANTSP 110BLEME 29BLODE 33BLODI 135BLORE 32BLORP 32BLRPE 27CACAP 80CACAR 80CACLC 79CACLP 79CHCAI 74CHCPE 74CHCPI 74CHCSI 74CHCZI 74CHEAI 73CHEPE 73CHEPI 73CHESI 73CHEZI 73CHHSI 79CHIAI 70

143
CHIPE 70CHIPI 70CHISI 70CHIZI 70CHLSI 79CHSAI 75CHSIP 78CHSOP 78CHSPE 75CHSPI 75CHSSI 75CHSZI 75CHTSE 76CHTSI 76CHTSP 76CIBAI 72CIBPE 72CIBPI 72CIBSI 72CIBZI 71CIPAI 72CIPSE 72CIPSI 72CIPSP 72CIPZI 72EACAI 123EACAR 123EACCI 123EACSE 123EACSI 123EACSP 123EACZI 123EXACP 62EXDAE 135EXDAI 33, 135EXDEP 33EXDRE 135EXDRI 33, 135EXDRP 34EXEME 29EXEMI 29EXEMP 29EXIAI 61EXMTE 132EXMTI 131, 132EXNSI 59, 61, 89EXNSP 62EXRBC 30, 31, 32, 109EXROI 30EXRPE 27EXRPI 26EXRPP 27EXRUI 26, 27EXSCE 140EXSCI 140EXSCP 140EXSPE 140EXSPI 135, 137, 140EXSSE 140EXSSI 135, 140EXSSP 136, 140LAEUL 26LAEUP 27PNASI 111PNASP 112PNBSP 84SAADI 22SAAEP 22SAAII 22STRDP 35

Exchange Data
144
STRSP 34SUEAC 120SULIE 60SULII 59, 89SUSCC 107, 109, 120
congestion signal 101
Ddata file 21data record 21data transcript 18day categories 80delayed seizure attempt 101destination code 105
Eemergency area 54end of selection codes 98end of selection signal 101end-of-selection analysis 42equal access analysis 43, 119equal access prefix 120exchange alarm state 54exchange requirement 18extended charging analysis 73extension modules, definition of 28
Fforced release 101function block
structure 6function change 18function code 31
Gglobal size alteration event 22
Hhigh cost/long duration 79hundred group 59hundred groups, change of 62
Iimmediate service 78implied area code 61internal route 30
Llanguage or discriminating digit 54local size alteration event 22
Mmodification of B-number 32modification of B-number, in end of selection 100modified Karlsson principle 66
Nnew seizure attempt 101number length 87numbering plan indicator 84
Oorigin for route analysis 32origin of B-number analysis 83
Pparameter
A, accounting case 87ACO, charging origin from A-no. analysis 113ACO, origin for charging from A-no. analysis 71AL, alarm state, in EOS 102AL, exchange alarm state 54

145
ANT, A-number type 112AO, accounting origin 113AREA 61, 94AREAL 94ATSC, telecommunication service code for A-subscriber 129B, B-number origin and B-number 93BE, branching in EOS 100BNT, B-number type 84BO, origin of B-number analysis 83BR, branching 47BTSC, telecommunication service code for B-subscriber 129CAC, carrier access code 120CACB 121CAU, cause code 101CCH, compatibility check 47CD, charging determining point 73CHAN, signalling channel 130CHM, charging method 73CHT, B-subscriber charging type 73CL, traffic class 102CL, type of class 71CO, charging origin 71COS, congestion signal 101CP, charged party 73D, destination code 106DCAT, day categories 80DCAT, day category 75DEV, device 60DSIC, default service indicator code 131DSR, delayed seizure attempt 101DT, dialling tone 90DTS, decreased time supervision 110EA, emergency area 54EO, origin for EOS analysis 102ES, end-of-selection code 84, 100ES, end-of-selection code, from A-no. analysis 114ESS, end-of-selection signal 101F, in EOS analysis 101F, restart B-number analsysis from first digit 86FRE, forced release 101HU, hundred group 61ICAC, international carrier access code 120ISPR, ISDN signalling preferred 129ISRE, ISDN signalling required 129L, length (hundred groups) 61L, number length in B-number analysis 87L, number length, in A-no. analysis 114LAY1, layer 1 129LCAC, length of CAC 123LOD, language or discriminating digit 54M, modification of B-number 100M, modification, in EOS analysis 101N, restart B-number analysis from next digit 86NA, number of previous connection attempts 102NAPI, numbering plan indicator 84, 111, 114NCAC, national carrier access code 120NCT, network conversion type 73NE, number end 91NSP, number of start pulses 76NTS, normal time supervision 110OBA, origin for B-number analysis 84PR, priority 53PR, priority, in EOS 102RA, random switch 53RC, routing case 47, 87RO, routing origin, in A-no. analysis 113RSSP, result of subscriber procedure 70SAT, satellite connection 54SCL, subscriber class 107SIC, service indicator case 131

Exchange Data
146
SNB, subscriber number 60SNBCH, susbscriber number change 62SP, sending program 48SR, new seizure 101SSC, service screening case 125SSI, subscriber service indicator 70SSP, subscriber service procedure 70SW, routing switch 54SWC, switching class 75T, tariff 76TBP, transmission break protection 130TC, tariff class 74TCAP, transfer capability 129TDCL, trunk discriminating class 107TDS, time duration in seconds 76TDSF 79TE, terminating call 87TI, time supervision case 110TMODE, transfer mode 129TMR, transmission medium requirement 54TN, table test number 91TN=AP, test of A-number pre-analysis 96TN=B, test of B-number analysis 95TN=BP, test of B-number pre-analysis 95TN=E, test of end-of-selection analysis 96TN=EA, test of equal access analysis 95TN=R, test of route analysis 95TONE 102TONE, tone information 130TRD, traffic destination code 91TSC, telecommunication service code 128TSERV, teleservice capability 128TSI, telecommunication service identifier 129URATE, user transmission rate 129VPN, virtual private network 71WSIG, wanted signalling 129WSIG, wanted type of signalling 54
post dialling delay 49POTS service 39pre-analysis of A-number 111pre-analysis of B-number 83pre-analysis of B-number information 40, 44pre-post service 33pre-selected carrier 120priority, branching on 53priority, for routes 32pulse metering 65
Rrandom switch, branching on 53records 6regional processor, definition of 25register signalling route 31route analysis 41route group 32route name 31route origin, branching on 50route, connect devices to 33route, definition of 30routing case 47, 87routing programs 48routing switch 54RP pair 25
SSAE number 22satellite connection 54semipermanent connections 133sending program 12, 48service indicator analysis 42, 130

147
service indicator case 130service screening analysis 43, 125size alteration 18
of hardware 19of software 19
size alteration event 22software route 30STP, signalling transfer point 14switching class analysis 74
Ttable test number 91tariff class analysis 74tariffs 76TCL category, branching on 52telecommunication service analysis 40, 44, 127telecommunication service code 127test numbers 96the Karlsson principle 66time supervision 109time supervision analysis 42toll ticketing 66traffic activity analysis 69traffic destination code 91transit network selection 120transmission characteristics 32transmission medium required 54
Vvariables 6
Wwanted type of signalling 54

Exchange Data
148


EN/LZT 101 1615 R1B© Ericsson Telecom AB
Ericsson Telecom ABMV/ETX/PN/CDXS-126 25 Stockholm, SwedenTelephone: +46 8 719 9222
Subj
ect t
o al
tera
tions
with
out p
rior
not
ice.
Pri
nted
in S
wed
en.