AUTOMATED FIREWALL RULE SET GENERATION THROUGH PASSIVE TRAFFIC INSPECTION
description
Transcript of AUTOMATED FIREWALL RULE SET GENERATION THROUGH PASSIVE TRAFFIC INSPECTION

Georg-Christian Pranschke Supervisor: Barry Irwin
Security and Networks Research Group
Department of Computer Science
Rhodes University
AUTOMATED FIREWALL RULE SET GENERATION
THROUGH PASSIVE TRAFFIC INSPECTION

AU
TO
MA
TED
FIREW
ALL R
ULE
SET
GEN
ER
ATIO
NBackground
Wireshark Tcpdump / Windump
ACM Classification System (1998) C.2.0. Security and Protection
• Introducing firewalls into existing networks is often problematic
• Production traffic cannot be interrupted
• Necessitates time consuming manual analysis of network traffic
• Ever increasing traffic volumes make manual analysis less feasible

AU
TO
MA
TED
FIREW
ALL R
ULE
SET
GEN
ER
ATIO
NTraffic Analyser – Flow Creation

AU
TO
MA
TED
FIREW
ALL R
ULE
SET
GEN
ER
ATIO
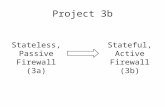
NHigh Level Design Overview – System Components

Pipeline: bpf -> sql -> scripts -> fwbuilder


Charybdis screencast
Scylla screencast

AU
TO
MA
TED
FIREW
ALL R
ULE
SET
GEN
ER
ATIO
NResults / Critical Evaluation
• Misconfigured firewall provides only the illusion of network security
• Imperfect information -> no proof of correctness
• “Dancing bears”
• HTTP universal firewall traversal protocol -> SQLi


AU
TO
MA
TED
FIREW
ALL R
ULE
SET
GEN
ER
ATIO
NQuestions ?