Assembly 02. Outline mov Command Registers Memory EFLAGS Arithmetic 1.
-
Upload
marcus-wood -
Category
Documents
-
view
216 -
download
0
Transcript of Assembly 02. Outline mov Command Registers Memory EFLAGS Arithmetic 1.

Assembly 02

2
Outline
• mov Command• Registers• Memory• EFLAGS• Arithmetic

3
mov Command
• “Moves” data from:• register to register• memory to register• register to memory
• CANNOT move data from memory to memory• (must use register as intermediate step)
• mov command actually copies data, does not move it

4
mov Command
• Takes two operands: destination and source
mov eax,42
“move (copy) 42 into 32-bit register eax”
destination
source

5
mov Command
• Source and destination must be same size• 8-bit byte• 16-bit word• 32-bit double-word

6
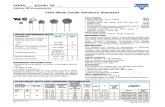
mov Command
mnemonic
destination
source notes
mov eax 0x42 source is immediate data
mov ebx edi both are 32-bit registers
mov bx cx both are 16-bit registers
mov dl bh both are 8-bit registers
mov [ebp] edidestination is 32-bit memory data stored at edp
mov edx [esi]source is 32-bit memory data at the address stored in esi

7
Immediate Data
• CPU does not have to “go anywhere” to get data• Data comes from instruction itself• Only source can be immediate data
mov eax,42
immediate data

8
mov Command
• Source can be ASCII character(s)• Must enclose ASCII character(s) with single quotes
mov ebx,’ABCD’

9
mov Command
mov ebx,’ABCD’
After instruction, contents of 32-bit register ebx:
ebx = 0x44434241
‘D’‘C’
’B’
’A’

10
mov Command
mov ebx,’ABCD’
• x86 architecture is little-endian• LSB stored at lowest address
4344 4142ebx
‘C’‘D’ ‘A’‘B’

11
Outline
• mov Command• Registers• Memory• EFLAGS• Arithmetic

12
Registers
• x86 has four 32-bit general purpose registers
eax
ebx
ecx
edx

13
Registers
• x86 has four 16-bit general purpose registers
ax
bx
cx
dx

14
Registers
• x86 has eight 8-bit general purpose registers
ah al
bh bl
ch cl
dh dl

15
Registers
ah al
eax
ax

16
Registers
mov eax, 0x11111111mov ax, 0x2222
mov ah, 0x33mov al, 0x44
What’s in eax after the instructions execute?Let’s find out..

17
Registers
mov eax, 0x11111111mov ax, 0x2222mov ah, 0x33mov al, 0x44
eax

18
Registers
mov eax, 0x11111111mov ax, 0x2222mov ah, 0x33mov al, 0x44
eax 1111 11 11

19
Registers
mov eax, 0x11111111mov ax, 0x2222mov ah, 0x33mov al, 0x44
eax 1111 22 22

20
Registers
mov eax, 0x11111111mov ax, 0x2222mov ah, 0x33mov al, 0x44
eax 1111 33 22

21
Registers
mov eax, 0x11111111mov ax, 0x2222mov ah, 0x33mov al, 0x44
eax 1111 33 44

22
Registers
mov eax, 0x11111111mov ax, 0x2222mov ah, 0x33mov al, 0x44
eax 0x11113344

23
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
What’s in eax, ebx, and ecx after these instructions execute?Let’s find out…

24
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
eax
ebx
ecx

25
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
eax 67 FE
ebx
ecx

26
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
eax 67 FE
ebx 67 FE
ecx

27
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
eax 67 FE
ebx 67 FE
ecx 67

28
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
eax 67 FE
ebx 67 FE
ecx FE 67

29
Registers
mov ax, 0x67FEmov bx, axmov cl, bhmov ch, bl
eax
ebx
ecx
0x67FE
0x67FE
0xFE67

30
Registers
• How to swap contents of eax and ebx?• Could use three mov instructions• Requires a third register
mov ecx, eaxmov eax, ebxmov ebx, ecx

31
Registers
• Or, use the xchg mnemonic
xchg eax, ebx

32
Outline
• mov Command• Registers• Memory• EFLAGS• Arithmetic

33
Memory
• Data stored in memory at 32-bit address• Segment of addressable memory “owned” by program• Operating System controls memory access• Why??
• Use square brackets to get data stored at memory address• Information inside the brackets: “effective address”
mov eax, [ ebx ]

34
Memory
mov ax, 4mov bx, [1]
address
data
0 0xFFFF
1 0xBEEF
2 0x0ACE
3 0xFEED
4 0xACDC
ax
bx

35
Memory
mov ax, 4mov bx, [1]
address
data
0 0xFFFF
1 0xBEEF
2 0x0ACE
3 0xFEED
4 0xACDC
4ax
bx

36
Memory
mov ax, 4mov bx, [1]
address
data
0 0xFFFF
1 0xBEEF
2 0x0ACE
3 0xFEED
4 0xACDC
4ax
0xBEEFbx

37
Memory
• In assembly, variable means address not data
var: db 0xAB…mov eax varmov ebx [var]
eax
ebx

38
Memory
• In assembly, variable means address not data
var: db 0xAB…mov eax varmov ebx [var]
eax
ebx
this variable declaration instruction must be declared in .data section of assembly code (more on this later)

39
Memory
• In assembly, variable means address not data
var: db 0xAB…mov eax varmov ebx [var]
0x0804909eax
ebx
32-bit memory address for var (may change depending on OS)

40
Memory
• In assembly, variable means address not data• Must use [square brackets] to access data
var: db 0xAB…mov eax varmov ebx [var]
0x0804909eax
0xABebx
value stored at address var

41
Memory
• Declaring a variable• Variable declaration goes in “section .data”
section .datax: db 0x01y: dw 0x2345z: dd 0x6789ABCD

42
Memory
• Declaring a variable• Variable declaration goes in “section .data”
x: db 0x01
variable name followed by :
variable typedb for byte
initial value

43
Memory
• Declaring a variable• Variable declaration goes in “section .data”
y: dw 0x2345
variable name followed by :
variable typedw for word (16-bits)
initial value

44
Memory
• Declaring a variable• Variable declaration goes in “section .data”
z: dd 0x6789ABCD
variable name followed by :
variable typedd for double word (32-bits)
initial value

45
Memory
• nasm does not “remember” variable size• You must specify either byte, word, or dword• (when entering an immediate value)
section .datax: db 0x01
…mov [x], byte 0x45mov al, [x] ; examine variable x

46
Memory
• nasm does not “remember” variable size• You must specify either byte, word, or dword• When accessing registers, register size tells assembler what to do
section .datay: dw 0x2345
…mov [y], word 0x6789mov bx, [y] ; examine variable y

47
Memory
• nasm does not “remember” variable size• You must specify either byte, word, or dword
section .dataz: dd 0x6789ABCD
…mov [z], dword 0xACEBEEF0mov ecx, [z] ; examine variable z

48
Outline
• mov Command• Registers• Memory• EFLAGS• Arithmetic

49
EFLAGS Register
• 32-bits wide• Each bit represents a flag• Bit position determines function• Check flags for various CPU states
• When flag is set, it equals 1• When flag is cleared, it equals 0

50
EFLAGS Register
• Analogous to red flags on row of rural mailboxes

51
EFLAGS Register
• Each flag has 2-3 letter symbol (for programmer use)• Some important flags:
OF: overflow flag (bit 11)• set when value too large to fit in operand
ZF: zero flag (bit 6)• set when operand set to zero
CF: carry flag (bit 0)• set when arithmetic or shift “carries” out a bit

52

53
EFLAGS Register
• How and when flags are set or cleared depends on instruction!
• Some instructions modify flags, others do not
• Check Appendix A for information!

54
Outline
• mov Command• Registers• Memory• EFLAGS• Arithmetic

55
Arithmetic
• add mnemonic• Addition• Straightforward
• mul mnemonic• Multiplication• Nuanced (implicit operand)

56
Arithmetic (add)
add dst,src
dst = dst + srcdst += src
destination register gets overwritten with destination + source

57
Arithmetic (add)
mov eax,2mov ebx,3add eax, ebx
eax
ebx

58
Arithmetic (add)
mov eax,2mov ebx,3add eax, ebx
2eax
ebx

59
Arithmetic (add)
mov eax,2mov ebx,3add eax, ebx
2eax
3ebx

60
Arithmetic (add)
mov eax,2mov ebx,3add eax, ebx
5eax
3ebx

61
Arithmetic (mul)
• mul mnemonic for multiplication• Multiplication slightly more complicated• Why? Because products can be VERY LARGE!!
• Multiplication uses an implicit operand• Assumption made by instruction• Does not / cannot be changed

62
Arithmetic (mul)
mul ebx
• Destination operand is implicit• Not explicitly defined in instruction, but assumed to be present
• Destination operand always ‘A’ register (eax, ax, al)
eax *= ebx

63
Arithmetic (mul)
mov eax, 2mov ebx, 4mul ebx
eax
ebx

64
Arithmetic (mul)
mov eax, 2mov ebx, 4mul ebx
2eax
ebx

65
Arithmetic (mul)
mov eax, 2mov ebx, 4mul ebx
2eax
4ebx

66
Arithmetic (mul)
mov eax, 2mov ebx, 4mul ebx
8eax
4ebx
remember, eax is implicit operand

67
Arithmetic (mul)
• When you multiply two large 32-bit numbers, you’ll need 64-bits to store the product
e.g., 231 * 231= 262
You can’t store 262 in 32 bits…

68
Arithmetic (mul)
• To get around this, x86 use the ‘D’ register• ‘D’ register holds the high-order bits
• After multiplication, check the CF (carry flag) to see if ‘D’ register is used…• If CF is set, D register holds high-order bits

69
Arithmetic (mul)
mov eax, 0xFFFFFFFFmov ebx, 0x3B72mul ebx
eax
ebx
edx
0CF

70
Arithmetic (mul)
mov eax, 0xFFFFFFFFmov ebx, 0x3B72mul ebx
0xFFFFFFFFeax
ebx
edx
0CF

71
Arithmetic (mul)
mov eax, 0xFFFFFFFFmov ebx, 0x3B72mul ebx
0xFFFFFFFFeax
0x3B72ebx
edx
0CF

72
Arithmetic (mul)
mov eax, 0xFFFFFFFFmov ebx, 0x3B72mul ebx
0xFFFFC48Eeax
0x3B72ebx
0x3B71edx
1CF

73
Arithmetic (mul)
mov eax, 0xFFFFFFFFmov ebx, 0x3B72mul ebx
0xFFFFC48Eeax
0x3B72ebx
0x3B71edx
1CF
carry flag (CF) bit of EFLAGS register is set
final product is 0x3B71FFFFC48E
edx eax

74
Arithmetic
• Division works the same way (implicit operand)• See Appendix A for more