Acl Tcam
-
Upload
amitmonty -
Category
Technology
-
view
2.505 -
download
1
Transcript of Acl Tcam

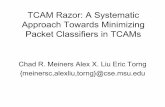
An Introduction To MindTree
Spring, 2004
Design Considerations for ACL TCAM
resource management
algorithms
A. Sivaramakrishnan
April 2005

Page 2
AgendaAgenda
Ternary CAM – an Overview ACL Flow Key Typical TCAM Management Framework TCAM Resource Managing Algorithm Data Plane Operation

Page 3
Ternary CAM – an OverviewTernary CAM – an Overview
Specialized piece of memory for rapid lookups Ternary – because 0, 1 & X (Don’t care) X
- acts as wildcard during the search - attractive for implementing longest prefix match Consists of Mask, Value, Result Mask – The pattern to be matched Eg. IP Addr, L4 Ports, etc Value – Mask bit associated with the pattern Result – Action that occurs when a lookup returns a hit for the pattern & mask Eg. Permit, Deny, etc

Page 4
Mask Value ArrangementMask Value Arrangement
1 – Many
1 - 1
Mask 1
Mask 2
Mask 1
Mask 2
Mask 3
Mask 4
Mask 5
Mask6
Value 2
Value 3
Value 4
Value 7
Value 6
Value 1Value 1
Value 2
Value 3
Value 4
Value 5
Value 6
Value 7
Value 8
Value 1
Value 2
Value 3
Value 4
Value 5
Value 6
Value 7
Value 8

Page 5
Programming Values & MasksProgramming Values & Masks
10.76.34.68
255.255.255.255
176.24.34.0
255.255.255.0
176.24.34.85
255.255.255.255
176.24.34.0
255.255.255.64
Mask 2
Mask 3
Mask 1
Mask 1
Entries pertaining to a particular mask should be grouped as much as possible, in case of one-many mask-entry arrangement mechanism

Page 6
Where we are?Where we are?
Ternary CAM – an Overview ACL Flow Key Typical TCAM Management Framework TCAM Resource Managing Algorithm Data Plane Operation

Page 7
Flow KeyFlow Key
What Constitutes a TCAM Entry?ACL Policies , QOS Policies, Route Table Entries
ACL/QOS Policies L4 Source, Destination Port Information L2/L3 Source, Destination Addresses
Permit / Deny a particular port Permit / Deny a range of ports Permit / Deny a set of ports except a particular port Permit / Deny a set of ports greater/less than particular port
Action to take (Result) Permit / Deny Permit / Deny + log the packet info Permit / Deny via software Redirect Bridge
Ingress/Egress Direction Route Table Entries
Source Destination IP Address, Protocol, Next Hop, Metric, Interface

Page 8
Flow Key FieldsFlow Key Fields
Source IP Address Destination IP Address Lookup Type Packet Type MPLS Packet L4 Protocol More Fragment Bit Fragment Details L4 Operation L4 Source Port L4 Destination Port TOS IGMP Message Type ICMP Code ICMP Type ESP Security ID IPv6 TAG Recirculation Bit Interface Details

Page 9
Where we are ? Where we are ?
Ternary CAM – an Overview ACL Flow Key Typical TCAM Management Framework TCAM Resource Managing Algorithm Data Plane Operation

Page 10
TCAM Resource Management FrameworkTCAM Resource Management Framework
Resource
Management Algorithm
Driver
TCAM Hardware

Page 11
Where we are?Where we are?
Ternary CAM – an Overview ACL Flow Key Typical TCAM Resource Management Framework (TRMF) TCAM Resource Managing Algorithm
Sequence of Events during hardware programming Design Focus Reducing number of entries Error Recovery Optimized CPU Utilization
Data Plane Operation

Page 12
When program the ACL TCAM?When program the ACL TCAM?
Apply ACL to an interface Remove ACL from interface Modify ACL applied to an interface Bring up/down interfaces with ACL Add/del interfaces with ACL Reuse ACL on different interfaces Concept
Order Dependent / Order Independent ACLs

Page 13
TCAM Resource Management Algorithm TCAM Resource Management Algorithm - Sequence of Events - Sequence of Events
Once the ACLs are (de)configured, the following sequence of events would takes place The ACL parameters to be passed to TRMF using message
based interface Callback functions can be used, if required TRMF wait on infinite queue Receive message Manipulate the info received from the message (use
guidelines in the next slide for message processing) step by step
Program the software tables for each of above steps Program the software table delta in the hardware In case a response needs to be sent back, send
success/failure of the message

Page 14
TCAM Resource Managing AlgorithmTCAM Resource Managing Algorithm - Design Focus - Design Focus
Use minimal number of entries in the TCAM Efficient algorithms to manage CPU utilization,
huge number of TCAM Entries Optimal programs to search, add, remove,
modify entries Error recovery, in case of exceptions Easy to use, user interface for the users to
identify relation between various entities Take care of entries being disturbed from
multiple points

Page 15
Reducing Number of TCAM EntriesReducing Number of TCAM Entries
Logical Operations with TCP/UDP Port Numbers
Merging ACLs Mask space freeing

Page 16
Logical operations for TCP/UDPLogical operations for TCP/UDP
L4 Operations Greater Than , Less Than Range Not equal To, equal to
All logical operations except ‘equal to’ might take more than 1 TCAM entry space Port Numbers : 0 – 65535 Assume an Entry
permit Source:IP 10.34.25.0/24, TCP Port Greater than 36 Dest :IP 20.34.25.0/24, TCP Port Range 60000 64000
Port greater than 36=> 65536-36 = 65500 entries required Range 60000 to 64000 = 4000 entries required Concerns
Uses more TCAM space Takes more lookup time

Page 17
Optimizing Logical operations for TCP/UDPOptimizing Logical operations for TCP/UDP
For optimizing ACL Flow Keys maintain the logical
operations for TCP/UDP in separate set of port registers Use those registers for all logical operations except ‘equal to’ Use just 1 ACL TCAM entry & refer to those port registers in
the flow key
ACL Flowkey optimized for TCP/UDP logical operations
Refer Port Registers
Reg 0
Reg 1
Reg 2
Reg 3
Reg 4
Reg 5
Reg 6
Reg 7
Reg 8
Reg 9
Reg 10
Reg 11
Reg 12
Reg 13
Reg 14
Reg 15
Greater than 34Range 60000 64000

Page 18
Merging ACLsMerging ACLs
Scenario 1 Entry1
Permit, source: ip 10.20.34.0/24 dest: ip 20.20.34.0/24 Entry2
Permit, source: ip 10.20.34.5/32 dest: ip 20.20.34.0/24 Entry2 subset of Entry11. Use single entry instead of 2
Scenario 2 Entry1, 2, 3 respectively are:
deny, source: ip 10.20.34.0/24 dest: ip 20.20.34.0/24 Permit, source: ip 10.20.34.5/32 dest: ip 20.30.34.0/24 Permit, source: ip 10.20.34.10/32 dest: ip 20.40.34.0/24
Entry 1 superset of entries 2 & 3. The packet is denied at Entry1, packet never hits entries 2 & 3 So, use only 1 entry space

Page 19
Mask Space freeingMask Space freeing
Prevents lookup of 2 mask spaces
Saves TCAM space for 2nd mask
Mask 1
E1, E2, E3, E4
E5, E6, E7, E8
Mask 2
E9, E10, E11
Mask 1
E20, E21
Mask 1
E1, E2, E3, E4
E5, E20, E21, E8
Mask 2
E9, E10, E11
Delete Entry E6 & E7

Page 20
Error RecoveryError Recovery
Usually number of entries, sequence, etc unpredictable while programming
So, contingency management framework necessary Example:
Say 10 entries to be programmed, only 8 free spaces in software
Non availability of space would be known only during programming 9th entry
Now, TRMF should return failure The 8 entries needs to be removed now

Page 21
Hardware programmingHardware programming- Optimization techniques- Optimization techniques
Algorithms update software tables Entries in software to be updated in the hardware Programming all the entries is tedious Transfer only the delta in software table to the hardware Identifying delta
Use separate data structures Example: bitlists can track delta Divide the software table into 2 parts. Program the delta
separately, once programmed transfer delta to permanent area

Page 22
Where we are ?Where we are ?
Ternary CAM – an Overview ACL Flow Key Typical TCAM Management Framework TCAM Resource Managing Algorithm Data Plane Operation

Page 23
Data Path OperationData Path Operation
B
Use reg info
to form the flowkey
get the interface infoGet the rest of info
from the packet
A
B C
form a flow key
lookup reg for
layer4 info
lookup TCAM
Use result
Use default result
start
identify the packet
get packet header
parse the fields
A
C
Get layer 4 info
start

Page 24
RecapRecap
Ternary CAM – an Overview ACL Flow Key Typical TCAM Management Framework TCAM Resource Managing Algorithm Data Plane Operation

Page 25
Imagination Action
Joy