A Systematic Approach - Cisco...Social Security Medical Record Bank Account Info > $1000 Global...
Transcript of A Systematic Approach - Cisco...Social Security Medical Record Bank Account Info > $1000 Global...
Cyber SecurityA Systematic Approach
Cristian Matei - Solutions Architect
Who are we?
A Team of Certified Specialists:
• Cisco Connect Technology Partner
• Cisco Enterprise Partner of the Year 2015
• Architectural Excellence in SP Architectures
2014
What are we doing?
Why are we here?
Who are we?
Only what we do best:
• Systems Integration
• Turnkey Technology Projects
• Innovation Through In-House Development
• Custom Solutions
Why are we here?
What are we doing?
Who are we?
What are we doing?
Why are we here?
To get connected:
• 12:00-12:30 IoT Turnkey Systems, Gabriel
Musat - Technical & Marketing Director
• 14:15-14:45 Automate Datacenter Service
Delivery, Mihai Gagea - Presales Consultant
• Booth Demo: Security, DataCenter and
Unified Communications
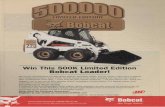
$300K
$1
$150
Exploits$1000-
Facebook Account
Malware Development
Spam
$0.25-$60
>$50
~$7
$1
Credit Card Data
DDOSas a Service
Social Security
Medical
Record
Bank
Account Info
>$1000
Global Cybercrime
Market:$450B-$1T
Mobile Malware
$50/ 500K
$2500
Cyber Crime Market
BEFOREDetect
Block
Defend
DURING AFTERControl
Enforce
Harden
Scope
Contain
Remediate
Attack Continuum
Network Endpoint Mobile Virtual Cloud
Point in Time Continuous
Networking Attack Phases
BEFOREDetect
Block
Defend
DURINGControl
Enforce
Harden
Guard Network Entries
Web Security
Email Security
Next Generation Firewall
Endpoints
Which vendor provides better security?
Covers the attack continuum
Protects against unknown malware
Secures the system, not individual components
Actual Disposition = Bad =Blocked
Antivirus
Sandboxing
Initial Disposition = Clean
RetrospectiveDetection,Analysis Continues
Initial Disposition = Clean
Continuous
Blind to scope of compromise
Sleep Techniques
Unknown Protocols
Encryption
Polymorphism
Turns back time
Visibility and Control are Key
AnalysisStops
Point-in-timeDetection
Cisco AMP Analyzes Beyond the Event Horizon
TrajectoryBehavioralIndications
of Compromise
BreachHunting
Attack Chain Weaving
Retrospective Security Is Built On
File trajectory automatically records propagation of the file across the network
Collective Security Intelligence Cloud
Computer
Virtual Machine
Mobile
Mobile
Virtual Machine Computer
Network
Collective Security Intelligence Cloud
Mobile
Mobile
File TrajectoryUnknown file is downloadedto device1
Fingerprint is recorded and sent to cloud for analysis2
The unknown file travels across the network to different devices
3
Sandbox analytics determines the file is malicious and notifies all devices
4
If file is deemed malicious, file trajectory can provide insight into which hosts are infected, and it provides greater visibility into the extent of an infection
5
TrajectoryBehavioralIndications
of Compromise
BreachHunting
Retrospective Security Is Built On
Computer
Unknown file is downloaded to a particular device
1
The file executes2
Device trajectory records this, the parent processes lineage and all actions performedby the file
3
File is convicted as malicious and the user is alerted to the root cause and extent of the compromise
4
Drive #1 Drive #2 Drive #3
Device Trajectory
If Something Gets in, Retrospective Security Helps You Find Answers to the Most Pressing Security Questions
What happened?
Where did the malware come from?
Where has the malware been?
What is it doing?
How do we stop it?
See AMP in Action!
What happened?
Understand the anatomy of the attack:
• Where is the threat now
• Which users are compromised
• What type of malware is it
Where did the malware come from?
Where has the malware been?
What is it doing?
How do we stop it?
See AMP in Action!
Understand How It All Happened
What happened?
Track threat’s origin and progression:
• How did it get into the system
• What is the point of origin
• What was the attack vector
Where has the malware been?
What is it doing?
How do we stop it?
Where did the malware come from?
See AMP in Action!
See Where It Entered the System
What happened?
Where did the malware come from?
Where has the malware been?
What is it doing?
How do we stop it?
Track infected areas in the system:
• Where is the attack now
• What other endpoints have seen it
• Where should I focus my response
See AMP in Action!
See Everywhere That It Has Been
What happened?
Where did the malware come from?
Where has the malware been?
What is it doing?
How do we stop it?
Understand how malware works:
• What is it trying to do, in plain English
• How does the malware behave
• Get detailed information vital for
incident response
See AMP in Action!
Determine What the Malware is Doing
Knowing the details above,
surgically remediate:
• Stop it at the source and all infected areas
• Simply right click and take action to stop the
attack
See AMP in Action!
What happened?
Where did the malware come from?
Where has the malware been?
What is it doing?
How do we stop it?
Stop It with a Few Clicks
Network ResourcesAccess Policy
Traditional Cisco TrustSec®
BYOD Access
Threat Containment
Guest Access
Role-BasedAccess
Identity Profilingand Posture
Who
Compliant
What
When
Where
How
A context-aware next-generation secure network access solution that reduces risks and contains threats by dynamically controlling network access
NetworkDoor
Context
ISE pxGridController
Cisco Identity Services Engine
Your Network Is Your Sensor
Use network data to extend
visibility to the access layer
Internal Network
Identity
Routers and Switches
Firewall
Context
Enrich flow of data with identity, events, proxy,
and application to create context Accelerated detection,
investigation and response.
WHO WHAT WHERE WHEN HOW
Proxy Server
Devices
Cisco Lancope for Visibility, Context, and Control
Rapid Threat Containment via pxGrid
When
Where
Who
How
What
Cisco and Partner Ecosystem
ISE
Cisco Network
pxGridController
Context
32
1
45
Cisco® ISE collects contextual data from network1
Context is shared viapxGrid technology2
Cisco AMP, Lancope and Partners use context to improve visibility
to detect threats3
Cisco AMP, Lancope and Partners can direct Cisco ISE to rapidly
contain threats4
Cisco ISE uses partner data to update context andrefine access policy
5
See RTC in Action!