5 Cybersecurity threats in Public Sector
-
Upload
seqrite -
Category
Government & Nonprofit
-
view
106 -
download
0
Transcript of 5 Cybersecurity threats in Public Sector

5 CYBERSECURITY
THREATS IN PUBLIC SECTOR
1

Introduction
2
Public Sector is amongst the favorite of hackers. As the public sector hoards valuable and sensitive information of citizens, it makes them an attractive target for cyber criminals.
Data breaches in Public Sector results in exposing massive amounts of data which is usually confidential in nature.

Major Threats Faced by Public Sector
3
Data loss
Insider and
Privilege Misuse
Cyber Espionage
PhishingRansomware
Web Application
AttacksDenial of Service
Malware
Attacks
Malicious InsidersPayment Card
Skimmers
Point of Sale
Intrusion
Crimeware
Lost and stolen asset
Social Error
Trojan
Human
Error
Spyware
Virus

IT Risks in Public Sector
41%Personal data
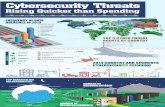
As per SecurityScorecard Research Report 2017:
Public Sector received one of the lowest security scores, when compared to 17 other major industries.
4
33%of organizations in Public Sector had compliance issues in 2016.
Data compromised in Public Sector
88%of IT operations teams are at least partially responsible for data breaches or security incidents in Public Sector.
Source: Netwrix, Cisco Annual Cybersecurity Report 2017
75%of organizations in Public Sector do not have any separate information security function.
“
41% Secrets
14% Credentials
9% Medical data

What Statistics have to say?
• 72% Public Sector entities worldwide had their security compromised in 2016.
• Only 14% of Public Sector organizations consider themselves to be well-protected against cyber threats.
• 100% of IT specialists working for Public Sector agencies worldwide, says employees are the biggest threat to security.
• 21.10% of overall data records were stolen or lost in Public Sector in the year 2016.
• Public sector entities were the third most prevalent industry to be breached (12%) in 2016.
• Public sector organizations worldwide experienced 269 data breach incidents in the year 2016.
• 43% of Public Sector IT professionals said they investigated security incidents that involved insider misuse.
• 6% of overall external vulnerabilities were found in Public Sector in 2016.
Source: Netwrix 2017, BLI 5

TOP 5 CYBERSECURITYTHREATS IN PUBLIC SECTOR
6

RANSOMWARE
Source: Verizon DBIR 2017, Bitsight Insights
Ransomware is a malware that works by encrypting information and then demanding ransom to decrypt it. Public Sector is one major target of ransomware attacks becasue of the large volumes of citizen's sensitive information.
99% of malware
sent via email or
webserver.
7
21,239Total number of security
incidents in Public Sector
in 2016.
“96% of Public
Sector data has
been
compromised
during multiple
ransomware
attacks in 2016.
5.9% of Public
Sector entities were
hit by ransomware
attacks in 2016,
which makes Public
Sector exhibites the
second highest hit
rate of ransomware
attacks after
Education industry.

INSIDER THREAT
100% of
Public Sector entities see their own employees as the biggest threat to security.
Source: Verizon DBIR 2017
Insider Threat: A malicious threat to the organization that comes from people within the organization.
Breaches in Public Sector often involves employees accessing sensitive information either maliciously or unintentionally, in a way that could affect the entities.
Insider threat can be categorized as:
• Human Error• Privilege Misuse• Data Theft
8
57% & 14%
Security Incidents
Data Breaches
“Privilege misuse as insider threats in
Public Sector entities caused:
7417Security
Incidents58Breaches
are caused by human errors as insider threats in Public Sector entities.

DISTRIBUTED DENIALOF SERVICE (DDoS) 617
security incidents were caused by DDoS in Public Sector.
Source: Verizon DBIR 2017
DDoS attacks are intended to compromise the availability of networks and systems by overwhelming the traffic, resulting in perfomance degradation or interruption of services.
Public sector experienced a huge number of DDoS attacks.
9
“In August 2016, the Australian Census website received four DDoS attacks by overseas hackers. Millions of Australians were unable to fill out the mandatory Census online. The hackers exposed names and addresses of the users, which were retained by the organization later.

CYBER ESPIONAGE
Source: Verizon DBIR 2017
Cyber Espionage, an incident pattern which includes unauthorized network or system access linked to state-affiliated actors and/or exhibiting the motive of espionage.
Among all other tactics of cyber attacks, Phishing is the most consistent tactic used by cyber criminals during cyber-espionage.
10
41% of data
breaches in Public Sector were related to cyber espionage.
“According to Verizon DBIR 2017:
Cyber Espionage is among the greatest threat to Public Sector entities.
112 security
incidents and breaches were caused by cyber-espionage in Public Sector in the year 2016.
More than 90%of data breaches were attributed to state-affiliated groups.

PHISHINGAs per the Verizon DBIR 2017:
9.23% people clicked on
phishing mails in Public Sector.
Source: Verizon DBIR 2017
Malicious payloads are commonly delivered via:
Phishing is a process of contacting a person through email, message or call where the receiver is tricked to leak sensitive data such as personally identifiable information.
100% of phishing emails comprise of ransomware or malicious software.
91% of
cyber attacks
start with a
phishing
email.
11
“
73%Email
13%Drive-by-download
Average click rate of phishing emails in Public Sector is
10.66%.

Helps mitigate all such security threats in the public sector with its range of
Dynamic, Scalable, and Future Ready solutions:
SEQRITE Endpoint Security
SEQRITE Unified Threat Management Solution (TERMINATOR)
SEQRITE Mobile Device Management
SEQRITE Data Loss Prevention
12

Endpoint Security FEATURES
PATCH MANAGEMENT
Enables IT administrators to check and
install missing security patches for all
applications installed on enterprise endpoints
from a centrally managed console.
WEB SECURITY
Automatically blocks websites infected with
malware or designed for phishing attacks.
APPLICATION CONTROL
Categories of applications can be authorized or
unauthorized from being executed within the
network.
DATA BACKUP AND RESTORE TOOL
Automatically and periodically (multiple times
a day), takes a backup of all important and
well-known file formats like PDF and Microsoft
Office files that are present on a computer.
RISKS MITIGATED
RANSOMWARE ATTACKS
INSIDER THREATS
CORE PROTECTION (IDS/IPS & FIREWALL)
IDS/IPS blocks threats that exploit software
vulnerabilities and Firewall thwarts malicious
attempts to access the corporate network.
BEHAVIOR DETECTION
Detects and blocks unknown viruses and
malware in real-time.
INFECTED WEBSITES
PHISHING ATTACKSINFECTED EXTERNAL DEVICES
SECURITY VULNERABILITIES
13

Data Loss Prevention
ADVANCED DEVICE CONTROL
- Configure access policies for more than 25 device
types.
- Blocks unverified devices.
- Prevents autorun infections.
ENHANCED PRIVACY PROTECTION & COMPLIANCE
- Identifies Office documents based on their origin.
- Prevents data leakage propagated by worms, Trojans,
and other malware threats.
- Issues regular notifications to reinforce user behavior
on data security.
LOWER COMPLEXITY & COST OF DEPLOYMENT
- Easy integration with existing Seqrite EPS.
- Defines DLP security polices and reports across multiple
endpoints in scattered locations.
- Centralized management and monitoring of crucial business
data.
CONTENT AWARE PROTECTION
- Monitors all actions on confidential files.
- Instantly notifies admins about unauthorized data leakage.
- Ensures that no confidential data leaves the organization.
- TARGETED ATTACKS
- HUMAN ERROR
- USB DRIVES
- WEB EMAIL
DATA LEAKAGE caused by:
RISKS MITIGATED
FEATURES
14
- BLUETOOTH
- CLOUD STORAGE

TERMINATOR
GATEWAY ANTIVIRUS
Scans all incoming and outgoing network traffic
at the gateway level. Augments existing virus
solutions by reducing the window of
vulnerability (WoV).
FIREWALL
Admins can permit or block access for traffic
between internal and external networks
based on enterprise compliance policies.
VIRTUAL PRIVATE NETWORK
Provides IT administrators with a means for
secure communications between the
company's remote users and for building site-to-
site connections.
IDS / IPS
Scrutinizes network traffic in real-time and
prevents a broad range of DoS and DDoS
attacks before they penetrate the network.
DoS & DDoS ATTACKS
INTERNET DOWNTIME
GATEWAY MAIL PROTECTION
Scans incoming/outgoing emails or attachments
at the gateway level to block spam and phishing
emails before they enter the network.
CONTENT FILTERING
Allows blocking of non-business related websites
including streaming media sites, downloads,
instant messaging, etc., in order to reduce
unnecessary load on enterprise bandwidth.
MALICIOUS INTERNET TRAFFIC
MALICIOUS EMAILSMAN-in-the-MIDDLE ATTACKS
ADVANCED PERSISTENT THREATS
FEATURES
RISKS MITIGATED
15

MDM
APPLICATION CONTROL
Apps can be remotely managed/ installed/
blocked in order to maintain policy compliance
and productivity within the network.
VIRTUAL FENCING
Preset virtual boundaries that restrict device
usage and functionality. These boundaries can
be triggered by geolocation-based, time-based
or Wi-Fi network-based data.
UNIFIED MANAGEMENT CONSOLE
Manage and synchronize all connected devices
through a centralized graphical interface.
NETWORK DATA MONITORING
Admins can view details of Internet data used
over mobile networks or Wi-Fi. They can also
monitor all incoming and outgoing calls and
SMSs on enterprise mobile devices.
DATA THEFT FROM LOST/
STOLEN MOBILE PHONES
ANTI-THEFT
Prevents misuse of lost/stolen mobile phones by
remotely tracking and locking them. Also prevents
data breach by remotely erasing the phone’s data.
INTERNET THREATS
JAILBREAKING/ ROOTING
OF MOBILE DEVICES
MALICIOUS MOBILE APPS
SECURITY MANAGEMENT
Features such as browsing protection, web
filtering, anti-theft, and geolocation tracking
ensure the safety of enterprise devices.
MOBILE MALWARE
BAD SECURITY HYGIENE
FEATURES
RISKS MITIGATED
16

17
THANK YOU
All Intellectual Property Right(s) including trademark(s), logo(s) and copyright(s) are properties of their respective owners. Copyright ©2017 Quick Heal Technologies Ltd. All rights reserved.