4, Ch2- Switch Security
-
Upload
daniel-lisowsky -
Category
Documents
-
view
223 -
download
0
Transcript of 4, Ch2- Switch Security

Ali Nezhad
Routing and Switching
CNET 311
Centennial CollegeCentennial College
Basic Switch Concepts and ConfigurationSwitch Security
Week #4Ch2. Wayne Lewis

2Ali Nezhad
Routing and SwitchingCNET 311
Outline
� Password Protection
� Securing Remote Access
� Security Risks
� Security Tools
� Configuring Port Security

3Ali Nezhad
Routing and SwitchingCNET 311
Password Protection

4Ali Nezhad
Routing and SwitchingCNET 311
Configuring Password Options
� Protection from unauthorized access
� Passwords for
� Console line
� vty lines
� Privileged EXEC mode
� Encrypt passwords
� Recover Passwords

5Ali Nezhad
Routing and SwitchingCNET 311
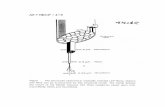
Securing Console Access
� Need direct local physical access
� Removing password protection� (config-line)#no password and no login

6Ali Nezhad
Routing and SwitchingCNET 311
Securing Virtual Terminal Access
� vty allows remote access.
� Does not need local access.
� Important to be secured
� All vty lines must be protected.
� 2960 has 15 terminal lines.

7Ali Nezhad
Routing and SwitchingCNET 311
Securing Virtual Terminal Access
� Removing password: similar to console line

8Ali Nezhad
Routing and SwitchingCNET 311
Securing Privileged EXEC Access
� This mode allows to view/config all options.
� You can also see unencrypted passwords.
� Important to be secured.
� Commands:
� enable password
� Stores password in startup-config and running-config as cleartext.
� enable secret
� Stores the password in an encrypted format.
� If configured, replaces the enable password.
� Cannot be the same as the enable password.

9Ali Nezhad
Routing and SwitchingCNET 311
Encrypting Switch Passwords
� service password-encryption command
� Encrypts already set passwords that are stored as
cleartext.
� Uses the very weak type7 encryption standard.
� Type5 is more secure but must be invoked manually for
each password.
� Disable with the keyword no:
� Only stops encrypting new passwords.
� Previously encrypted passwords remain encrypted.

10Ali Nezhad
Routing and SwitchingCNET 311
Password Recovery
� Different for different devices.
� Requires physical access.
� May not be able to recover passwords:
� Specially if encrypted.
� Can reset them to a new value.
� Will practice in the lab.

11Ali Nezhad
Routing and SwitchingCNET 311
Login Banners and MOTD
� Messages that people can see at login.
� Login Banner
� (config)# banner login “Authorized …”
� Appears before login prompts.
� MOTD Banner
� Appears before the login banner.
� (config)# banner motd “Device Maintenance!”
� Remove both with no.

12Ali Nezhad
Routing and SwitchingCNET 311
Secure Remote Access

13Ali Nezhad
Routing and SwitchingCNET 311
Telnet and SSH
� SSH is secure and newer than
telnet.
� SSH encrypts messages.

14Ali Nezhad
Routing and SwitchingCNET 311
Configuring Telnet
� Default on all Cisco switches
� If the transport protocol has been switched
to only support SSH, telnet can be restored:
� (config-line)# transport input telnet
or
� (config-line)# transport input all

15Ali Nezhad
Routing and SwitchingCNET 311
SSH Characteristics
� Switch supports SSHv1 or SSHv2 for server.
� Switch supports only SSHv1 for client.
� Supports DES & 3DES encryption algorithms.
� Supports password-based authentication.
� Uses public key cryptography based on RSA.

16Ali Nezhad
Routing and SwitchingCNET 311
Configuring SSH
1. Configure a host domain for the switch.
(config)# ip domain-name mydomain.com
2. Generate an encrypted RSA key pair
(config)# crypto key generate rsa
� A modulus size of 1024 is recommended.
� Enables SSH server for local and remote access.
� To delete the keys, use crypto key zeroize rsa
� After deletion, SSH server is automatically disabled.

17Ali Nezhad
Routing and SwitchingCNET 311
Configuring SSH- Fine Tuning
Next steps only fine tune the SSH configuration.
1. Choose the ssh version (optional)
(config)# ip ssh version [1|2]
2. Configure SSH control parameters
A. Timeout value in seconds
� Default is 120 sec
� Range is 0-120 sec
� Applies to SSH phases such as connection, protocol
negotiation, parameter negotiation

18Ali Nezhad
Routing and SwitchingCNET 311
Configuring SSH- Fine Tuning
B. Number of times a client can re-
authenticate.
� Default is 3 and the range is 0-5.
� For example, a user may allow the SSH session
idle more than 10min, 3 times before it terminates.
(config)# ip ssh {timeout seconds|authentication-retries number}

19Ali Nezhad
Routing and SwitchingCNET 311
Configuring SSH- Fine Tuning
3. To prevent non-SSH connections
(config-line)# transport input ssh
Telnet sessions will be refused.

20Ali Nezhad
Routing and SwitchingCNET 311
SSH Configuration Example

21Ali Nezhad
Routing and SwitchingCNET 311
Security RisksCommon L2 Security Attacks

22Ali Nezhad
Routing and SwitchingCNET 311
MAC Address Flooding Attack
� Makes the MAC address table overflow.
� Floods the switch with fake SRC addresses.
� Switch enters fail-open mode.
� Acts like a hub.
� Attacker receives all packets.
� Prevention: Port Security

23Ali Nezhad
Routing and SwitchingCNET 311
MAC Address Flooding Attack

24Ali Nezhad
Routing and SwitchingCNET 311
DHCP Spoofing Attack
� Attacker acts as a legitimate DHCP server.
� If on the same segment as a DHCP client, its
responses to DHCP requests reach the client sooner
than those from a valid server.
� The client uses the rogue device as its default
gateway and DNS server.
� Prevention: Port security and DHCP snooping

25Ali Nezhad
Routing and SwitchingCNET 311
DHCP Snooping Technique

26Ali Nezhad
Routing and SwitchingCNET 311
DHCP Snooping Technique
� Determines which ports can respond to DHCP requests.
� Ports are identified as trusted or untrusted.
� Trusted Ports
� Can send all kinds of DHCP messages.
� Can host a DHCP server or be connected to one.
� Untrusted Ports
� Can only send DHCP requests.

27Ali Nezhad
Routing and SwitchingCNET 311
DHCP Snooping Technique
� A port is deemed untrusted if not
explicitly configured as trusted.
� If a DHCP response message is
detected from an untrusted port,
that port is disabled.

28Ali Nezhad
Routing and SwitchingCNET 311
Configuring DHCP Snooping
1. Enable Snooping.
(config)# ip dhcp snooping
2. Enable DHCP snooping for a VLAN.
(config)# ip dhcp snooping vlan number <no.>
3. Define a port as trusted.
(config-if)# ip dhcp snooping trust
4. Do Rate Limiting. (Optional)- see next slide.

29Ali Nezhad
Routing and SwitchingCNET 311
DHCP Starvation Attack
� Attacker bombards the DHCP server with
many DHCP requests with fake SRC
addresses.
� It depletes the available leases. (DoS)
� Prevention: Rate Limiting
� For the DHCP requests from untrusted ports
(config)# ip dhcp snooping limit rate <rate>

30Ali Nezhad
Routing and SwitchingCNET 311
CDP Attack
� Cisco Discovery Protocol is targeted.
� CDP is a Cisco proprietary L2 protocol.
� It discovers other directly connected Cisco devices. Simplifies network configuration.
� CDP messages are not encrypted.
� They are broadcasted periodically.
� These messages contain info. such as SW version, IP_add, platform, capabilities, …

31Ali Nezhad
Routing and SwitchingCNET 311
CDP Attack
� This info. can be used by an
attacker for attacks such as DoS.
� Prevention
� Disable CDP on devices that do not
use it.

32Ali Nezhad
Routing and SwitchingCNET 311
Telnet Attacks� Password Attacks
� vty password is not enough.� They can be disabled using brute force.
� Prevention:� strong frequently changed passwords.
� Still the attacker may use MAC address flooding and a packet capture software to obtain the passwords.
� ACLs on vty lines.
� SSH instead of Telnet!
� DoS Attacks
� Exploiting flaws in the telnet SW to render it unavailable.

33Ali Nezhad
Routing and SwitchingCNET 311
Security Tools

34Ali Nezhad
Routing and SwitchingCNET 311
Network Security Tools
� Help verify security configurations.
� Test the network for weaknesses.
� Mimic attacks.
� Also test for application level
vulnerabilities.
� Email clients, browsers, missing patches, …

35Ali Nezhad
Routing and SwitchingCNET 311
Network Security Tools
Basic Functions
� Security Audit
� Reveals what kind of information an attacker
can gather by traffic monitoring.
� Ex: MAC address flooding is used to audit
switches on what kind of info they broadcast.
� Penetration Tests
� Identify weaknesses within the configuration of
networking devices.

36Ali Nezhad
Routing and SwitchingCNET 311
Network Security Tools
Common Features
� Service Identification� Identify services running on a host.
� Identify services running on non-standard transport layer ports e.g FTP on 210 (not 21)
� Support of SSL Services� Testing services that use SSL-level security such as
HTTPS, SMTPS, …
� Destructive Testing� Pressure testing. Done occasionally.
� Non-destructive Testing� Done routinely. Little impact on network performance.
� Up-to-date Database of Vulnerabilities

37Ali Nezhad
Routing and SwitchingCNET 311
Port Security

38Ali Nezhad
Routing and SwitchingCNET 311
Configuring Port Security
� Limit the number of valid MAC addresses allowed
on a port.
� A secure port forwards only the frames with a
source MAC-address from among its assigned
secure MAC addresses.
� The limit can be one.
� If the port is assigned to a particular MAC address, only
that host can use the port.
� Any attempt by another host results in a violation.

39Ali Nezhad
Routing and SwitchingCNET 311
Implementing Port Security
� Do it for all interfaces.
� Specify a group of valid MAC addresses on
each port. (secure MAC addresses table)
� Allow only one MAC address to access the
port at a time.
� Specify that the port automatically shut
down if a violation is detected.

40Ali Nezhad
Routing and SwitchingCNET 311
Secure MAC Address Types
� Static: stored in the address table and added to
the running config.(config-if)# switchport port-security mac-address <mac>
� Dynamic: learned dynamically and added to
the address table.
� Removed if switch restarts.
� Sticky: learned dynamically, added to the
address table and saved to the running config.

41Ali Nezhad
Routing and SwitchingCNET 311
Sticky Secure MAC AddressesCharacteristics� (config-if)# switchport port-security mac-address sticky
� Enables sticky learning on an interface.
� The port converts all dynamic secure MAC addresses, including those learned before, to sticky and adds all of them to the running config.
� If disabled, the sticky addresses remain in the running config but are removed from the table.
� Addresses that were removed can be dynamically learned again and added to the address table dynamically.

42Ali Nezhad
Routing and SwitchingCNET 311
Sticky Secure MAC Addresses
� (config-if)# switchport port-security mac-address sticky <mac>
� Configures a sticky secure MAC address.
� Addresses are added to the address table and the
running config.
� If port security is disabled, the sticky MAC
addresses remain in the running config.

43Ali Nezhad
Routing and SwitchingCNET 311
Sticky Secure MAC Addresses
� If the sticky addresses are saved to the
config file, when the switch restarts or the
port is shut down, the port does not need to
relearn these addresses.
� If not saved, they are lost.
� If sticky learning is disabled, sticky addresses
are converted to dynamic addresses and
removed from the running config.

44Ali Nezhad
Routing and SwitchingCNET 311
Sticky Secure MAC Addresses
� If you disable sticky learning and then issue:
(config-if)# switchport port-security mac-address sticky <mac>
� An error message appears.
� The sticky MAC address is not added to the
running config.

45Ali Nezhad
Routing and SwitchingCNET 311
Security Violations
� The max. number of secure MAC addresses
have been added to the address table and:
� A station whose address is not in the address
table attempts to access the interface.
� An address learned or configured on one
secure interface is seen on another secure
interface in the same VLAN.

46Ali Nezhad
Routing and SwitchingCNET 311
Violation Modes
� The action that a port is configured to
perform if a violation occurs.
� 3 Modes
� Protect
� Restrict
� Shutdown

47Ali Nezhad
Routing and SwitchingCNET 311
Violation ModesProtect
� When the number of secure addresses reaches
the limit allowed on the port:
� Packets with unknown SRC addresses are
dropped until a sufficient number of secure
MACs are removed or the limit is increased.
� No violation notification is generated.

48Ali Nezhad
Routing and SwitchingCNET 311
Violation ModesRestrict
� When the number of secure addresses
reaches the limit allowed on the port:
� Packets with unknown SRC addresses are
dropped until a sufficient number of secure
MACs are removed or the limit is increased.
� A violation notification is generated.
� An SNMP trap is sent, a syslog message is
logged and the violation counter is incremented.

49Ali Nezhad
Routing and SwitchingCNET 311
Violation ModesShutdown
� Default mode on Cisco switches.
� A violation causes the port to immediately
shut down.
� The port becomes err-disabled.
� LED turns off.
� Notification and logging similar to Restrict.
� To resolve: shutdown and no shutdown.

50Ali Nezhad
Routing and SwitchingCNET 311
Violation Modes

51Ali Nezhad
Routing and SwitchingCNET 311
Default Port Security ConfigCatalyst Switches

52Ali Nezhad
Routing and SwitchingCNET 311
Configuring Port Security
Note: Violation mode is not specified here. Defaults to shutdown.

53Ali Nezhad
Routing and SwitchingCNET 311
Enabling Sticky Port Security
Note: Violation mode is not specified here. Defaults to shutdown.

54Ali Nezhad
Routing and SwitchingCNET 311
Verifying Port Security� Check all interfaces.
� Check that any static MAC addresses are set correctly.

55Ali Nezhad
Routing and SwitchingCNET 311
Verify Secure MAC Addresses
� Display all secure addresses on all ports or a
specific one.

56Ali Nezhad
Routing and SwitchingCNET 311
Securing Unused Ports
� Disable them!
� (config-if)# shutdown
� Can use the range option:
(config)# int range fa0/3 – 24
(config-if-range)# shutdown
� Make them members of the black hole vlan.

57Ali Nezhad
Routing and SwitchingCNET 311
Questions?