Innovate.cadinc.com/wp-content/uploads/ITHotTopicsBooklet_2015-_v...3:00 - 3:45 Afternoon Break 4:00...
Transcript of Innovate.cadinc.com/wp-content/uploads/ITHotTopicsBooklet_2015-_v...3:00 - 3:45 Afternoon Break 4:00...
Welcome!
TAB
LE
OF
CON
TEN
TS
About the Event Host .....................................................................................................................................................................................................................................5Agenda .............................................................................................................................................................................................................................................................................................................................................................................9Keynote.............................................................................................................................................................................................................................................................................................................................................................12Wednesday Sessions.................................................................................................................................................................................................................................13Cyber Security Student Track.................................................................................................................................................18Keynote Fireside Chat ......................................................................................................................................................................................................................19Thursday Sessions .........................................................................................................................................................................................................................................................20Prizes ......................................................................................................................................................................................................................................................................................................................................................................................24Golf Tournament ......................................................................................................................................................................................................................................................................25Meet the Team ...........................................................................................................................................................................................................................................................................................26Sponsors ...................................................................................................................................................................................................................................................................................................................................................29
Welcome!
13th Annual IT Hot Topics Conference 13h Annual IT Hot Topics Conference
54
WELCOME ABOUT THE HOST
13th Annual IT Hot Topics Conference
On behalf of the entire Carolina Advanced Digital family, welcome to our 13th annual IT Hot Topics Conference. This year also marks the 30th Anniversary of our company. It started, officially, in 1985 when the company consisted of me, an old typewriter table, a brown pushbutton desk phone and a box of business cards that proclaimed me as a Computer Systems Consultant. Within four or five years I was able to coax my wife Susan away from her employer to join me in our small enterprise; to date that is still the best business decision I ever made. We incorporated as Carolina Advanced Digital, Inc. in February 1989, and grew slowly but steadily over the years. Our business model has changed many times over the last 30 years which is something that we always anticipated would be a part of our evolution. This year our model is changing again to include a stronger focus on security. Other changes include an intensified integration of customer feedback in to our processes and continuous improvement initiatives. Our efforts in customer service satisfaction have been noticed and rewarded greatly over time. In April of this year we were awarded a NASA SEWP V prime contract, a testament to our team’s abilities and solid past performance. These considerations will of course affect the nature of our operations but our fundamental values have never changed: We demand practical efficacy from any of our designs, products and projects. Our first loyalty is to our customer’s mission. That is the primary consideration in our movement toward Strategic IT Design. We invite you to participate in our efforts to move Information Technology in that direction. First work with us to
define the mission in detail, knowing that, we can then select the technologies that best support the design required to accomplish the missions. Welcome to the conference, and to our 30th anniversary celebration!
— John Jabbusch
President & Chief Engineer Carolina Advanced Digital, Inc.
WEL
COM
E ABO
UT U
S
The IT Hot Topics Conference is hosted by technology integrator Carolina Advanced Digital, Inc. Carolina Advanced Digital is a nationally-recognized leader in technology infrastructure and security solutions. Family owned and operated since 1984, the company has been providing exceptional engineering services and products to government, education, healthcare and commercial clients across the United States, including Fortune 100 and 500 companies, DoD and civilian agencies. Headquartered in Cary, NC, Carolina Advanced Digital has offices and resources in North Carolina, Florida and Texas.
OUR SERVICES
Wired Networks
Wireless Security
SOLUTION DELIVERYFor special projects and planning, infrastructure design, certified security consulting or just to supplement their IT staff, customers enlist our expertise to ensure projects are properly planned and completed while meeting budgets and deadlines.
SIGNATURE SERVICES• Network discovery• Wireless evaluation• Full network surveys with
documentation
• Network configuration reviews• Customized security solutions• Enterprise wireless projects
StrategicConsulting
TurnkeySolutions
+Everythingin between
13th Annual IT Hot Topics Conference 13h Annual IT Hot Topics Conference
76
OUR PARTNERS
• Wireless intrusion prevention• Spectrum management• Troubleshooting and analysis• Security and policy enforcement• Compliance reporting
• Network access control• Network visibility• Guest management• BYOD security and onboarding• 802.1X management
• Switching and routing• Wireless• Software Defined Networking (SDN)• Servers and storage• Network management
ABO
UT
US A
BOU
T US
• Packeting shaping• Proxies• Web filters• SSL inspection• WAN optimization
OUR PARTNERS
• Wireless security• Zero-touch deployment• Cloud services• Network management and software• Wireless arays and access points
• Next-gen firewalls• Email security and archiving• Web filters• Backup appliances and cloud• Link and load balancers
• 802.11ac solutions• Multi-vendor management• Instant controller-less access points• Scalable controller solutions• Spectrum analysis and WIPS
• Switching and routing• Network security• Enterprise wireless• Meraki wireless• Firewalls and UTMs
• Chromebooks• Management services• Applications• Google for Education• Google business solutions
• Wireless, SCA and MCA• 802.11ac solutions• Guest and BYOD management• Wireless security• Spectrum management
• Next-gen firewalls• Remote access and SSL-VPN• Network access control• Switching and routing• Virtual environment security
• SonicWALL Security• Next-gen firewalls and UTMs• Remote access• Security reporting• Severs, storage
• Next-gen firewalls• Email security and archiving• Web filters• Backup appliances and cloud• Link and load balancers
• Wireless intrustion prevention• Spectrum management• Troubleshooting and analysis• Security and policy enforcement• Compliance reporting
• Switching and routing• Servers and Storage• Network management• PCs, laptops and tablets• Wireless
• SonicWALL Security• Next-gen firewalls and UTMs• Remote access• Security reporting• Severs, storage
• Network access control• Network visibility• Guest management• BYOD security and onboarding• 802.1X management
• Network management• Device configuration• Traffic, flow, QoS monitoring• Network mapping• Log and event management
• Wireless, SCA and MCA• 802.11ac solutions• Guest and BYOD management• Wireless security• Spectrum management
• Next-gen firewalls• Remote access and SSL-VPN• Network access control• Switching and routing• Virtual environment security
• Strategic consulting• Turnkey projects• Pre-audit security review• Assessments and documentation• Wired, wireless, security
• Encryption• Key management• Windows and Mac• Pre-boot authentication• Port and media control
OUR PARTNERS
133 Triangle Trade Drive, Cary, NC 27513919-460-1313 www.cadinc.com
@cadincCADincorporated
• Packeting shaping• Proxies• Web filters• SSL inspection• WAN optimization
• Wireless security• Zero-touch deployment• Cloud services• Network management and software• Wireless arays and access points
• Switching and routing• Network security• Enterprise wireless• Meraki wireless• Firewalls and UTMs
• 802.11ac solutions• Multi-vendor management• Instant controller-less access points• Scalable controller solutions• Spectrum analysis and WIPS
• Chromebooks• Management services• Applications• Google for Education• Google business solutions
• Encryption• Key management• Windows and Mac• Pre-boot authentication• Port and media control
• Next-gen firewalls• Email security and archiving• Web filters• Backup appliances and cloud• Link and load balancers
• Wireless intrustion prevention• Spectrum management• Troubleshooting and analysis• Security and policy enforcement• Compliance reporting
• Switching and routing• Servers and Storage• Network management• PCs, laptops and tablets• Wireless
• SonicWALL Security• Next-gen firewalls and UTMs• Remote access• Security reporting• Severs, storage
• Network access control• Network visibility• Guest management• BYOD security and onboarding• 802.1X management
• Network management• Device configuration• Traffic, flow, QoS monitoring• Network mapping• Log and event management
• Wireless, SCA and MCA• 802.11ac solutions• Guest and BYOD management• Wireless security• Spectrum management
• Next-gen firewalls• Remote access and SSL-VPN• Network access control• Switching and routing• Virtual environment security
• Strategic consulting• Turnkey projects• Pre-audit security review• Assessments and documentation• Wired, wireless, security
• Encryption• Key management• Windows and Mac• Pre-boot authentication• Port and media control
OUR PARTNERS
133 Triangle Trade Drive, Cary, NC 27513919-460-1313 www.cadinc.com
@cadincCADincorporated
• Packeting shaping• Proxies• Web filters• SSL inspection• WAN optimization
• Wireless security• Zero-touch deployment• Cloud services• Network management and software• Wireless arays and access points
• Switching and routing• Network security• Enterprise wireless• Meraki wireless• Firewalls and UTMs
• 802.11ac solutions• Multi-vendor management• Instant controller-less access points• Scalable controller solutions• Spectrum analysis and WIPS
• Chromebooks• Management services• Applications• Google for Education• Google business solutions
• Network management• Device configuration• Traffic, flow, QoS monitoring• Network mapping• Log and event management
• Next-gen firewalls• Email security and archiving• Web filters• Backup appliances and cloud• Link and load balancers
• Wireless intrustion prevention• Spectrum management• Troubleshooting and analysis• Security and policy enforcement• Compliance reporting
• Switching and routing• Servers and Storage• Network management• PCs, laptops and tablets• Wireless
• SonicWALL Security• Next-gen firewalls and UTMs• Remote access• Security reporting• Severs, storage
• Network access control• Network visibility• Guest management• BYOD security and onboarding• 802.1X management
• Network management• Device configuration• Traffic, flow, QoS monitoring• Network mapping• Log and event management
• Wireless, SCA and MCA• 802.11ac solutions• Guest and BYOD management• Wireless security• Spectrum management
• Next-gen firewalls• Remote access and SSL-VPN• Network access control• Switching and routing• Virtual environment security
• Strategic consulting• Turnkey projects• Pre-audit security review• Assessments and documentation• Wired, wireless, security
• Encryption• Key management• Windows and Mac• Pre-boot authentication• Port and media control
OUR PARTNERS
133 Triangle Trade Drive, Cary, NC 27513919-460-1313 www.cadinc.com
@cadincCADincorporated
• Packeting shaping• Proxies• Web filters• SSL inspection• WAN optimization
• Wireless security• Zero-touch deployment• Cloud services• Network management and software• Wireless arays and access points
• Switching and routing• Network security• Enterprise wireless• Meraki wireless• Firewalls and UTMs
• 802.11ac solutions• Multi-vendor management• Instant controller-less access points• Scalable controller solutions• Spectrum analysis and WIPS
• Chromebooks• Management services• Applications• Google for Education• Google business solutions
• Strategic consulting• Turnkey projects• Pre-audit security review• Assessments and documentation• Wired, wireless, security
13th Annual IT Hot Topics Conference 13h Annual IT Hot Topics Conference
98
CONFERENCE AGENDA
Super Easy Purchasing
Buy online with federal diversity status and over 20 state and federal contracts.
Pre-Sales Design& Support
Qualified engineers design and review bills of materials to reduce costs as much as 60% on products and
support.
Best Pricing $Our certifications and
partner relationships can save you up to 48% on
products and services.
+ • Certified engineering• Promos and special offers• Access to top level support• Post-sales support
• Complete infrastructure solutions• Family-owned and operated• Woman-owned, Veteran-owned,
Small Business Federal status
Strategic Engineering
Our mission-centric solutions work the first time and give you zero hours of unplanned downtime.
Lifelong
RelationshipsMany clients have been with us for 15+ years because of our support and Customer Loyalty Program.
ABOUT US
ABO
UT
US A
GEN
DA
FEDERAL CERTIFICATIONS
Wednesday, May 6th TIME EVENT LOCATION8:00 - 9:00 Breakfast & Registration Grandville Ballroom
9:00 - 10:15 Intro & Keynote Grandville Ballroom
10:30 - 4:50 LockPick Village Wentworth
10:30 - 11:20 Breakout A Upstairs
11:30 - 1:00 Lunch Grandville Ballroom
1:00 - 1:50 Breakout B Upstairs
2:00 - 2:50 Breakout C Upstairs
3:00 - 3:45 Afternoon Break
4:00 - 4:50 Breakout D Upstairs
5:00 - 6:00 Cyber Security Student Reception Café East
6:00 - 9:00 30 Year Anniversary Bash Grandville Ballroom
Thursday, May 7th TIME EVENT LOCATION8:00 - 9:00 Breakfast & Registration Grandville Ballroom
9:00 - 10:15 Intro & Keynote Grandville Ballroom
10:30 - 4:50 LockPick Village Wentworth
10:30 - 11:20 Breakout A Upstairs
11:30 - 1:00 Lunch Grandville Ballroom
1:00 - 1:50 Breakout B Upstairs
2:00 - 2:50 Breakout C Upstairs
3:00 - 3:30 Afternoon Break Grandville Ballroom
3:30 - 4:30 Tech Challenges Grandville Ballroom
4:40 - 5:00 Prizes & Wrap-up Grandville Ballroom
Friday, May 8th TIME EVENT LOCATION7:30 - 8:00 Golfer Registration & Breakfast Griffin B
8:00 - 8:30 Practice Range Time Driving Range
8:30 - 1:30 IT Hot Topics Golf Tournament East Course
1:30 - 3:00 Tournament Award Luncheon Griffin B
13th Annual IT Hot Topics Conference 13h Annual IT Hot Topics Conference
1110
WEDNESDAY SESSION PLANNER
THURSDAY SESSION PLANNER
AG
END
AAG
END
A
WINDSORShowcase
TRINIT Y NOT TINGHAM SAVOY WENT WORTH BEAUMONTCyber Security Student Track
INTRO & KEYNOTE: Dr. Uma Gupta
Session A10:30-11:20
Open Stack Cloud and Hyper-
Converged SystemsDennis Tolliver
HP Servers & Storage
Getting the Most Out of SonicWALL’s CGSS
Rob Baxley
The Shape of Things to Come: Unexpected
Attack Vectors, Today and Tomorrow
Rob Pingor
The Shoulders of InfoSecJack Daniel
LockPick Village Social Media (In)SecurityRob Martin
LUNCH: Grandville Ballroom
Session B 1:00-1:50
Total Threat Protection with
Barracuda NetworksPaul Troy
Barracuda Networks
Healthcare IT Security: Why Is It So Hard?
Chuck Kesler
Wireless Planning and 802.11acTom Carpenter
Back to the Network Security Future:
Detection Comes BackMike Rothman
LockPick Village
Sniper Forensics: Targeting Data to Get Answers Fast
Ryan Linn
Session C 2:00-2:50
Network Access Control 101: Securing
the Critical Edge of Your Network
Tom MurphyBradford Networks
The Breaches Won’t Stop Until We Get
Serious About AppSecPhilip Casesa
Identity Management: Securing Your Data in the Digital Economy
Lance Peterman
Living and Leading with Power and Authenticity
Dr. Uma Gupta
CyberPatriot Challenge RoundtablesChris Gaw and
Jennifer Minella
BREAK
Session D 4:00-4:50
Next Generation Campus Architecture
Adam PerregoHP Networking
Best Practices for Security Best Pricing
Julie Allen & Susan Jabbusch
Google 2015, What’s New and
Important to YouFleetwood, Felts, Fogleman
Pen Testing Your Incident Response
ProgramRyan Linn
LockPick VillageSurvival Wi-FiTom Carpenter
WINDSORShowcase
TRINIT Y NOT TINGHAM SAVOY WENT WORTH
INTRO & KEYNOTE: Howard Schmidt
Session A10:30-11:20
Why I “Sold Out” and Why You Should Too: Making the Leap from
Operations to Sales EngineeringKarlo Arozqueta
HP Security
Holistic OpSec: Bringing Application, Server and
Network Security Together aka “When a security architect
writes an application”David Zendzian
Panel Discussion: SaaS Cloud Security
and ComplianceManny Landron,
Mike Rains and Holli Harrison
Actionable Threat Intelligence, ISIS,
and the SuperBallIan Amit
LockPick Village
LUNCH: Grandville Ballroom
Session B 1:00-1:50
Examining the Cyber Security Landscape and Discussing How
Next Generation Firewalls Bolster Your Security Posture
Chris Vazquez and Brittany RobertsonDell SonicWall
Software Defined Networking (SDN) Workshop (2 hour)
Dale Smith
Are Branded- Vulnerabilities
Helping Make the Internet a Better Place?
Omar Santos
Integrating Web Application Security Best Practices Within
the SDLCFrank Catucci LockPick
Village
Session C 2:00-2:50
Mobile EngagementJuan Tardio
Aruba
Cyber Threats and Trends 2015
Peter Ahearn
Cracking the Code: How IT Experts
Become IT LeadersMichael Santarcangelo
1312
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics Conference
WEDNESDAY SESSIONS
WED
NESD
AYWED
NES
DAY
Getting the most out of SonicWALL’s CGSSRob Baxley, Network Engineer, Carolina Advanced Digital, Inc.
SonicWALL’s Comprehensive Gateway Security Suite provides a host of services to enhance security and increase control of your network making it an excellent value for any SonicWALL UTM. Perfect for network administrators who want to learn how to enable and configure security services like Gateway Anti-virus and Intrusion Prevention. During this breakout you will hear how you can create content filtering and application control polices to prevent users from accessing inappropriate content or to stop those who are hogging your network’s bandwidth. Discover how to integrate Active Directory with Single Sign On to authenticates users and allows access based on user groups.
Open Stack Cloud and Hyper-Converged SystemsDennis Tolliver, Enterprise Server Specialist, HP
Many providers are jumping on two band wagons; Open Stack Cloud, and Hyper-Converged Systems. We will discuss what Open Stack Cloud is, how it is applied by some of the major vendors such as HP, VMware, and Red Hat. We will then talk about Hyper-Converged systems and their implementations of Operating Systems, Virtual Storage and their connection to the Cloud if so desired. As a sub topic we will look at Storage Virtualization.
The Shape of Things to Come: Unexpected Attack Vectors, Today and TomorrowRobert Pingor, Chief of Law Enforcement Division, The CORE Group
There is an intimate relationship between physical security and information security. Gone are the days were one discipline can operate in ignorance of the other. Criminals are often the early adopters of new technology and are the first to turn it on an unwitting public. Blended attacks are the new norm. Join us for an expose of attacks(some diabolically simple) being used today and talk about the possibilities for exploitation the future will bring.
The Shoulders of InfoSecJack Daniel, Strategist, Tenable Network Security & Founder, Security Bsides
We all know our information security history, right? Or at least we pretend we do. Many people in the security community really know the history of InfoSec from the perspective of the history of the business of InfoSec. Many of us aren’t aware of the foundations of information assurance laid down in government, military, and education- this talk is an introduction to some of the people and ideas at the foundation of what we do today. The early days of information assurance and security predate the Internet, so many stories are only available to the diminishing few who remember them; the Shoulders of InfoSec project is my attempt to recognize many foundational figures in our industry.
10:30am-11:20am
KEYNOTE
Dr. Uma Gupta
STEM ADVOCATE
Dr. Gupta is a highly sought after
speaker. She is a popular keynote
speaker who consistently delivers
outstanding leadership talks, lunch-
and-learn initiatives, workshops,
and corporate training. Her depth
and breadth of expertise covers a
wide range of current and cutting-
edge topics, including leadership, decision-making, technology
management, STEM, and entrepreneurship.
She holds a Ph.D in Industrial Engineering and an M.B.A. from the
University of Central Florida and has published four textbooks in
Information Systems and Technology and more than 65 journal papers.
She was recognized for her technology contributions with the Women
in Technology Award in Houston and was nominated a second time for
this award in Rochester, New York. She is the Founder and Executive
Director of STEM-SMART.org, a non-profit dedicated to giving college
and high school students work experiences through internships with
local and national corporate, non-profit, and government entities.
1514
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics ConferenceW
EDN
ESD
AYW
EDN
ESDAY
Back to the Network Security Future: Detection Comes BackMike Rothman, President, Securosis
“If you’re old enough to remember when intrusion detection became intrusion prevention, you’ll laugh as the pendulum swings back to detecting compromised devices. We’re going back to the future because prevention has largely failed as adversaries increasing evade IPS and network-based sandboxes, and employees continue to click on stuff they shouldn’t. In this session, Securosis analyst Mike Rothman will talk a number of approaches to supplement network-based prevention and sandboxing. And he’ll sprinkle in a whole mess of buzzwords like big data, cyber, and threat intelligence just to make sure you’re paying attention.”
Healthcare IT Security: Why Is It So Hard?Chuck Kesler, CISO, Duke Medicine
Healthcare is one of the most highly regulated industries, with IT security in particular being one area that is addressed extensively through industry regulations such as HIPAA, HITECH, and The Joint Commission. With all of these regulations, it would seem that healthcare organizations would be at the top of the game with respect to protecting information assets. However, as demonstrated by recent data breaches, healthcare struggles with these issues as much, if not more, than any other industry. In this talk, we will examine the challenges that healthcare organizations face in building an information security program, and some resources and approaches that can help them get started.
Total Threat Protection with Barracuda NetworksPaul Troy, Engineer, Barracuda Networks
Barracuda Total Threat Protection integrates security components to provide real-time protection against advanced threats. Each component provides comprehensive protection on its own respective vector—network, user, email, Web application, remote access, and mobile. This solution scales with your organizations and evolves with a constantly changing threat landscape, while simplifying management and providing you with flexible deployment options.
Wireless Planning and 802.11acTom Carpenter, Chief Technology Officer, CWNP
This presentation will focus on the important steps involved in wireless LAN planning and design. It will address issues introduced by 802.11ac and also ensure that security planning is part of the wireless LAN design process.
1:0
0-1:
50pm
2:00pm-2:50pm
Identity Management: Securing Your Data in the Digital EconomyLance Peterman, Sr. Information Security Professional, a global healthcare organization
With more and more data moving beyond conventional enterprise boundaries, identity has been established as the new perimeter for securing critical assets and intellectual property. In this session we will review some recent data breaches, focusing specifically on where identities have been compromised to both gain access to a network and to elevate privileges for more damaging activities. From there we will review various strategies for leveraging an identity management program to reduce risk for companies and better secure their data, whether inside their enterprise or in the cloud.
Living and Leading with Power and AuthenticityUma Gupta, STEM Advocate and Leader, STEM-SMART
“Clarity of purpose and resilience to life’s challenges are the foundations for personal and professional success in the speed-driven digital world in which we live today. Understanding who we are, why we do what we do, and how to live and lead from a place of authenticity can be an immensely rewarding experience that firmly establishes our place in the world.
In her keynote address, Dr. Gupta will offer the following insights:
• How our fast-thinking and slow-thinking brain influences our decisions and perceptions
• The impact and power of our habits on our life: how to keep the good ones and drop the not-so-good ones
• Motivation, rewards, and dreams: how to embark on a powerful journey of authentic living.
• The surprising relationship between happiness and success”
Network Access Control 101: Securing the Critical Edge of Your NetworkTom Murphy, SVP of Sales and Marketing, Bradford Networks
“As the volume and diversity of mobile devices on your network continue to rise, so does the need to ensure that every device is safe. Cyber criminals leverage vulnerable endpoints as backdoors to the network and Gartner predicts the source of breaches will have shifted from workstations to tablets and smartphones by 2017. As the attack surface of your network continues to multiply with each new device, network access control is essential to securing your data, assets and critical infrastructure. Attend this webinar to get a complete understanding of NAC functionality and how you can leverage visibility, policies, and automation to secure the critical edge of your network, including: Safe Onboarding, Device Profiling, Endpoint Compliance, Network Automation, Security Automation, and Rapid Threat Response.
WEDNESDAY SESSIONS WEDNESDAY SESSIONS
1716
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics Conference
The Breaches Won’t Stop Until We Get Serious About AppSecPhilip Casesa, Director of Information Technology, (ISC)2
With security breaches on a massive scale flooding the headlines, it seems that the answer is more security people to help stop the madness. What if we spent our time and energy fixing the root cause of most breaches – vulnerable software? Would we be able to stem the tide of these massive security breaches and win back our sanity? A compelling case that software security (AppSec) is the next great frontier in information security and the key to exiting this vicious cycle of incidents we find ourselves in and why the solution is harder than it seems. We will cover stories from the field, internet of things, application security programs, software supply chain and the perception gap between security executives and the developers. Wrapping up we will discuss opportunities to turn our fortunes around.
Best Practices for Securing Best PricingJulie Allen, Inside Sales Manager, Carolina Advanced DigitalSusan Jabbusch, VP, Carolina Advanced Digital
Best practices aren’t just for configuring your equipment anymore! Go behind the scenes with Carolina Advanced Digital for an in-depth look at what goes into each quote & order request from a VAR & integrator viewpoint. Learn how & when to engage Carolina Advanced Digital for the best possible pricing, how to plan for engineering projects & technical bills of materials, why Carolina Advanced Digital is rated highly by customers in value-add and customer satisfaction, and much more from an insider’s point of view on pricing, fulfillment, and the VAR-manufacturer relationship.
Google 2015, What’s New and Important to YouJordan Felts, Mike Fleetwood, Google Solutions, Synnex Corporation Scott Fogleman, Google Solutions, Synnex Corporation
During this session we will discuss where Google for Education and Google for Work have come over the last year and talk about why that is important to you. We will discuss the ever evolving classroom of the future and how Google has just the right solutions to fit your school’s needs. What is new with Chrome and how does Google Play for Education change the use of content in the classroom. We will also discuss the evolution of Google for Work and what types of solutions Google has for the commercial markets today. Where does Chrome and Android fit in the enterprise and what solutions could be using these technologies for the better. Through Google Apps, Chrome and Android Google can help solve daily problems in the both the classroom commercial space and we look forward to discussing these with you.
WED
NES
DAY
2:00
-2:5
0pm
4:00
pm-4
:50p
m
WEDNESDAY SESSIONS WEDNESDAY SESSIONS4:00pm
-4:50pm6pm
-9:00pmW
EDN
ESDAY
Next Generation Campus ArchitectureAdam Perrego, Solutions Architect, HP Networking
During this session we will cover the emerging technologies and architecture that is evolving in the industry as it relates to campus networks. We will be speaking to the enablement of mobility, SDN, multi rate Ethernet, High Speed Backbones, and Unified Policy for campus access.
Pen Testing your Incident Response ProgramRyan Linn, Director of Penetration Testing, Nuix
“Whether for compliance or for security, penetration testing is now being incorporated into most organization’s security programs. Penetration testing is an active attack simulation which serves to expose vulnerabilities, configuration oversights, and strategic and architectural weaknesses. However, many organizations treat this test as an independent and isolated tool. This viewpoint significantly reduces the value of the exercise by only realizing a portion of the value that pen tests provide. This talk will look beyond the report results and discuss how to maximize the value of a penetration test both during and after the exercise. The additional benefits can include greater ability to identify and respond to attacks as well as identifying monitoring blind spots.
This talk will play out a sample scenario and discuss different ways that penetration testing and incident response can work together to make an organization stronger.”
30TH ANNIVERSARY BASH Cheers to 30 Years! Join us for a fun and intimate evening party to celebrate 30 years in business. Network with peers, colleagues, and speakers. Enjoy nostalgia, music, interactive games, caricaturist, technology challenges, and our own Family Feud Twisted Tech Edition with your host Matt Helmer.
Cheers to 30 Years!
19
13th Annual IT Hot Topics Conference
18
13th Annual IT Hot Topics Conference
Fireside Chat with Howard Schmidt Partner at Ridge Schmidt, Former Cyber Advisor to Presidents Barack Obama and George W. Bush; former CISO and CSO at Microsoft; former CISO at eBay
Howard Schmidt serves as a partner in the strategic advisory firm, Ridge-Schmidt Cyber, an executive services firm that helps leaders in business and government navigate the increasing demands of cybersecurity. He serves in this position with Tom Ridge, the first secretary of the Department of Homeland Security. He also serves as executive director of The Software Assurance Forum for Excellence in Code (SAFECode).
Howard A. Schmidt brings together talents in business, defense, intelligence, law enforcement, privacy, academia and international relations, gained from a distinguished career spanning 40 years.
He served as Special Assistant to the President and the Cybersecurity Coordinator for the federal government. In this role Mr. Schmidt was responsible for coordinating interagency cybersecurity policy development and implementation and for coordinating engagement with federal, state, local, international, and private sector cybersecurity partners.
Previously, Mr. Schmidt was the President and CEO of the Information Security Forum (ISF). Before ISF, he served as Vice President and Chief Information Security Officer and Chief Security Strategist for eBay Inc., and formerly operated as the Chief Security Officer for Microsoft Corp. He also served as Chief Security Strategist for the US-CERT Partners Program for the Department of Homeland Security.
Mr. Schmidt also brings to bear over 26 years of military service. Beginning active duty with the Air Force, he later joined the Arizona Air National Guard. With the AF he served in a number of military and civilian roles culminating as Supervisory Special Agent with the Office of Special Investigations (AFOSI). He finished his last 12 years as an Army Reserve Special Agent with Criminal Investigation Division’s (CID) Computer Crime Unit, all while serving over a decade as police officer with the Chandler Police Department.
Mr. Schmidt holds a bachelor’s degree in business administration (BSBA) and a master’s degree in organizational management (MAOM) from the University of Phoenix. He also holds an Honorary Doctorate degree in Humane Letters. Howard was an Adjunct Professor at GA Tech, GTISC, Professor of Research at Idaho State University and Adjunct Distinguished Fellow with Carnegie Mellon’s CyLab and a Distinguished Fellow of the Ponemon Privacy Institute.
Howard is a Ham Radio operator (W7HAS), a private pilot, outdoorsman and an avid Harley-Davidson rider. He is married to Raemarie J. Schmidt, a forensic scientist and researcher and instructor in the field of computer forensics. Together, they are proud parents, and happy grandparents.
WED
NES
DAY
10:00am-11:20am Social Media (In)SecurityRob Martin, President, Raleigh ISSAStatistics say less than 1/3 of users properly secure their social media accounts. Find out how sites like Facebook, Twitter, and Instagram are becoming threats to students, military, and every day users. Learn about meta data, geotagging and more. When it comes to cyber security, sometimes we’re our own worst enemy.
1:00pm-1:50pm Sniper Forensics: Targeting Data to Get Answers FastRyan Linn, Director of Penetration Testing, Nuix
Forensics has historically been a lengthy process: start imaging systems, wait, load the data for analysis, wait, then finally review. If more imaging is necessary the cycle repeats. If you are in the middle of a critical event, that process takes longer than upper management is willing to wait. Sniper Forensics is a different methodology which speeds up the classic forensics process and helps uncover answers sooner. The theory is “start with what you know to get to the data you need faster”. This presentation will discuss what data to focus on first and walk through some sample scenarios of how Sniper Forensics plays out in typical incident response exercises.
2:00pm-2:50pm CyberPatriot Challenge RoundtablesChris Gaw Coach & Mentor, CyberPatriotJennifer Minella
Join your peers for collaborative roundtable discussions of past CyberPatriot Challenges. Roundtable topics by table for Windows Admin, Ubuntu, and Networking challenges.
4:00pm-4:50pm Survival Wi-FiTom Carpenter, Chief Technology Officer, CWNP
An introduction to Wi-Fi topics you need to survive in today’s connected world. Covers the basics of RF (radio frequency) technologies, security concepts, and the wacky world of endpoints - knowledge to help troubleshoot, secure, or wow your friends.
KEYNOTECYBER SECURITY STUDENT TRACK THU
RSDAY
2120
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics ConferenceTH
URSD
AY10:30am
-11:20am1:00pm
-1:50pm
Actionable Threat Intelligence, ISIS, and the SuperBallIan Amit, Vice President, ZeroFox
“When adding a new threat intelligence feed into your threat model and security practice, one always has to ask: “what is the value?” Unfortunately, over the past couple of years, organizations have struggled with showing true value from standard threat intelligence feeds for several reasons, most of which coincide with the fact that the feeds are too generic, and do not directly relate to the operating environment of the organization.
In this talk, we will discuss how to create a customized, organization-specific threat intelligence feed, that in turn will be used to actively increase the security posture of the organization in a measurable way. Some of the examples we will address include dealing with DDoS attacks & social media account takeovers and adjusting to finding threats and threat actors in order to proactively tune defenses before an attack.”
Holistic OpSec: Bringing application, server and network security together aka “When a security architect writes an application”David Zendzian, Founder & Managing Partner, ZZ Servers
“This case-study will present a story of Operational Security as it is today and dig into an examination of a modern enterprise rails application. It will review application security best practices going through specific controls within the application, best practices in deploying and how to integrate application controls, local host and network firewall controls into a self monitoring, alerting and automated security system.
All techniques and tools reviewed are open source and not only freely available but strongly encouraged to use. A short list of technologies that will be reviewed include: rails, nginx, naxsi, rack-attack, brakeman, syslog, fail2ban, ossec and more.”
Panel Discussion - SaaS Cloud Security and ComplianceManny Landron, Security and Compliance team, Citrix ShareFile Mike Rains, Security and Compliance team, Citrix ShareFile Holli Harrison, Security and Compliance team, Citrix ShareFile
Q&A around securing and ensuring compliance for Software-as-a-Service(SaaS) application hosted in a hybrid cloud environment comprised on collocation data centers and Infrastructure-as-a-Service (IaaS) cloud providers leveraging traditional network and software defined security.
THURSDAY SESSIONS
THU
RSD
AY10
:30a
m-1
1:20
am
Why I “Sold Out” and Why You Should Too: Making the Leap from Operations to Sales EngineeringKarlo Arozqueta, Systems Engineer, HP Security Solutions, Federal
“Mr. Arozqueta left a 7 year career conducting incident response in a 24/7 environment for a simple sales engineering position. He applied for the job on nothing but the trust he had in a long time friend who said it was the best move she ever made and he wouldn’t regret it. His Operations peers were quick to point out that he had “sold out” and that they would leave the proverbial porch light on for him because there was no way he would enjoy it and he would definitely be back.
However, Mr. Arozqueta’s entire life’s journey had prepared him for and led him to succeed in the sales engineering role: a role devoid of late night phone calls, haphazard sleep schedules and chasing down subordinates to sign their timesheets. He had found the perfect job that would allow him to remain technical, specialize in a few technologies and never worry about being “promoted” to management. Delivered in an informal story-telling style, Mr. Arozqueta will talk about how he’s been doing 1.5 years into his role and why it may be a viable career change for you too.”
Are Branded-Vulnerabilities Helping Make the Internet a Better Place?Omar Santos, Senior Incident Manager, Cisco PSIRTIf the vulnerability is sexy enough, it gets a name. If the vulnerability can make the researcher or the company that found it rich, it gets a name. From Heartbleed to ShellShock, Poodle and GHOST, vulnerability branding is the new normal. Is this new trend in vulnerability disclosure helping make the Internet a better place? This session is an active discussion on how bad actors are benefitting more from these branded-vulnerabilities than the good guys. We will discuss the trends in vulnerability disclosure and the evolution of network security.
Examining the Cyber Security Landscape and Discussing How Next Generation Firewalls Bolster Your Security PostureChris Vazquez, Field Security Specialist, Dell SonicWALL Brittany Robertson, Field Security Specialist, Dell SonicWALL
Join us in discussing how security threats continue to grow and evolve with networks being overburdened with increased usage, bandwidth and devices. An examination of the current threat landscape, and what is predicted in 2015. A discussion about how Next Generation Firewalls continue to revolutionize network security.
THURSDAY SESSIONS
2322
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics Conference
Integrating Web Application Security Best Practices Within the SDLCFrank Catucci, Director of Web Application Security, Qualys
This discussion will focus on how to utilize and integrate web application security and scanning best practices within the software development life-cycle (SDLC). Frank will address how to build security into the software development lifecycle, discuss security requirements, governance, planning, goals, challenges, implementations and plans for growth. This talk will focus on high level practices but also give insight into the technical aspects of what will be required for success.
Software Defined Networking (SDN) Workshop (2 hour)Dale Smith, SDN Specialist, HP Networking
“Overview of Current Software Defined Networking (SDN) Technologies. Survey session to provide an overview of Software Defined Networking (SDN)current trends, frameworks and technologies. This session will provide an overview of various SDN architectures with a focus on the requirements for designing and deploying the SDN enabled campus and branch site.
The session will briefly touch on automation and programming technologies, but a programming or software development background is not required.”
Cracking the Code: How IT Experts Become IT LeadersMichael Santarcangelo, Security Catalyst
“The challenge isn’t technology. The opportunity is IT leadership. The pathway from IT expert to IT leader includes understanding 5 foundational elements and demonstrating the 9 competencies of remarkable IT leadership. In this session, Michael reveals the benefits of a competency based approach, explains how to assess where you are currently, and shares insights on how to demonstrate your value, earn your place in the executive suite, and have your voice heard by the board and other leaders.
This session is for IT experts and IT leaders with an appetite for personal development, and the desire and ability to be remarkable.”
Cyber Threats and Trends 2015Peter Ahearn, Special Agent, Cyber Crimes, FBI
How do you ensure the security of your data is preserved in a way that stays one step ahead of the bad guys? Unfortunately, criminals - domestic and abroad - are relentless in searching for creative new ways to obtain money and/or intellectual property from companies and their clients. Today’s cybercriminals are innovative and organized. This is your opportunity to hear the FBI share current case studies and offer tangible suggestions for what you can do to mitigate your cybersecurity risks to keep your company and clients from being victimized.
1:00
pm-1
:50p
m2:
00pm
-2:5
0pm
THU
RSDAYTH
URS
DAY
Mobile EngagementJuan Tardio, Senior Systems Engineer, Aruba Networks
The new mobile engagement solution offering media-rich apps and indoor location services over the fastest Wi-Fi on the planet. It is a contextually aware of connected users, devices and apps as well as location and time of day.
THURSDAY SESSIONS THURSDAY SESSIONS
TECH CHALLENGES
This year’s Tech Challenge features Tech Jeopardy – a new twist on trivia! Test your skills across several areas of technology and security with our custom engineering-approved Jeopardy answers. Make your mark with Double Jeopardy to really shine. Who will win the Jeopardy challenge?
Take a trip through technology memory lane with a visit to the Vintage Tech Museum onsite Wednesday. Ooh and aah at this nostalgic collection of Apple IIs, Commodores, Ataris, and other vintage computers and classic gaming systems. This ain’t your grandkids’ gaming console!
http://vintagetechmuseum.org | Twitter: @VinTechMuseum
25
13th Annual IT Hot Topics Conference
24
13th Annual IT Hot Topics ConferenceFRID
AYTH
URS
DAY CONFERENCE PRIZES:
ATTEND TO WIN
Don’t miss the Thursday afternoon wrap-up with prizes for your opportunity to win gift cards, prize baskets, geeky gadgets, drones, tablets and more!
Participate for more tickets and MORE CHANCES TO WIN! Attend breakout sessions and fill out evaluation forms to earn prize raffle tickets.
Carolina Advanced Digital, Inc. is a USAC E-Rate Service Provider. If you participate in the E-Rate program you may be ineligible to receive certain event prizes or giveaways. CAD assumes all attendees are self-monitoring since many event attendees are not part of this program.
IT HOT TOPICS DEMO NETWORK Each year, the Carolina Advanced Digital Engineering Team puts together an enterprise-class conference network that provides both attendee wireless access as well as a demo environment for attendees and partner engineers to view and evaluate.
This year the IT Hot Topics Demo Network includes equipment from HP, Meru, Barracuda, Bradford, SonicWALL and Exinda. Visit http://demo.hottopicsconference.com for information and links to management interfaces and credentials. Also look for printed network drawings in the conference areas and upstairs, where our conference “MDF” is located.
Visit http://demo.hottopicsconference.com
Friday, May 8th • Grandover East Course
Come play with the pros! Well, the IT pros that is. Join our team of industry experts and test your skills on the green. Our annual Hot Topics Golf Tourney is a fun, casual way to meet and mingle with peers and our IT experts while enjoying a little bit of the outdoors.
Hot Topics Golf Tourney is captain’s choice with a shotgun start. Prizes are awarded for First and Second Place teams as well as for eight specialty marked contest holes.
The Golf Tourney is open to any conference attendees who wish to play.
Tournament PackThe tournament fee includes a Tournament Play Pack, breakfast, and entry to the awards luncheon immediately after the tournament.
Your Tournament Play Pack includes:• Golfers Kickoff Breakfast• CAD Golf Play Pack• Golf Cart• GPS• Range Balls• Beverages (no snacks)• Golfers Awards Luncheon
Proper attire is required:• Shirts with collar• No jeans or short shorts• No metal spikes
Course DetailsAll 2015 tournament participants will play the East Course at Grandover. Grandover received four and a half stars, noted as one of “America’s Best Places to Play” by Golf Digest and “Best Conditioned Courses in North America” by Golf Digest (4th place).
GOLF TOURNAMENT
IMPORTANT INFOPlaying Grandover East CourseBreakfast at 7:30amShotgun Start at 8:30amCaptain’s Choice / Best BallMen play from White teesLadies play from Red tees
CONTEST HOLESHole 3: Closest to the PinHole 6: Longest PuttHole 10: Longest Drive Hole 14: Straightest Drive
HOLE-IN-ONE PRIZESHole 3: $5,000 cashHole 7: Premium electronics
package Hole 12: Golf Package with
Driver & Woods Hole 16: Golf Package with Irons
2726
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics Conference
LOCKPICK VILLAGE Want to tinker with locks and tools the likes of which you’ve only seen in movies featuring police, spies, and secret agents? Then come on by the Lockpick Village, run by The CORE Group, where you will have the opportunity to learn hands-on how the fundamental hardware of physical security operates and how it can be compromised. No experience is needed, instruction is provided. Try your hand at challenges with progressive tumbler locks, padlock shims, and more.
enterthecore.net/lockpicking-manipulation
EMCEEEnjoy the antics of long-time friend John McCumber as he serves as master of ceremonies. John is an Air Force veteran, Cryptographic Fellow of the NSA, Professorial Lecturer at George Washington University, speaker, author, motorcycle-lover, and voted “Best Entertainer” by the Carolina Advanced Digital staff four years in a row.
@johnmccumber
MEE
T TH
E TE
AM
MEET THE TEAM
Julie AllenInside Sales [email protected]
Rob BaxleyNetwork [email protected]
Bre ColemanSales [email protected]
Heather MooreSales [email protected]
Michelle DziengelBusiness [email protected]
Morgan DziengelGovernment Sales [email protected]
Brenda KingSales [email protected]
Jennifer MinellaVP of [email protected]
Geraldine [email protected]
Kory ThornbergTechnical Team Lead & Network [email protected]
Matt HelmerPro Services [email protected]
John JabbuschPresident & Chief Engineer
Susan JabbuschExecutive Vice President
Carolina Advanced Digital, Inc. is proud to have a dedicated team of engineers and account specialists to make sure your every need is covered. Meet the 2015 team!
TIDBITS
Who’s Your
Daddy?
American college professor and scientist Robert Goddard built and flew the world’s first liquid propellant rocket on March 16, 1926. Its flight, though unimpressive (it climbed only 12.5 meters), was the forerunner of the Saturn V Moon rocket 43 years later. He is often referred to as the “father of modern rocketry.”
Did You Know?
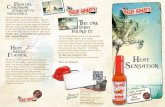
Did you know? John and Susan met in the 70s while serving in Naval Intelligence in Key West, FL.
2928
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics Conference
THANK YOU TO OUR CONFERENCE SPONSORS
TIDBITSTI
DB
ITS
GOLD SPONSORS
Carolina Advanced Digital, Inc. would like to take the time to thank all of our generous sponsors who support this year’s IT Hot Topics Conference.
SILVER SPONSORS
INDUSTRY PARTNERS
BRONZE SPONSORS
THANK YOU TO OUR ADVISORY COMMITTEE
David Bankole Chief Security Architect Novant Health Gray CassellChief Information OfficerTown of Kernersville Jason ClaytonTechnology CoordinatorPerson County Schools Ryan DraughnChief Information OfficerNC League of Municipalities Maurice FerrellAssistant Director, Center for Public TechnologyUNC School of Government
Joel HartleyChief Information OfficerDavidson County Government Chuck KeslerChief Information Security OfficerDuke Medicine Dominic MesserNetwork AdministratorHarnett Health System Wes RinehartDirector of Technical SupportCarteret County Schools Michael SeymourVice President of Information TechnologyPike Enterprises
Gary SteeleyInformation Technology ManagerPiedmont Triad Regional Council Scott Van MoppesAirport Systems ManagerHorry County Dept. Airports Chris WheelerDirector, Network ServicesWake Tech Community College Jason WhitakerChief Information OfficerVillage of Pinehurst
STEM MATTERS MAGAZINE Featured keynote speaker Dr. Uma Gupta is a founder of STEM-SMART, an organization that offers educational programs, consulting, conferences, resources and partnerships to build, strengthen and diversify STEM talent. This includes a print magazine, STEMatters, that provides step-by-step guidance on STEM degree programs and careers, an internship hub that links local employers with high school and college students, evening and weekend STEM educational and career programs for high school students, an online mentoring forum that brings together employers and students, and
other resources necessary for individuals to succeed in STEM.
http://www.stem-smart.org | Twitter: @STEM-SMART
3130
13th Annual IT Hot Topics Conference 13th Annual IT Hot Topics ConferenceTI
DB
ITS
We’re tweeting updates throughout the event @hottopics. Use the hashtag #hottopics15 when tweeting about IT Hot Topics Conference!
Want to follow CAD year round? Find us on Twitter@CADinc.
We are also on Facebook! Like us atfacebook.com/CADincorporated.
Find us on LinkedIn
https://www.linkedin.com/company/carolina-advanced-digital
SUPPORT CYBERPATRIOT Carolina Advanced Digital is committed to the advancement of our community through education on STEM and Cyber Security topics. We’re pleased to support our local students competing in the CyberPatriot Challenges, and we encourage professionals to participate as sponsors, advisors and mentors. Visit www.cyberpatriot.org for more information and to register as a mentor.
http://cyberpatriot.hottopicsconference.com
SOCIAL MEDIA INFO
IT HOT TOPICS CONFERENCE 2016
Join us next year at IT Hot Topics 2016!Carolina Advanced Digital’s 14th annual
IT Hot Topics Conference & Golf TourneyMay 4-6, 2015
Grandover Resort Greensboro, NC
By attending IT Hot Topics Conference 2015, you understand and agree that photographs and video taken at the event may be used
in print media publications, advertisements, online and in any other format Carolina Advanced Digital, Inc. at its sole discretion may choose.
Old School Robots!
The word robot was introduced to the public by the Czech writer Karel Čapek in his play R.U.R. (Rossum’s Universal Robots), published in 1920. But robots existed in legend long before then. Many ancient mythologies, and most modern religions include artificial people, such as the mechanical servants built by the Greek god Hephaestus (Vulcan to the Romans).